Microsoft 70-411 Exam Dumps 2021
Exam Code: 70-411 (exam 70 411), Exam Name: Administering Windows Server 2012, Certification Provider: Microsoft Certifitcation, Free Today! Guaranteed Training- Pass 70-411 Exam.
Free 70-411 Demo Online For Microsoft Certifitcation:
NEW QUESTION 1
Your network contains one Active- Directory domain named contoso.com. The domain contains a file server named Server0l that runs Windows Server 2012 R2. Server0l has an operating system drive and a data drive. Server0l has a Trusted Platform Module (7PM).
You need to enable Bit Locker Drive Encryption (BitLocker) for the data drive on Server0l. Which cmdlet should you run first?
- A. Unblock TPM
- B. Enable-BitLocker
- C. Add-BitLockerKcyProtector
- D. Install-WindowsFeature
Answer: D
NEW QUESTION 2
HOTSPOT
Your network contains an Active Directory domain named contoso.com.
All DNS servers host a DNS zone named adatum.com. The adatum.com zone is not Active Directory-integrated.
An administrator modifies the start of authority (SOA) record for the adatum.com zone. After the modification, you discover that when you add or modify DNS records in the
adatum.com zone, the changes are not transferred to the DNS servers that host secondary
copies of the adatum.com zone.
You need to ensure that the records are transferred to all the copies of the adatum.com zone.
What should you modify in the SOA record for the adatum.com zone? To answer, select the appropriate setting in the answer area.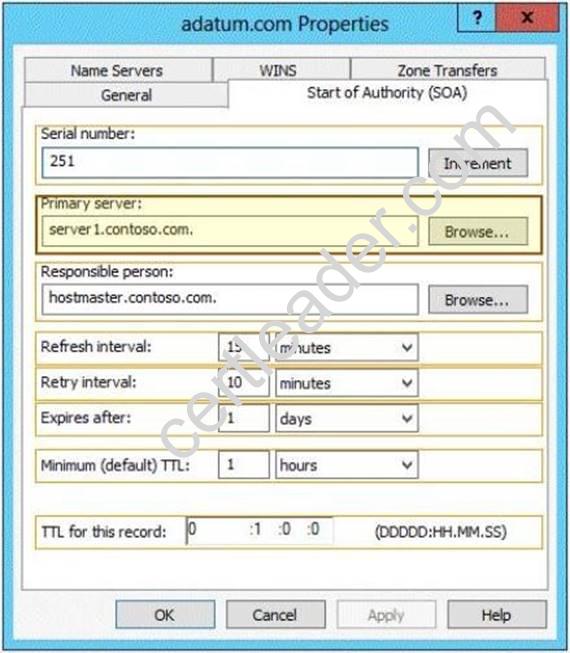
Answer:
Explanation: When a DNS server receives an update through Active Directory replication:
If the serial number of the replicated record is higher than the serial number in the SOA record of the local copy of the zone, the local zone serial number is set to the serial number in the replicated record.
Note Each DNS record in the zone has a copy of the zone serial number at the time when the record was last modified.
If the serial number of the replicated record is the same or lower than the local serial number, and if the local DNS server is configured not to allow zone transfer of the zone, the local zone serial number is not changed.
If the serial number of the replicated record is the same or lower than the local zone serial number, if the DNS server is configured to allow a zone transfer of the zone, and if the local
zone serial number has not been changed since the last zone transfer occurred to a remote DNS server, then the local zone serial number will be incremented. Otherwise that is if a copy of the zone with the current local zone serial number has not been transferred to a remote DNS server, the local zone serial number is not changed.
NEW QUESTION 3
Your network contains an Active Directory domain named contoso.com. The domain contains a RADIUS server named Server1 that runs Windows Server 2012 R2.
You add a VPN server named Server2 to the network. On Server1, you create several network policies.
You need to configure Server1 to accept authentication requests from Server2. Which tool should you use on Server1?
- A. Server Manager
- B. Routing and Remote Access
- C. New-NpsRadiusClient
- D. Connection Manager Administration Kit (CMAK)
Answer: C
Explanation: New-NpsRadiusClient -Name "NameOfMyClientGroup" -Address "10.1.0.0/16" - AuthAttributeRequired 0 -NapCompatible 0 -SharedSecret "SuperSharedSecretxyz" - VendorName "RADIUS Standard"

Reference:
http: //technet. microsoft. com/en-us/library/hh918425(v=wps. 620). aspx
http: //technet. microsoft. com/en-us/library/jj872740(v=wps. 620). aspx
http: //technet. microsoft. com/en-us/library/dd469790. aspx
NEW QUESTION 4
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2008 R2.
You plan to test Windows Server 2012 R2 by using native-boot virtual hard disks (VHDs). You have a Windows image file named file1.wim.
You need to add an image of a volume to file1.wim. What should you do?
- A. Run imagex.exe and specify the /append parameter.
- B. Run imagex.exe and specify the /export parameter.
- C. Run dism.exe and specify the /image parameter.
- D. Run dism.exe and specify the /append-image parameter.
Answer: D
Explanation: The Deployment Image Servicing and Management (DISM) tool is a command-line tool that enables the creation of Windows image (.wim) files for deployment in a manufacturing or corporate IT environment. The /Append-Image option appends a volume image to an existing .wim file allowing you to store many customized Windows images in a fraction of the space. When you combine two or more Windows image files into
a single .wim, any files that are duplicated between the images are only stored once.
Incorrect:
Not A, Not B: Imagex has been retired and replaced by dism.
Reference: Append a Volume Image to an Existing Image Using DISM https://technet.microsoft.com/en-us/library/hh824916.aspx
NEW QUESTION 5
Your network contains an Active Directory domain named contoso.com. All servers run Windows Server 2012 R2.
Client computers run either Windows 7 or Windows 8. All of the client computers have an application named App1 installed.
The domain contains a Group Policy object (GPO) named GPO1 that is applied to all of the client computers.
You need to add a system variable named App1Data to all of the client computers. Which Group Policy preference should you configure?
- A. Environment
- B. Ini Files
- C. Data Sources
- D. Services
Answer: A
Explanation: Environment Variable preference items allow you to create, update, replace, and delete user and system environment variables or semicolon-delimited segments of the PATH variable. Before you create an Environment Variable preference item, you should review the behavior of each type of action possible with this extension.
NEW QUESTION 6
Your network contains a Hyper-V host named Hyperv1. Hyperv1 runs Windows Server 2012 R2.
Hyperv1 hosts four virtual machines named VM1, VM2, VM3, and VM4. AH of the virtual machines run Windows Server 2008 R2.
You need to view the amount of memory resources and processor resources that VM4 currently uses.
Which tool should you use on Hyperv1?
- A. Windows System Resource Manager (WSRM)
- B. Task Manager
- C. Hyper-V Manager
- D. Resource Monitor
Answer: C
Explanation: Hyper-V Performance Monitoring Tool
Know which resource is consuming more CPU. Find out if CPUs are running at full capacity or if they are being underutilized. Metrics tracked include Total CPU utilization, Guest CPU utilization, Hypervisor CPU utilization, idle CPU utilization, etc.
WSRM is deprecated starting with Windows Server 2012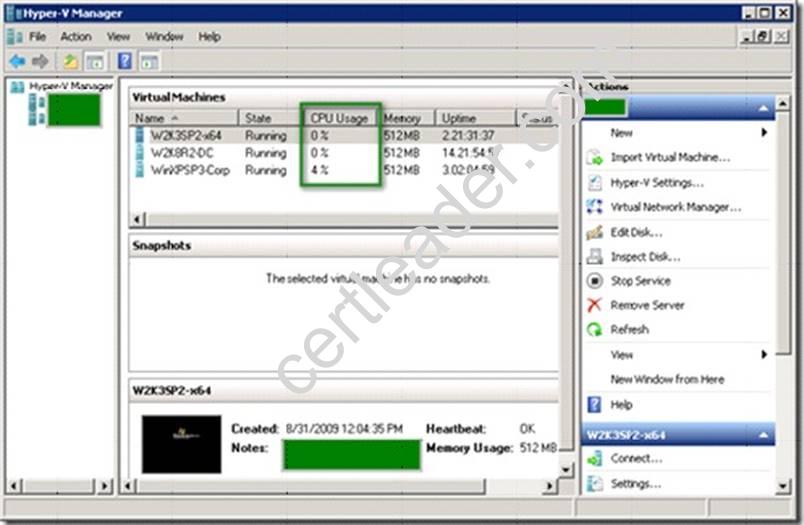
NEW QUESTION 7
Your network contains two servers named Server1 and Server2. Both servers run Windows Server 2012 R2 and have the DNS Server server role installed. Server1 hosts a primary zone for contoso.com. Server2 hosts a secondary zone for contoso.com. The zone is not configured to notify secondary servers of changes automatically.
You update several records on Server1.
You need to force the replication of the contoso.com zone records from Server1 to Server2. What should you do from Server2?
- A. Right-click the contoso.com zone and click Reload.
- B. Right-click the contoso.com zone and click Transfer from Master.
- C. Right-click Server2 and click Update Server Data Files.
- D. Right-click Server2 and click Refresh.
Answer: B
Explanation: Initiates zone transfer from secondary server
Open DNS; In the console tree, right-click the applicable zone and click Transfer from master.
References:
http: //technet. microsoft. com/en-us/library/cc779391%28v=ws. 10%29. aspx
http: //technet. microsoft. com/en-us/library/cc779391%28v=ws. 10%29. aspx
http: //technet. microsoft. com/en-us/library/cc786985(v=ws. 10). aspx
http: //technet. microsoft. com/en-us/library/cc779391(v=ws. 10). aspx
NEW QUESTION 8
Your network contains an Active Directory domain named contoso.com. The domain contains a domain controller named DC1 that runs Windows Server 2012.
You have a Group Policy object (GPO) named GPO1 that contains several custom Administrative templates.
You need to filter the GPO to display only settings that will be removed from the registry when the GPO falls out of scope. The solution must only display settings that are either enabled or disabled and that have a comment.
How should you configure the filter?
To answer, select the appropriate options below. Select three.

- A. Set Managed to: Yes
- B. Set Managed to: No
- C. Set Managed to: Any
- D. Set Configured to: Yes
- E. Set Configured to: No
- F. Set Configured to: Any
- G. Set Commented to: Yes
- H. Set Commented to: No
- I. Set Commented to: Any
Answer: AFG
NEW QUESTION 9
Your network contains a single Active Directory domain named contoso.com. The domain contains a domain controller named DC1 that hosts the primary DNS zone for contoso.com.
All servers dynamically register their host names.
You install three new Web servers that host identical copies of your company's intranet website. The servers are configured as shown in the following table.
You need to use DNS records to load balance name resolution queries for intranet.contoso.com between the three Web servers.
What is the minimum number of DNS records that you should create manually?
- A. 1
- B. 3
- C. 4
- D. 6
Answer: B
Explanation: To create DNS Host (A) Records for all internal pool servers
1. Click Stabrt, click All Programs, click Administrative Tools, and then click DNS.
2. In DNS Manager, click the DNS Server that manages your records to expand it.
3. Click Forward Lookup Zones to expand it.
4. Right-click the DNS domain that you need to add records to, and then click New Host (A or AAAA).
5. In the Name box, type the name of the host record (the domain name will be automatically appended).
6. In the IP Address box, type the IP address of the individual Front End Server and then select Create associated pointer (PTR) record or Allow any authenticated user to update DNS records with the same owner name, if applicable.
7. Continue creating records for all member Front End Servers that will participate in DNS Load Balancing.
For example, if you had a pool named pool1.contoso.com and three Front End Servers, you would create the following DNS entries: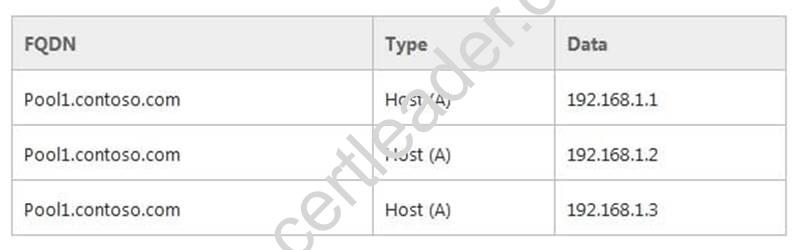
erence:
http: //technet. microsoft. com/en-us/library/cc772506. aspx
http: //technet. microsoft. com/en-us/library/gg398251. aspx
NEW QUESTION 10
HOTSPOT
Your network contains an Active Directory domain named contoso.com. The domain contains servers named Server1 and Server2. Both servers have the DFS Replication role service installed.
You need to configure the DFS Replication environment to meet the following requirements:
✑ Increase the quota limit of the staging folder.
✑ Configure the staging folder cleanup process to provide the highest amount of free space possible.
Which cmdlets should you use to meet each requirement? To answer, select the appropriate options in the answer area.
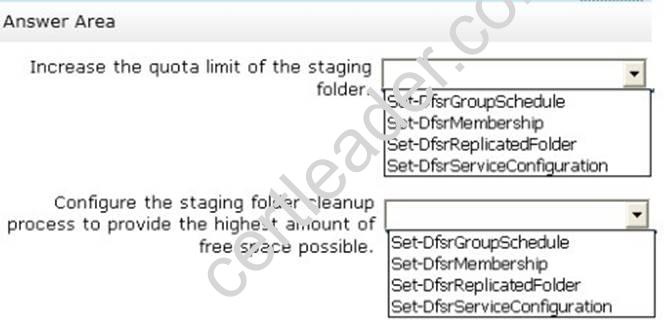
Answer:
Explanation: 
NEW QUESTION 11
Your network contains an Active Directory forest named contoso.com. The forest contains a single domain. All domain controllers run Windows Server 2012 R2.
The domain contains two domain controllers. The domain controllers are configured as shown in the following table.
Active Directory Recycle Bin is enabled.
You discover that a support technician accidentally removed 100 users from an Active Directory group named Group1 an hour ago.
You need to restore the membership of Group1. What should you do?
- A. Recover the items by using Active Directory Recycle Bin.
- B. Modify the Recycled attribute of Group1.
- C. Perform tombstone reanimation.
- D. Perform an authoritative restore.
- E. Perform a non- authoritative restore.
Answer: A
Explanation: Active Directory Recycle Bin helps minimize directory service downtime by enhancing your ability to preserve and restore accidentally deleted Active Directory objects without restoring Active Directory data from backups, restarting Active Directory Domain Services (AD DS), or rebooting domain controllers.
When you enable Active Directory Recycle Bin, all link-valued and non-link-valued attributes of the deleted Active Directory objects are preserved and the objects are restored in their entirety to the same consistent logical state that they were in immediately before deletion. For example, restored user accounts automatically regain all group memberships and corresponding access rights that they had immediately before deletion, within and across domains.
NEW QUESTION 12
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that has the Remote Access server role installed.
DirectAccess is implemented on Server1 by using the default configuration.
You discover that DirectAccess clients do not use DirectAccess when accessing websites on the Internet.
You need to ensure that DirectAccess clients access all Internet websites by using their DirectAccess connection.
What should you do?
- A. Configure a DNS suffix search list on the DirectAccess clients.
- B. Configure DirectAccess to enable force tunneling.
- C. Disable the DirectAccess Passive Mode policy setting in the DirectAccess Client Settings Group Policy object (GPO).
- D. Enable the Route all traffic through the internal network policy setting in the DirectAccess Server Settings Group Policy object (GPO).
Answer: B
Explanation: With IPv6 and the Name Resolution Policy Table (NRPT), by default, DirectAccess clients separate their intranet and Internet traffic as follows:
✑ DNS name queries for intranet fully qualified domain names (FQDNs) and all
intranet traffic is exchanged over the tunnels that are created with the DirectAccess server or directly with intranet servers. Intranet traffic from DirectAccess clients is IPv6 traffic.
✑ DNS name queries for FQDNs that correspond to exemption rules or do not match
the intranet namespace, and all traffic to Internet servers, is exchanged over the physical interface that is connected to the Internet. Internet traffic from DirectAccess clients is typically IPv4 traffic.
In contrast, by default, some remote access virtual private network (VPN) implementations, including the VPN client, send all intranet and Internet traffic over the remote access VPN
connection. Internet-bound traffic is routed by the VPN server to intranet IPv4 web proxy servers for access to IPv4 Internet resources. It is possible to separate the intranet and Internet traffic for remote access VPN clients by using split tunneling. This involves configuring the Internet Protocol (IP) routing table on VPN clients so that traffic to intranet locations is sent over the VPN connection, and traffic to all other locations is sent by using the physical interface that is connected to the Internet.
You can configure DirectAccess clients to send all of their traffic through the tunnels to the DirectAccess server with force tunneling. When force tunneling is configured, DirectAccess clients detect that they are on the Internet, and they remove their IPv4 default route. With the exception of local subnet traffic, all traffic sent by the DirectAccess client is IPv6 traffic that goes through tunnels to the DirectAccess server.
NEW QUESTION 13
Your network contains an Active Directory domain named adatum.com. The domain
contains a server named Server1 that runs Windows Server 2012 R2. Server1 is configured as a Network Policy Server (NPS) server and as a DHCP server.
The network contains two subnets named Subnet1 and Subnet2. Server1 has a DHCP scope for each subnet.
You need to ensure that noncompliant computers on Subnet1 receive different network policies than noncompliant computers on Subnet2.
Which two settings should you configure? (Each correct answer presents part of the solution. Choose two.)
- A. The NAP-Capable Computers conditions
- B. The NAS Port Type constraints
- C. The Health Policies conditions
- D. The MS-Service Class conditions
- E. The Called Station ID constraints
Answer: CD
Explanation: The NAP health policy server uses the NPS role service with configured health policies and system health validators (SHVs) to evaluate client health based on administrator-defined requirements. Based on results of this evaluation, NPS instructs the DHCP server to provide full access to compliant NAP client computers and to restrict access to client computers that are noncompliant with health requirements.
If policies are filtered by DHCP scope, then MS-Service Class is configured in policy conditions.
NEW QUESTION 14
Your network contains an Active Directory domain named contoso.com. All servers run Windows Server 2012 R2. The domain contains two servers. The servers are configured as shown in the following table.
All client computers run Windows 8 Enterprise.
You plan to deploy Network Access Protection (NAP) by using IPSec enforcement.
A Group Policy object (GPO) named GPO1 is configured to deploy a trusted server group to all of the client computers.
You need to ensure that the client computers can discover HRA servers automatically. Which three actions should you perform? (Each correct answer presents part of the
solution. Choose three.)
- A. On all of the client computers, configure the EnableDiscovery registry key.
- B. In a GPO, modify the Request Policy setting for the NAP Client Configuration.
- C. On Server2, configure the EnableDiscovery registry key.
- D. On DC1, create an alias (CNAME) record.
- E. On DC1, create a service location (SRV) record.
Answer: ABE
Explanation: Requirements for HRA automatic discovery
The following requirements must be met in order to configure trusted server groups on NAP client computers using HRA automatic discovery:
Client computers must be running Windows Vista® with Service Pack 1 (SP1) or Windows XP with Service Pack 3 (SP3).
The HRA server must be configured with a Secure Sockets Layer (SSL) certificate. The EnableDiscovery registry key must be configured on NAP client computers. DNS SRV records must be configured.
The trusted server group configuration in either local policy or Group Policy must be cleared.
http: //technet. microsoft. com/en-us/library/dd296901. aspx
NEW QUESTION 15
DRAG DROP
Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2. All servers run Windows Server 2012 R2.
You generalize Server2.
You install the Windows Deployment Services (WDS) server role on Server1. You need to capture an image of Server2 on Server1.
Which three actions should you perform?
To answer, move the three appropriate actions from the list of actions to the answer area and arrange them in the correct order.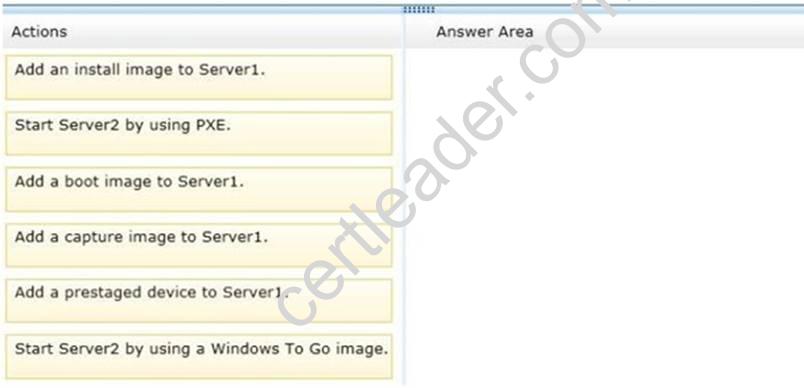
Answer:
Explanation: Box 1: Start Server2 by using PXE. Box 2: Add a capture image to Server1. Box 3: Add an install image to Server1. Note:
* Capture images are Windows Preinstallation Environment (Windows PE) images that allow you to easily capture the install images that you prepare using Sysprep.exe. Instead of using complex command-line tools, once you have run Sysprep.exe on your reference computer, you can boot to the Windows Deployment Services client computer using PXE and select the capture image. When the capture image boots, it starts the Capture Image Wizard, which will guide you through the capture process and optionally upload the new install image to a Windows Deployment Services server.
Steps
/ create a capture image.
/ Create an install image.
/ Add the install image to the Windows Deployment Services server.
NEW QUESTION 16
You have a server named Server1 that runs Windows Server 2012 R2. Server1 has the File Server Resource Manager role service installed.
Each time a user receives an access-denied message after attempting to access a folder on Server1, an email notification is sent to a distribution list named DLL.
You create a folder named Folder1 on Server1, and then you configure custom NTFS permissions for Folder1.
You need to ensure that when a user receives an access-denied message while attempting to access Folder1, an email notification is sent to a distribution list named DL2. The solution must not prevent DL1 from receiving notifications about other access-denied messages.
What should you do?
- A. From the File Server Resource Manager console, create a local classification property.
- B. From Server Manager, run the New Share Wizard to create a share for Folder1 by selecting the SMB Share - Applications option.
- C. From the File Server Resource Manager console, modify the Access-Denied Assistance settings.
- D. From the File Server Resource Manager console, set a folder management property.
Answer: D
NEW QUESTION 17
Your network contains one Active Directory domain named contoso.com. The forest functional level is Windows Server 2012. All servers run Windows Server 2012 R2. All client computers run Windows 8.1.
The domain contains 10 domain controllers and a read-only domain controller (RODC) named RODC01. All domain controllers and RODCs are hosted on a Hyper-V host that
runs Windows Server 2012 R2.
You need to identify whether deleted objects can be recovered from the Active Directory Recycle Bin.
Which cmdlet should you use?
- A. Get-ADGroupMember
- B. Get-ADDomainControllerPasswordReplicationPolicy
- C. Get-ADDomainControllerPasswordReplicationPolicyUsage
- D. Get-ADDomain
- E. Get-ADOptionalFeature
- F. Get-ADAccountAuthorizationGroup
Answer: E
Explanation: The Get-ADOptionalFeature cmdlet gets an optional feature or performs a search to retrieve multiple optional features from an Active Directory.
Example: Get-ADOptionalFeature 'Recycle Bin Feature'
Get the optional feature with the name 'Recycle Bin Feature'.
Reference: Get-ADOptionalFeature https://technet.microsoft.com/en-us/library/ee617218.aspx
NEW QUESTION 18
You have a server named Server1 that runs Windows Server 2012 R2. Server1 has the Windows Deployment Services server role installed.
Server1 contains two boot images and four install images.
You need to ensure that when a computer starts from PXE, the available operating system images appear in a specific order.
What should you do?
- A. Modify the properties of the boot images.
- B. Create a new image group.
- C. Modify the properties of the install images.
- D. Modify the PXE Response Policy.
Answer: C
NEW QUESTION 19
Your network is configured as shown in the exhibit. (Click the Exhibit button.)
Server1 regularly accesses Server2.
You discover that all of the connections from Server1 to Server2 are routed through Routerl.
You need to optimize the connection path from Server1 to Server2. Which route command should you run on Server1?
- A. Route add -p 192.168.2.0 MASK 255.255.255.0 192.168.2.1 METRIC 50
- B. Route add -p 192.168.2.12 MASK 255.255.255.0 192.168.2.1 METRIC 100
- C. Route add -p 192.168.2.12 MASK 255.255.255.0 192.168.2.0 METRIC 50
- D. Route add -p 192.168.2.0 MASK 255.255.255.0 192.168.1.2 METRIC 100
Answer: D
NEW QUESTION 20
Your network contains two Active Directory forests named adatum.com and contoso.com. The network contains three servers. The servers are configured as shown in the following table.
You need to ensure that connection requests from adatum.com users are forwarded to Server2 and connection requests from contoso.com users are forwarded to Server3.
Which two should you configure in the connection request policies on Server1? (Each correct answer presents part of the solution. Choose two.)
- A. The Authentication settings
- B. The Standard RADIUS Attributes settings
- C. The Location Groups condition
- D. The Identity Type condition
- E. The User Name condition
Answer: AE
Explanation: The User Name attribute group contains the User Name attribute. By using this attribute, you can designate the user name, or a portion of the user name, that must match the user name supplied by the access client in the RADIUS message. This attribute is a character string that typically contains a realm name and a user account name. You can use pattern- matching syntax to specify user names.
By using this setting, you can override the authentication settings that are configured in all network policies and you can designate the authentication methods and types that are required to connect to your network.
Forward requests to the following remote RADIUS server group . By using this setting, NPS forwards connection requests to the remote RADIUS server group that you specify. If the NPS server receives a valid Access-Accept message that corresponds to the Access- Request message, the connection attempt is considered authenticated and authorized. In this case, the NPS server acts as a RADIUS proxy
Connection request policies are sets of conditions and profile settings that give network administrators flexibility in configuring how incoming authentication and accounting request messages are handled by the IAS server. With connection request policies, you can create a series of policies so that some RADIUS request messages sent from RADIUS clients are processed locally (IAS is being used as a RADIUS server) and other types of messages are forwarded to another RADIUS server (IAS is being used as a RADIUS proxy). This capability allows IAS to be deployed in many new RADIUS scenarios.
With connection request policies, you can use IAS as a RADIUS server or as a RADIUS proxy, based on the time of day and day of the week, by the realm name in the request, by the type of connection being requested, by the IP address of the RADIUS client, and so on.
References:
http: //technet. microsoft. com/en-us/library/cc757328. aspx
http: //technet. microsoft. com/en-us/library/cc753603. aspx
Thanks for reading the newest 70-411 exam dumps! We recommend you to try the PREMIUM 2passeasy 70-411 dumps in VCE and PDF here: https://www.2passeasy.com/dumps/70-411/ (294 Q&As Dumps)