Breathing 70-411 Braindumps 2021
It is impossible to pass Microsoft 70-411 exam without any help in the short term. Come to us soon and find the most advanced, correct and guaranteed 70 411 exam dumps pdf. You will get a surprising result by our 70 411 administering windows server 2012 r2 pdf.
Also have 70-411 free dumps questions for you:
NEW QUESTION 1
Your network contains one Active Directory domain. The domain contains a DirectAcess deployment.
You need to ensure that when the DirectAccess connection is active, the connection appears as "Contoso Internal Network -Authorized Users Only" on the DirectAccess clents.
What should you configure in the DirectAccess client Group Policy object (GPO)?
- A. Friendly Name
- B. Corporate Resources
- C. User Interface
- D. Prefer Local Names Allowed
Answer: A
NEW QUESTION 2
You have a server named Server1 that runs Windows Server 2012 R2.
On Server1, you configure a custom Data Collector Set (DCS) named DCS1. DCS1 is configured to store performance log data in C:Logs.
You need to ensure that the contents of C:Logs are deleted automatically when the folder reaches 100 MB in size.
What should you configure?
- A. A File Server Resource Manager (FSRM) file screen on the C:Logs folder
- B. The Data Manager settings of DCS1
- C. A schedule for DCS1
- D. A File Server Resource Manager (FSRM) quota on the C:Logs folder
Answer: B
Explanation: To configure data management for a Data Collector Set
1. In Windows Performance Monitor, expand Data Collector Sets and click User Defined.
2. In the console pane, right-click the name of the Data Collector Set that you want to configure and click Data Manager.
3. On the Data Manager tab, you can accept the default values or make changes according to your data retention policy. See the table below for details on each option.
When Minimum free disk or Maximum folders is selected, previous data will be deleted according to the Resource policy you choose (Delete largest or Delete oldest) when the limit is reached. When Apply policy before the data collector set starts is selected, previous data will be deleted according to your selections before the data collector set creates its next log file.
When Maximum root path size is selected, previous data will be deleted according to your selections when the root log folder size limit is reached.
4. Click the Actions tab. You can accept the default values or make changes. See the table below for details on each option.
5. When you have finished making your changes, click OK.
NEW QUESTION 3
Your network contains an Active Directory domain named contoso.com. The domain contains a server named NPS1 that has the Network Policy Server server role installed. All servers run Windows Server 2012 R2.
You install the Remote Access server role on 10 servers.
You need to ensure that all of the Remote Access servers use the same network policies.
Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
- A. Configure each Remote Access server to use the Routing and Remote Access service (RRAS) to authenticate connection requests.
- B. On NPS1, create a remote RADIUS server grou
- C. Add all of the Remote Access servers to the remote RADIUS server group.
- D. On NPS1, create a new connection request policy and add a Tunnel-Type and a Service-Type condition.
- E. Configure each Remote Access server to use a RADIUS server named NPS1.
- F. On NPS1, create a RADIUS client template and use the template to create RADIUS clients.
Answer: CD
Explanation: Connection request policies are sets of conditions and settings that allow network administrators to designate which RADIUS servers perform the authentication and authorization of connection requests that the server running Network Policy Server (NPS) receives from RADIUS clients. Connection request policies can be configured to designate which RADIUS servers are used for RADIUS accounting.
When you configure Network Policy Server (NPS) as a Remote Authentication Dial-In User Service (RADIUS) proxy, you use NPS to forward connection requests to RADIUS servers that are capable of processing the connection requests because they can perform authentication and authorization in the domain where the user or computer account is located. For example, if you want to forward connection requests to one or more RADIUS servers in untrusted domains, you can configure NPS as a RADIUS proxy to forward the requests to the remote RADIUS servers in the untrusted domain.
To configure NPS as a RADIUS proxy, you must create a connection request policy that contains all of the information required for NPS to evaluate which messages to forward and where to send the messages.
Reference: http://technet.microsoft.com/en-us/library/cc730866(v=ws.10).aspx
NEW QUESTION 4
CORRECT TEXT
You have a server named Server1 that is a number of a domain named contoso.com. You view the properties of a service on Server1 as shown in the graphic.
Use the drop-down menus to select the answer choice that completes each statement. NOTE: Each correct selection is worth one point.
Answer:
Explanation: 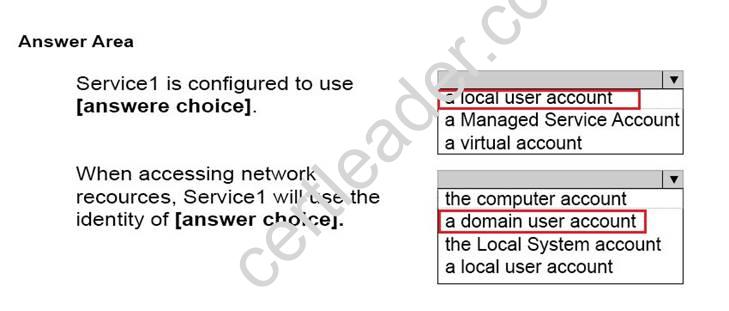
References:
https://msdn.microsoft.com/en-us/library/ms677272(v=vs.85).aspx https://msdn.microsoft.com/en-us/library/ms675915(v=vs.85).aspx
Virtual accounts are "managed local accounts" that provide the following features to simplify service administration:
- No password management is required.
- The ability to access the network with a computer identity in a domain environment.
Virtual accounts require very little management. They cannot be created or deleted, nor do they require any password management.
You must be a member of the Administrators group on the local computer to perform the following procedures. To configure a service to use a virtual account:
- Click Start, point to Administrative Tools, and then click Services.
- In the details pane, right-click the service that you want to configure, and then click Properties.
- Click the Log On tab, click This account, and then type NT SERVICEServiceName.
When you are finished, click OK.
- Restart the service for the change to take effect. https://technet.microsoft.com/en-us/library/dd548356%20(v=WS.10).aspx
NEW QUESTION 5
Your network contains an Active Directory domain named adatum.com. You have a standard primary zone named adatum.com.
You need to provide a user named User1 the ability to modify records in the zone. Other users must be prevented from modifying records in the zone.
What should you do first?
- A. Run the Zone Signing Wizard for the zone.
- B. From the properties of the zone, modify the start of authority (SOA) record.
- C. From the properties of the zone, change the zone type.
- D. Run the New Delegation Wizard for the zone.
Answer: C
Explanation: The Zone would need to be changed to a AD integrated zone When you use directory- integrated zones, you can use access control list (ACL) editing to secure a dnsZone object container in the directory tree. This feature provides detailed access to either the zone or a specified resource record in the zone. For example, an ACL for a zone resource record can be restricted so that dynamic updates are allowed only for a specified client computer or a secure group, such as a domain administrators group. This security feature is not available with standard primary zones.
DNS update security is available only for zones that are integrated into Active Directory. After you integrate a zone, you can use the access control list (ACL) editing features that are available in the DNS snap-in to add or to remove users or groups from the ACL for a specific zone or for a resource record.
Standard (not an Active Directory integrated zone) has no Security settings:
You need to firstly change the "Standard Primary Zone" to AD Integrated Zone:
Now there's Security tab:
References:
http: //technet. microsoft. com/en-us/library/cc753014. aspx http: //technet. microsoft. com/en-us/library/cc726034. aspx http: //support. microsoft. com/kb/816101
NEW QUESTION 6
Your network contains an Active Directory domain named contoso.com. All domain controllers run Windows Server 2012 R2. You plan to use fine-grained password policies to customize the password policy settings ofcontoso.com.
You need to identify to which Active Directory object types you can directly apply the fine- grained password policies.
Which two object types should you identify? (Each correct answer presents part of the solution. Choose two.)
- A. Users
- B. Global groups
- C. computers
- D. Universal groups
- E. Domain local groups
Answer: AB
Explanation: First off, your domain functional level must be at Windows Server 2008. Second, Fine- grained password policies ONLY apply to user objects, and global security groups. Linking them to universal or domain local groups is ineffective. I know what you’re thinking, what about OU’s? Nope, Fine-grained password policy cannot be applied to an organizational unit (OU) directly. The third thing to keep in mind is, by default only members of the Domain Admins group can set fine-grained password policies. However, you can delegate this ability to other users if needed.
Fine-grained password policies apply only to user objects (or inetOrgPerson objects if they are used instead of user objects) and global security groups.
You can apply Password Settings objects (PSOs) to users or global security groups: References:
http: //technet. microsoft. com/en-us/library/cc731589%28v=ws. 10%29. aspx
http: //technet. microsoft. com/en-us/library/cc731589%28v=ws. 10%29. aspx http: //technet. microsoft. com/en-us/library/cc770848%28v=ws. 10%29. aspx
http: //www. brandonlawson. com/active-directory/creating-fine-grained-password-policies/
NEW QUESTION 7
HOTSPOT
Your network contains 25 Web servers that run Windows Server 2012 R2. You need to configure auditing policies that meet the following requirements:
✑ Generate an event each time a new process is created.
✑ Generate an event each time a user attempts to access a file share.
Which two auditing policies should you configure? To answer, select the appropriate two auditing policies in the answer area.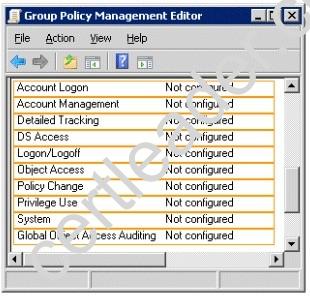
Answer:
Explanation: 
NEW QUESTION 8
You have a server named Server1 that runs Windows Server 2012 R2. You create a Data Collector Set (DCS) named DCS1.
You need to configure DCS1 to log data to D:logs.
What should you do?
- A. Right-click DCS1 and click Properties.
- B. Right-click DCS1 and click Export list.
- C. Right-click DCS1 and click Data Manager.
- D. Right-click DCS1 and click Save template.
Answer: A
Explanation: The Root Directory will contain data collected by the Data Collector Set. Change this setting if you want to store your Data Collector Set data in a different location than the default. Browse to and select the directory, or type the directory name.
To view or modify the properties of a Data Collector Set after it has been created, you can:
* Select the Open properties for this data collector set check box at the end of the Data Collector Set Creation Wizard.
* Right-click the name of a Data Collector Set, either in the MMC scope tree or in the console window, and click Properties in the context menu.
Directory tab:
In addition to defining a root directory for storing Data Collector Set data, you can specify a single Subdirectory or create a Subdirectory name format by clicking the arrow to the right of the text entry field.
NEW QUESTION 9
You have a server named Server1 that runs Windows Server 2012 R2. Server1 has the Remote Access server role installed.
On Server1, you create a network policy named Policy1.
You need to configure Policy1 to ensure that users are added to a VLAN. Which attributes should you add to Policy1?
- A. Tunnel-Tag, Tunnel-Password, Tunnel-Medium-Type, and Tunnel-Preference
- B. Tunnel-Tag, Tunnel-Server-Auth-ID, Tunnel-Preference, and Tunnel-Pvt-Group-ID
- C. Tunnel-Type, Tunnel-Tag, Tunnel-Medium-Type, and Tunnel-Pvt-Group-ID
- D. Tunnel-Type, Tunnel-Password, Tunnel-Server-Auth-ID, and Tunnel-Pvt-Group-ID
Answer: C
Explanation: VLAN attributes used in network policy
When you use network hardware, such as routers, switches, and access controllers that support virtual local area networks (VLANs), you can configure Network Policy Server (NPS) network policy to instruct the access servers to place members of Active Directory® groups on VLANs.
Before configuring network policy in NPS for VLANs, create groups of users in Active Directory Domain Services (AD DS) that you want to assign to specific VLANs. Then when you run the New Network Policy wizard, add the Active Directory group as a condition of the network policy.
You can create a separate network policy for each group that you want to assign to a VLAN. For more information, see Create a Group for a Network Policy. When you configure network policy for use with VLANs, you must configure the RADIUS standard attributes Tunnel-Medium-Type, Tunnel-Pvt-Group-ID, and Tunnel-Type. Some hardware vendors also require the use of the RADIUS standard attribute Tunnel-Tag.
To configure these attributes in a network policy, use the New Network Policy wizard to create a network policy. You can add the attributes to the network policy settings while running the wizard or after you have successfully created a policy with the wizard.
✑ Tunnel-Medium-Type. Select a value appropriate to the previous selections you
made while running the New Network Policy wizard. For example, if the network policy you are configuring is a wireless policy, in Attribute Value, select 802 (Includes all 802 media plus Ethernet canonical format).
✑ Tunnel-Pvt-Group-ID. Enter the integer that represents the VLAN number to which
group members will be assigned. For example, if you want to create a Sales VLAN for your sales team by assigning team members to VLAN 4, type the number 4.
✑ Tunnel-Type. Select the value Virtual LANs (VLAN).
✑ Tunnel-Tag. Some hardware devices do not require this attribute. If your hardware device requires this attribute, obtain this value from your hardware documentation.
NEW QUESTION 10
Your network contains two servers named Server1 and Server2. Both servers run Windows Server 2012 R2 and have the DNS Server server role installed.
On Server1, you create a standard primary zone named contoso.com.
You need to ensure that Server2 can host a secondary zone for contoso.com. What should you do from Server1?
- A. Add Server2 as a name server.
- B. Create a trust anchor named Server2.
- C. Convert contoso.com to an Active Directory-integrated zone.
- D. Create a zone delegation that points to Server2.
Answer: A
Explanation: Typically, adding a secondary DNS server to a zone involves three steps:
1. On the primary DNS server, add the prospective secondary DNS server to the list of name servers that are authoritative for the zone.
2. On the primary DNS server, verify that the transfer settings for the zone permit the zone to be transferred to the prospective secondary DNS server.
3. On the prospective secondary DNS server, add the zone as a secondary zone.
You must add a new Name Server. To add a name server to the list of authoritative servers for the zone, you must specify both the server's IP address and its DNS name. When entering names, click Resolve to resolve the name to its IP address prior to adding it to the list.
Secondary zones cannot be AD-integrated under any circumstances.
You want to be sure Server2 can host, you do not want to delegate a zone.
Secondary Domain Name System (DNS) servers help provide load balancing and fault tolerance. Secondary DNS servers maintain a read-only copy of zone data that is transferred periodically from the primary DNS server for the zone. You can configure DNS clients to query secondary DNS servers instead of (or in addition to) the primary DNS server for a zone, reducing demand on the primary server and ensuring that DNS queries for the zone will be answered even if the primary server is not available.
How-To: Configure a secondary DNS Server in Windows Server 2012
We need to tell our primary DNS that it is ok for this secondary DNS to pull information from it. Otherwise replication will fail and you will get this big red X.
Head over to your primary DNS server, launch DNS manager, expand Forward Lookup Zones, navigate to your primary DNS zone, right-click on it and go to Properties.
Go to “Zone Transfers” tab, by default, for security reasons, the “Allow zone transfers: ” is un-checked to protect your DNS information. We need to allow zone transfers, if you value your DNS records, you do not want to select “To any server” but make sure you click on “Only to servers listed on the Name Servers tab”.
Head over to the “Name Servers” tab, click Add.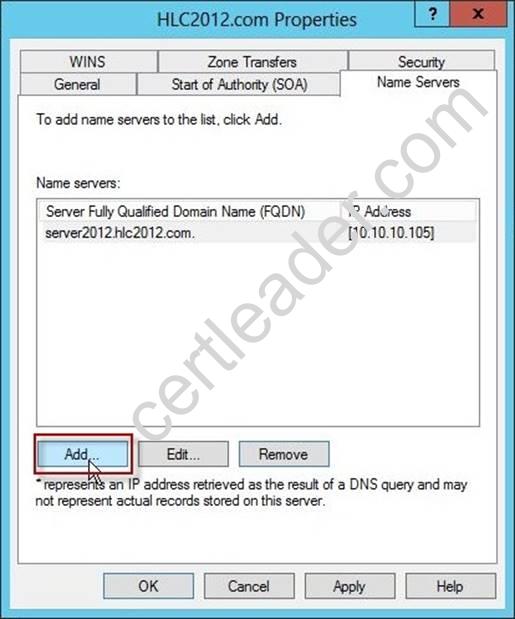
You will get “New Name Server Record” window, type in the name of your secondary DNS server. it is always better to validate by name not IP address to avoid future problems in case your IP addresses change. Once done, click OK.
You will see your secondary DNS server is now added to your name servers selection, click OK.
Now if you head back to your secondary DNS server and refresh, the big red X will go away and your primary zone data will populate.
Your secondary DNS is fully setup now. You cannot make any DNS changes from your secondary DNS. Secondary DNS is a read-only DNS, Any DNS changes have to be done from the primary DNS.
References:
http: //technet. microsoft. com/en-us/library/cc816885%28v=ws. 10%29. aspx
http: //technet. microsoft. com/en-us/library/cc816814%28v=ws. 10%29. aspx
http: //blog. hyperexpert. com/how-to-configure-a-secondary-dns-server-in-windows-server- 2012/
http: //technet. microsoft. com/en-us/library/cc770984. aspx
http: //support. microsoft. com/kb/816101
http: //technet. microsoft. com/en-us/library/cc753500. aspx
http: //technet. microsoft. com/en-us/library/cc771640(v=ws. 10). aspx
http: //technet.microsoft.com/en-us/library/ee649280(v=ws. 10). aspx
NEW QUESTION 11
Your network contains an Active Directory domain named contoso.com. The domain contains a read-only domain controller (RODC) named R0DC1.
You create a global group named RODC_Admins.
You need to provide the members of RODC_Admins with the ability to manage the
hardware and the software on R0DC1. The solution must not provide RODC_Admins with the ability to manage Active Directory objects.
What should you do?
- A. From Active Directory Sites and Services, run the Delegation of Control Wizard.
- B. From a command prompt, run the dsadd computer command.
- C. From Active Directory Site and Services, configure the Security settings of the R0DC1 server object.
- D. From a command prompt, run the dsmgmt local roles command.
Answer: D
Explanation: RODC: using the dsmgmt.exe utility to manage local administrators
One of the benefits of RODC is that you can add local administrators who do not have full access to the domain administration. This gives them the ability to manage the server but not add or change active directory objects unless those roles are delegated. Adding this type of user is done using the dsmdmt.exe utility at the command prompt.
NEW QUESTION 12
Your network contains one Active Directory domain named contoso.com. The forest functional level is Windows Server 2012. All servers run Windows Server 2012 R2. All client computers run Windows 8.1.
The domain contains 10 domain controllers and a read-only domain controller (RODC) named RODC01. All domain controllers and RODCs are hosted on a Hyper-V host that runs Windows Server 2012 R2.
You need to identify whether the members of the Protected Users group will be prevented from authenticating by using NTLM.
Which cmdlet should you use?
- A. Get-ADGroupMember
- B. Get-ADDomainControllerPasswordReplicationPolicy
- C. Get-ADDomainControllerPasswordReplicationPolicyUsage
- D. Get-ADDomain
- E. Get-ADOptionalFeature
- F. Get-ADAccountAuthorizationGroup
- G. Get-ADAuthenticationPolicySilo
- H. Get-ADAuthenticatonPolicy
Answer: D
Explanation: If the domain functional level is Windows Server 2012 R2, members of the (Protected Users) group can no longer authenticate by using NTLM authentication. So we need to check the domain functional level with Get-ADDomain. https://technet.microsoft.com/en-us/library/Dn518179.aspx
NEW QUESTION 13
Your network contains two Active Directory domains named contoso.com and adatum.com.
The network contains a server named Server1 that runs Windows Server 2012 R2. Server1 has the DNS Server server role installed. Server1 has a copy of the contoso.com DNS zone.
You need to configure Server1 to resolve names in the adatum.com domain. The solution must meet the following requirements:
Prevent the need to change the configuration of the current name servers that host zones for adatum.com. Minimize administrative effort.
Which type of zone should you create?
- A. Secondary
- B. Stub
- C. Reverse lookup
- D. Primary
Answer: B
Explanation: When a zone that this DNS server hosts is a stub zone, this DNS server is a source only for information about the authoritative name servers for this zone. The zone at this server must be obtained from another DNS server that hosts the zone. This DNS server must have network access to the remote DNS server to copy the authoritative name server information about the zone.
A stub zone is a copy of a zone that contains only necessary resource records (Start of Authority (SOA), Name Server (NS), and Address/Host (A) record) in the master zone and acts as a pointer to the authoritative name server. The stub zone allows the server to forward queries to the name server that is authoritative for the master zone without going up to the root name servers and working its way down to the server. While a stub zone can improve performance, it does not provide redundancy or load sharing.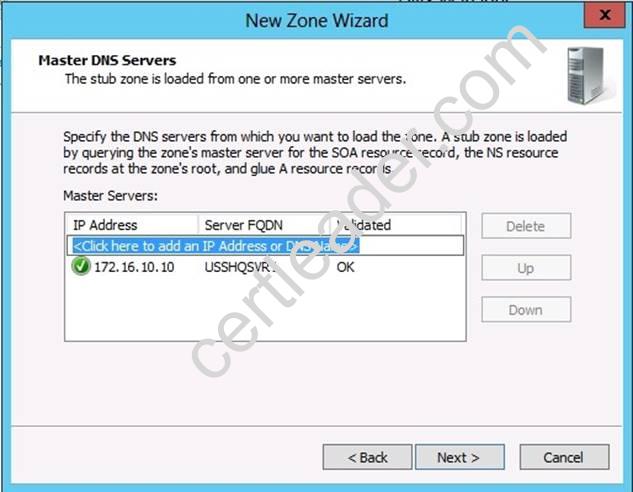
You can use stub zones to:
Keep delegated zone information current. By updating a stub zone for one of its child zones regularly, the DNS server that hosts both the parent zone and the stub zone will maintain a current list of authoritative DNS servers for the child zone.
Improve name resolution. Stub zones enable a DNS server to perform recursion using the stub zone's list of name servers, without having to query the Internet or an internal root server for the DNS namespace.
Simplify DNS administration. By using stub zones throughout your DNS infrastructure, you can distribute a list of the authoritative DNS servers for a zone without using secondary zones. However, stub zones do not serve the same purpose as secondary zones, and they are not an alternative for enhancing redundancy and load sharing.
There are two lists of DNS servers involved in the loading and maintenance of a stub zone: The list of master servers from which the DNS server loads and updates a stub zone. A master server may be a primary or secondary DNS server for the zone. In both cases, it will have a complete list of the DNS servers for the zone.
The list of the authoritative DNS servers for a zone. This list is contained in the stub zone using name server (NS) resource records.
When a DNS server loads a stub zone, such as widgets. tailspintoys.com, it queries the master servers, which can be in different locations, for the necessary resource records of the authoritative servers for the zone widgets. tailspintoys.com. The list of master servers may contain a single server or multiple servers, and it can be changed anytime.
References:
http: //technet.microsoft.com/en-us/library/cc771898.aspx http: //technet.microsoft.com/en-us/library/cc754190.aspx http: //technet.microsoft.com/en-us/library/cc730980.aspx
NEW QUESTION 14
Your network contains an Active Directory domain named adatum.com. A network administrator creates a Group Policy central store.
After the central store is created, you discover that when you create new Group Policy objects (GPOs), the GPOs do not contain any Administrative Templates.
You need to ensure that the Administrative Templates appear in new GPOs.
What should you do?
- A. Add your user account to the Group Policy Creator Owners group.
- B. Configure all domain controllers as global catalog servers.
- C. Copy files from %Windir%Policydefinitions to the central store.
- D. Modify the Delegation settings of the new GPOs.
Answer: C
Explanation: To take advantage of the benefits of .admx files, you must create a Central Store in the SYSVOL folder on a domain controller. The Central Store is a file location that is checked by the Group Policy tools. The Group Policy tools use any .admx files that are in the Central Store. The files that are in the Central Store are later replicated to all domain controllers in the domain.
NEW QUESTION 15
You have a Windows Server Update Services (WSUS) server named Server1.. Server1 synchronizes from Microsoft Update.
You plan to deploy a new WSUS server named Server2. Server2 will synchronize updates from Server1. Server2 will be separated from Server1 by a firewall.
You need to identify which port must be open on the firewall so that Server2 can synchronize the updates.
Which port should you identify?
- A. 8530
- B. 3389
- C. 443
- D. 80
Answer: A
Explanation: WSUS upstream and downstream servers will synchronize on the port configured by the WSUS Administrator. By default, these ports are configured as follows: On WSUS 3.2 and earlier, port 80 for HTTP and 443 for HTTPS
On WSUS 6.2 and later (at least Windows Server 2012), port 8530 for HTTP and 8531 for HTTPS
The firewall on the WSUS server must be configured to allow inbound traffic on these ports. https://technet.microsoft.com/en-us/library/hh852346.aspx
NEW QUESTION 16
Your network contains an Active Directory domain named contoso.com. All domain controllers run Windows Server 2012 R2. One of the domain controllers is named DC1.
The DNS zone for the contoso.com zone is Active Directory-integrated and has the default settings.
A server named Server1 is a DNS server that runs a UNIX-based operating system. You plan to use Server1 as a secondary DNS server for the contoso.com zone.
You need to ensure that Server1 can host a secondary copy of the contoso.com zone. What should you do?
- A. From DNS Manager, modify the Advanced settings of DC1.
- B. From DNS Manager, modify the Zone Transfers settings of the contoso.com zone.
- C. From Windows PowerShell, run the Set-DnsServerForwardercmdlet and specify the contoso.com zone as a target.
- D. From DNS Manager, modify the Security settings of DC1.
Answer: C
Explanation: There are two ways that a secondary DNS server can be added. In both scenarios you will need to add the new server to the Forwarders list of the primary Domain Controller.
1. The Set-DnsServerForwarder cmdlet changes forwarder settings on a Domain Name System (DNS) server.
2. From the primary server, open DNS Manager, right click on the server name and select Properties. Click on the Forwarders tab and click the Edit button in the middle of the dialogue box.
NEW QUESTION 17
Your network contains one Active Directory domain named contoso.com. The forest functional level is Windows Server 2012. All servers run Windows Server 2012 R2. All client computers run Windows 8.1.
The domain contains 10 domain controllers and a read-only domain controller (RODC) named RODC01. All domain controllers and RODCs are hosted on a Hyper-V host that runs Windows Server 2012 R2.
You need to identify which user accounts were authenticated by RODC1. Which cmdlet should you use?
- A. Get-ADGroupMember
- B. Get-ADDomainControllerPasswordReplicationPolicy
- C. Get-ADDomainControllerPasswordReplicationPolicyUsage
- D. Get-ADDomain
- E. Get-ADOptionalFeature
- F. Get-ADAccountAuthorizationGroup
Answer: B
Explanation: Gets the Active Directory accounts that are authenticated by a read-only domain controller or that are in the revealed list of the domain controller.
Reference: Get-ADDomainControllerPasswordReplicationPolicyUsage https://technet.microsoft.com/en-us/library/ee617194.aspx
NEW QUESTION 18
Your network contains an Active Directory domain named contoso.com. You create a new user account named Admin5.
You need to ensure that Admin5 can create Group Policy objects (GPOs) and link the GPOs to all of the organizational units (OUs) in the domain. Admin5 must be prevented from modifying GPOs created by other administrators.
Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
- A. From Active Directory Users and Computers, modify the members of the Network Configuration Operators group.
- B. From Active Directory Users and Computers, modify the Security settings of the Admin5 user account.
- C. From Group Policy Management, click the Group Policy Objects node and modify the Delegation settings.
- D. From Group Policy Management, click the contoso.com node and modify the Delegationsettings.
- E. From Active Directory Users and Computers, modify the members of the Group Policy Creator Owners group.
Answer: CD
NEW QUESTION 19
Your network contains two Active Directory forests named contoso.com and adatum.com. The contoso.com forest contains a server named Server1.contoso.com. The adatum.com forest contains a server named server2. adatum.com. Both servers have the Network Policy Server role service installed.
The network contains a server named Server3. Server3 is located in the perimeter network and has the Network Policy Server role service installed.
You plan to configure Server3 as an authentication provider for several VPN servers. You need to ensure that RADIUS requests received by Server3 for a specific VPN server
are always forwarded to Server1.contoso.com.
Which two should you configure on Server3? (Each correct answer presents part of the solution. Choose two.)
- A. Remediation server groups
- B. Remote RADIUS server groups
- C. Connection request policies
- D. Network policies
- E. Connection authorization policies
Answer: BC
Explanation: To configure NPS as a RADIUS proxy, you must create a connection request policy that contains all of the information required for NPS to evaluate which messages to forward and where to send the messages.
When you configure Network Policy Server (NPS) as a Remote Authentication Dial-In User Service (RADIUS) proxy, you use NPS to forward connection requests to RADIUS servers that are capable of processing the connection requests because they can perform authentication and authorization in the domain where the user or computer account is located. For example, if you want to forward connection requests to one or more RADIUS servers in untrusted domains, you can configure NPS as a RADIUS proxy to forward the requests to the remote RADIUS servers in the untrusted domain. To configure NPS as a RADIUS proxy, you must create a connection request policy that contains all of the information required for NPS to evaluate which messages to forward and where to send the messages.
When you configure a remote RADIUS server group in NPS and you configure a connection request policy with the group, you are designating the location where NPS is to forward connection requests.
References:
http: //technet. microsoft. com/en-us/library/cc754518. aspx
http: //technet. microsoft. com/en-us/library/cc754518. aspx
http: //technet. microsoft. com/en-us/library/cc754518. aspx
NEW QUESTION 20
Your network contains an Active Directory domain named contoso.com. The domain contains six domain controllers. The domain controllers are configured as shown in the following table.
The network contains a server named Server1 that has the Hyper-V server role installed. DC6 is a virtual machine that is hosted on Server1.
You need to ensure that you can clone DC6. What should you do?
- A. Transfer the schema master to DC6.
- B. Transfer the PDC emulator to DC5.
- C. Transfer the schema master to DC4.
- D. Transfer the PDC emulator to DC2.
Answer: D
Explanation: A deployed Windows Server 2012 domain controller (virtualized or physical) that hosts the PDC emulator role (DC1). To verify whether the PDC emulator role is hosted on a Windows Server 2012 domain controller, run the following Windows PowerShell command:
Get-ADComputer (Get-ADDomainController –Discover –Service "PrimaryDC").name
–Propertyoperatingsystemversion|fl
Reference: http: //technet. microsoft. com/en-us/library/hh831734. aspx#steps_deploy_vdc
Thanks for reading the newest 70-411 exam dumps! We recommend you to try the PREMIUM Certleader 70-411 dumps in VCE and PDF here: https://www.certleader.com/70-411-dumps.html (294 Q&As Dumps)