All About 100% Correct SY0-701 Exam Prep
Master the SY0-701 CompTIA Security+ Exam content and be ready for exam day success quickly with this Exambible SY0-701 rapidshare. We guarantee it!We make it a reality and give you real SY0-701 questions in our CompTIA SY0-701 braindumps.Latest 100% VALID CompTIA SY0-701 Exam Questions Dumps at below page. You can use our CompTIA SY0-701 braindumps and pass your exam.
Online SY0-701 free questions and answers of New Version:
NEW QUESTION 1
A security analyst receives an alert that indicates a user's device is displaying anomalous behavior The analyst suspects the device might be compromised Which of the following should the analyst to first?
- A. Reboot the device
- B. Set the host-based firewall to deny an incoming connection
- C. Update the antivirus definitions on the device
- D. Isolate the device
Answer: D
Explanation:
Isolating the device is the first thing that a security analyst should do if they suspect that a user’s device might be compromised. Isolating the device means disconnecting it from the network or placing it in a separate network segment to prevent further communication with potential attackers or malicious hosts. Isolating the device can help contain the incident, limit the damage or data loss, preserve the evidence, and facilitate the investigation and remediation.
References: https://www.comptia.org/certifications/security#examdetails https://www.comptia.org/content/guides/comptia-security-sy0-601-exam-objectives https://resources.infosecinstitute.com/topic/incident-response-process/
NEW QUESTION 2
A local server recently crashed, and the team is attempting to restore the server from a backup. During the restore process, the team notices the file size of each daily backup is large and will run out of space at the current rate.
The current solution appears to do a full backup every night. Which of the following would use the least amount of storage space for backups?
- A. A weekly, incremental backup with daily differential backups
- B. A weekly, full backup with daily snapshot backups
- C. A weekly, full backup with daily differential backups
- D. A weekly, full backup with daily incremental backups
Answer: D
Explanation:
A weekly, full backup with daily incremental backups would use the least amount of storage space for backups, as it would only store the changes made since the last backup, whether it is a full or incremental backup. Incremental backups are faster and use less storage space than full or differential backups, but they require more time and media to restore data. A full backup is a complete copy of all data, which requires more time and storage space to perform, but allows a faster and easier recovery. A differential backup is a copy of the data that changed since the last full backup, which requires less time and storage space than a full backup, but more than an incremental backup. A differential backup allows a faster recovery than an incremental backup, but slower than a full backup. References: https://www.nakivo.com/blog/backup-types-explained/
https://www.nakivo.com/blog/backup-types-explained/
NEW QUESTION 3
A security analyst is currently addressing an active cyber incident. The analyst has been able to identify affected devices that are running a malicious application with a unique hash. Which of the following is the next step according to the incident response process?
- A. Recovery
- B. Lessons learned
- C. Containment
- D. Preparation
Answer: C
Explanation:
Containment is the next step according to the incident response process after identifying affected devices that are running a malicious application with a unique hash. Containment involves isolating the compromised devices or systems from the rest of the network to prevent the spread of the attack and limit its impact. Containment can be done by disconnecting the devices from the network, blocking network traffic to or from them, or applying firewall rules or access control lists. Containment is a critical step in incident response because it helps to preserve evidence for further analysis and remediation, and reduces the risk of data loss or exfiltration
https://www.fortinet.com/resources/cyberglossary/incident-response https://www.ibm.com/topics/incident-response
NEW QUESTION 4
A network engineer and a security engineer are discussing ways to monitor network operations. Which of the following is the BEST method?
- A. Disable Telnet and force SSH.
- B. Establish a continuous ping.
- C. Utilize an agentless monitor
- D. Enable SNMPv3 With passwords.
Answer: C
Explanation:
An agentless monitor is the best method to monitor network operations because it does not require any software or agents to be installed on the devices being monitored, making it less intrusive and less likely to disrupt network operations. This method can monitor various aspects of network operations, such as traffic, performance, and security.
CompTIA Security+ Study Guide, Sixth Edition (SY0-601), Chapter 4: Attacks, Threats, and Vulnerabilities, Monitoring and Detection Techniques, pg. 167-170.
NEW QUESTION 5
An employee used a corporate mobile device during a vacation Multiple contacts were modified in the device vacation Which of the following method did attacker to insert the contacts without having 'Physical access to device?
- A. Jamming
- B. BluJacking
- C. Disassoaatm
- D. Evil twin
Answer: B
Explanation:
bluejacking is the sending of unsolicited messages over Bluetooth to Bluetooth-enabled devices such as mobile phones, PDAs or laptop computers. Bluejacking does not involve device hijacking, despite what the
name implies. In this context, a human might say that the best answer to the question is B. BluJacking, because it is a method that can insert contacts without having physical access to the device.
NEW QUESTION 6
The Chief Executive Officer announced a new partnership with a strategic vendor and asked the Chief Information Security Officer to federate user digital identities using SAML-based protocols. Which of the following will this enable?
- A. SSO
- B. MFA
- C. PKI
- D. OLP
Answer: A
Explanation:
Federating user digital identities using SAML-based protocols enables Single Sign-On (SSO), which allows users to log in once and access multiple applications without having to enter their credentials for each one. References: CompTIA Security+ Certification Exam Objectives 1.3: Explain authentication and access controls.
CompTIA Security+ Certification Exam Objectives 1.3: Explain authentication and access controls.  CompTIA Security+ Study Guide, Sixth Edition, pages 41-42
CompTIA Security+ Study Guide, Sixth Edition, pages 41-42
NEW QUESTION 7
While performing a threat-hunting exercise, a security analyst sees some unusual behavior occurring in an application when a user changes the display name. The security analyst decides to perform a static code analysis and receives the following pseudocode: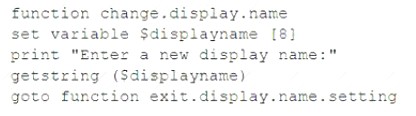
Which of the following attack types best describes the root cause of the unusual behavior?
- A. Server-side request forgery
- B. Improper error handling
- C. Buffer overflow
- D. SQL injection
Answer: D
Explanation:
SQL injection is one of the most common web hacking techniques. SQL injection is the placement of malicious code in SQL statements, via web page input12. A SQL injection attack consists of insertion or “injection” of a SQL query via the input data from the client to the application. A successful SQL injection exploit can read sensitive data from the database, modify database data (Insert/Update/Delete), execute administration operations on the database (such as shutdown the DBMS), recover the content of a given file present on the DBMS file system and in some cases issue commands to the operating system3.
According to the pseudocode given in the question, the application takes a user input for display name and concatenates it with a SQL query to update the user’s profile. This is a vulnerable practice that allows an attacker to inject malicious SQL code into the query and execute it on the database. For example, an attacker could enter something like this as their display name:
John'; DROP TABLE users; -
This would result in the following SQL query being executed:
UPDATE profile SET displayname = 'John'; DROP TABLE users; --' WHERE userid = 1;
The semicolon (;) terminates the original update statement and starts a new one that drops the users table. The double dash (–) comments out the rest of the query. This would cause a catastrophic loss of data for the application.
NEW QUESTION 8
An organization recently released a software assurance policy that requires developers to run code scans each night on the repository. After the first night, the security team alerted the developers that more than 2,000 findings were reported and need to be addressed. Which of the following is the MOST likely cause for the high number of findings?
- A. The vulnerability scanner was not properly configured and generated a high number of false positives
- B. Third-party libraries have been loaded into the repository and should be removed from the codebase.
- C. The vulnerability scanner found several memory leaks during runtime, causing duplicate reports for the same issue.
- D. The vulnerability scanner was not loaded with the correct benchmarks and needs to be updated.
Answer: A
Explanation:
The most likely cause for the high number of findings is that the vulnerability scanner was not properly configured and generated a high number of false positives. False positive results occur when a vulnerability scanner incorrectly identifies a non-vulnerable system or application as being vulnerable. This can happen due to incorrect configuration, over-sensitive rule sets, or outdated scan databases.
https://www.professormesser.com/security-plus/sy0-601/sy0-601-video/sy0-601-comptia-security-plus-course/
NEW QUESTION 9
An attacker is targeting a company. The attacker notices that the company’s employees frequently access a particular website. The attacker decides to infect the website with malware and hopes the employees’ devices will also become infected. Which of the following techniques is the attacker using?
- A. Watering-hole attack
- B. Pretexting
- C. Typosquatting
- D. Impersonation
Answer: A
Explanation:
a watering hole attack is a form of cyberattack that targets a specific group of users by infecting websites that they commonly visit123. The attacker seeks to compromise the user’s computer and gain access to the network at the user’s workplace or personal data123. The attacker observes the websites often visited by the victim or the group and infects those sites with malware14. The attacker may also lure the user to a malicious site4. A watering hole attack is difficult to diagnose and poses a significant threat to websites and users2.
NEW QUESTION 10
Which of the following controls would be the MOST cost-effective and time-efficient to deter intrusions at the perimeter of a restricted, remote military training area?
(Select TWO).
- A. Barricades
- B. Thermal sensors
- C. Drones
- D. Signage
- E. Motion sensors
- F. Guards
- G. Bollards
Answer: AD
Explanation:
Barricades and signage are the most cost-effective and time-efficient controls to deter intrusions at the perimeter of a restricted, remote military training area. References: CompTIA Security+ Study Guide Exam SY0-601, Chapter 7
CompTIA Security+ Study Guide Exam SY0-601, Chapter 7
NEW QUESTION 11
An organization with a low tolerance for user inconvenience wants to protect laptop hard drives against loss or data theft. Which of the following would be the most acceptable?
- A. SED
- B. HSM
- C. DLP
- D. TPM
Answer: A
Explanation:
SED stands for Self-Encrypting Drive, which is a type of hard drive that automatically encrypts and decrypts data using a built-in hardware encryption engine1. SEDs do not require any additional software or configuration, and they do not affect the performance or usability of the laptop2. SEDs also have a feature called Instant Secure Erase, which allows the user to quickly and securely wipe the data on the drive by deleting the encryption key1.
NEW QUESTION 12
During a recent cybersecurity audit, the auditors pointed out various types of vulnerabilities in the production area. The production area hardware runs applications that are critical to production Which of the following describes what the company should do first to lower the risk to the
Production the hardware.
- A. Back up the hardware.
- B. Apply patches.
- C. Install an antivirus solution.
- D. Add a banner page to the hardware.
Answer: B
Explanation:
Applying patches is the first step to lower the risk to the production hardware, as patches are updates that fix vulnerabilities or bugs in the software or firmware. Patches can prevent attackers from exploiting known vulnerabilities and compromising the production hardware. Applying patches should be done regularly and in a timely manner, following a patch management policy and process. References: 1
CompTIA Security+
Certification Exam Objectives, page 9, Domain 2.0: Architecture and Design, Objective 2.3: Summarize
secure application development, deployment, and automation concepts 2
CompTIA Security+ Certification
Exam Objectives, page 10, Domain 2.0: Architecture and Design, Objective 2.4: Explain the importance of
embedded and specialized systems security 3 https://www.comptia.org/blog/patch-management-best-practices
NEW QUESTION 13
An organization decided not to put controls in place because of the high cost of implementing the controls
compared to the cost of a potential fine. Which of the following risk management strategies is the organization following?
- A. Transference
- B. Avoidance
- C. Mitigation
- D. Acceptance
Answer: D
Explanation:
Acceptance is a risk management strategy that involves acknowledging the existence and potential impact of a risk, but deciding not to take any action to reduce or eliminate it. This strategy is usually adopted when the cost of implementing controls outweighs the benefit of mitigating the risk, or when the risk is deemed acceptable or unavoidable. In this case, the organization decided not to put controls in place because of the high cost compared to the potential fine, which means they accepted the risk. References: https://www.comptia.org/blog/what-is-risk-acceptance
NEW QUESTION 14
A security analyst is investigating a report from a penetration test. During the penetration test, consultants were able to download sensitive data from a back-end server. The back-end server was exposing an API that should have only been available from the company’s mobile application. After reviewing the back-end server logs, the security analyst finds the following entries:
Which of the following is the most likely cause of the security control bypass?
- A. IP address allow list
- B. User-agent spoofing
- C. WAF bypass
- D. Referrer manipulation
Answer: B
Explanation:
User-agent spoofing is a technique that involves changing the user-agent string of a web browser or other client to impersonate another browser or device. The user-agent string is a piece of information that identifies the client to the web server and can contain details such as the browser name, version, operating system, and device type. User-agent spoofing can be used to bypass security controls that rely on the user-agent string to determine the legitimacy of a request. In this scenario, the consultants were able to spoof the user-agent string of the company’s mobile application and access the API that should have been restricted to it.
NEW QUESTION 15
Which of the following incident response phases should the proper collection of the detected 'ocs and establishment of a chain of custody be performed before?
- A. Containment
- B. Identification
- C. Preparation
- D. Recovery
Answer: A
Explanation:
Containment is the phase where the incident response team tries to isolate and stop the spread of the incident12. Before containing the incident, the team should collect and preserve any evidence that may be useful for analysis and investigation12. This includes documenting the incident details, such as date, time, location, source, and impact12. It also includes establishing a chain of custody, which is a record of who handled the evidence, when, where, how, and why3. A chain of custody ensures the integrity and admissibility of the evidence in court or other legal proceedings3.
NEW QUESTION 16
......
P.S. Dumpscollection.com now are offering 100% pass ensure SY0-701 dumps! All SY0-701 exam questions have been updated with correct answers: https://www.dumpscollection.net/dumps/SY0-701/ (0 New Questions)