Top Tips Of Improve SY0-601 Real Exam
Proper study guides for Replace CompTIA CompTIA Security+ Exam certified begins with CompTIA SY0-601 preparation products which designed to deliver the Real SY0-601 questions by making you pass the SY0-601 test at your first time. Try the free SY0-601 demo right now.
Online SY0-601 free questions and answers of New Version:
NEW QUESTION 1
A security engineer needs to enhance MFA access to sensitive areas in a building. A key card and fingerprint scan are already in use. Which of the following would add another factor of authentication?
- A. Hard token
- B. Retina scan
- C. SMS text
- D. Keypad PIN
Answer: B
NEW QUESTION 2
A cybersecurity analyst needs to implement secure authentication to third-party websites without users’ passwords. Which of the following would be the BEST way to achieve this objective?
- A. OAuth
- B. SSO
- C. SAML
- D. PAP
Answer: C
NEW QUESTION 3
Which of the following are the MOST likely vectors for the unauthorized inclusion of vulnerable code in a software company’s final software releases? (Select TWO.)
- A. Unsecure protocols
- B. Use of penetration-testing utilities
- C. Weak passwords
- D. Included third-party libraries
- E. Vendors/supply chain
- F. Outdated anti-malware software
Answer: AD
NEW QUESTION 4
A user reports constant lag and performance issues with the wireless network when working at a local coffee shop. A security analyst walks the user through an installation of Wireshark and get a five-minute pcap to analyze. The analyst observes the following output: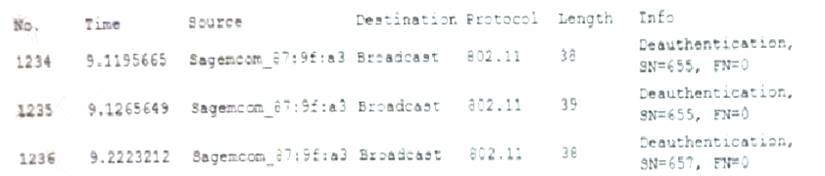
Which of the following attacks does the analyst MOST likely see in this packet capture?
- A. Session replay
- B. Evil twin
- C. Bluejacking
- D. ARP poisoning
Answer: B
NEW QUESTION 5
A remote user recently took a two-week vacation abroad and brought along a corporate-owned laptop. Upon returning to work, the user has been unable to connect the laptop to the VPN. Which of the following is the MOST likely reason for the user’s inability to connect the laptop to the VPN?
- A. Due to foreign travel, the user’s laptop was isolated from the network.
- B. The user’s laptop was quarantined because it missed the latest path update.
- C. The VPN client was blacklisted.
- D. The user’s account was put on a legal hold.
Answer: A
NEW QUESTION 6
After entering a username and password, and administrator must gesture on a touch screen. Which of the following demonstrates what the administrator is providing?
- A. Multifactor authentication
- B. Something you can do
- C. Biometric
- D. Two-factor authentication
Answer: D
NEW QUESTION 7
A public relations team will be taking a group of guest on a tour through the facility of a large e-commerce company. The day before the tour, the company sends out an email to employees to ensure all whiteboars are cleaned and all desks are cleared. The company is MOST likely trying to protect against.
- A. Loss of proprietary information
- B. Damage to the company’s reputation
- C. Social engineering
- D. Credential exposure
Answer: C
NEW QUESTION 8
A user recently attended an exposition and received some digital promotional materials The user later noticed blue boxes popping up and disappearing on the computer, and reported receiving several spam emails, which the user did not open Which of the following is MOST likely the cause of the reported issue?
- A. There was a drive-by download of malware
- B. The user installed a cryptominer
- C. The OS was corrupted
- D. There was malicious code on the USB drive
Answer: D
NEW QUESTION 9
An incident response technician collected a mobile device during an investigation. Which of the following should the technician do to maintain chain of custody?
- A. Document the collection and require a sign-off when possession changes.
- B. Lock the device in a safe or other secure location to prevent theft or alteration.
- C. Place the device in a Faraday cage to prevent corruption of the data.
- D. Record the collection in a blockchain-protected public ledger.
Answer: A
NEW QUESTION 10
A Chief Security Officer (CSO) is concerned about the amount of PII that is stored locally on each salesperson’s laptop. The sales department has a higher-than-average rate of lost equipment. Which of the following recommendations would BEST address the CSO’s concern?
- A. Deploy an MDM solution.
- B. Implement managed FDE.
- C. Replace all hard drives with SEDs.
- D. Install DLP agents on each laptop.
Answer: B
NEW QUESTION 11
An organization has decided to host its web application and database in the cloud Which of the following BEST describes the security concerns for this decision?
- A. Access to the organization's servers could be exposed to other cloud-provider clients
- B. The cloud vendor is a new attack vector within the supply chain
- C. Outsourcing the code development adds risk to the cloud provider
- D. Vendor support will cease when the hosting platforms reach EOL.
Answer: B
NEW QUESTION 12
Which of the following describes the ability of code to target a hypervisor from inside
- A. Fog computing
- B. VM escape
- C. Software-defined networking
- D. Image forgery
- E. Container breakout
Answer: B
NEW QUESTION 13
Which of the following refers to applications and systems that are used within an organization without consent or approval?
- A. Shadow IT
- B. OSINT
- C. Dark web
- D. Insider threats
Answer: A
NEW QUESTION 14
A security assessment determines DES and 3DES at still being used on recently deployed production servers. Which of the following did the assessment identify?
- A. Unsecme protocols
- B. Default settings
- C. Open permissions
- D. Weak encryption
Answer: D
NEW QUESTION 15
A company recently moved sensitive videos between on-premises. Company-owned websites. The company then learned the videos had been uploaded and shared to the internet. Which of the following would MOST likely allow the company to find the cause?
- A. Checksums
- B. Watermarks
- C. Oder of volatility
- D. A log analysis
- E. A right-to-audit clause
Answer: D
NEW QUESTION 16
A security analyst needs to complete an assessment. The analyst is logged into a server and must use native tools to map services running on it to the server's listening ports. Which of the following tools can BEST accomplish this talk?
- A. Netcat
- B. Netstat
- C. Nmap
- D. Nessus
Answer: B
NEW QUESTION 17
Select the appropriate attack and remediation from each drop-down list to label the corresponding attack with its remediation.
INSTRUCTIONS
Not all attacks and remediation actions will be used.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.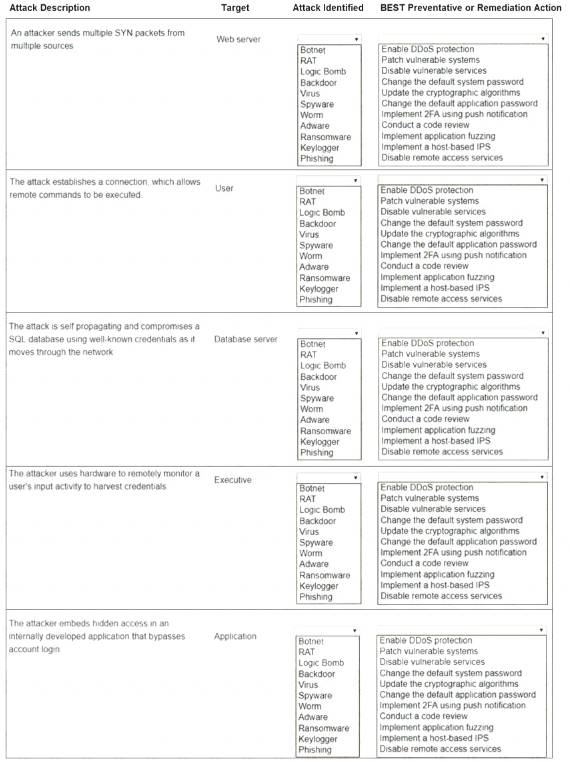
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 
NEW QUESTION 18
A security administrator suspects there may be unnecessary services running on a server. Which of the following tools will the administrator MOST likely use to confirm the suspicions?
- A. Nmap
- B. Wireshark
- C. Autopsy
- D. DNSEnum
Answer: A
NEW QUESTION 19
An organization hired a consultant to assist with an active attack, and the consultant was able to identify the compromised accounts and computers. Which of the following is the consultant MOST likely to recommend to prepare for eradication?
- A. Quarantining the compromised accounts and computers, only providing them with network access
- B. Segmenting the compromised accounts and computers into a honeynet so as to not alert the attackers.
- C. Isolating the compromised accounts and computers, cutting off all network and internet access.
- D. Logging off and deleting the compromised accounts and computers to eliminate attacker access.
Answer: B
NEW QUESTION 20
A commercial cyber-threat intelligence organization observes IoCs across a variety of unrelated customers. Prior to releasing specific threat intelligence to other paid subscribers, the organization is MOST likely obligated by contracts to:
- A. perform attribution to specific APTs and nation-state actors.
- B. anonymize any PII that is observed within the IoC data.
- C. add metadata to track the utilization of threat intelligence reports.
- D. assist companies with impact assessments based on the observed data.
Answer: B
NEW QUESTION 21
A smart retail business has a local store and a newly established and growing online storefront. A recent storm caused a power outage to the business and the local ISP, resulting in several hours of lost sales and delayed order processing. The business owner now needs to ensure two things:
* Protection from power outages
* Always-available connectivity In case of an outage
The owner has decided to implement battery backups for the computer equipment Which of the following would BEST fulfill the owner's second need?
- A. Lease a point-to-point circuit to provide dedicated access.
- B. Connect the business router to its own dedicated UPS.
- C. Purchase services from a cloud provider for high availability
- D. Replace the business's wired network with a wireless network.
Answer: C
NEW QUESTION 22
......
100% Valid and Newest Version SY0-601 Questions & Answers shared by DumpSolutions.com, Get Full Dumps HERE: https://www.dumpsolutions.com/SY0-601-dumps/ (New 218 Q&As)