Top Tips Of Avant-garde SY0-601 Vce
we provide Pinpoint CompTIA SY0-601 free practice test which are the best for clearing SY0-601 test, and to get certified by CompTIA CompTIA Security+ Exam. The SY0-601 Questions & Answers covers all the knowledge points of the real SY0-601 exam. Crack your CompTIA SY0-601 Exam with latest dumps, guaranteed!
Online CompTIA SY0-601 free dumps demo Below:
NEW QUESTION 1
An organization wants to implement a third factor to an existing multifactor authentication. The organization already uses a smart card and password. Which of the following would meet the organization’s needs for a third factor?
- A. Date of birth
- B. Fingerprints
- C. PIN
- D. TPM
Answer: B
NEW QUESTION 2
A security engineer is reviewing log files after a third discovered usernames and passwords for the organization’s accounts. The engineer sees there was a change in the IP address for a vendor website one earlier. This change lasted eight hours. Which of the following attacks was MOST likely used?
- A. Man-in- the middle
- B. Spear-phishing
- C. Evil twin
- D. DNS poising
Answer: D
NEW QUESTION 3
A cybersecurity analyst reviews the log files from a web server and sees a series of files that indicates a directory-traversal attack has occurred. Which of the following is the analyst MOST likely seeing?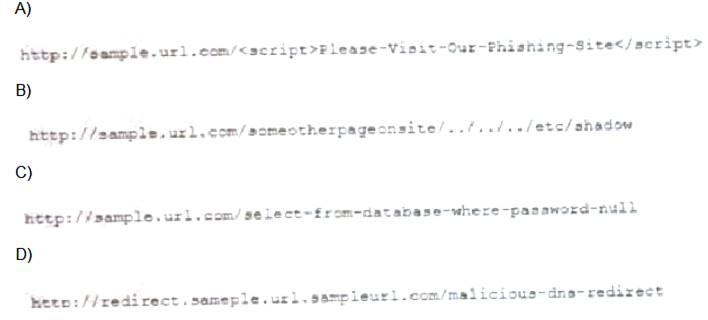
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: B
NEW QUESTION 4
A security engineer is setting up passwordless authentication for the first time. INSTRUCTIONS
Use the minimum set of commands to set this up and verify that it works. Commands cannot be reused.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.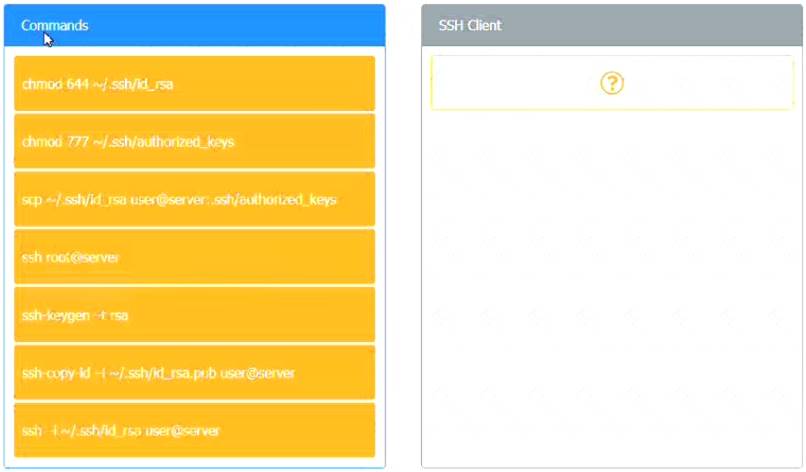
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 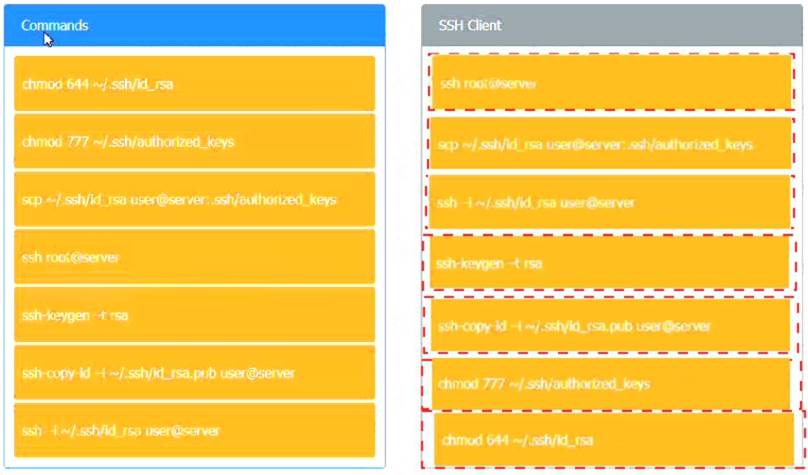
NEW QUESTION 5
Phishing and spear-phishing attacks have been occurring more frequently against a company’s staff. Which of the following would MOST likely help mitigate this issue?
- A. DNSSEC and DMARC
- B. DNS query logging
- C. Exact mail exchanger records in the DNS
- D. The addition of DNS conditional forwarders
Answer: C
NEW QUESTION 6
An analyst needs to set up a method for securely transferring files between systems. One of the requirements is to authenticate the IP header and the payload. Which of the following services would BEST meet the criteria?
- A. TLS
- B. PFS
- C. ESP
- D. AH
Answer: A
NEW QUESTION 7
Several employees return to work the day after attending an industry trade show. That same day, the security manager notices several malware alerts coming from each of the employee’s workstations. The security manager investigates but finds no signs of an attack on the perimeter firewall or the NIDS. Which of the following is MOST likely causing the malware alerts?
- A. A worm that has propagated itself across the intranet, which was initiated by presentation media
- B. A fileless virus that is contained on a vCard that is attempting to execute an attack
- C. A Trojan that has passed through and executed malicious code on the hosts
- D. A USB flash drive that is trying to run malicious code but is being blocked by the host firewall
Answer: A
NEW QUESTION 8
A Chief Information Security Officer (CISO) needs to create a policy set that meets international standards for data privacy and sharing. Which of the following should the CISO read and understand before writing the policies?
- A. PCI DSS
- B. GDPR
- C. NIST
- D. ISO 31000
Answer: B
NEW QUESTION 9
A security analyst needs to produce a document that details how a security incident occurred, the steps that were taken for recovery, and how future incidents can be avoided. During which of the following stages of the response process will this activity take place?
- A. Recovery
- B. Identification
- C. Lessons learned
- D. Preparation
Answer: C
NEW QUESTION 10
In which of the following situations would it be BEST to use a detective control type for mitigation?
- A. A company implemented a network load balancer to ensure 99.999% availability of its web application.
- B. A company designed a backup solution to increase the chances of restoring services in case of a natural disaster.
- C. A company purchased an application-level firewall to isolate traffic between the accounting department and the information technology department.
- D. A company purchased an IPS system, but after reviewing the requirements, the appliance was supposed to monitor, not block, any traffic.
- E. A company purchased liability insurance for flood protection on all capital assets.
Answer: D
NEW QUESTION 11
A company wants to deploy PKI on its Internet-facing website. The applications that are currently deployed are: www.company.com (main website)
www.company.com (main website) contactus.company.com (for locating a nearby location)
contactus.company.com (for locating a nearby location)  quotes.company.com (for requesting a price quote)
quotes.company.com (for requesting a price quote)
The company wants to purchase one SSL certificate that will work for all the existing applications and any future applications that follow the same naming conventions, such as store.company.com. Which of the following certificate types would BEST meet the requirements?
- A. SAN
- B. Wildcard
- C. Extended validation
- D. Self-signed
Answer: B
NEW QUESTION 12
Users have been issued smart cards that provide physical access to a building. The cards also contain tokens that can be used to access information systems. Users can log m to any thin client located throughout the building and see the same desktop each time. Which of the following technologies are being utilized to provide these capabilities? (Select TWO)
- A. COPE
- B. VDI
- C. GPS
- D. TOTP
- E. RFID
- F. BYOD
Answer: BE
NEW QUESTION 13
Which of the following are requirements that must be configured for PCI DSS compliance? (Select TWO).
- A. Testing security systems and processes regularly
- B. Installing and maintaining a web proxy to protect cardholder data
- C. Assigning a unique ID to each person with computer access
- D. Encrypting transmission of cardholder data across private networks
- E. Benchmarking security awareness training for contractors
- F. Using vendor-supplied default passwords for system passwords
Answer: BD
NEW QUESTION 14
A network administrator is setting up wireless access points in all the conference rooms and wants to authenticate device using PKI. Which of the following should the administrator configure?
- A. A captive portal
- B. PSK
- C. 802.1X
- D. WPS
Answer: C
NEW QUESTION 15
A security analyst is performing a forensic investigation compromised account credentials. Using the Event Viewer, the analyst able to detect the following message, ‘’Special privileges assigned to new login.’’ Several of these messages did not have a valid logon associated with the user before these privileges were assigned. Which of the following attacks is MOST likely being detected?
- A. Pass-the-hash
- B. Buffer overflow
- C. Cross-site scripting
- D. Session replay
Answer: A
NEW QUESTION 16
A network administrator would like to configure a site-to-site VPN utilizing iPSec. The administrator wants the tunnel to be established with data integrity encryption, authentication and anti- replay functions Which of the following should the administrator use when configuring the VPN?
- A. AH
- B. EDR
- C. ESP
- D. DNSSEC
Answer: C
NEW QUESTION 17
An organization has hired a security analyst to perform a penetration test. The analyst captures 1Gb worth of inbound network traffic to the server and transfer the pcap back to the machine for analysis. Which of the following tools should the analyst use to further review the pcap?
- A. Nmap
- B. cURL
- C. Netcat
- D. Wireshark
Answer: D
NEW QUESTION 18
A security audit has revealed that a process control terminal is vulnerable to malicious users installing and executing software on the system. The terminal is beyond end-of-life support and cannot be upgraded, so it is placed on a projected network segment. Which of the following would be MOST effective to implement to further mitigate the reported vulnerability?
- A. DNS sinkholding
- B. DLP rules on the terminal
- C. An IP blacklist
- D. Application whitelisting
Answer: D
NEW QUESTION 19
A security engineer needs to Implement the following requirements:
• All Layer 2 switches should leverage Active Directory tor authentication.
• All Layer 2 switches should use local fallback authentication If Active Directory Is offline.
• All Layer 2 switches are not the same and are manufactured by several vendors.
Which of the following actions should the engineer take to meet these requirements? (Select TWO).
- A. Implement RADIUS.
- B. Configure AAA on the switch with local login as secondary.
- C. Configure port security on the switch with the secondary login method.
- D. Implement TACACS+
- E. Enable the local firewall on the Active Directory server.
- F. Implement a DHCP server.
Answer: AB
NEW QUESTION 20
A network administrator needs to build out a new datacenter, with a focus on resiliency and uptime. Which of the following would BEST meet this objective? (Choose two.)
- A. Dual power supply
- B. Off-site backups
- C. Automatic OS upgrades
- D. NIC teaming
- E. Scheduled penetration testing
- F. Network-attached storage
Answer: AB
NEW QUESTION 21
The IT department at a university is concerned about professors placing servers on the university network in an attempt to bypass security controls. Which of the following BEST represents this type of threat?
- A. A script kiddie
- B. Shadow IT
- C. Hacktivism
- D. White-hat
Answer: B
NEW QUESTION 22
......
P.S. Easily pass SY0-601 Exam with 218 Q&As Thedumpscentre.com Dumps & pdf Version, Welcome to Download the Newest Thedumpscentre.com SY0-601 Dumps: https://www.thedumpscentre.com/SY0-601-dumps/ (218 New Questions)