Top Tips Of Renewal SY0-601 Exam Topics
It is more faster and easier to pass the CompTIA SY0-601 exam by using Real CompTIA CompTIA Security+ Exam questuins and answers. Immediate access to the Up to the minute SY0-601 Exam and find the same core area SY0-601 questions with professionally verified answers, then PASS your exam with a high score now.
Check SY0-601 free dumps before getting the full version:
NEW QUESTION 1
A company is adopting a BYOD policy and is looking for a comprehensive solution to protect company information on user devices. Which of the following solutions would BEST support the policy?
- A. Mobile device management
- B. Full-device encryption
- C. Remote wipe
- D. Biometrics
Answer: A
NEW QUESTION 2
A security analyst needs to make a recommendation for restricting access to certain segments of the network using only data-link layer security. Which of the following controls will the analyst MOST likely recommend?
- A. MAC
- B. ACL
- C. BPDU
- D. ARP
Answer: A
NEW QUESTION 3
In which of the following risk management strategies would cybersecurity insurance be used?
- A. Transference
- B. Avoidance
- C. Acceptance
- D. Mitigation
Answer: A
NEW QUESTION 4
A company's Chief Information Office (CIO) is meeting with the Chief Information Security Officer (CISO) to plan some activities to enhance the skill levels of the company's developers. Which of the following would be MOST suitable for training the developers'?
- A. A capture-the-flag competition
- B. A phishing simulation
- C. Physical security training
- D. Baste awareness training
Answer: B
NEW QUESTION 5
Employees are having issues accessing the company's website. Some employees report very slow performance, while others cannot the website at all. The web and security administrators search the logs and find millions of half-open connections to port 443 on the web server. Further analysis reveals thousands of different source IPs initiating this traffic. Which of the following attacks is MOST likely occurring?
- A. DDoS
- B. Man-in-the-middle
- C. MAC flooding
- D. Domain hijacking
Answer: A
NEW QUESTION 6
Which of the following would be BEST to establish between organizations to define the responsibilities of each party outline the key deliverables and include monetary penalties for breaches to manage third-party risk?
- A. An ARO
- B. An MOU
- C. An SLA
- D. A BPA
Answer: B
NEW QUESTION 7
A smart switch has the ability to monitor electrical levels and shut off power to a building in the event of power surge or other fault situation. The switch was installed on a wired network in a hospital and is monitored by the facilities department via a cloud application. The security administrator isolated the switch on a separate VLAN and set up a patch routine. Which of the following steps should also be taken to harden the smart switch?
- A. Set up an air gap for the switch.
- B. Change the default password for the switch.
- C. Place the switch In a Faraday cage.
- D. Install a cable lock on the switch
Answer: B
NEW QUESTION 8
A security analyst is using a recently released security advisory to review historical logs, looking for the specific activity that was outlined in the advisory. Which of the following is the analyst doing?
- A. A packet capture
- B. A user behavior analysis
- C. Threat hunting
- D. Credentialed vulnerability scanning
Answer: C
NEW QUESTION 9
An organization that is located in a flood zone is MOST likely to document the concerns associated with the restoration of IT operation in a:
- A. business continuity plan
- B. communications plan.
- C. disaster recovery plan.
- D. continuity of operations plan
Answer: C
NEW QUESTION 10
Which of the following BEST describes a security exploit for which a vendor patch is not readily available?
- A. Integer overflow
- B. Zero-day
- C. End of life
- D. Race condition
Answer: B
NEW QUESTION 11
A startup company is using multiple SaaS and IaaS platforms to stand up a corporate infrastructure and build out a customer-facing web application. Which of the following solutions would be BEST to provide security, manageability, and visibility into the platforms?
- A. SIEM
- B. DLP
- C. CASB
- D. SWG
Answer: C
NEW QUESTION 12
The Chief Executive Officer (CEO) of an organization would like staff members to have the flexibility to work from home anytime during business hours, incident during a pandemic or crisis, However, the CEO is concerned that some staff members may take advantage of the of the flexibility and work from high-risk countries while on holidays work to a third-party organization in another country. The Chief information Officer (CIO) believes the company can implement some basic to mitigate the majority of the risk. Which of the following would be BEST to mitigate CEO’s concern? (Select TWO).
- A. Geolocation
- B. Time-of-day restrictions
- C. Certificates
- D. Tokens
- E. Geotagging
- F. Role-based access controls
Answer: AE
NEW QUESTION 13
A manufacturer creates designs for very high security products that are required to be protected and controlled by the government regulations. These designs are not accessible by corporate networks or the Internet. Which of the following is the BEST solution to protect these designs?
- A. An air gap
- B. A Faraday cage
- C. A shielded cable
- D. A demilitarized zone
Answer: A
NEW QUESTION 14
Which of the following technical controls is BEST suited for the detection and prevention of buffer overflows on hosts?
- A. DLP
- B. HIDS
- C. EDR
- D. NIPS
Answer: C
NEW QUESTION 15
A forensics examiner is attempting to dump password cached in the physical memory of a live system but keeps receiving an error message. Which of the following BEST describes the cause of the error?
- A. The examiner does not have administrative privileges to the system
- B. The system must be taken offline before a snapshot can be created
- C. Checksum mismatches are invalidating the disk image
- D. The swap file needs to be unlocked before it can be accessed
Answer: A
NEW QUESTION 16
A Chief Security Office's (CSO's) key priorities are to improve preparation, response, and recovery practices to minimize system downtime and enhance organizational resilience to ransomware attacks. Which of the following would BEST meet the CSO's objectives?
- A. Use email-filtering software and centralized account management, patch high-risk systems, and restrict administration privileges on fileshares.
- B. Purchase cyber insurance from a reputable provider to reduce expenses during an incident.
- C. Invest in end-user awareness training to change the long-term culture and behavior of staff and executives, reducing the organization's susceptibility to phishing attacks.
- D. Implement application whitelisting and centralized event-log management, and perform regular testing and validation of full backups.
Answer: D
NEW QUESTION 17
Which of the following BEST explains the reason why a server administrator would place a document named password.txt on the desktop of an administrator account on a server?
- A. The document is a honeyfile and is meant to attract the attention of a cyberintruder.
- B. The document is a backup file if the system needs to be recovered.
- C. The document is a standard file that the OS needs to verify the login credentials.
- D. The document is a keylogger that stores all keystrokes should the account be compromised.
Answer: A
NEW QUESTION 18
Which of the following BEST explains the difference between a data owner and a data custodian?
- A. The data owner is responsible for adhering to the rules for using the data, while the data custodian is responsible for determining the corporate governance regarding the data
- B. The data owner is responsible for determining how the data may be used, while the data custodian is responsible for implementing the protection to the data
- C. The data owner is responsible for controlling the data, while the data custodian is responsible for maintaining the chain of custody when handling the data
- D. The data owner grants the technical permissions for data access, while the data custodian maintains the database access controls to the data
Answer: B
NEW QUESTION 19
A security analyst is investigation an incident that was first reported as an issue connecting to network shares and the internet, While reviewing logs and tool output, the analyst sees the following: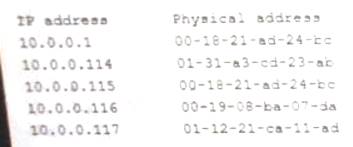
Which of the following attacks has occurred?
- A. IP conflict
- B. Pass-the-hash
- C. MAC flooding
- D. Directory traversal
- E. ARP poisoning
Answer: E
NEW QUESTION 20
A security auditor is reviewing vulnerability scan data provided by an internal security team. Which of the following BEST indicates that valid credentials were used?
- A. The scan results show open ports, protocols, and services exposed on the target host
- B. The scan enumerated software versions of installed programs
- C. The scan produced a list of vulnerabilities on the target host
- D. The scan identified expired SSL certificates
Answer: B
NEW QUESTION 21
A RAT that was used to compromise an organization’s banking credentials was found on a user’s computer. The RAT evaded antivirus detection. It was installed by a user who has local administrator rights to the system as part of a remote management tool set. Which of the following recommendations would BEST prevent this from reoccurring?
- A. Create a new acceptable use policy.
- B. Segment the network into trusted and untrusted zones.
- C. Enforce application whitelisting.
- D. Implement DLP at the network boundary.
Answer: C
NEW QUESTION 22
......
Recommend!! Get the Full SY0-601 dumps in VCE and PDF From Allfreedumps.com, Welcome to Download: https://www.allfreedumps.com/SY0-601-dumps.html (New 218 Q&As Version)