Top Tips Of Renovate 156-215.80 Question
It is more faster and easier to pass the Check-Point 156-215.80 exam by using Tested Check-Point Check Point Certified Security Administrator questuins and answers. Immediate access to the Updated 156-215.80 Exam and find the same core area 156-215.80 questions with professionally verified answers, then PASS your exam with a high score now.
Free 156-215.80 Demo Online For Check-Point Certifitcation:
NEW QUESTION 1
Anti-Spoofing is typically set up on which object type?
- A. Security Gateway
- B. Host
- C. Security Management object
- D. Network
Answer: A
NEW QUESTION 2
The most important part of a site-to-site VPN deployment is the ____.
- A. Internet
- B. Remote users
- C. Encrypted VPN tunnel
- D. VPN gateways
Answer: C
Explanation:
Site to Site VPN
The basis of Site to Site VPN is the encrypted VPN tunnel. Two Security Gateways negotiate a link and create a VPN tunnel and each tunnel can contain more than one VPN connection. One Security Gateway can maintain more than one VPN tunnel at the same time.
NEW QUESTION 3
You are unable to login to SmartDashboard. You log into the management server and run #cpwd_admin list with the following output: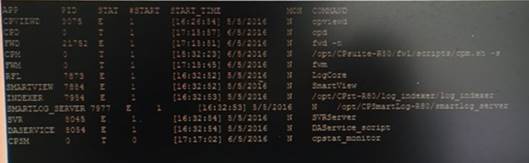
What reason could possibly BEST explain why you are unable to connect to SmartDashboard?
- A. CDP is down
- B. SVR is down
- C. FWM is down
- D. CPSM is down
Answer: C
Explanation:
The correct answer would be FWM (is the process making available communication between SmartConsole applications and Security Management Server.). STATE is T (Terminate = Down)
Symptoms
SmartDashboard fails to connect to the Security Management server.
Verify if the FWM process is running. To do this, run the command:
[Expert@HostName:0]# ps -aux | grep fwm
If the FWM process is not running, then try force-starting the process with the following command: [Expert@HostName:0]# cpwd_admin start -name FWM -path "$FWDIR/bin/fwm" -command "fwm" [Expert@HostName:0]# ps -aux | grep fwm
[Expert@HostName:0]# cpwd_admin start -name FWM -path "$FWDIR/bin/fwm" -command "fwm"
NEW QUESTION 4
If there is an Accept Implied Policy set to “First”, what is the reason Jorge cannot see any logs?
- A. Log Implied Rule was not selected on Global Properties.
- B. Log Implied Rule was not set correctly on the track column on the rules base.
- C. Track log column is set to none.
- D. Track log column is set to Log instead of Full Log.
Answer: A
Explanation:
Implied Rules are configured only on Global Properties.
NEW QUESTION 5
You want to reset SIC between smberlin and sgosaka.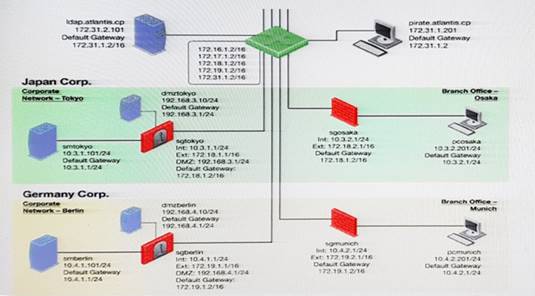
In SmartDashboard, you choose sgosaka, Communication, Reset. On sgosaka, you start cpconfig, choose Secure Internal Communication and enter the new SIC Activation Key. The screen reads The SIC was successfully initialized and jumps back to the menu. When trying to establish a connection, instead of a working connection, you receive this error message:
What is the reason for this behavior?
- A. The Gateway was not rebooted, which is necessary to change the SIC key.
- B. You must first initialize the Gateway object in SmartDashboard (i.e., right-click on the object, choose Basic Setup > Initialize).
- C. The check Point services on the Gateway were not restarted because you are still in the cpconfig utility.
- D. The activation key contains letters that are on different keys on localized keyboard
- E. Therefore, the activation can not be typed in a matching fashion.
Answer: C
NEW QUESTION 6
Packet acceleration (SecureXL) identifies connections by several attributes. Which of the attributes is NOT used for identifying connection?
- A. Source Address
- B. Destination Address
- C. TCP Acknowledgment Number
- D. Source Port
Answer: C
NEW QUESTION 7
Your bank's distributed R77 installation has Security Gateways up for renewal. Which SmartConsole application will tell you which Security Gateways have licenses that will expire within the next 30 days?
- A. SmartView Tracker
- B. SmartPortal
- C. SmartUpdate
- D. SmartDashboard
Answer: C
NEW QUESTION 8
When logging in for the first time to a Security management Server through SmartConsole, a fingerprint is saved to the:
- A. Security Management Server’s /home/.fgpt file and is available for future SmartConsole authentications.
- B. Windows registry is available for future Security Management Server authentications.
- C. there is no memory used for saving a fingerprint anyway.
- D. SmartConsole cache is available for future Security Management Server authentications.
Answer: D
NEW QUESTION 9
An administrator is creating an IPsec site-to-site VPN between his corporate office and branch office. Both offices are protected by Check Point Security Gateway managed by the same Security Management Server. While configuring the VPN community to specify the pre-shared secret the administrator found that the check box to enable pre-shared secret is shared and cannot be enabled. Why does it not allow him to specify the pre-shared secret?
- A. IPsec VPN blade should be enabled on both Security Gateway.
- B. Pre-shared can only be used while creating a VPN between a third party vendor and Check Point Security Gateway.
- C. Certificate based Authentication is the only authentication method available between two Security Gateway managed by the same SMS.
- D. The Security Gateways are pre-R75.40.
Answer: C
NEW QUESTION 10
Using mgmt_cli, what is the correct syntax to import a host object called Server_1 from the CLI?
- A. mgmt_cli add-host “Server_1” ip_address “10.15.123.10” --format txt
- B. mgmt_cli add host name “Server_1” ip_address “10.15.123.10” --format json
- C. mgmt_cli add object-host “Server_1” ip_address “10.15.123.10” --format json
- D. mgmt_cli add object “Server_1” ip_address “10.15.123.10” --format json
Answer: A
NEW QUESTION 11
Which deployment adds a Security Gateway to an existing environment without changing IP routing?
- A. Distributed
- B. Bridge Mode
- C. Remote
- D. Standalone
Answer: B
NEW QUESTION 12
What is the purpose of Captive Portal?
- A. It provides remote access to SmartConsole
- B. It manages user permission in SmartConsole
- C. It authenticates users, allowing them access to the Internet and corporate resources
- D. It authenticates users, allowing them access to the Gaia OS
Answer: C
Explanation:
Captive Portal – a simple method that authenticates users through a web interface before granting them access to Intranet resources. When users try to access a protected resource, they get a web page that
must be filled out to continue.
Reference : https://www.checkpoint.com/products/identity-awareness-software-blade/
NEW QUESTION 13
Which of the following are available SmartConsole clients which can be installed from the R77 Windows CD? Read all answers and select the most complete and valid list.
- A. SmartView Tracker, SmartDashboard, CPINFO, SmartUpdate, SmartView Status
- B. SmartView Tracker, SmartDashboard, SmartLSM, SmartView Monitor
- C. SmartView Tracker, CPINFO, SmartUpdate
- D. Security Policy Editor, Log Viewer, Real Time Monitor GUI
Answer: C
NEW QUESTION 14
How Capsule Connect and Capsule Workspace differ?
- A. Capsule Connect provides a Layer3 VP
- B. Capsule Workspace provides a Desktop with usable applications
- C. Capsule Workspace can provide access to any application
- D. Capsule Connect provides Business data isolation
- E. Capsule Connect does not require an installed application at client
Answer: A
NEW QUESTION 15
With which command can you view the running configuration of Gaia-based system.
- A. show conf-active
- B. show configuration active
- C. show configuration
- D. show running-configuration
Answer: C
NEW QUESTION 16
The system administrator of a company is trying to find out why acceleration is not working for the traffic. The traffic is allowed according to the rule base and checked for viruses. But it is not accelerated. What is the most likely reason that the traffic is not accelerated?
- A. There is a virus foun
- B. Traffic is still allowed but not accelerated
- C. The connection required a Security server
- D. Acceleration is not enabled
- E. The traffic is originating from the gateway itself
Answer: D
NEW QUESTION 17
The ______ software blade package uses CPU-level and OS-level sandboxing in order to delect and block malware.
- A. Next Generation Threat Prevention
- B. Next Generation Threat Emulation
- C. Next Generation Threat Extraction
- D. Next Generation Firewall
Answer: B
NEW QUESTION 18
Which firewall daemon is responsible for the FW CLI commands?
- A. fwd
- B. fwm
- C. cpm
- D. cpd
Answer: A
NEW QUESTION 19
Fill in the blank: Once a license is activated, a ____ should be installed.
- A. License Management file
- B. Security Gateway Contract file
- C. Service Contract file
- D. License Contract file
Answer: C
Explanation:
Service Contract File
Following the activation of the license, a Service Contract File should be installed. This file contains important information about all subscriptions purchased for a specific device and is installed via SmartUpdate. A detailed Explanation: of the Service Contract File can be found in sk33089.
NEW QUESTION 20
What does it mean if Deyra sees the gateway status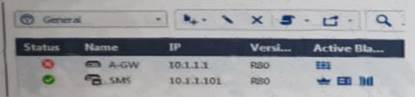
Choose the BEST answer.
- A. SmartCenter Server cannot reach this Security Gateway
- B. There is a blade reporting a problem
- C. VPN software blade is reporting a malfunction
- D. Security Gateway s MGNT NIC card is disconnected
Answer: A
NEW QUESTION 21
Packages and licenses are loaded from all of these sources EXCEPT
- A. Download Center Web site
- B. UserUpdate
- C. User Center
- D. Check Point DVD
Answer: B
Explanation:
the Download Center web site (packages)
the Check Point DVD (packages)
the User Center (licenses)
by importing a file (packages and licenses)
by running the cplic command line
Packages and licenses are loaded into these repositories from several sources: References:
NEW QUESTION 22
Examine the following Rule Base.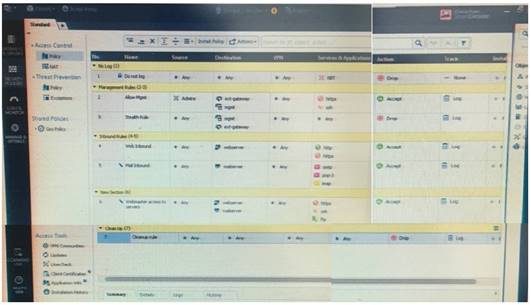
What can we infer about the recent changes made to the Rule Base?
- A. Rule 7 was created by the 'admin' administrator in the current session
- B. 8 changes have been made by administrators since the last policy installation
- C. The rules 1, 5 and 6 cannot be edited by the 'admin' administrator
- D. Rule 1 and object webserver are locked by another administrator
Answer: D
Explanation:
On top of the print screen there is a number "8" which consists for the number of changes made and not saved. Session Management Toolbar (top of SmartConsole)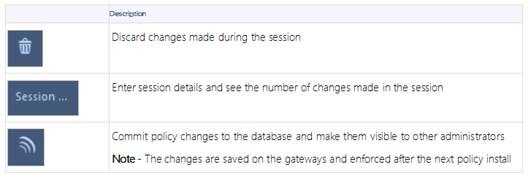
NEW QUESTION 23
Fill in the blank: The ____ software blade enables Application Security policies to allow, block, or limit website access based on user, group, and machine identities.
- A. Application Control
- B. Data Awareness
- C. URL Filtering
- D. Threat Emulation
Answer: A
NEW QUESTION 24
Which two of these Check Point Protocols are used by ?
- A. ELA and CPD
- B. FWD and LEA
- C. FWD and CPLOG
- D. ELA and CPLOG
Answer: B
NEW QUESTION 25
......
Recommend!! Get the Full 156-215.80 dumps in VCE and PDF From Downloadfreepdf.net, Welcome to Download: https://www.downloadfreepdf.net/156-215.80-pdf-download.html (New 485 Q&As Version)