Up To Date 156-215.80 Preparation Exams 2021
Exambible offers free demo for 156-215.80 exam. "Check Point Certified Security Administrator", also known as 156-215.80 exam, is a Check-Point Certification. This set of posts, Passing the Check-Point 156-215.80 exam, will help you answer those questions. The 156-215.80 Questions & Answers covers all the knowledge points of the real exam. 100% real Check-Point 156-215.80 exams and revised by experts!
Also have 156-215.80 free dumps questions for you:
NEW QUESTION 1
Which of the following is NOT an advantage to using multiple LDAP servers?
- A. You achieve a faster access time by placing LDAP servers containing the database at remote sites
- B. Information on a user is hidden, yet distributed across several servers
- C. You achieve compartmentalization by allowing a large number of users to be distributed across several servers
- D. You gain High Availability by replicating the same information on several servers
Answer: B
NEW QUESTION 2
What are types of Check Point APIs available currently as part of R80.10 code?
- A. Security Gateway API, Management API, Threat Prevention API and Identity Awareness Web Services API
- B. Management API, Threat Prevention API, Identity Awareness Web Services API and OPSEC SDK API
- C. OSE API, OPSEC SDK API, Threat Prevention API and Policy Editor API
- D. CPMI API, Management API, Threat Prevention API and Identity Awareness Web Services API
Answer: B
NEW QUESTION 3
Packet acceleration (SecureXL) identifies connections by several attributes. Which of the attributes is NOT used for identifying connection?
- A. Source Address
- B. Destination Address
- C. TCP Acknowledgment Number
- D. Source Port
Answer: C
NEW QUESTION 4
You want to define a selected administrator's permission to edit a layer. However, when you click the + sign in the “Select additional profile that will be able edit this layer” you do not see anything. What is the most likely cause of this problem? Select the BEST answer.
- A. “Edit layers by Software Blades” is unselected in the Permission Profile
- B. There are no permission profiles available and you need to create one first.
- C. All permission profiles are in use.
- D. “Edit layers by selected profiles in a layer editor” is unselected in the Permission profile.
Answer: B
NEW QUESTION 5
When launching SmartDashboard, what information is required to log into R77?
- A. User Name, Management Server IP, certificate fingerprint file
- B. User Name, Password, Management Server IP
- C. Password, Management Server IP
- D. Password, Management Server IP, LDAP Server IP
Answer: B
NEW QUESTION 6
The organization's security manager wishes to back up just the Gaia operating system parameters. Which command can be used to back up only Gaia operating system parameters like interface details, Static routes and Proxy ARP entries?
- A. show configuration
- B. backup
- C. migrate export
- D. upgrade export
Answer: B
Explanation:
3. System Backup (and System Restore)
System Backup can be used to backup current system configuration. A backup creates a compressed file that contains the Check Point configuration including the networking and operating system parameters, such as routing and interface configuration etc., but unlike a snapshot, it does not include the operating system, product binaries, and hotfixes.
NEW QUESTION 7
How do you configure an alert in SmartView Monitor?
- A. An alert cannot be configured in SmartView Monitor.
- B. By choosing the Gateway, and Configure Thresholds.
- C. By right-clicking on the Gateway, and selecting Properties.
- D. By right-clicking on the Gateway, and selecting System Information.
Answer: B
NEW QUESTION 8
The CPD daemon is a Firewall Kernel Process that does NOT do which of the following?
- A. Secure Internal Communication (SIC)
- B. Restart Daemons if they fail
- C. Transfer messages between Firewall processes
- D. Pulls application monitoring status
Answer: D
NEW QUESTION 9
After trust has been established between the Check Point components, what is TRUE about name and IP-address changes?
- A. Security Gateway IP-address cannot be changed without re-establishing the trust
- B. The Security Gateway name cannot be changed in command line without re-establishing trust
- C. The Security Management Server name cannot be changed in SmartConsole without re-establishing trust
- D. The Security Management Server IP-address cannot be changed without re-establishing the trust
Answer: A
NEW QUESTION 10
Which command can you use to enable or disable multi-queue per interface?
- A. cpmq set
- B. Cpmqueue set
- C. Cpmq config
- D. Set cpmq enable
Answer: A
NEW QUESTION 11
What is true about the IPS-Blade?
- A. in R80, IPS is managed by the Threat Prevention Policy
- B. in R80, in the IPS Layer, the only three possible actions are Basic, Optimized and Strict
- C. in R80, IPS Exceptions cannot be attached to “all rules”
- D. in R80, the GeoPolicy Exceptions and the Threat Prevention Exceptions are the same
Answer: A
NEW QUESTION 12
Which component functions as the Internal Certificate Authority for R77?
- A. Security Gateway
- B. Management Server
- C. Policy Server
- D. SmartLSM
Answer: B
NEW QUESTION 13
When attempting to start a VPN tunnel, in the logs the error 'no proposal chosen' is seen numerous times. No other VPN-related log entries are present. Which phase of the VPN negotiations has failed?
- A. IKE Phase 1
- B. IPSEC Phase 2
- C. IPSEC Phase 1
- D. IKE Phase 2
Answer: D
NEW QUESTION 14
How Capsule Connect and Capsule Workspace differ?
- A. Capsule Connect provides a Layer3 VP
- B. Capsule Workspace provides a Desktop with usable applications
- C. Capsule Workspace can provide access to any application
- D. Capsule Connect provides Business data isolation
- E. Capsule Connect does not require an installed application at client
Answer: A
NEW QUESTION 15
Check Point APIs allow system engineers and developers to make changes to their organization’s security policy with CLI tools and Web Services for all of the following except:
- A. Create new dashboards to manage 3rd party task
- B. Create products that use and enhance 3rd party solutions
- C. Execute automated scripts to perform common tasks
- D. Create products that use and enhance the Check Point Solution
Answer: A
NEW QUESTION 16
When using GAiA, it might be necessary to temporarily change the MAC address of the interface eth 0 to 00:0C:29:12:34:56. After restarting the network the old MAC address should be active. How do you configure this change?
- A. As expert user, issue these commands:# IP link set eth0 down# IP link set eth0 addr 00:0C:29:12:34:56# IP link set eth0 up
- B. Edit the file /etc/sysconfig/netconf.C and put the new MAC address in the field(conf:(conns:(conn:hwaddr (“00:0C:29:12:34:56”)
- C. As expert user, issue the command:# IP link set eth0 addr 00:0C:29:12:34:56
- D. Open the WebUI, select Network > Connections > eth0. Place the new MAC address in the field Physical Address, and press Apply to save the settings.
Answer: C
NEW QUESTION 17
Which of the following commands is used to monitor cluster members?
- A. cphaprob state
- B. cphaprob status
- C. cphaprob
- D. cluster state
Answer: A
NEW QUESTION 18
You find a suspicious connection from a problematic host. You decide that you want to block everything from that whole network, not just the problematic host. You want to block this for an hour while you investigate further, but you do not want to add any rules to the Rule Base. How do you achieve this?
- A. Use dbedit to script the addition of a rule directly into the Rule Bases_5_0.fws configuration file.
- B. Select Block intruder from the Tools menu in SmartView Tracker.
- C. Create a Suspicious Activity Rule in Smart Monitor.
- D. Add a temporary rule using SmartDashboard and select hide rule.
Answer: C
NEW QUESTION 19
Which of the below is the MOST correct process to reset SIC from SmartDashboard?
- A. Run cpconfig, and click Reset.
- B. Click the Communication button for the firewall object, then click Rese
- C. Run cpconfig on the gateway and type a new activation key.
- D. Run cpconfig, and select Secure Internal Communication > Change One Time Password.
- E. Click Communication > Reset on the Gateway object, and type a new activation key.
Answer: B
NEW QUESTION 20
What is the default time length that Hit Count Data is kept?
- A. 3 month
- B. 4 weeks
- C. 12 months
- D. 6 months
Answer: A
Explanation:
Keep Hit Count data up to - Select one of the time range options. The default is 6 months. Data is kept in the Security Management Server database for this period and is shown in the Hits column.
NEW QUESTION 21
What is the purpose of Priority Delta in VRRP?
- A. When a box is up, Effective Priority = Priority + Priority Delta
- B. When an Interface is up, Effective Priority = Priority + Priority Delta
- C. When an Interface fails, Effective Priority = Priority - Priority Delta
- D. When a box fails, Effective Priority = Priority - Priority Delta
Answer: C
NEW QUESTION 22
Your manager requires you to setup a VPN to a new business partner site. The administrator from the partner site gives you his VPN settings and you notice that he setup AES 128 for IKE phase 1 and AES 256 for IKE phase 2. Why is this a problematic setup?
- A. The two algorithms do not have the same key length and so don't work togethe
- B. You will get the error… No proposal chosen…
- C. All is fine as the longest key length has been chosen for encrypting the data and a shorter key length for higher performance for setting up the tunnel.
- D. Only 128 bit keys are used for phase 1 keys which are protecting phase 2, so the longer key length in phase 2 only costs performance and does not add security due to a shorter key in phase 1.
- E. All is fine and can be used as is.
Answer: C
NEW QUESTION 23
Which set of objects have an Authentication tab?
- A. Templates, Users
- B. Users, Networks
- C. Users, User Group
- D. Networks, Hosts
Answer: A
NEW QUESTION 24
You want to verify if there are unsaved changes in GAiA that will be lost with a reboot. What command can be used?
- A. show unsaved
- B. show save-state
- C. show configuration diff
- D. show config-state
Answer: D
NEW QUESTION 25
On the following picture an administrator configures Identity Awareness: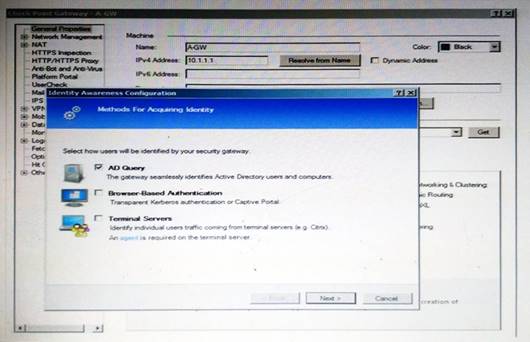
After clicking “Next” the above configuration is supported by:
- A. Kerberos SSO which will be working for Active Directory integration
- B. Based on Active Directory integration which allows the Security Gateway to correlate Active Directory users and machines to IP addresses in a method that is completely transparent to the user
- C. Obligatory usage of Captive Portal
- D. The ports 443 or 80 what will be used by Browser-Based and configured Authentication
Answer: B
Explanation:
To enable Identity Awareness:
Log in to R80 SmartConsole.
From the Awareness.
Gateway&s
Servers
view, double-click the Security Gateway on which to enable Identity
On the Network Security tab, select Identity Awareness.
The Identity Awareness
Configuration wizard opens.
Select one or more options. These options set the methods for acquiring identities of managed and unmanaged assets.
AD Query - Lets the Security Gateway seamlessly identify Active Directory users and computers
Browser-Based Authentication - Sends users to a Web page to acquire identities from unidentified users. If Transparent Kerberos Authentication is configured, AD users may be identified transparently.
Terminal Servers - Identify users in a Terminal Server environment (originating from one IP address).
NEW QUESTION 26
R80 Security Management Server can be installed on which of the following operating systems?
- A. Gaia only
- B. Gaia, SPLAT, Windows Server only
- C. Gaia, SPLAT, Windows Server and IPSO only
- D. Gaia and SPLAT only
Answer: A
Explanation:
R80 can be installed only on GAIA OS.
Supported Check Point Installations All R80 servers are supported on the Gaia Operating System:
• Security Management Server
• Multi-Domain Security Management Server
• Log Server
• Multi-Domain Log Server
• SmartEvent Server
NEW QUESTION 27
While enabling the Identity Awareness blade the Identity Awareness wizard does not automatically detect the windows domain. Why does it not detect the windows domain?
- A. Security Gateways is not part of the Domain
- B. SmartConsole machine is not part of the domain
- C. SMS is not part of the domain
- D. Identity Awareness is not enabled on Global properties
Answer: B
Explanation:
To enable Identity Awareness:
Log in to SmartDashboard.
From the Network Objects tree, expand the Check Poinbtranch.
Double-click the Security Gateway on which to enable Identity Awareness.
In the Software Blades section, select Identity Awarenesosn the Network Security tab. The Identity Awareness Configuration wizard opens.
Select one or more options. These options set the methods for acquiring identities of managed and unmanaged assets.
AD Query - Lets the Security Gateway seamlessly identify Active Directory users and computers.
Browser-Based Authentication - Sends users to a Web page to acquire identities from unidentified users. If Transparent Kerberos Authentication is configured, AD users may be identified transparently.
Terminal Servers - Identify users in a Terminal Server environment (originating from one IP address).
See Choosing Identity Sources.
Note - When you enable Browser-Based Authentication on a Security Gateway that is on an IP Series appliance, make sure to set the Voyager management application port to a port other than 443 or 80.
Click Next.
The Integration With Active Directory window opens.
When SmartDashboard is part of the domain, SmartDashboard suggests this domain automatically. If you select this domain, the system creates an LDAP Account Unit with alolf the domain controllers in the organization's Active Directory.
NEW QUESTION 28
The following graphic shows: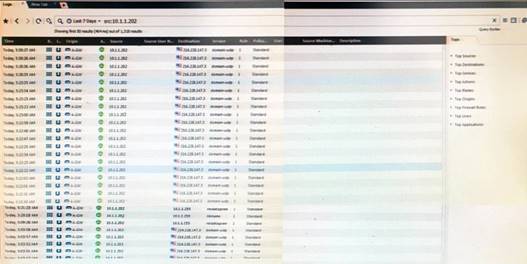
- A. View from SmartLog for logs initiated from source address 10.1.1.202
- B. View from SmartView Tracker for logs of destination address 10.1.1.202
- C. View from SmartView Tracker for logs initiated from source address 10.1.1.202
- D. View from SmartView Monitor for logs initiated from source address 10.1.1.202
Answer: C
NEW QUESTION 29
......
P.S. Certleader now are offering 100% pass ensure 156-215.80 dumps! All 156-215.80 exam questions have been updated with correct answers: https://www.certleader.com/156-215.80-dumps.html (485 New Questions)