100% Correct Check-Point 156-215.80 Braindumps Online
Cause all that matters here is passing the Check-Point 156-215.80 exam. Cause all that you need is a high score of 156-215.80 Check Point Certified Security Administrator exam. The only one thing you need to do is downloading Pass4sure 156-215.80 exam study guides now. We will not let you down with our money-back guarantee.
Online Check-Point 156-215.80 free dumps demo Below:
NEW QUESTION 1
What is the appropriate default Gaia Portal address?
- A. HTTP://[IPADDRESS]
- B. HTTPS://[IPADDRESS]:8080
- C. HTTPS://[IPADDRESS]:4434
- D. HTTPS://[IPADDRESS]
Answer: D
NEW QUESTION 2
The SIC Status “Unknown” means
- A. There is connection between the gateway and Security Management Server but it is not trusted.
- B. The secure communication is established.
- C. There is no connection between the gateway and Security Management Server.
- D. The Security Management Server can contact the gateway, but cannot establish SIC.
Answer: CExplanation:SICStatus
Explanation:
After the gateway receives the certificate issued by the ICA, the SIC status shows if the Security Management Server can communicate securely with this gateway:
Communicating - The secure communication is established.
Unknown - There is no connection between the gateway and Security Management Server.
Not Communicating - The Security Management Server can contact the gateway, but cannot establish SIC. A message shows more information.
NEW QUESTION 3
Choose the SmartLog property that is TRUE.
- A. SmartLog has been an option since release R71.10.
- B. SmartLog is not a Check Point product.
- C. SmartLog and SmartView Tracker are mutually exclusive.
- D. SmartLog is a client of SmartConsole that enables enterprises to centrally track log records and security activity with Google-like search.
Answer: D
NEW QUESTION 4
Which the following type of authentication on Mobile Access can NOT be used as the first authentication method?
- A. Dynamic ID
- B. RADIUS
- C. Username and Password
- D. Certificate
Answer: A
NEW QUESTION 5
Traffic from source 192.168.1.1 is going to www.google.com. The Application Control Blade on the gateway is inspecting the traffic. Assuming acceleration is enable which path is handling the traffic?
- A. Slow Path
- B. Medium Path
- C. Fast Path
- D. Accelerated Path
Answer: A
NEW QUESTION 6
What is the purpose of the Clean-up Rule?
- A. To log all traffic that is not explicitly allowed or denied in the Rule Base.
- B. To clean up policies found inconsistent with the compliance blade reports.
- C. To remove all rules that could have a conflict with other rules in the database.
- D. To eliminate duplicate log entries in the Security Gateway
Answer: A
NEW QUESTION 7
Fill in the blank: The tool ____ generates a R80 Security Gateway configuration report.
- A. infoCP
- B. infoview
- C. cpinfo
- D. fw cpinfo
Answer: C
Explanation:
CPInfo is an auto-updatable utility that collects diagnostics data on a customer's machine at the time of execution and uploads it to Check Point servers (it replaces the standalone cp_uploader utility for uploading files to Check Point servers).
The CPinfo output file allows analyzing customer setups from a remote location. Check Point support engineers can open the CPinfo file in a demo mode, while viewing actual customer Security Policies and Objects. This allows the in-depth analysis of customer's configuration and environment settings.
When contacting Check Point Support, collect the cpinfo files from the Security Management server and Security Gateways involved in your case.
NEW QUESTION 8
You are using SmartView Tracker to troubleshoot NAT entries. Which column do you check to view the NAT'd source port if you are using Source NAT?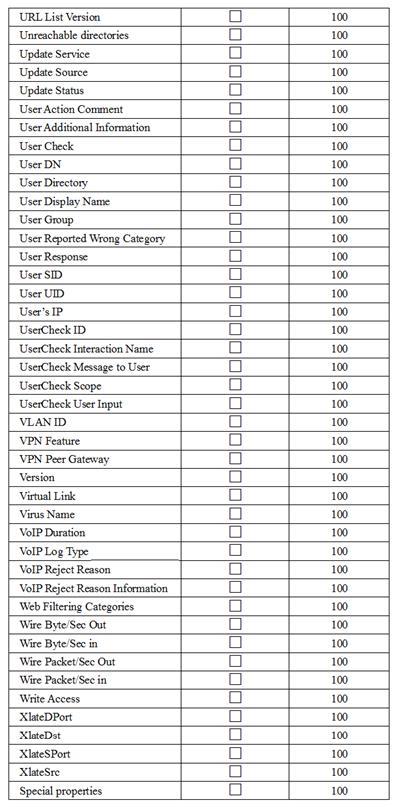
- A. XlateDst
- B. XlateSPort
- C. XlateDPort
- D. XlateSrc
Answer: B
NEW QUESTION 9
As a Security Administrator, you must refresh the Client Authentication authorized time-out every time a new user connection is authorized. How do you do this? Enable the Refreshable Timeout setting:
- A. in the user object's Authentication screen.
- B. in the Gateway object's Authentication screen.
- C. in the Limit tab of the Client Authentication Action Properties screen.
- D. in the Global Properties Authentication screen.
Answer: C
NEW QUESTION 10
After trust has been established between the Check Point components, what is TRUE about name and IP-address changes?
- A. Security Gateway IP-address cannot be changed without re-establishing the trust
- B. The Security Gateway name cannot be changed in command line without re-establishing trust
- C. The Security Management Server name cannot be changed in SmartConsole without re-establishing trust
- D. The Security Management Server IP-address cannot be changed without re-establishing the trust
Answer: A
NEW QUESTION 11
Fill in the blank: In order to install a license, it must first be added to the ______ .
- A. User Center
- B. Package repository
- C. Download Center Web site
- D. License and Contract repository
Answer: B
NEW QUESTION 12
Which tool provides a list of trusted files to the administrator so they can specify to the Threat Prevention blade that these files do not need to be scanned or analyzed?
- A. ThreatWiki
- B. Whitelist Files
- C. AppWiki
- D. IPS Protections
Answer: A
NEW QUESTION 13
Using ClusterXL, what statement is true about the Sticky Decision Function?
- A. Can only be changed for Load Sharing implementations
- B. All connections are processed and synchronized by the pivot
- C. Is configured using cpconfig
- D. Is only relevant when using SecureXL
Answer: A
NEW QUESTION 14
Which options are given on features, when editing a Role on Gaia Platform?
- A. Read/Write, Read Only
- B. Read/Write, Read only, None
- C. Read/Write, None
- D. Read Only, None
Answer: B
Explanation:
Roles
Role-based administration (RBA) lets you create administrative roles for users. With RBA, an administrator can allow Gaia users to access specified features by including those features in a role and assigning that role to users. Each role can include a combination of administrative (read/write) access to some features, monitoring (readonly) access to other features, and no access to other features.
You can also specify which access mechanisms (WebUI or the CLI) are available to the user.
Note - When users log in to the WebUI, they see only those features that they have read-only or read/write access to. If they have read-only access to a feature, they can see the settings pages, but cannot change the settings.
Gaia includes these predefined roles:
You cannot delete or change the predefined roles.
Note - Do not define a new user for external users. An external user is one that is defined on an authentication server (such as RADIUS or TACACS) and not on the local Gaia system.
NEW QUESTION 15
Which utility shows the security gateway general system information statistics like operating system information and resource usage, and individual software blade statistics of VPN, Identity Awareness and DLP?
- A. cpconfig
- B. fw ctl pstat
- C. cpview
- D. fw ctl multik stat
Answer: C
Explanation:
CPView Utility is a text based built-in utility that can be run ('cpview' command) on Security Gateway / Security Management Server / Multi-Domain Security Management Server. CPView Utility shows statistical data that contain both general system information (CPU, Memory, Disk space) and information for different Software Blades (only on Security Gateway). The data is continuously updated in easy to access views.
NEW QUESTION 16
On the following picture an administrator configures Identity Awareness: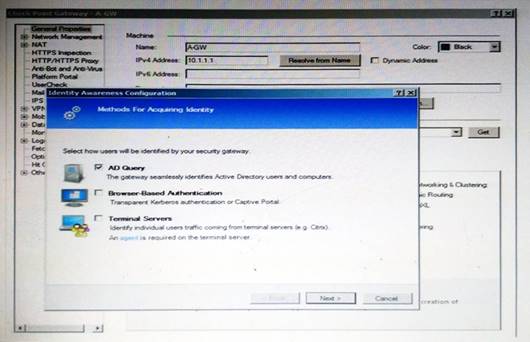
After clicking “Next” the above configuration is supported by:
- A. Kerberos SSO which will be working for Active Directory integration
- B. Based on Active Directory integration which allows the Security Gateway to correlate Active Directory users and machines to IP addresses in a method that is completely transparent to the user
- C. Obligatory usage of Captive Portal
- D. The ports 443 or 80 what will be used by Browser-Based and configured Authentication
Answer: B
Explanation:
To enable Identity Awareness:
Log in to R80 SmartConsole.
From the Awareness.
Gateway&s
Servers
view, double-click the Security Gateway on which to enable Identity
On the Network Security tab, select Identity Awareness.
The Identity Awareness
Configuration wizard opens.
Select one or more options. These options set the methods for acquiring identities of managed and unmanaged assets.
AD Query - Lets the Security Gateway seamlessly identify Active Directory users and computers
Browser-Based Authentication - Sends users to a Web page to acquire identities from unidentified users. If Transparent Kerberos Authentication is configured, AD users may be identified transparently.
Terminal Servers - Identify users in a Terminal Server environment (originating from one IP address).
NEW QUESTION 17
What are the three tabs available in SmartView Tracker?
- A. Network & Endpoint, Management, and Active
- B. Network, Endpoint, and Active
- C. Predefined, All Records, Custom Queries
- D. Endpoint, Active, and Custom Queries
Answer: C
NEW QUESTION 18
Which one of the following is TRUE?
- A. Ordered policy is a sub-policy within another policy
- B. One policy can be either inline or ordered, but not both
- C. Inline layer can be defined as a rule action
- D. Pre-R80 Gateways do not support ordered layers
Answer: C
NEW QUESTION 19
Identify the API that is not supported by Check Point currently.
- A. R80 Management API-
- B. Identity Awareness Web Services API
- C. Open REST API
- D. OPSEC SDK
Answer: C
NEW QUESTION 20
Which of the following is TRUE about the Check Point Host object?
- A. Check Point Host has no routing ability even if it has more than one interface installed.
- B. When you upgrade to R80 from R77.30 or earlier versions, Check Point Host objects are converted to gateway objects.
- C. Check Point Host is capable of having an IP forwarding mechanism.
- D. Check Point Host can act as a firewall.
Answer: A
Explanation:
A Check Point host is a host with only one interface, on which Check Point software has been installed, and which is managed by the Security Management server. It is not a routing mechanism and is not capable of IP forwarding.
NEW QUESTION 21
Fill in the blanks: A _____ license requires an administrator to designate a gateway for attachment whereas a _____ license is automatically attached to a Security Gateway.
- A. Format; corporate
- B. Local; formal
- C. Local; central
- D. Central; local
Answer: D
NEW QUESTION 22
The Captive Portal tool:
- A. Acquires identities from unidentified users.
- B. Is only used for guest user authentication.
- C. Allows access to users already identified.
- D. Is deployed from the Identity Awareness page in the Global Properties settings.
Answer: A
NEW QUESTION 23
Review the rules. Assume domain UDP is enabled in the implied rules.
What happens when a user from the internal network tries to browse to the internet using HTTP? The user:
- A. can connect to the Internet successfully after being authenticated.
- B. is prompted three times before connecting to the Internet successfully.
- C. can go to the Internet after Telnetting to the client authentication daemon port 259.
- D. can go to the Internet, without being prompted for authentication.
Answer: D
NEW QUESTION 24
Which option would allow you to make a backup copy of the OS and Check Point configuration, without stopping Check Point processes?
- A. All options stop Check Point processes
- B. backup
- C. migrate export
- D. snapshot
Answer: D
NEW QUESTION 25
......
100% Valid and Newest Version 156-215.80 Questions & Answers shared by Downloadfreepdf.net, Get Full Dumps HERE: https://www.downloadfreepdf.net/156-215.80-pdf-download.html (New 485 Q&As)