The Secret Of Cisco 300-910 Preparation
Your success in Cisco 300-910 is our sole target and we develop all our 300-910 braindumps in a way that facilitates the attainment of this target. Not only is our 300-910 study material the best you can find, it is also the most detailed and the most updated. 300-910 Practice Exams for Cisco Cisco Other Exam 300-910 are written to the highest standards of technical accuracy.
Check 300-910 free dumps before getting the full version:
NEW QUESTION 1
AppDynamics is being used to monitor your distributed Python application. Each individual container of the application is instrumented with an AppD agent. Which two configuration variables uniquely determine the module being monitored? (Choose two.)
- A. node
- B. app
- C. agent
- D. tier
- E. event
Answer: AB
NEW QUESTION 2
Which description of a canary deployment is true?
- A. deployment by accident
- B. deployment that is rolled back automatically after a configurable amount of minutes
- C. deployment relating to data mining development
- D. deployment to a limited set of servers or users
Answer: D
NEW QUESTION 3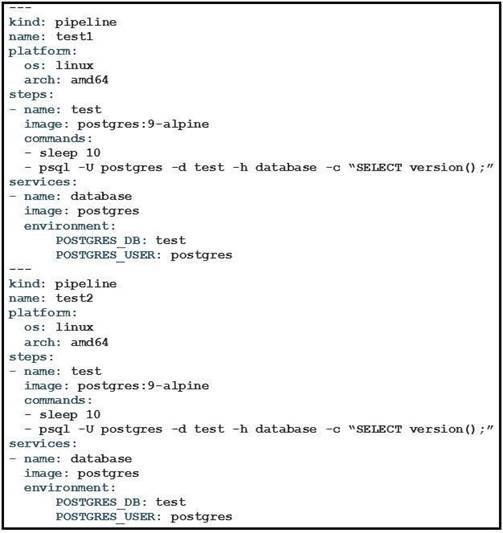
Refer to the exhibit. What is the user doing with Drone in this automated test?
- A. testing Alpine Linux versus Ubuntu Linux
- B. testing a PostgreSQL DB against multiple architectures
- C. testing only the amd64 architecture
- D. testing PostgreSQL deployment in an Alpine Linux VM
Answer: D
NEW QUESTION 4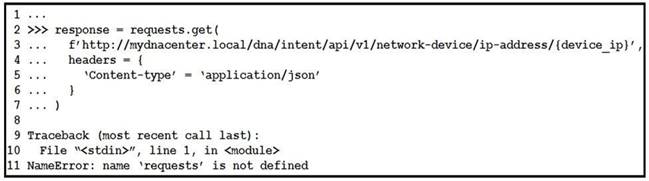
Refer to the exhibit. What is causing the requests code to fail?
- A. Rython3 is not compatible with requests.
- B. The requests library is not imported.
- C. The requests library is not installed.
- D. The requests coming into stdin fail because device_ip cannot be parsed.
Answer: B
NEW QUESTION 5
A DevOps engineer must validate the working state of the network before implementing a CI/CD pipeline model. Which configuration management tool is designed to accomplish this?
- A. Jenkins
- B. Genie CLI
- C. Travis CI
- D. Python YAML data libraries
Answer: A
NEW QUESTION 6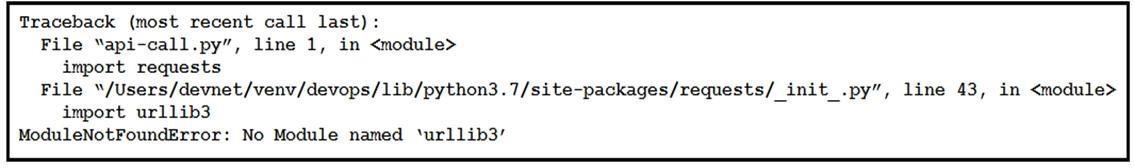
Refer to the exhibit. What is the reason for this error message?
- A. The required dependencies for the urllib3 module are not installed.
- B. The requests module is not installed.
- C. The required dependencies for the requests module are not installed.
- D. The site-packages directory has been corrupted.
Answer: B
NEW QUESTION 7
A DevOps engineer is supporting a containerized application with multiple components running across the Kubernetes cluster. Metrics from the container (CPU and memory) and application (requests per second and heap size) are being collected by Prometheus and displayed with Grafana. Users report transaction timeout problems with the application, but the metric graphs all look within normal levels.
Which type of failure would prevent the engineer from seeing the problem using the captured metrics?
- A. Grafana has lost connectivity to Prometheus, which causes graphs to display only the cached data.
- B. CPU and memory metrics from Kubernetes nodes are not accurate due to the way that containers share resources.
- C. Some containers are crashing regularly and being restarted automatically by Kubernetes.
- D. The metricbeat agent has crashed and is no longer sending new data to Prometheus, so the metrics are not updating.
Answer: D
NEW QUESTION 8
A developer is nearing the end of a software development cycle and is ready to deploy the software. The customer wants to continue using a secure software development lifecycle methodology and must plan for postproduction components. Which two areas should be the developer address? (Choose two.)
- A. performing code reviews
- B. requirement gathering
- C. change management process
- D. new code scanning
- E. rollback plans
Answer: AC
NEW QUESTION 9
Which type of testing should be integrated into a CI/CD pipeline to ensure the correct behavior of all of the modules in the source code that were developed using TDD?
- A. soak testing
- B. unit testing
- C. load testing
- D. volume testing
Answer: B
NEW QUESTION 10
Which step must be taken to enable centralized logging in a Kubernetes environment?
- A. No steps need to be take
- B. The master node automatically aggregates logs from all worker nodes and stores them on the specified persistent volume.
- C. Create a CustomResourceDefinition in each deployment that specifies the IP or names the log collector.
- D. Deploy a sidecar node that aggregates logs from the entire cluster.
- E. Create a DaemonSet that deploys a container with a logging agent on every node in the cluster.
Answer: C
NEW QUESTION 11
When static routes are added to a router in a network using a CI/CD pipeline, an Ansible playbook is used to make these changes. Which steps must be added to the pipeline to validate that the changes have the intended effect on the traffic flow?
- A. Add a step to run the debug ip routing command before the change, and add a step after the change to issue the no debug ip routing command.
- B. Add a step to capture the routing table before the change, and add a step after the change to capture it agai
- C. Calculate the difference between the two for review.
- D. Add a step to ping a host on each of the static routes before the change, and a step after to repeat the same chec
- E. Calculate the difference between the two checks for review.
- F. Add a step to run the same playbook again with the debug option enabled and use grep on the log output to ensure that the commands are not applied again.
Answer: B
NEW QUESTION 12
How long analysis systems such as Elasticsearch, Logstash, and Kibana Stack handle ingesting unstructured logs from different devices in various formats?
- A. All devices that generate syslogs must use agents that process the local logs and transmit them in a specific format to the ELK Stack.
- B. All logs are stored in their unstructured text format, and the ELK Stack performs data analysis by intelligently parsing the logs using machine learning algorithms.
- C. All different message formats are parsed separately using custom filters, and the resulting structured data is stored for later analysis.
- D. A single, comprehensive log format is defined on the ELK Stac
- E. All incoming logs, regardless of format, are transformed to match the comprehensive format, and only applicable fields are populated.
Answer: D
NEW QUESTION 13
Which two actions help limit the attack surface of your Docker container? (Choose two.)
- A. Run only a single service in each container.
- B. Run all services in a single image.
- C. Use version tags for base images and dependencies.
- D. Use Kali Linux as a base image.
- E. Download images over HTTPS supporting sites.
Answer: CE
NEW QUESTION 14
How does eliminating hardcoded or default passwords help to secure an environment?
- A. helps by enforcing your password in a repository and storing it in a secure vault
- B. helps to manage passwords centrally
- C. helps penetration testing team to focus on other issues more efficiently
- D. helps by removing back doors in your environments
Answer: A
NEW QUESTION 15
A user wants to deploy a new service to a Kubernetes cluster. Which two commands accomplish this goal? (Choose two.)
- A. Apply
- B. Install
- C. Deploy
- D. Create
- E. Expose
Answer: AE
NEW QUESTION 16
Configuration changes to the production network devices are performed by a CI/CD pipeline. The code repository and the CI tool are running on separate servers. Some configuration changes are pushed to the code repository, but the pipeline did not start.
Why did the pipeline fail to start?
- A. The CI server was not configured as a Git remote for the repository.
- B. The webhook call from the code repository did not reach the CI server.
- C. Configuration changes must be sent to the pipeline, which then updates the repository.
- D. The pipeline must be started manually after the code repository is updated.
Answer: C
NEW QUESTION 17
A developer wants to deploy a highly available web server cluster and decides to put a load balancer in front of multiple clustered nodes that run the same web service. The goal is for the load balancer to take in users and distribute the load across the whole cluster.
What kind of high-availability configuration is the developer running?
- A. active
- B. passive
- C. active-passive
- D. active-active
Answer: C
NEW QUESTION 18
What is the purpose of using a build tool in software development?
- A. It complies source code into binaries and executables.
- B. It provides a way to edit source code using a graphical interface.
- C. It is a manual process that is followed to build software.
- D. It tracks bugs and incidents in a built application.
Answer: A
NEW QUESTION 19
......
Thanks for reading the newest 300-910 exam dumps! We recommend you to try the PREMIUM 2passeasy 300-910 dumps in VCE and PDF here: https://www.2passeasy.com/dumps/300-910/ (0 Q&As Dumps)