Approved 300-320 Bible 2021
Our pass rate is high to 98.9% and the similarity percentage between our 300-320 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the Cisco 300-320 exam in just one try? I am currently studying for the Cisco 300-320 exam. Latest Cisco 300-320 Test exam practice questions and answers, Try Cisco 300-320 Brain Dumps First.
Free demo questions for Cisco 300-320 Exam Dumps Below:
NEW QUESTION 1
A network manager wants all remote sites to be designed to communicate dynamically with each other using DMVPN technology without requiring much configuration on the spoke routers. DMVPN uses which protocol to achieve this goal?
- A. GRE
- B. NHRP
- C. SSH
- D. ARP
Answer: B
NEW QUESTION 2
SDN solution for WAN which is support automation, PnP (Plug and Play) application delivers on WAN..
- A. APIC
- B. APIC-EM
- C. Enterprise NFV
- D. WAAS
- E. ACI
Answer: B
NEW QUESTION 3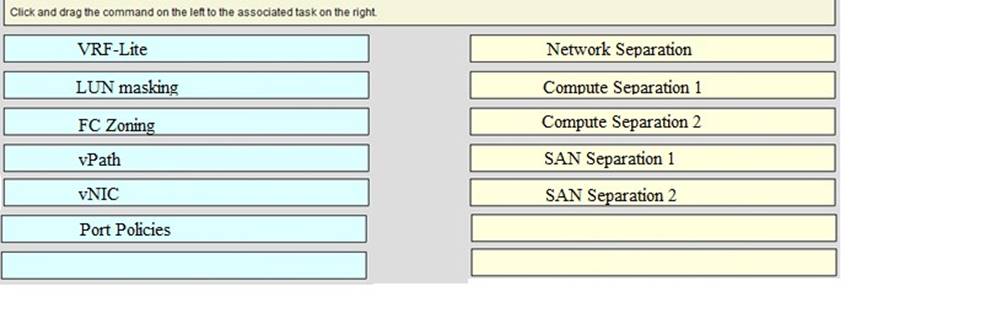
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 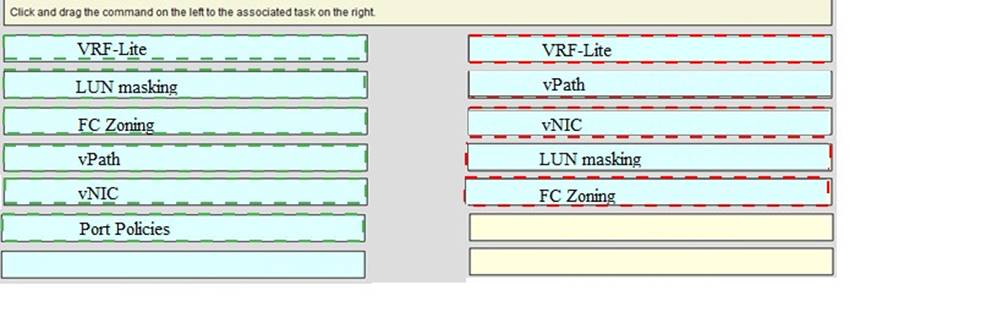
NEW QUESTION 4
Which security function is inherent in an Application Centric Infrastructure network?
- A. Intrusion Prevention
- B. Intrusion Detection
- C. Default Denial Network
- D. Default Inter-EPG connectivity
Answer: D
NEW QUESTION 5
A Layer 2 switch in the network has recently started broadcasting traffic out of every port and is impacting network performance. The engineering department determines that a MAC overflow attack is the cause. Which two features can protect and mitigate the damage of the attacks? (Choose two.)
- A. Storm Control
- B. Port Security
- C. SPAN
- D. BPDU Filters
- E. IP Source Guard
- F. VACLs
Answer: AB
NEW QUESTION 6
Which technology should a network designer combine with VSS to ensure a loop free topology with optimal convergence time?
- A. PortFast
- B. UplinkFast
- C. RPVST+
- D. Multichassis EtherChannel
Answer: D
Explanation:
"C" definitely not as STP is disabled when VSS is configured at the distribution layer. MEC comes with Cisco Catalyst (VSS) like vPC comes with Cisco NX-OS.
NEW QUESTION 7
A client request includes a network design that ensures all connections between the access layer and distribution layer are active and forwarding traffic at all times. Which design approach achieves this request?
- A. Enable backbone fast on the two distribution switches and create a port channel between each accesslayer switch and both distribution switches
- B. Configure HSRP for all VLANs and adjust the hello timer for faster convergence
- C. Configure Rapid PVST+ and adjust the timers for fast convergence
- D. Create a VSS between the two distribution switches and also create a MEC between the VSS and each access layer switch.
Answer: D
NEW QUESTION 8
What is the preferred protocol for a router that is running an IPv4 and IPv6 dual stack configuration?
- A. IPX
- B. microsoft Netbios
- C. IPv6
- D. IPv4
Answer: C
NEW QUESTION 9
What is the physical topology of ACI?
- A. leaf & spine
- B. point to point
- C. hub & spoke
- D. spoke to spoke
Answer: A
NEW QUESTION 10
Refer to the exhibit. A customer wants to use HSRP as a First Hop Redundancy Protocol. Both routers are currently running and all interfaces are active. Which factor determines which router becomes the active HSRP device?
- A. the router with the highest MAC address for the respective group
- B. the router with the highest IP address for the respective group
- C. the router that boots up last
- D. the router with the highest interface bandwidth for the respective group
Answer: B
NEW QUESTION 11
Which of the following facts must be considered when designing for IP telephony within an Enterprise Campus network?
- A. Because the IP phone is a three-port switch, IP telephony extends the network edge, impacting the Distribution layer.
- B. Video and voice are alike in being bursty and bandwidth intensive, and thus impose requirements to be lossless, and have minimized delay and jitter.
- C. IP phones have no voice and data VLAN separation, so security policies must be based on upper layer traffic characteristics.
- D. Though multi-VLAN access ports are set to Dot1Q and carry more than two VLANs they are not trunk ports.
Answer: D
Explanation:
https://www.cisco.com/c/en/us/support/docs/switches/catalyst-4500-series-switches/69632-configuring-cat-ipph html#topic1
When you connect an IP phone to a switch using a trunk link, it can cause high CPU utilization in the switches.
As all the VLANs for a particular interface are trunked to the phone, it increases the number of STP instances the switch has to manage. This increases the CPU utilization. Trunking also causes unnecessary broadcast / multicast / unknown unicast traffic to hit the phone link. In order to avoid this, remove the trunk configuration and keep the voice and access VLAN configured along with Quality of Service (QoS). Technically, it is still a trunk, but it is called a Multi-VLAN Access Port (MVAP). Because voice and data traffic can travel through the same port, you should specify a different VLAN for each type of traffic. You can configure a switch port to forward voice and data traffic on different VLANs. Configure IP phone ports with a voice VLAN configuration.
This configuration creates a pseudo trunk, but does not require you to manually prune the unnecessary VLANs.
NEW QUESTION 12
While designing quality of service policies, which two types of traffic must be prioritized as management traffic? (Choose two )
- A. SCP
- B. ICMP
- C. RADIUS
- D. HTTPS
- E. SSH
Answer: DE
NEW QUESTION 13
A link state routing protocol wants to connect tow separate domains, what should be configured (it's a question about IS-IS)?
- A. Level 1 router
- B. Level 1 router interface
- C. Level 2 router interface
- D. Level 2 router
Answer: D
NEW QUESTION 14
What protocol is used for connectivity between VSS layers?
- A. PAgP
- B. IVR
- C. ISL
- D. VSL
- E. ...
Answer: D
NEW QUESTION 15
Which VRF component ensures control plane separation between the different Layer 3 VPNs?
- A. FIB
- B. routing protocol instance
- C. RIB
- D. a subset of the router interfaces
Answer: B
NEW QUESTION 16
A data center is being deployed, and one design requirement is to be able to readily scale server virtualization. Which IETF standard technology can provide this requirement?
- A. Transparent interconnection of Lots of Links
- B. data center bridging
- C. cisco fabric path
- D. cisco unified fabric
Answer: A
NEW QUESTION 17
Which two values does EIGRP use to calculate the metric of a route in a converged EIGRP topology? (Choose two)
- A. redundancy
- B. bandwidth
- C. cost
- D. delay
- E. hops
Answer: BD
NEW QUESTION 18
Which option maximizes EIGRP scalability?
- A. route redistribution
- B. route redundancy
- C. route filtering
- D. route summarization
Answer: D
NEW QUESTION 19
Explain to a customer 2 advantages of the routing summarization.(Choose two)
- A. small routing table
- B. small upstream impact of a flapping interface
- C. fast convergence
- D. security
- E. enhance view of the architecture
Answer: AB
NEW QUESTION 20
Which mechanism is enabled by default in the OTV technology to conserve bandwidth?
- A. Control plane traffic is prevented from traversing the OTV link
- B. Unknown unicast flooding is suppressed over the OTV link.
- C. BPDUs are allowed to traverse the OTV link
- D. Data plane traffic is prevented from traversing the OTV link.
Answer: B
NEW QUESTION 21
At which layer in the ACI fabric are policies enforced?
- A. leaf
- B. spine
- C. APIC
- D. endpoint
Answer: C
NEW QUESTION 22
An engineer is redesigning the infrastructure for a campus environment. The engineer must maximize the use of the links between the core and distribution layers. By which two methods can this usage be maximized? (Choose two.)
- A. Design the links between the core and distribution layers to use RPVSTP+
- B. Design with multiple unequal-cost links between the core and distribution layers.
- C. Design the links between the core and distribution layers to use an IGP
- D. Design the links between the core and distribution layers to use HSRP.
- E. Design with multiple equal-cost links between the core and distribution layers.
Answer: AD
NEW QUESTION 23
Engineer is designing QoS for application. Which QoS architecture should he choose if application needs to
have reserved bandwidth prior to sending data?
- A. Differentiated services
- B. Integrated services
- C. LLQ
- D. ToS
Answer: B
NEW QUESTION 24
about IPv4 and IPv6 on the same router (dual stack) with IS-IS
- A. …
- B. IS-IS
- C. …
- D. …
Answer: B
Explanation:
- Cisco added multitopolgy support for IS-IS to increase flexibility within dual-stack environment.
- Two TLVs added:
• IPv6 reachability TLV
• IPv6 interface address TLV
- Multi topology IS-IS:
• A separate topology is kept for both IPv4 and IPv6 (some links may not be able to carry IPv6 --> Avoid traffic black-holed)
• This mode removes the restriction that all interfaces on which IS-IS is configured must support the identical set of network address families.
• A separate SFP per address family.
• Wide metric must be used.
- Single-topology IS-IS:
• One SPF instance for both IPv4 and IPv6.
• Easier to administer but network must be homogeneous.
• Due to consistency checks, a router running IS-IS for both IPv4 and IPv6 does notform an adjacency with a router running IS-IS for IPv4 or IPv6 only. Disable consistency checks to maintain adjacencies active in heterogeneous environments. ForL1 links, this is primarily done during transition.
• As in any IS-IS design, L2 routers must be contiguous. IPv6 adjacency checks are notdone on L2 links.
NEW QUESTION 25
What is one function of key server in Cisco GETVPN deployment?
- A. sending the RSA certificate
- B. providing pre-shared keys
- C. maintaining security polices
- D. providing the group ID
Answer: C
Explanation:
Key server is responsible for maintaining security policies, authenticating the GMs and providing the session key for encrypting traffic. KS authenticates the individual GMs at the time of registration. Only after
successful registration the GMs can participate in group SA. https://www.cisco.com/c/en/us/products/collateral/security/group-encrypted-transportvpn/deployment_guide_c07_554713.html
NEW QUESTION 26
An engineer is considering time of convergence in a new Layer 3 environment design. Which two attribute must be considered? (Choose two.)
- A. OSPF database updates
- B. addition of a valid forwarding path
- C. forwarding table updates
- D. loss of a valid forwarding path
- E. SPT timer updates
Answer: CD
NEW QUESTION 27
An engineer wants to have a resilient access layer in data center so that switches on the access layer have separate physical connections to a pair of redundant distribution switches. Which technology achieves this goals?
- A. PaGP
- B. LACP
- C. VSL
- D. EVPC
- E. VSS
- F. ECMP
Answer: E
NEW QUESTION 28
Which routing protocol provides the fastest convergence and greatest flexibility within a campus environment?
- A. OSPF
- B. IS-IS
- C. BGP
- D. EIGRP
Answer: D
NEW QUESTION 29
An engineer must design a Cisco VSS-based configuration within a customer campus network. The two VSS switches are provisioned for the campus distribution layer… Which option is the primary reason to avoid plugging both VSL links into the supervisor ports?
- A. The implementation creates a loop
- B. The design lacks optimal hardware diversity
- C. Limited bandwidth is available for VSS convergence
- D. QoS is required on the VSL links
Answer: B
Explanation:
The best-practice recommendation for VSL link resiliency is to bundle two 10-Gbps ports from different sources. Doing this might require having one port from the supervisor and other from a Cisco 6708 line card. When configuring the VSL, note the following guidelines and restrictions:
For line redundancy, we recommend configuring at least two ports per switch for the VSL. For module redundancy, the two ports can be on different switching modules in each chassis.
NEW QUESTION 30
What should be implemented to prevent exceeding the 50mb allowable bandwidth of internet circuit?
- A. policing
- B. shaping
- C. CIR
- D. rate-limit
Answer: B
NEW QUESTION 31
......
100% Valid and Newest Version 300-320 Questions & Answers shared by Certshared, Get Full Dumps HERE: https://www.certshared.com/exam/300-320/ (New 448 Q&As)