Simulation 300-165 Guidance 2021
Ucertify offers free demo for 300-165 exam. "DCII Implementing Cisco Data Center Infrastructure (DCII)", also known as 300-165 exam, is a Cisco Certification. This set of posts, Passing the Cisco 300-165 exam, will help you answer those questions. The 300-165 Questions & Answers covers all the knowledge points of the real exam. 100% real Cisco 300-165 exams and revised by experts!
Free 300-165 Demo Online For Cisco Certifitcation:
NEW QUESTION 1
Which feature must be enabled for Cisco TrustSec FC Link Encryption to work on a Cisco MDS 9000 Series Switch?
- A. crypto IKE
- B. port security
- C. LDAP
- D. FC-SP
Answer: D
NEW QUESTION 2
Which statement about Cisco FabricPath is true?
- A. It is the best solution for interconnecting multiple data centers.
- B. It optimizes STP throughout the Layer 2 network.
- C. It is a simplified extension of Layer 3 networks across a single data center.
- D. The Cisco FabricPath domain appears as a single STP bridge, where each edge port uses the same MAC address.
Answer: D
Explanation:
To have a loop-free topology for the CE/FabricPath hybrid network, the FabricPath network automatically displays as a single bridge to all connected CE devices. The STP domains do not cross into the FabricPath network. If multiple STP domains are defined, BPDUs and topology change notifications (TCNs) are localized to the domain. If a connected STP domain is multihomed to the FabricPath domain, a TCN must be able to reach to all devices in the STP domain through the FabricPath domain. As a result, the TCN is sent to the FabricPath domain through the IS-IS protocol data unit (PDU) by default.
Reference: http://www.cisco.com/en/US/docs/switches/datacenter/nexus5000/sw/mkt_ops_guides/513_n1_1/n5k_ops_fabricpath.html
NEW QUESTION 3
Refer to the exhibit.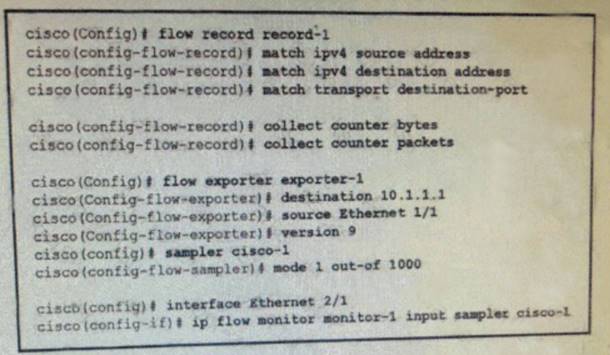
Which statement about the NetFlow implementation is true?
- A. It samples inbound IPv6 traffic on Ethernet 2/1
- B. It uses TCP for data export.
- C. It samples outbound traffic on Ethernet 2/1
- D. It samples inbound traffic on Ethernet 2/1
Answer: D
Explanation:
Reference:
https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/fnetflow/configuration/15-mt/fnf-15-mtbook/use-fnflow-redce-cpu.html
NEW QUESTION 4
In OTV, how are the VLANs split when a site has two edge devices?
- A. They are configured manually by user.
- B. They are split in half among each edge device.
- C. They are split as odd and even VLAN IDs on each edge device.
- D. It is not possible to have two edge devices in same sit
Answer: C
NEW QUESTION 5
Which technology facilitates a nondisruptive upgrade on a Cisco Nexus 5000 Series Switch?
- A. VSS
- B. ITD
- C. VDC
- D. vPC
Answer: D
NEW QUESTION 6
Which action limits the maximum number of routes that are allowed in the routing table?
- A. Use a BGP filter.
- B. Use only static routes.
- C. Use the maximum routes command inside address family.
- D. Use a route map to filter route
Answer: C
NEW QUESTION 7
Which description of Cisco zoning is true?
- A. With enhanced zoning a single configuration session locks the entire fabric to implement achange.
- B. In soft zoning individual frames are inspected on ingress.
- C. Hard zoning is the most efficient method because it is enforced through software.
- D. Soft zoning is implemented by using TCA
Answer: A
NEW QUESTION 8
You have a Cisco Fabric Path network, you must extend the network to support more than 16 million segment, what should you do?
- A. Enable the interface-vlan feature and configure the VLAN IDs
- B. Enable the nv overlay feature and configure the segment IDs
- C. Enable the vn-segment-vlan-based feature and configure segment IDs
- D. Enable the FabricPath feature and configure the VLAN IDs.
Answer: C
Explanation:
https://www.cisco.com/c/en/us/products/collateral/switches/nexus-7000-series-switches/whitepaper- c11-737022.html
NEW QUESTION 9
DRAG DROP
Drag the security description on the left to the appropriate security feature on the right.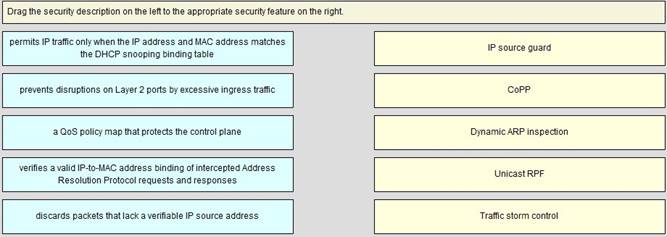
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
IP Source guard: IP Source Guard provides source IP address filtering on a Layer 2 port to prevent a malicious host from impersonating a legitimate host by assuming the legitimate host's IP address. The feature uses dynamic DHCP snooping and static IP source binding to match IP addresses to hosts on untrusted Layer 2 access ports.
Initially, all IP traffic on the protected port is blocked except for DHCP packets. After a client receives an IP address from the DHCP server, or after static IP source binding is configured by the administrator, all traffic with that IP source address is permitted from that client. Traffic from other hosts is denied. This filtering limits a host's ability to attack the network by claiming a neighbor host's IP address. IP Source Guard is a port-based feature that automatically creates an implicit port access control list (PACL).
CoPP: Control Plane Policing (CoPP) introduced the concept of early rate-limiting protocol specific traffic destined to the processor by applying QoS policies to the aggregate control-plane interface. Control Plane Protection extends this control plane functionality by providing three additional control-plane subinterfaces under the top-level (aggregate) control-plane interface. Each subinterface receives and processes a specific type of control-plane traffic.
Dynamic Arp Inspection: Dynamic ARP inspection is a security feature that validates ARP packets in a network. It intercepts, logs, and discards ARP packets with invalid IP-to-MAC address bindings. This capability protects the network from certain man-in-the-middle attacks.
Dynamic ARP inspection ensures that only valid ARP requests and responses are relayed. The switch performs these activities:
• Intercepts all ARP requests and responses on untrusted ports
• Verifies that each of these intercepted packets has a valid IP-to-MAC address binding before updating the local ARP cache or before forwarding the packet to the appropriate destination
• Drops invalid ARP packets
Unicast RPF: The Unicast RPF feature reduces problems that are caused by the introduction of malformed or forged (spoofed) IP source addresses into a network by discarding IP packets that lack a verifiable IP source address. For example, a number of common types of Denial-of-Service (DoS) attacks, including Smurf and Tribal Flood Network (TFN) attacks, can take advantage of forged or rapidly changing source IP addresses to allow attackers to thwart efforts to locate or filter the attacks. Unicast RPF defilects attacks by forwarding only the packets that have source addresses that are valid
and consistent with the IP routing table.
When you enable Unicast RPF on an interface, the device examines all ingress packets received on that interface to ensure that the source address and source interface appear in the routing table and match the interface on which the packet was received. This examination of source addresses relies on the Forwarding Information Base (FIB).
Traffic Storm Control: A traffic storm occurs when packets flood the LAN, creating excessive traffic and degrading network performance. You can use the traffic storm control feature to prevent disruptions on Layer 2 ports by a broadcast, multicast, or unicast traffic storm on physical interfaces. Traffic storm control (also called traffic suppression) allows you to monitor the levels of the incoming broadcast, multicast, and unicast traffic over a 1-second interval. During this interval, the traffic level, which is a percentage of the total available bandwidth of the port, is compared with the traffic storm control level that you configured. When the ingress traffic reaches the traffic storm control level that is configured on the port, traffic storm control drops the traffic until the interval ends.
NEW QUESTION 10
Refer to the exhibit.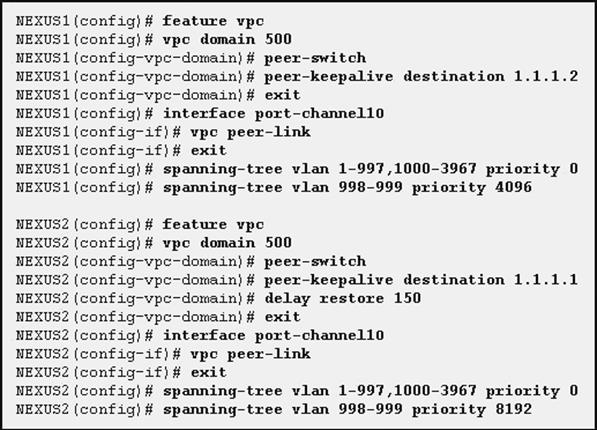
You configure two switches named NEXUS1 and NEXUS2. Which two results of implementing the configuration are true? (Choose two.)
- A. NEXUS1 is the spanning-tree root for VLAN 100.
- B. NEXUS1 is the spanning-tree root for VLAN 998.
- C. NEXUS2 is the spanning-tree root for VLAN 100.
- D. Both switches are the spanning-tree root for VLAN 998.
- E. Both switches are the spanning-tree root for VLAN 100.
Answer: BE
NEW QUESTION 11
Refer to the exhibit.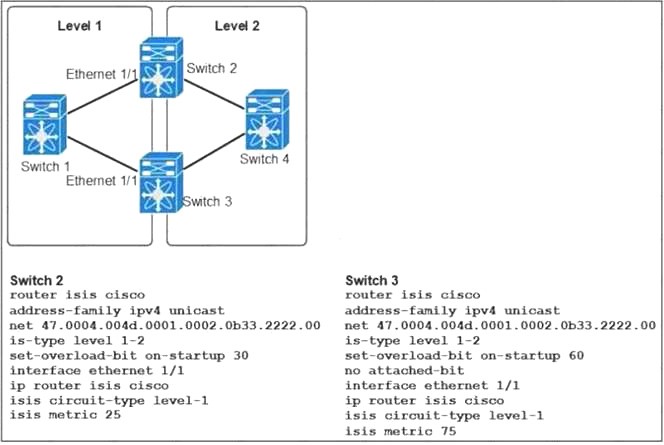
How does Switch 1 route traffic to the Level 2 network?
- A. Switch 1 prefers Switch 2 as the path to the Level 2 network.
- B. Switch 1 load balances traffic destined for Level 2 between Switch 2 and Switch.
- C. Switch 1 sends 75 percent of the traffic destined for Level 2 to Switch 3 and 25 percent to Switch 2.
- D. Switch 1 prefers Switch 3 as the oath to the Level 2 networ
Answer: A
NEW QUESTION 12
Refer to the exhibit,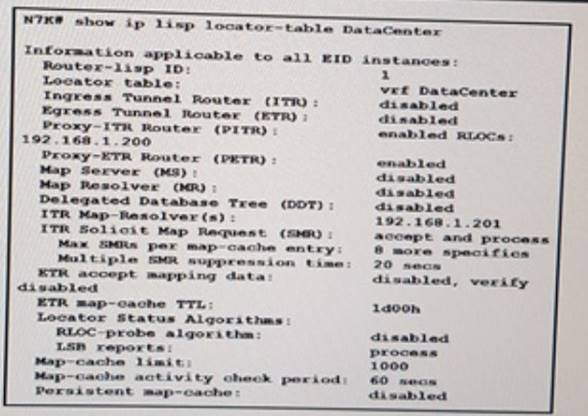
Which description of the output is true?
- A. The default map-cache limit is used.
- B. PETR is disable
- C. The table output apply to the default VRF
- D. The switch acts as an IPv4 LISP ETR
Answer: A
NEW QUESTION 13
When configuring HSRP on IPv6-enabled interfaces, which two commands are required? (Choose
two)
- A. SwitchA(config-if)# hsrp version 2
- B. SwitchA(config-if)# hsrp <group-number> ipv6
- C. SwitchA(config-if># key 6
- D. SwitchA(config-if)# standby 6 preempt
- E. SwitchA(config-if)#priority <level>
Answer: AB
Explanation:
https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/ipapp_fhrp/configuration/15-sy/fhp-15-sybook/ ip6-fhrp-hsrp.html#topic_BC3E645261274DE6B46AA7F2A8E70048
NEW QUESTION 14
You plan to configure a SAN zone set. Which two facts should you consider before you configure the SAN zone set? (Choose two)
- A. VSANs can be activated by using enhanced zoning.
- B. A SAN zone set consists of one or more SAN zones.
- C. A SAN zone set must be activated manually on all of the fabric nodes.
- D. Only the SAN zone set can be activated simultaneously.
- E. One SAN zone can be the member of only one zone se
Answer: BE
NEW QUESTION 15
When a local RBAC user account has the same name as a remote user account on an AAA server, what happens when a user with that name logs into a Cisco Nexus switch?
- A. The user roles from the remote AAA user account are applied, not the configured local user roles.
- B. All the roles are merged (logical OR).
- C. The user roles from the local user account are applied, not the remote AAA user roles.
- D. Only the roles that are defined on both accounts are merged (logical AND).
Answer: C
Explanation:
If you have a user account configured on the local Cisco NX-OS device that has the same name as a remote user account on an AAA server, the Cisco NX-OS software applies the user roles for the local user account to the remote user, not the user roles configured on the AAA server.
Reference: http://www.cisco.com/c/en/us/td/docs/switches/datacenter/sw/4_1/nxos/ security/configuration/guide/sec_nx-os-cfg/sec_rbac.html
NEW QUESTION 16
A Cisco Nexus 2000 Series Fabric Extender is connected to two Cisco Nexus 5000 Series switches via a vPC link. After both Cisco Nexus 5000 Series switches lose power, only one switch is able to power back up. At this time, the Cisco Nexus 2000 Series Fabric Extender is not active and the vPC ports are unavailable to the network.
Which action will get the Cisco Nexus 2000 Series Fabric Extender active when only one Cisco Nexus 5000 Series switch is up and active?
- A. Move the line from the failed Cisco Nexus 5000 Series switch to the switch that is powered on, so the port channel forms automatically on the switch that is powered on.
- B. Shut down the peer link on the Cisco Nexus 5000 Series switch that is powered on.
- C. Configure reload restore or auto-recovery reload-delay on the Cisco Nexus 5000 Series switch that is powered on.
- D. Power off and on the Cisco Nexus 2000 Series Fabric Extender so that it can detect only one Cisco Nexus 5000 Series switch at power up.
Answer: C
Explanation:
The vPC consistency check message is sent by the vPC peer link. The vPC consistency check cannot be
performed when the peer link is lost. When the vPC peer link is lost, the operational secondary switch suspends all of its vPC member ports while the vPC member ports remain on the operational primary switch. If the vPC member ports on the primary switch flaps afterwards (for example, when the switch or server that connects to the vPC primary switch is reloaded), the ports remain down due to the vPC consistency check and you cannot add or bring up more vPCs.
Beginning with Cisco NX-OS Release 5.0(2)N2(1), the auto-recovery feature brings up the vPC links when one peer is down. This feature performs two operations:
• If both switches reload, and only one switch boots up, auto-recovery allows that switch to assume the role of the primary switch. The vPC links come up after a configurable period of time if
the vPC peer-link and the peer-keepalive fail to become operational within that time. If the peer-link comes up but the peer-keepalive does not come up, both peer switches keep the vPC links down. This feature is similar to the reload restore feature in Cisco NX-OS Release 5.0(2)N1(1) and earlier releases. The reload delay period can range from 240 to 3600 seconds.
• When you disable vPCs on a secondary vPC switch because of a peer-link failure and then the primary vPC switch fails, the secondary switch reenables the vPCs. In this scenario, the vPC waits for three consecutive keepalive failures before recovering the vPC links.
Reference: http://www.cisco.com/c/en/us/td/docs/switches/datacenter/nexus5000/sw/operations/n5k_vpc_op s.html
NEW QUESTION 17
Which statement about electronic programmable logic device image upgrades is true?
- A. EPLD and ISSU image upgrades are nondisruptive.
- B. An EPLD upgrade must be performed during an ISSU system or kickstart upgrade.
- C. Whether the module being upgraded is online or offline, only the EPLD images that have different current and new versions are upgraded.
- D. You can execute an upgrade or downgrade only from the active supervisor modul
Answer: D
Explanation:
You can upgrade (or downgrade) EPLDs using CLI commands on the Nexus 7000 Series device. Follow these guidelines when you upgrade or downgrade EPLDs:
• You can execute an upgrade from the active supervisor module only. All the modules, including the active supervisor module, can be updated individually.
• You can individually update each module whether it is online or offline as follows:
– If you upgrade EPLD images on an online module, only the EPLD images with version numbers that differ from the new EPLD images are upgraded.
– If you upgrade EPLD images on an offline module, all of the EPLD images are upgraded.
• On a system that has two supervisor modules, upgrade the EPLDs for the standby supervisor and then switch the active supervisor to standby mode to upgrade its EPLDs. On a system that has only one supervisor module, you can upgrade the active supervisor, but this will disrupt its operations during the upgrade.
• If you interrupt an upgrade, you must upgrade the module that is being upgraded again.
• The upgrade process disrupts traffic on the targeted module.
• Do not insert or remove any modules while an EPLD upgrade is in progress. Reference:
http://www.cisco.com/c/en/us/td/docs/switches/datacenter/sw/4_0/epld/release/notes/epld_rn.ht ml
NEW QUESTION 18
DRAG DROP
Drag and drop the spanning tree types on the left to their correct descriptions on the right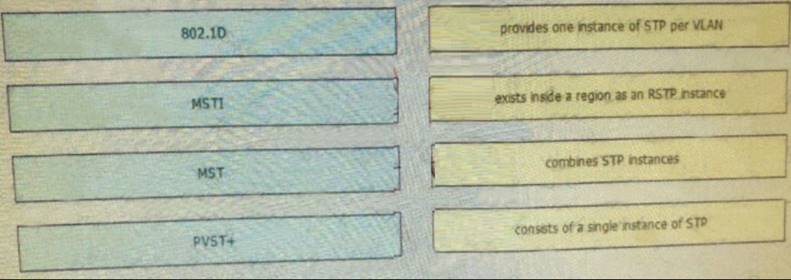
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 
NEW QUESTION 19
Refer to the exhibit.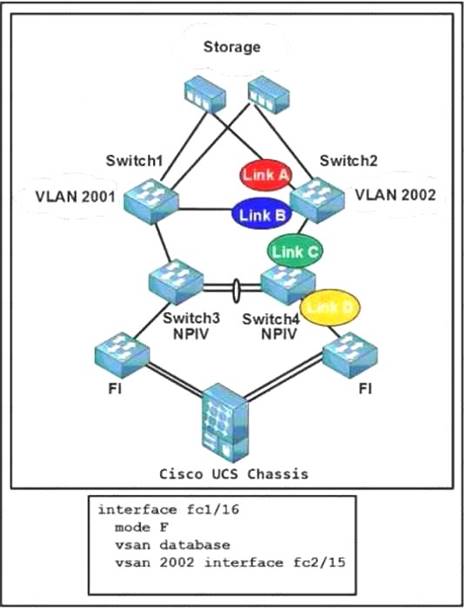
The configuration belongs to which link?
- A. Link A on Switch2
- B. Link B on Switch2
- C. Link C on Switch4
- D. Link D on Switch4
Answer: D
NEW QUESTION 20
Which two statements are true when performing a SPAN capture of traffic reaching the Supervisor CPU in order to troubleshoot control plane protocols in the tenant VDC? (Choose two.)
- A. The destination interface will also receive control plane traffic from other VDCs.
- B. The SPAN configuration must be added to the default or administrative VDC.
- C. SPAN only supports monitoring of ingress traffic to the supervisor.
- D. Captured traffic from the supervisor can be shown directly on the terminal.
- E. Only monitoring of egress traffic from the supervisor is possibl
Answer: BD
NEW QUESTION 21
Which three options are capabilities of the Cisco Nexus 7000 Series Supervisor Module? (Choose three.)
- A. hardware forwarding on the supervisor module
- B. fully decoupled control plane and data plane with no forwarding on the supervisor module
- C. Sup2 requires Cisco NX-OS 5.1 or later.
- D. Sup2 requires Cisco NX-OS 6.1 or later.
- E. Sup2E supports 8+1 VDC with the N7K-VDC1K9 license per chassis.
- F. Sup2 supports 8+1 VDCs with the N7K-VDC1K9 license per chassi
Answer: BDE
NEW QUESTION 22
Which statement about scalability in Cisco OTV is true?
- A. The control plane avoids flooding by exchanging MAC reachability.
- B. IP-based functionality provides Layer 3 extension over any transport.
- C. Any encapsulation overhead is avoided by using IS-IS.
- D. Unknown unicasts are handled by the authoritative edge devic
Answer: A
Explanation:
Cisco calls the underlying concept of OTV traffic forwarding "MAC routing", since it behaves as if you are routing Ethernet frames over the DCI transport. OTV uses a control plane protocol to proactively propagate MAC address reachability before traffic is allowed to pass, which eliminates dependency
on flooding mechanism to either learn MAC addresses or forward unknown unicasts. Reference:
http://www.computerworld.com/article/2515468/data-center/layer-2-data-center-interconnectoptions. html
NEW QUESTION 23
Which protocol is used to exchange MAC address reachability between OTV-enabled switches?
- A. EIGRP
- B. IS-IS
- C. iBGP
- D. RIPv2
Answer: B
NEW QUESTION 24
Which features must be enabled to implement manual MACsec?
- A. CTS and dot1x
- B. MSDP and dot1x
- C. CTS and MSDP
- D. CTS and private VLAN
Answer: A
NEW QUESTION 25
What is the purpose of the resequence command for ACLs?
- A. to rearrange the order of the access lists in the running configuration
- B. to assign new sequence numbers to the rules in an ACL
- C. to refresh ACI programming in ASICs to apply the ACL changes
- D. to rearrange ACL entries
Answer: B
Explanation:
https://www.cisco.com/c/en/us/td/docs/switches/datacenter/sw/4_1/nxos/security/configuration/guide/sec_nx-os-cfg/sec_macacls.pdf
NEW QUESTION 26
In policy-based routing, which action is taken for packets that do not match any of the route-map statements?
- A. forwarded after the egress queue empties on the outbound interface
- B. forwarded using the last statement in the route map
- C. forwarded using the closest matching route-map statement
- D. forwarded using destination-based routing
Answer: D
Explanation:
Each entry in a route map contains a combination of match and set statements. The match statements define the criteria for whether appropriate packets meet the particular policy (that is, the conditions to be met). The set clauses explain how the packets should be routed once they have met the match criteria.
You can mark the route-map statements as permit or deny. You can interpret the statements as follows:
• If the statement is marked as permit and the packets meet the match criteria, the set clause is applied. One of these actions involves choosing the next hop.
• If a statement is marked as deny, the packets that meet the match criteria are sent back through the normal forwarding channels, and destination-based routing is performed.
• If the statement is marked as permit and the packets do not match any route-map statements, the packets are sent back through the normal forwarding channels, and destination-based routing is performed.
Reference: http://www.cisco.com/c/en/us/td/docs/switches/datacenter/nexus9000/sw/7-x/unicast/configuration/guide/l3_cli_nxos/l3pbr.pdf
NEW QUESTION 27
Which of the following Cisco Nexus features is best managed with DCNM-LAN?
- A. VSS
- B. Domain parameters
- C. Virtual switches
- D. AAA
Answer: C
Explanation:
DCNM-LAN supports the following platforms:
• Cisco Nexus 1000V switches
• Cisco Nexus 2000 Fabric Extenders
• Cisco Nexus 3000 Series switches
• Cisco Nexus 4000 Series switches
• Cisco Nexus 5000 Series switches
• Catalyst 6500
DCNM-LAN provides limited support for the Catalyst 6500 Series switches that runs classic IOS version 12.2(33)SXI or higher.
– DCNM-LAN supports the viewing of the current configuration attributes of the device.
– DCNM-LAN does not support changing the configuration of the device.
– DCNM-LAN supports the Firewall Service Module (FWSM) version 4.0 or higher for the Catalyst 6500 Series switches.
• Cisco Nexus 7000 Series switches Reference:
http://www.cisco.com/c/en/us/td/docs/switches/datacenter/mds9000/sw/5_2/configuration/guides
/fund/DCNM-SAN-LAN_5_2/DCNM_Fundamentals/fund_overview.html
NEW QUESTION 28
......
Recommend!! Get the Full 300-165 dumps in VCE and PDF From prep-labs.com, Welcome to Download: https://www.prep-labs.com/dumps/300-165/ (New 303 Q&As Version)