100% Guarantee 300-210 Braindumps 2021
Proper study guides for 300-210 Implementing Cisco Threat Control Solutions (SITCS) certified begins with preparation products which designed to deliver the by making you pass the 300-210 test at your first time. Try the free right now.
Online Cisco 300-210 free dumps demo Below:
NEW QUESTION 1
Drag and drop the Cisco Security IntelliShield Alert Manager Service components on the left onto the corresponding description on the right.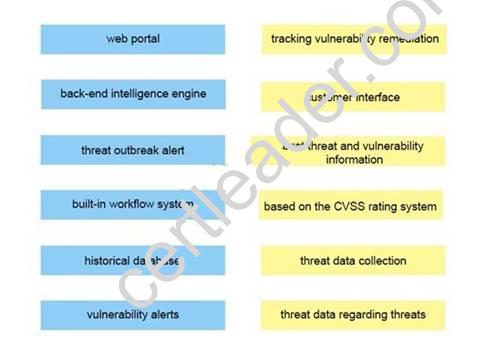
Answer:
Explanation: 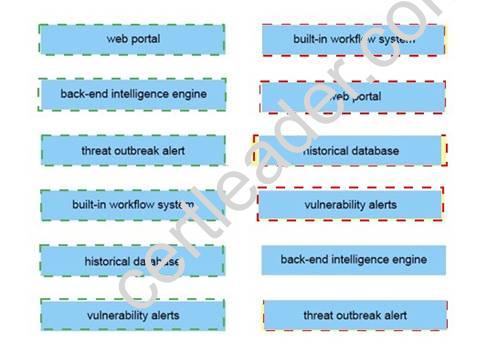
NEW QUESTION 2
Which option lists the minimum requirements to deploy a managed device inline?
- A. passive interface, security zone, MTU, and link mode.
- B. passive interface, MTU, MDI/MDIX, and link mode.
- C. inline interfaces, MTU, MDI/MDIX, and link mode.
- D. inline interfaces, security zones, MTU, and link mode.
Answer: A
NEW QUESTION 3
What is a value that Cisco ESA can use for tracing mail flow?
- A. the FQDN of the source IP address
- B. the FQDN of the destination IP address
- C. the destination IP address
- D. the source IP address
Answer: A
NEW QUESTION 4
Refer to the exhibit.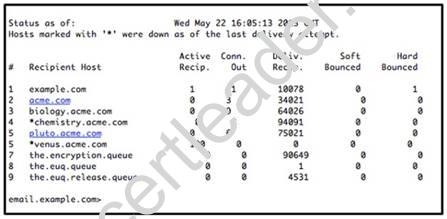
What Cisco ESACLI command generated the output?
- A. smtproutes
- B. tophosts
- C. hoststatus
- D. workqueuestatus
Answer: B
NEW QUESTION 5
To enable the Cisco ASA Host Scan with remediation capabilities, an administrator must have which two Cisco ASA licenses enabled on its security appliance? (Choose two.)
- A. Cisco AnyConnect Premium license
- B. Cisco AnyConnect Essentials license
- C. Cisco AnyConnect Mobile license
- D. Host Scan license
- E. Advanced Endpoint Assessment license
- F. Cisco Security Agent license
Answer: AE
NEW QUESTION 6
Which website can be used to validate group information about connections that flow through Cisco CWS?
- A. whoami.scansafe.com
- B. policytrace.scansafe.com
- C. policytrace.scansafe.net
- D. whoami.scansafe.net
Answer: C
NEW QUESTION 7
An engineer wants to configure a method to verify the authenticity of emails on cisco ESA and noticed the sender policy framework. How can the SPF help in that task?
- A. SPF allows the sender to sign the email using presharekey
- B. SPF allows the sender to sign the email using public key
- C. SPF allow the owner of internal domain to use DNS record which machines are
Answer: B
NEW QUESTION 8
Which command disables SSH access for administrators on the Cisco ESA?
- A. interfaceconfig
- B. sshconfig
- C. sslconfig
- D. systemsetup
Answer: A
NEW QUESTION 9
Which two configuration steps are required for implementing SSH for management access to a Cisco router? (Choose two.)
- A. Configuring the SSH version with the ip ssh version 2 command.
- B. Generating RSA key pairs with the crypto key generate rsa command.
- C. Enabling AAA for authentication, authorization, and accounting with the aaa new-model command.
- D. Enabling SSH transport with the transport input ssh command.
- E. Configuring a domain name with the ip domain-name [name] command.
Answer: DE
Explanation:
Reference: http://www.cisco.com/c/en/us/support/docs/security-vpn/secure-shell-ssh/4145ssh.html
NEW QUESTION 10
Access the configuration of the Cisco Email Security Appliance using the MailFlowPolicies tab. Within the GUI, you can navigate between the Host Access Table Overview and Mail Flow Policies tables. You can also navigate to the individual Mail Flow Policies and Sender Groups that are configured on the appliance.
Consider the configuration and the SenderBase Reputation Scores of the following fictitious domains when answering the four multiple choice questions.
- A. red.public, -6
- B. orange.public, -4
- C. yellow.public, -2
- D. gree
- E. .public, 2
- F. blue.public, 6
- G. violet.public, 8
Answer: D
NEW QUESTION 11
Which three options are IPS signature classifications? (Choose three.)
- A. tuned signatures
- B. response signatures
- C. default signatures
- D. custom signatures
- E. preloaded signatures
- F. designated signatures
Answer: ACD
NEW QUESTION 12
Which Cisco technology is a customizable web-based alerting service designed to report threats and vulnerabilities?
- A. Cisco Security Intelligence Operations
- B. Cisco Security IntelliShield Alert Manager Service
- C. Cisco Security Optimization Service
- D. Cisco Software Application Support Service
Answer: B
NEW QUESTION 13
Joe was asked to secure access to the Cisco Web Security Appliance to prevent unauthorized access. Which four steps should Joe implement to accomplish this goal? (Choose four.)
- A. Implement IP access lists to limit access to the management IP address in the Cisco Web Security Appliance GUI.
- B. Add the Cisco Web Security Appliance IP address to the local access list.
- C. Enable HTTPS access via the GUI/CLI with redirection from HTTP.
- D. Replace the Cisco self-signed certificate with a publicly signed certificate.
- E. Put the Cisco WSA Management interface on a private management VLAN.
- F. Change the netmask on the Cisco WSA Management interface to a 32-bit mask.
- G. Create an MX record for the Cisco Web Security Appliance in DNS.
Answer: ACDE
NEW QUESTION 14
A web security appliance is inspecting inbound traffic. In which sequence is inbound https traffic inspected?
- A. Routing Policy > Decryption Policy > Access Policy
- B. Access Policy > Decryption Policy > Routing Policy
- C. Routing Policy > Access Policy > Decryption Policy
- D. Decryption Policy > Access Policy > Routing Policy
- E. Decryption Policy > Routing Policy > Access Policy
- F. Access Policy > Routing Policy > Decryption Policy
Answer: B
NEW QUESTION 15
Which feature does Acceptable Use Controls use to implement Cisco AVC?
- A. ISA
- B. Cisco Web Usage Controls
- C. Cisco WSA
- D. Cisco ESA
Answer: B
NEW QUESTION 16
Which Cisco IPS deployment mode is best suited for bridged interfaces?
- A. inline interface pair mode
- B. inline VLAN pair mode
- C. inline VLAN group mode
- D. inline pair mode
Answer: B
NEW QUESTION 17
Your corporate finance department purchased a new non-web-based TCP application tool to run on one of its servers. The finance employees need remote access to the software during non- business hours. The employees do not have "admin" privileges to their PCs. How would you configure the SSL VPN tunnel to allow this application to run?
- A. Configure a smart tunnel for the application.
- B. Configure a "finance tool" VNC bookmark on the employee clientless SSL VPN portal.
- C. Configure the plug-in that best fits the application.
- D. Configure the Cisco ASA appliance to download the Cisco AnyConnect SSL VPN client to the financeemployee each time an SSL VPN tunnel is established
Answer: A
P.S. Easily pass 300-210 Exam with 431 Q&As Certleader Dumps & pdf Version, Welcome to Download the Newest Certleader 300-210 Dumps: https://www.certleader.com/300-210-dumps.html (431 New Questions)