Certified 300-210 Exam Questions 2021
Want to know features? Want to lear more about experience? Study . Gat a success with an absolute guarantee to pass Cisco 300-210 (Implementing Cisco Threat Control Solutions (SITCS)) test on your first attempt.
Online Cisco 300-210 free dumps demo Below:
NEW QUESTION 1
Which access control policy action must be selected to inspect traffic for malware using cisco AMP for Networks?
- A. monitor
- B. inspect
- C. trust
- D. allow
Answer: D
NEW QUESTION 2
Which type of interface do you configure to receive traffic from a switch or tap, promiscuously, on a cisco firePOWER device?
- A. inline set
- B. transparent
- C. Routed
- D. Passive
Answer: D
NEW QUESTION 3
Which method does Cisco recommend for collecting streams of data on a sensor that has been virtualized?
- A. VACL capture
- B. SPAN
- C. the Wireshark utility
- D. packet capture
Answer: D
NEW QUESTION 4
When does the Cisco ASA send traffic to the Cisco ASA IPS module for analysis?
- A. before firewall policy are applied
- B. after outgoing VPN traffic is encrypted
- C. after firewall policies are applied
- D. before incoming VPN traffic is decrypted.
Answer: C
NEW QUESTION 5
A new Cisco IPS device has been placed on the network without prior analysis. Which CLI command shows the most fired signature?
- A. Show statistics virtual-sensor
- B. Show event alert
- C. Show alert
- D. Show version
Answer: A
NEW QUESTION 6
Which sensor deployment mode does Cisco recommend when interface capacity is limited and you need to increase sensor functionality?
- A. inline interface pair mode
- B. inline VLAN pair mode
- C. inline VLAN group mode
- D. VLAN group mode
Answer: C
NEW QUESTION 7
Troubleshoot command for NGIPSv.
- A. system generate-troubleshoot all
- B. sudo sf_troubleshoot.pl
Answer: A
NEW QUESTION 8
The Web Cache Communication Protocol (WCCP) is a content-routing protocol that can facilitate the redirection of traffic flows in real time. Your organization has deployed WCCP to redirect web traffic that traverses their Cisco Adaptive Security Appliances (ASAs) to their Cisco Web Security Appliances (WSAs).
The simulator will provide access to the graphical user interfaces of one Cisco ASA and one Cisco WSA that are participating in a WCCP service. Not all aspects of the GUIs are implemented in the simulator. The options that have been implemented are sufficient to determine the best answer to each of the questions that are presented.
Your task is to examine the details available in the simulated graphical user interfaces and select the best answer.
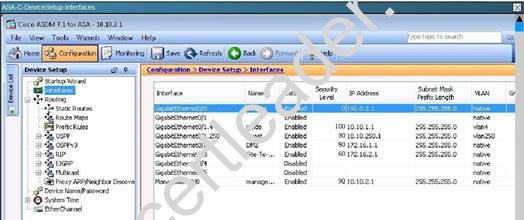
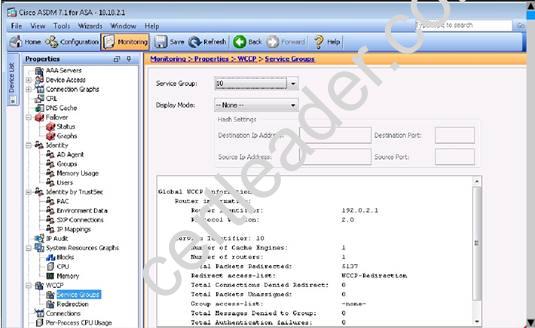
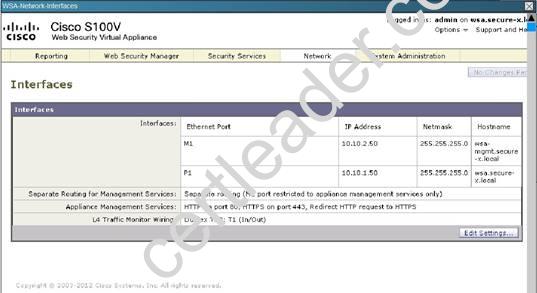
How many Cisco ASAs and how many Cisco WSAs are participating in the WCCP service?
- A. One Cisco ASA or two Cisco ASAs configured as an Active/Standby failover pair, and one Cisco WSA.
- B. One Cisco ASA or two Cisco ASAs configured as an Active/Active failover pair, and one Cisco WSA.
- C. One Cisco ASA or two Cisco ASAs configured as an Active/Standby failover pair, and two Cisco WSAs.
- D. One Cisco ASA or two Cisco ASAs configured as an Active/Active failover pair, and two Cisco WSAs.
- E. Two Cisco ASAs and one Cisco WSA.
- F. Two Cisco ASAs and two Cisco WSAs.
Answer: A
Explanation: We can see from the output that the number of routers (ASA’s) is 1, so there is a single ASA or an active/ standby pair being used, and 1 Cache Engine. If the ASA’s were in a active/active role it would show up as 2 routers.
NEW QUESTION 9
Which Cisco monitoring solution displays information and important statistics for the security devices in a network?
- A. Cisco Prime LAN Management
- B. Cisco ASDM Version 5.2
- C. Cisco Threat Defense Solution
- D. Syslog Server
- E. TACACS+
Answer: B
NEW QUESTION 10
What are three best practices for a Cisco Intrusion Prevention System? (Choose three.)
- A. Checking for new signatures every 4 hours
- B. Checking for new signatures on a staggered schedule
- C. Automatically updating signature packs
- D. Manually updating signature packs
- E. Group tuning of signatures
- F. Single tuning of signatures
Answer: BCE
NEW QUESTION 11
Cisco AVC allows control of which three of the following? (Choose three.)
- A. Facebook
- B. LWAPP
- C. IPv6
- D. MySpace
- E. Twitter
- F. WCCP
Answer: ADE
NEW QUESTION 12
Which two conditions must you configure in an event action rule to match all IPv4 addresses in the victim range and filter on the complete subsignature range? (Choose two.)
- A. Disable event action override.
- B. Leave the victim address range unspecified.
- C. Set the subsignature ID-range to the default.
- D. Set the deny action percentage to 100.
- E. Set the deny action percentage to 0.
Answer: BC
NEW QUESTION 13
When attempting to tunnel FTP traffic through a stateful firewall that may be performing NAT or PAT, which type of VPN tunneling should be used to allow the VPN traffic through the stateful firewall?
- A. clientless SSL VPN
- B. IPsec over TCP
- C. Smart Tunnel
- D. SSL VPN plug-ins
Answer: B
NEW QUESTION 14
In a Cisco AMP for Networks deployment, which disposition is returned if the cloud cannot be reached?
- A. clean
- B. disconnected
- C. unavailable
- D. unknown
Answer: C
NEW QUESTION 15
Which command is used to enable strong ciphers on the Cisco Web Security Appliance?
- A. interfaceconfig
- B. strictssl
- C. etherconfig
- D. adminaccessconfig
Answer: B
NEW QUESTION 16
What command alters the SSL ciphers used by the Cisco Email Security Appliance for TLS sessions and HTTPS access?
- A. sslconfig
- B. sslciphers
- C. tlsconifg
- D. certconfig
Answer: A
NEW QUESTION 17
Which port is used for CLI Secure shell access?
- A. Port 23
- B. Port 25
- C. Port 22
- D. Port 443
Answer: C
100% Valid and Newest Version 300-210 Questions & Answers shared by 2passeasy, Get Full Dumps HERE: https://www.2passeasy.com/dumps/300-210/ (New 431 Q&As)