Cisco 300-210 Exam Questions and Answers 2021
are updated and are verified by experts. Once you have completely prepared with our you will be ready for the real 300-210 exam without a problem. We have . PASSED First attempt! Here What I Did.
Online 300-210 free questions and answers of New Version:
NEW QUESTION 1
Which of the following are Cisco FirePOWER Application Layer Preprocessors? (Choose 2).
- A. SIP preprocessor
- B. HTTP preprocessor
- C. ICMP preprocessor
- D. Modbus
Answer: AB
NEW QUESTION 2
Which two appliances support logical routed interfaces? (Choose two.)
- A. FirePOWER services for ASA-5500-X
- B. FP-4100-series
- C. FP-8000-series
- D. FP-7000-series
- E. FP-9300-series
Answer: D
NEW QUESTION 3
Which option describes device trajectory on Cisco Advanced Matware Protection for Endpoints?
- A. It shows the file path on a host.
- B. It shows a full packet capture of the file.
- C. It shows which devices on the network received the file.
- D. It shows what a file did on a host.
Answer: C
NEW QUESTION 4
Which command can change the HTTPS SSL method on the Cisco ESA?
- A. sslconfig
- B. strictssl
- C. sshconfig
- D. adminaccessconfig
Answer: A
NEW QUESTION 5
Which option describes a customer benefit of the Cisco Security IntelliShield Alert Manager?
- A. It provides access to threat and vulnerability information for Cisco related products only.
- B. It consolidates vulnerability information from an internal Cisco source, which allows security personnel to focus on remediation and proactive protection versus research.
- C. It provides effective and timely security intelligence via early warnings about new threats and technology vulnerabilities.
- D. It enhances the efficiency of security staff with accurate, noncustomizable threat intelligence, critical remediation information, and easy-to-use workflow tools.
Answer: C
NEW QUESTION 6
Which statement regarding hashing is correct?
- A. MD5 produces a 64-bit message digest
- B. SHA-1 produces a 160-bit message digest
- C. MD5 takes more CPU cycles to compute than SHA-1.
- D. Changing 1 bit of the input to SHA-1 can change up to 5 bits in the output.
Answer: B
NEW QUESTION 7
Which cloud-based malware detection engine uses machine-learning detection techniques in the Cisco Advanced Malware Protection cloud?
- A. third-party detections
- B. Spero
- C. Ethos
- D. Memcache
Answer: B
NEW QUESTION 8
Who or what calculates the signature fidelity rating in a Cisco IPS?
- A. the signature author
- B. Cisco Professional Services
- C. the administrator
- D. the security policy
Answer: A
NEW QUESTION 9
Which three administrator actions are used to configure IP logging in Cisco IME? (Choose three.)
- A. Select a virtual sensor.
- B. Enable IP logging.
- C. Specify the host IP address.
- D. Set the logging duration.
- E. Set the number of packets to capture.
- F. Set the number of bytes to capture.
Answer: ACD
NEW QUESTION 10
Which three options are valid event actions for a Cisco IPS? (Choose three.)
- A. deny-packet-inline
- B. deny-attack-reset
- C. produce-verbose-alert
- D. log-attacker-packets
- E. deny-packet-internal
- F. request-block-drop-connection
Answer: ACD
NEW QUESTION 11

For which domains will the Cisco Email Security Appliance allow up to 5000 recipients per message?
- A. viole
- B. public
- C. viole
- D. public and blu
- E. public
- F. viole
- G. Public, blu
- H. Public and green.public
- I. re
- J. public orang
- K. publicre
- L. public and orang
- M. public
Answer: B
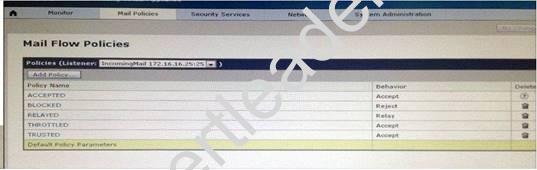
NEW QUESTION 12
An engineer is configuring a Cisco Email Security Appliance (ESA) and chooses "Preferred" as the settings for TLS on a HAT Mail Flow Policy. Which result occurs?.
- A. TLS is allowed for outgoing connections to MTA
- B. Connection to the listener require encrypted Simp Mail Transfer Protocol conversations
- C. TLS is allowed for incoming connections to the listener from MTAs, even after a STARTTLS command received
- D. TLS is allowed for incoming connections to the listener from MTA
- E. Until a STARTTLS command received, the ESA responds with an error message to every command other than No Option, EHLO, or QUIT.
- F. TLS is allowed for outgoing connections to the listener from MTA
- G. Until a STARTTLS command received, the ESA responds with an error message to every command other than No Option (NOOP), EHLO, or QUIT.
Answer: D
NEW QUESTION 13
Which two routing options are valid with cisco firePOWER threat Defense version 6.0?(choose two)
- A. ECMP with up to three equal cost paths across multiple interfaces
- B. BGPv6
- C. BGPv4 with nonstop forwarding
- D. BGPv4 unicast address family
- E. ECMP with up to four equal cost paths
Answer: AD
NEW QUESTION 14
What FirePOWER protocol provides gateway redundancy for IPv4 and IPv6 addresses on routed or hybrid interfaces?
- A. ECLB
- B. SFRP
- C. OSPF
- D. WCCP
Answer: B
Explanation: Explanation
SFRPYou can configure Cisco Redundancy Protocol (SFRP) to achieve network redundancy for high availability on either a 7000 or 8000 Series device high-availability pair or individual devices. SFRP provides gateway redundancy for both IPv4 and IPv6 addresses. You can configure SFRP on routed and hybrid interfaces.If the interfaces are configured on individual devices, they must be in the same broadcast domain. You must designate at least one of the interfaces as master and an equal number as backup. The system supports only one master and one backup per IP address. If network connectivity is lost, the system automatically promotes the backup to master to maintain connectivity.The options you set for SFRP must be the same on all interfaces in a group of SFRP interfaces. Multiple IP addresses in a group must be in the same master/ backup state. Therefore, when you add or edit an IP address, the state you set for that address propagates to all the addresses in the group. For security purposes, you must enter values for Group ID and Shared Secret that are shared among the interfaces in the group.To enable SFRP IP addresses on a virtual router, you must also configure at least one non-SFRP IP address.For 7000 or 8000 Series devices in a
high-availability pair, you designate the shared secret and the system copies it to the high-availability pair peer along with the SFRP IP configuration.
NEW QUESTION 15
During initial configuration, the Cisco ASA can be configured to drop all traffic if the ASACX SSP fails by using which command in a policy-map?
- A. cxsc fail
- B. cxsc fail-close
- C. cxsc fail-open
- D. cxssp fail-close
Answer: B
NEW QUESTION 16
A user is deploying a Cisco IPS appliance in a data center to mitigate most attacks, including atomic attacks. Which two modes does Cisco recommend using to configure for this? (Choose two.)
- A. VLAN pair
- B. interface pair
- C. transparent mode
- D. EtherChannel load balancing
- E. promiscuous mode
Answer: AD
NEW QUESTION 17
Which three sender reputation ranges identify the default behavior of the Cisco Email Security Appliance? (Choose three.)
- A. If it is between -1 and +10, the email is accepted
- B. If it is between +1 and +10, the email is accepted
- C. If it is between -3 and -1, the email is accepted and additional emails from the sender are throttled
- D. If it is between -3 and +1, the email is accepted and additional emails from the sender are throttled
- E. If it is between -4 and +1, the email is accepted and additional emails from the sender are throttled
- F. If it is between -10 and -3, the email is blocked
- G. If it is between -10 and -3, the email is sent to the virus and spam engines for additional scanning
- H. If it is between -10 and -4, the email is blocked
Answer: ACF
100% Valid and Newest Version 300-210 Questions & Answers shared by Surepassexam, Get Full Dumps HERE: https://www.surepassexam.com/300-210-exam-dumps.html (New 431 Q&As)