Update CompTIA Network+ N10-006 Free Practice Test
Master the N10-006 CompTIA Network+ content and be ready for exam day success quickly with this Actualtests N10-006 book. We guarantee it!We make it a reality and give you real N10-006 questions in our CompTIA N10-006 braindumps.Latest 100% VALID CompTIA N10-006 Exam Questions Dumps at below page. You can use our CompTIA N10-006 braindumps and pass your exam.
Also have N10-006 free dumps questions for you:
NEW QUESTION 1
A network technician is configuring a wireless network. To avoid interference from other wireless networks in the area, the technician should change which setting?
- A. Channel
- B. SSID
- C. Firewall rule
- D. Encryption
Answer: A
NEW QUESTION 2
Workers in a company branch office are required to click on an initial web page and agree to have web surfing mentioned. This is an example of:
- A. an end-user license agreement
- B. an SLA
- C. an AUP
- D. an MOU
Answer: C
Explanation:
https://en.wikipedia.org/wiki/Acceptable_use_policy
NEW QUESTION 3
An administrator needs to set up a space in the office where co-workers can relax. The administrator sets up several TV's with interconnected gaming systems in the office. Which of the following did the administrator set up?
- A. CAN
- B. MAN
- C. WAN
- D. LAN
Answer: A
NEW QUESTION 4
An organization is upgrading the operating system on several servers and wants to keep legacy input devices. Which of the following needs to be verified before the upgrade to ensure the input devices will be supported after the upgrade?
- A. Driver updates
- B. Virtual terminals
- C. Firmware updates
- D. IP address assignments
Answer: A
NEW QUESTION 5
A network technician is diligent about maintaining all system servers' at the most current service pack level available. After performing upgrades, users experience issues with server-based applications. Which of the following should be used to prevent issues in the future?
- A. Configure an automated patching server
- B. Virtualize the servers and take daily snapshots
- C. Configure a honeypot for application testing
- D. Configure a test lab for updates
Answer: D
Explanation:
To prevent the service pack issues make sure, before going ahead and applying a new Service Pack in your production environment, to validate them in a test/lab environment first.
NEW QUESTION 6
Which of the following is a logical host on the network where unauthorized users believe they are on the production network?
- A. Virtual server
- B. VLAN
- C. Honeypot
- D. Virtual Terminal
Answer: C
NEW QUESTION 7
Which of the following protocols utilizes 3DES encryption by default?
- A. GRE
- B. PPTP
- C. STP
- D. IPSec
Answer: D
Explanation:
https://support.microsoft.com/en-us/kb/325158
NEW QUESTION 8
A company has decided to upgrade its legacy phone system to VoIP. The new phones will download the configurations from a TFTP server each time they boot up. Which of the following firewall ports must be opened to ensure the phones can communicate with the server?
- A. 20
- B. 53
- C. 69
- D. 161
Answer: C
Explanation:
https://en.wikipedia.org/wiki/Trivial_File_Transfer_Protocol
NEW QUESTION 9
An administrator is replacing an existing WAP because the customer is reporting that the connection speeds are too slow. Which of the following should be installed?
- A. 802.11a
- B. 802.11b
- C. 802.11g
- D. 802.11n
Answer: D
NEW QUESTION 10
A technician has responded to a security issue with an employee's computer. Which of the following basic forensic steps should be taken NEXT?
- A. Secure the area
- B. Initiate Data collection
- C. Create the forensics report
- D. Verify thechain of custody
Answer: A
NEW QUESTION 11
A network technician has set up an FTP server for the company to distribute software updates for their products. Each vendor is provided with a unique username and password for security. Several vendors have discovered a virus in one of the security updates. The company tested all files before uploading them but retested the file and found the virus. Which of the following could the technician do for vendors to validate the proper security patch?
- A. Use TFTP for tested and secure downloads
- B. Require biometric authentication for patch updates
- C. Provide an MD5 hashfor each file
- D. Implement a RADIUS authentication
Answer: C
Explanation:
If we put an MD5 has for each file we can see if the file has been changed or not.
MD5 is an algorithm that is used to verify data integrity through the creation of a 128-bit message digest from data input (which may be a message of any length) that is claimed to be as unique to that specific data as a fingerprint is to the specific individual.
NEW QUESTION 12
A user is unable to log into the network successfully. Which of the following are steps of the troubleshooting methodology used to identify the problem? (Select TWO).
- A. Use troubleshooting tools
- B. Document actions
- C. Duplicate problem
- D. Identify effects of resolution
- E. Question users
Answer: BE
NEW QUESTION 13
A PC technician has installed a new network printer that was preconfigured with the correct static IP address, subnet mask, and default gateway. The printer was installed with a new cable and appears to have link activity, but the printer will not respond to any network communication attempts. Which of the following is MOST likely the cause of the problem?
- A. Damaged cable
- B. Duplex mismatch
- C. Incorrect VLAN assignment
- D. Speed mismatch
Answer: C
Explanation:
If a port is accidentally assigned to the wrong VLAN in a switch, it’s as if that client was magicallytransported to another place in the network. This would explain the inability to communication with the printer, as it is on a different VLAN.
NEW QUESTION 14
Which of the following allows a technician to gather information about the operating system?
- A. Domain services
- B. Fingerprinting
- C. Countermeasures
- D. Reconnaissance
Answer: B
NEW QUESTION 15
Kim, a user, took a laptop on vacation and made changes to the configuration in order to use the device at the hotel. She can reach the Internet, but cannot access any internal network resources.
Which of the following is the MOST likely reason?
- A. Incorrect DNS
- B. Incorrect subnet mask
- C. Duplicate IP address
- D. Incorrect SSID
Answer: A
NEW QUESTION 16
Which of the following WAN technologies is associated with high latency?
- A. T1
- B. Satellite
- C. Cable
- D. OCx
Answer: B
Explanation:
Latency in this instance is the time it takes for the signal to and from the satellite. Since signal has to travel to the satellite, then from the satellite to the ground station, and then out to the Internet (or IP WAN). Not forgetting the return trip, and processing delays.
NEW QUESTION 17
Which of the following is considered a classless routing protocol?
- A. IGRP
- B. IS-IS
- C. RIPv1
- D. STP
Answer: B
NEW QUESTION 18
A web-based application is responding very slowly. The network administrator is looking at the following information from the transparent web proxy, which is configured in virtual-wire
mode and is in the between the company’s network and the Internet.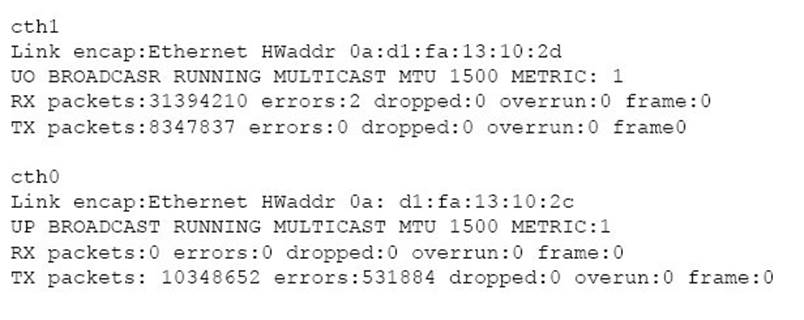
Given the above information, which of the following is the layer of the OSI model at which the issue is occurring and the MOST likely reason it is occurring? (Select two.)
- A. Layer 1
- B. Layer 4
- C. Layer 3
- D. Layer 7
- E. The application crashed
- F. NO IP addresses on interfaces
- G. Excessive TCP resets
- H. Bad cable
Answer: CH
Explanation:
http://www.cisco.com/en/US/docs/internetworking/troubleshooting/guide/tr1907.html https://blog.ruxit.com/detecting-network-errors-impact-on-services/
NEW QUESTION 19
Several users at an adjacent office building report connectivity issues after a new building was built in between the two offices. The network technician has determined the adjacent office building is connected to the main office building via an 802.11ac bridge. The network
technician logs into the AP and confirms the SSID, encryption and channels are all correct. Which of the following is MOST likely the cause of this issue?
- A. Device saturation
- B. Antenna type
- C. Bandwidth saturation
- D. Interference
Answer: D
NEW QUESTION 20
Which of the following ports is used to provide secure sessions over the web by default?
- A. 22
- B. 25
- C. 80
- D. 5004
Answer: A
NEW QUESTION 21
A network technician is tasked with designing a firewall to improve security for an existing FTP server that is on the company network and is accessible from the internet. The security concern is that the FTP server is compromised it may be used as a platform to attack other company servers. Which of the following is the BEST way to mitigate this risk?
- A. Add an outbound ACL to the firewall
- B. Change the FTP server to a more secure SFTP
- C. Use the implicit deny of the firewall
- D. Move the server to the DMZ of the firewall
Answer: D
NEW QUESTION 22
A user receives a new computer and now is unable to connect to a database using ODBC. Other users on the network are able to connect successfully. A technician is able to successfully ping the database server but still is unable to connect. Which of the following is the issue?
- A. Missing IP routes on router
- B. Wrong default gateway address
- C. Software firewall is blocking ports
- D. Failing network interface card
Answer: C
NEW QUESTION 23
A wireless network technician for a local retail store is installing encrypted access points within the store for real-time inventory verification, as well as remote price checking capabilities, while employees are away from the registers. The store is in a fully occupied strip mall that has multiple neighbors allowing guest access to the wireless networks. There are a finite known number of approved handheld devices needing to access the store's wireless network. Which of the following is the BEST security method to implement on the access points?
- A. Port forwarding
- B. MAC filtering
- C. TLS/TTLS
- D. IP ACL
Answer: B
Explanation:
MAC filtering allows traffic to be permitted or denied based on a device’s MAC address. We make a MAC filtering which contains the MAC addresses of all approved devices that need to access the wireless network. This ensures that only approved devices are given access to the network.
NEW QUESTION 24
Which of the following is a UC application?
- A. Softphone
- B. Intranet
- C. Proxy
- D. Facsimile
Answer: A
NEW QUESTION 25
Which of the following technologies is designed to keep systems uptime running in the event of a disaster?
- A. High availability
- B. Load balancing
- C. Quality of service
- D. Caching engines
Answer: A
Explanation:
If a network switch or router stops operating correctly (meaning that a network fault occurs), communication through the network could be disrupted, resulting in a network becoming unavailable to its users. Therefore, network availability, called uptime, is a major design consideration.
NEW QUESTION 26
A technician has verified that a recent loss of network connectivity to multiple workstations is due to a bad CAT5 cable in the server room wall. Which of the following tools can be used to locate its physical location within the wall?
- A. Cable certifier
- B. Multimeter
- C. Cable tester
- D. Toner probe
Answer: D
Explanation:
Toner probes are specifically used to trace cables hidden in floors, ceilings, or walls. They can alsobe used to track cables from the patch panels to their destinations.
NEW QUESTION 27
A new OC3 experiencing intermittent connectivity and loss of signal alarms. A network administrator finds all the cables are properly connected. There is excess cable between the patch panel and the network node. The cables were forced into their storage compartments about the rack. Which of the following is MOST likely cause of the connectivity issue and alarms?
- A. The OC2 was improperly provisioned.
- B. The cable was improperly crimped.
- C. The bend radius of the cable has been exceeded.
- D. The new OC3 cable is experiencing EMI.
Answer: C
NEW QUESTION 28
A network technician has just run a new point-to point fiber link between two local routers, however, after the fiber has been plugged in on both ends, the interface will not come up. The technician has double-checked the interface configuration on both routers, both SFPs have been hard looped to confirm they are functioning, connectors on both ends of the links have been cleaned, and there is sufficient optical power. Which of the following is the cause of the issue?
- A. Wavelength mismatch
- B. Duplex mismatch
- C. Distance limitations
- D. Wrong IP address
Answer: A
NEW QUESTION 29
An Amplitude Modulation (AM) radio station may have a detrimental effect on which of the following services?
- A. DOCSIS
- B. Frame relay
- C. SONET
- D. Metro-Ethernet
Answer: A
NEW QUESTION 30
Which of the following is an IPv6 address?
- A. 00:14:38:05:7B:E5
- B. 10.10.1.1
- C. 192.168.1.1
- D. 2001:cdba::3257:9652
Answer: D
NEW QUESTION 31
......
Recommend!! Get the Full N10-006 dumps in VCE and PDF From DumpSolutions.com, Welcome to Download: https://www.dumpsolutions.com/N10-006-dumps/ (New 742 Q&As Version)