What 100% Guarantee CS0-002 Training Tools Is
Your success in CompTIA CS0-002 is our sole target and we develop all our CS0-002 braindumps in a way that facilitates the attainment of this target. Not only is our CS0-002 study material the best you can find, it is also the most detailed and the most updated. CS0-002 Practice Exams for CompTIA CS0-002 are written to the highest standards of technical accuracy.
Check CS0-002 free dumps before getting the full version:
NEW QUESTION 1
Which of the following software security best practices would prevent an attacker from being able to run arbitrary SQL commands within a web application? (Choose two.)
- A. Parameterized queries
- B. Session management
- C. Input validation
- D. Output encoding
- E. Data protection
- F. Authentication
Answer: AC
NEW QUESTION 2
A security analyst is reviewing a web application. If an unauthenticated user tries to access a page in the application, the user is redirected to the login page. After successful authentication, the user is then redirected back to the original page. Some users have reported receiving phishing emails with a link that takes them to the application login page but then redirects to a fake login page after successful authentication.
Which of the following will remediate this software vulnerability?
- A. Enforce unique session IDs for the application.
- B. Deploy a WAF in front of the web application.
- C. Check for and enforce the proper domain for the redirect.
- D. Use a parameterized query to check the credentials.
- E. Implement email filtering with anti-phishing protection.
Answer: D
NEW QUESTION 3
A security analyst receives an alert that highly sensitive information has left the company's network Upon investigation, the analyst discovers an outside IP range has had connections from three servers more than 100 times m the past month The affected servers are virtual machines Which of the following is the BEST course of action?
- A. Shut down the servers as soon as possible, move them to a clean environment, restart, run a vulnerability scanner to find weaknesses determine the root cause, remediate, and report
- B. Report the data exfiltration to management take the affected servers offline, conduct an antivirus scan, remediate all threats found, and return the servers to service.
- C. Disconnect the affected servers from the network, use the virtual machine console to access the systems, determine which information has left the network, find the security weakness, and remediate
- D. Determine if any other servers have been affected, snapshot any servers found, determine the vector that was used to allow the data exfiltratio
- E. fix any vulnerabilities, remediate, and report.
Answer: A
NEW QUESTION 4
Which of the following will allow different cloud instances to share various types of data with a minimal amount of complexity?
- A. Reverse engineering
- B. Application log collectors
- C. Workflow orchestration
- D. API integration
- E. Scripting
Answer: D
NEW QUESTION 5
A small electronics company decides to use a contractor to assist with the development of a new FPGA-based device. Several of the development phases will occur off-site at the contractor's labs.
Which of the following is the main concern a security analyst should have with this arrangement?
- A. Making multiple trips between development sites increases the chance of physical damage to the FPGAs.
- B. Moving the FPGAs between development sites will lessen the time that is available for security testing.
- C. Development phases occurring at multiple sites may produce change management issues.
- D. FPGA applications are easily cloned, increasing the possibility of intellectual property theft.
Answer: B
NEW QUESTION 6
A security analyst is investigating malicious traffic from an internal system that attempted to download proxy avoidance software as identified from the firewall logs but the destination IP is blocked and not captured. Which of the following should the analyst do?
- A. Shut down the computer
- B. Capture live data using Wireshark
- C. Take a snapshot
- D. Determine if DNS logging is enabled.
- E. Review the network logs.
Answer: A
NEW QUESTION 7
A storage area network (SAN) was inadvertently powered off while power maintenance was being performed in a datacenter. None of the systems should have lost all power during the maintenance. Upon review, it is discovered that a SAN administrator moved a power plug when testing the SAN's fault notification features.
Which of the following should be done to prevent this issue from reoccurring?
- A. Ensure both power supplies on the SAN are serviced by separate circuits, so that if one circuit goes down, the other remains powered.
- B. Install additional batteries in the SAN power supplies with enough capacity to keep the system powered on during maintenance operations.
- C. Ensure power configuration is covered in the datacenter change management policy and have the SAN administrator review this policy.
- D. Install a third power supply in the SAN so loss of any power intuit does not result in the SAN completely powering off.
Answer: A
NEW QUESTION 8
A system administrator is doing network reconnaissance of a company’s external network to determine the vulnerability of various services that are running. Sending some sample traffic to the external host, the administrator obtains the following packet capture: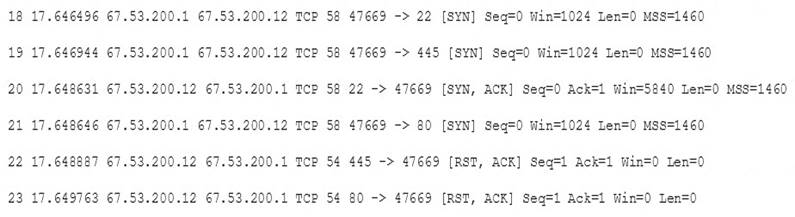
Based on the output, which of the following services should be further tested for vulnerabilities?
- A. SSH
- B. HTTP
- C. SMB
- D. HTTPS
Answer: C
NEW QUESTION 9
A security analyst, who is working for a company that utilizes Linux servers, receives the following results from a vulnerability scan: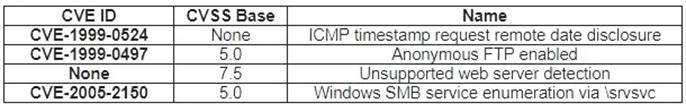
Which of the following is MOST likely a false positive?
- A. ICMP timestamp request remote date disclosure
- B. Windows SMB service enumeration via \srvsvc
- C. Anonymous FTP enabled
- D. Unsupported web server detection
Answer: B
NEW QUESTION 10
A cybersecurity analyst has access to several threat feeds and wants to organize them while simultaneously comparing intelligence against network traffic.
Which of the following would BEST accomplish this goal?
- A. Continuous integration and deployment
- B. Automation and orchestration
- C. Static and dynamic analysis
- D. Information sharing and analysis
Answer: B
NEW QUESTION 11
Which of the following are components of the intelligence cycle? (Select TWO.)
- A. Collection
- B. Normalization
- C. Response
- D. Analysis
- E. Correction
- F. Dissension
Answer: BE
NEW QUESTION 12
An analyst identifies multiple instances of node-to-node communication between several endpoints within the 10.200.2.0/24 network and a user machine at the IP address 10.200.2.5. This user machine at the IP address 10.200.2.5 is also identified as initiating outbound communication during atypical business hours with several IP addresses that have recently appeared on threat feeds.
Which of the following can be inferred from this activity?
- A. 10.200.2.0/24 is infected with ransomware.
- B. 10.200.2.0/24 is not routable address space.
- C. 10.200.2.5 is a rogue endpoint.
- D. 10.200.2.5 is exfiltrating data.
Answer: D
NEW QUESTION 13
After receiving reports latency, a security analyst performs an Nmap scan and observes the following output: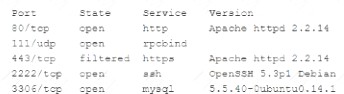
Which of the following suggests the system that produced output was compromised?
- A. Secure shell is operating of compromise on this system.
- B. There are no indicators of compromise on this system.
- C. MySQL services is identified on a standard PostgreSQL port.
- D. Standard HTP is open on the system and should be closed.
Answer: B
NEW QUESTION 14
An organization wants to move non-essential services into a cloud computing environment. Management has a cost focus and would like to achieve a recovery time objective of 12 hours. Which of the following cloud recovery strategies would work BEST to attain the desired outcome?
- A. Duplicate all services in another instance and load balance between the instances.
- B. Establish a hot site with active replication to another region within the same cloud provider.
- C. Set up a warm disaster recovery site with the same cloud provider in a different region
- D. Configure the systems with a cold site at another cloud provider that can be used for failover.
Answer: C
NEW QUESTION 15
Which of the following policies would slate an employee should not disable security safeguards, such as host firewalls and antivirus on company systems?
- A. Code of conduct policy
- B. Account management policy
- C. Password policy
- D. Acceptable use policy
Answer: D
NEW QUESTION 16
The inability to do remote updates of certificates, keys, software, and firmware is a security issue commonly associated with:
- A. web servers on private networks
- B. HVAC control systems
- C. smartphones
- D. firewalls and UTM devices
Answer: D
NEW QUESTION 17
......
P.S. Certshared now are offering 100% pass ensure CS0-002 dumps! All CS0-002 exam questions have been updated with correct answers: https://www.certshared.com/exam/CS0-002/ (186 New Questions)