Top Tips Of Update C9510-418 Exams
Download of C9510-418 exams materials and pdf for IBM certification for IT engineers, Real Success Guaranteed with Updated C9510-418 pdf dumps vce Materials. 100% PASS IBM WebSphere Application Server Network Deployment V9.0 Core Administration exam Today!
Check C9510-418 free dumps before getting the full version:
NEW QUESTION 1
When installing a new application to IBM WebSphere Application Server, which location is valid for the application file?
- A. Client Machine
- B. Managed Node
- C. Unmanaged Node
- D. Remote Web Server
Answer: B
Explanation:
Configuration file location during application installation
Several things occur upon installation of an application onto WebSphere Application Server:
Note: A node is a logical grouping of managed servers. Nodes can be managed or unmanaged. An unmanaged node does not have a node agent or administrative agent to manage its servers, whereas a managed node does. Both application servers and supported web servers can be on unmanaged or managed nodes.
References: WebSphere Application Server V8.5, July 2013, page 17
NEW QUESTION 2
Through what protocol can a Java client directly access EJBs running on an application server?
- A. JDBC
- B. RMI/IIOP
- C. SOAP/JMS
- D. SOAP/HTTP
Answer: D
Explanation:
Provided that it uses the correct protocols (SOAP, HTTP, WSDL), any web service client can access a stateless session bean, whether ornot the client is written in the Java programming language. The client doesn’t even “know” what technology implements the service: stateless session bean, JAX-WS, or some other technology. In addition, enterprise beans and web components can be clients ofweb services. This flexibility enables you to integrate Java EE applications with web services.
References:http://docs.oracle.com/javaee/6/tutorial/doc/gipjf.html
NEW QUESTION 3
Which two methods are used for communicating session linkages between the client and the server? (Select two.)
- A. Cookies
- B. LTPA Token
- C. Rest Services
- D. URL Rewriting
- E. HTTP Response codes
Answer: CE
Explanation:
Representational State Transfer (REST) is a lightweight framework for designing
applications that use HTTP to make calls. REST uses HTTP to perform the Create, Read, Update, and Delete (CRUD) operations between client and server. Applications interactwith the services by using HTTP, POST, PUT, GET, and DELETE operations.
References:https://www.ibm.com/support/knowledgecenter/en/SSZLC2_7.0.0/com.ibm.commerce.webservices.doc/concepts/cwvrest.htm
NEW QUESTION 4
What does the following JVM argument do?
-Xverbosegclog:${SERVER_LOG_ROOT}/verbose.m%d.7/18/16M%S.%pid.txt,20,10000
- A. It changes the default values for verbosegc logging.
- B. It changes the default location of the verbosegc logging.
- C. It configured verbosegc logging once it has already been enabled.
- D. It sets the default value for enabling and configuring verbosegc logging.
Answer: B
Explanation:
-Xverbosegclog[: <file> [,<X>,<Y>]]
Causes -verbose:gc output to be written to the specified file.
If it cannot create the file (for example, if an invalid filename is passed into the command), it will redirect the output to stderr.
If you specify <X>and <Y> the -verbose:gc output is redirected to <X> files, each containing <Y> GC cycles.
The dump agent tokens can be used in the filename. See Dump agent tokens for more information. If you do not specify <file>, verbosegc.%Y%m%d.%H%M%S.%pid.txt is used. example: -Xverbosegclog:newgclogname.log,7,10000
References:http://www-01.ibm.com/support/docview.wss?uid=swg21384096
NEW QUESTION 5
In an IBM WebSphere Application Server cluster, an administrator notices EJB requests are not evenly distributed on the cluster members during the load test.
What two things can the administrator verify in order to identify and resolve the issue? (Select two.)
- A. Ensure Dynamic Workload Management is enabled.
- B. Ensure host scoped routing optimization is enabled.
- C. Ensure PMI Workload Management counters are enabled.
- D. Ensure each server in the cluster has an equal weighted value.
- E. Ensure the Web server plug-in is using the round robin algorithm.
Answer: AD
Explanation:
A: Workload management optimizes the distribution of client processing tasks. Incoming work requests are distributed to the application servers, enterprise beans, servlets, and other objects that can most effectively process the requests.
D: The server weighted round robin routing policy ensures a balanced routing distribution based on the set of server weights that have been assigned to the members of a cluster. For example, if all servers in the cluster have the same weight, the expected distribution for the cluster is that all servers receive the same number of requests. If the weights for the servers are not equal, the distribution mechanism sends more requests to the higher weight value servers than the lower weight value servers. The policy ensures the distribution that you want, based on the weights that are assigned to the cluster members.
References:https://www.ibm.com/support/knowledgecenter/en/SSAW57_8.5.5/com.ibm.websphere.nd.doc/ae/crun_srvgrp.html
NEW QUESTION 6
When updating an application, what is important to keep in mind?
- A. The application is only updated during the next server restart.
- B. The applicationis automatically stopped, updated, and restarted.
- C. The application is only updated during the next restart of the application.
- D. The application is stopped, updated, and restarted at the scheduled time.
Answer: B
Explanation:
If the application is updated while it is running, WebSphere Application Server automatically stops the application, updates the application logic and restarts the application.
References:https://www.ibm.com/support/knowledgecenter/en/SSAW57_8.5.5/com.ibm.websphere.nd.doc/ae/crun_app_upgrade.html
NEW QUESTION 7
Which of the following can be queried to get PMI data?
- A. Server Cell
- B. JMX Connectors
- C. MBean ObjectNames
- D. Application ServerNames
Answer: C
Explanation:
PMI data can be gathered from the J2EE managed object MBeans or the WebSphere Application Server PMI Perf MBean.
References:https://www.ibm.com/support/knowledgecenter/en/SSAW57_8.5.5/com.ibm.websphere.nd.doc/ae/cprf_pmi_datacol.html
NEW QUESTION 8
When enabling SSL directives in the IBM HTTP Server configuration file, which parameter is required?
- A. The name of the key file
- B. The AllowOverride statement
- C. The IP address of the VirtualHost
- D. The DocumentRoot directory path
Answer: A
Explanation:
Enable SSL and define a key file to use. Uncomment the following lines to enable SSL and define a key file to use:
References:https://www.ibm.com/support/knowledgecenter/en/SSAW57_8.5.5/com.ibm.websphere.ihs.doc/ihs/tihs_setupsslwithwas.html
NEW QUESTION 9
Which of the following is true regarding disk offload?
- A. The amount of disk space to use cannot be specified.
- B. On server startup, DynaCache loads the entire disk cache into memory.
- C. The number of cache entries that are offloaded to disk cannot be specified.
- D. Disk offload can be enabled to have a cache entry copied to the file system at a configurable location.
Answer: ACD
Explanation:
AC:Before you enable disk offload, consider the following:
You cannot specify the number of cache entries that are offloaded to disk. You cannot specify the amount of disk space touse.
D: You can enable disk offload to have a cache entry copied to the file system (the location is configurable).
References:https://www.ibm.com/support/knowledgecenter/SSEQTP_9.0.0/com.ibm.websphere.base.doc/ae/udyn_rcachesettings.html
NEW QUESTION 10
How can the administrator change the console session expiration for the Integrated Solutions Console?
- A. Modify timeout value and run thetimeout.jaclscript.
- B. Set the timeout value in the Console Preferences panel.
- C. Use thesettimeout wsadmincommand and specify the value.
- D. Set theConnectionResponseTimeoutvalue in the Integrated Solutions Console.
Answer: A
Explanation:
Change the <timeout value> on the two lines of thetimeout.jaclscript to the new session expiration value. This number specifies the number of minutes the console preserves the session during inactivity.
References:https://www.ibm.com/support/knowledgecenter/en/SSAW57_8.5.5/com.ibm.websphere.nd.doc/isc/cons_sessionto.html
NEW QUESTION 11
To write a Jython script to stop a running application server, an administrator should use which administrative object?
- A. AdminApp
- B. AdminTask
- C. AdminConfig
- D. AdminControl
Answer: D
Explanation:
You can use the wsadmin tool to stop applications.
There are two ways to complete this task.Firstly you canuse the AdminControl object to stop the application. Alternatively, you can use the scripts in the AdminApplication script library to start, stop, and administer your application configurations.
References:https://www.ibm.com/support/knowledgecenter/en/SSAW57_8.0.0/com.ibm.websphere.nd.doc/info/ae/ae/txml_stopapplication.html
NEW QUESTION 12
An administrator configures an IBM DB2data source at cell scope. The environment variable DB2UNIVERSAL_JDBC_DRIVER_PATH is configured at cluster scope. The data source test connection on one node succeeds, but fails on the other node with java.lang.ClassNotFoundException:com.ibm.db2.jcc.DB2ConnectionPoolDataSource.
Which of the below is the likely cause for the exception?
- A. The data source is configured at cell scope.
- B. Multiple driver JARs are installed on the second node.
- C. DB2UNIVERSAL_JDBC_DRIVER_PATH is configured at cluster scope.
- D. A different version of the JDBC driver JAR does not exist on the second node.
Answer: C
Explanation:
Check that the variable is correctly defined at the scope where the JDBCProvider/DataSource is defined.
Note: At runtime, WebSphere Application Server invokes a physical data source by resolving the appropriate variable at a level where one of thefollowing criteria exists: The scope of the variable can contain the data source configuration; that is, the variable has the larger scope.
The variable and the data source have identical scopes.
Application Server meets these conditions by attempting to resolve the variable at each level of the scope spectrum. That is, the product tries to resolve the variable in the server scope, then the cluster scope, then the node scope, and lastly the cell scope.
References:https://www.ibm.com/support/knowledgecenter/SSAW57_8.0.0/com.ibm.websphere.nd.doc/info/ae/ae/cdat_testcon.html
NEW QUESTION 13
What data source property can an administrator configure to minimize the chances of encountering StaleConnectionExceptions?
- A. Minimum connections = 0
- B. Reap Timeout < Unused Timeout
- C. Purge Policy = FailingConnectionOnly
- D. Unused Timeout > Half firewall timeout
Answer: A
Explanation:
The configuration options below help minimize the chances of encounteringStaleConnectionExceptions by helping to ensure that your WebSphere Application Server maintains control of database connections, specifically, the only one closing them, rather than other components in your network:
The datasource MIN connections should beset to 0. By setting a MIN > 0, you are telling
the application server that this number of connections will be valid for the life of the application server JVM. Unless you can guarantee the MIN number of connections will never be timed out or dropped, setting a MIN will cause a StaleConnectionException when the connection becomes invalid.
References:https://www.ibm.com/developerworks/community/blogs/aimsupport/entry/websphere_application_server_staleconnectionexceptions?lang=en
NEW QUESTION 14
Which is true when an administrator properly updates a single file within an application?
- A. The administrator can use apartial application update.
- B. The administrator must redeploy the full application file.
- C. The administrator can manually update the file on the file system.
- D. The administrator must uninstall the application, and then, reinstall with the updated application file.
Answer: C
NEW QUESTION 15
When adding a repository to a federated repository configuration, which type of repository can be added only using wsadmin commands?
- A. File repository
- B. LDAP repository
- C. SAML repository
- D. Database repository
Answer: D
Explanation:
Federated repositories
Supports multiple types ofrepositories such as file-based, LDAP, database, and custom. In WebSphere Application Server Version 8.5, file-based and LDAP repositories are supported by the administrative console. For database and custom repositories, you can use the wsadmin command-line interface or the configuration application programming interfaces (API).
References: https://www.ibm.com/support/knowledgecenter/en/SSAW57_8.5.5/com.ibm.websphere.nd. doc/ae/cwim_fedrepos.html
NEW QUESTION 16
Which of the following statements is true regarding the relationship of nodes and node groups?
- A. Nodes can belong to only one node group.
- B. Nodes managed by a node group cannot be deleted.
- C. All nodes are initially not associated with a node group.
- D. All nodes are initially associated with a default node group.
Answer: D
Explanation:
D: a node must be a member ofa node group. Initially, all Application Server nodes are members of the default DefaultNodeGroup node group.
Note:A node group is a collection of managed nodes.
NEW QUESTION 17
What are two differences between dynamic clusters and static clusters? (Select two.)
- A. Dynamic Workload Management is enabled by default in dynamic clusters.
- B. The application placement controller can start and stop a dynamic cluster that is in automatic mode only.
- C. Using the autonomic request flow manager (ARFM) in manual mode will not affect dynamic cluster mode.
- D. Using static clusters in an Intelligent Management enabled environment will acquire some of a dynamic cluster features.
- E. When creating a static cluster using an application server template, any changes made to the template after creating the instances do not change the instances.
Answer: AE
Explanation:
A:The dynamic workload manager is enabled by default and assigns weights to the application server instances.
E: When you define a static cluster, you can select an application server template on which to base all the application server instances that you create. However, any changes that you make to the template after creating the instances do not change the instances.
References:https://www.ibm.com/support/knowledgecenter/en/SSUP64_7.0.0/com.ibm.websphere.virtualenterprise.doc/odoe_task/rodrcompareclusters.html
NEW QUESTION 18
An administrator noticed that one of the servers in the core group is experiencing OutOfMemory. As a result, other servers in the core group failed to start.
What core group custom property should the administrator tune to prevent the affected server from impacting other servers in the core group?
- A. IBM_CS_OOM_ACTION
- B. IBM_CS_DATASTACK_MEG
- C. IBM_CS_WIRE_FORMAT_VERSION
- D. IBM_CS_HAM_PROTOCOL_VERSION
Answer: A
Explanation:
IBM_CS_OOM_ACTION
Use this custom property to explicitly enable exception handlers that are specific for OutOfMemoryExceptions that occur when sending or receiving network messages. When this property is set to Isolate, if an OutOfMemoryException occurs when a network message is being sent or received, these exception handlers stop High Availability Manager communications to the Out of Memory process.
If IBM_CS_OOM_ACTION=Isolate is not added to the configuration settings for a core group, if a core group process runs out of memory, the Out of memory process might not
be able to respond to all messages. This situation prevents multi-step protocols from completing, and prevents the starting server from receiving its initial view of the distributed state.
References:https://www.ibm.com/support/knowledgecenter/en/SSAW57_8.0.0/com.ibm.websphere.nd.doc/info/ae/ae/urun_ha_cg_custprop.html
NEW QUESTION 19
Which two statements describe a web server in a cell topology?
- A. Creating a new node for a web server adds a managed node.
- B. Creating a new node for a web server adds an unmanaged node.
- C. Adding a web server to an existing node created a managed node.
- D. Deleting a web server from an unmanaged node creates a managed node.
- E. Deleting a web server from a managed node creates an unmanaged node.
Answer: AE
Explanation:
A managed node must exist to define a Web server definition, which is always on a managed node.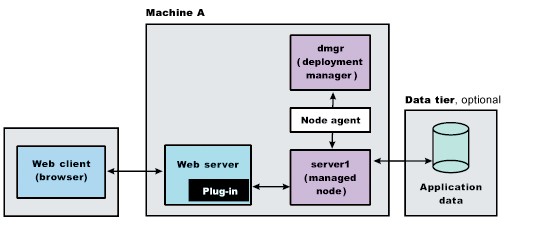
References:https://www.ibm.com/support/knowledgecenter/en/SSAW57_8.5.5/com.ibm.websphere.nd.doc/ae/tins_webplugins_single.html
NEW QUESTION 20
What must be modified to configure the authentication settings for IIOP requests?
- A. Bus security settings
- B. J2C authentication settings
- C. Session Initiation Protocol (SIP) authentication settings
- D. Common Secure Interoperability Version 2 (CSIV2) settings
Answer: D
Explanation:
WebSphere Application Server can propagate attributes directly as part of theCSIv2 protocol for RMI/IIOP requests.
References:https://www.ibm.com/developerworks/websphere/techjournal/0508_benantar/0508_benantar.html
NEW QUESTION 21
Which is true when installing interim fixes silently?
- A. No response file is needed.
- B. A password file is required.
- C. Greater permissions are needed.
- D. An online repository must beused.
Answer: C
Explanation:
Use the Update Installer program from the same user ID that installed the product that you are updating. Otherwise, the file ownership mismatches might require correction by the root user.
Note: An interim fix is also known as a patch.
NEW QUESTION 22
When verbose Garbage Collection is enabled, in which file(s) does the operating system collect the data?
- A. trace.log
- B. activity.log
- C. SystemOut.logandSystemErr.log
- D. native_stdout.logandnative_stderr.log
Answer: D
Explanation:
Depending on the operating system in use, the verboseGC output will be written to the following file by default:
AIX, Linux, or Windows: native_stderr.log Solaris or HP-UX native_stdout.log
References:http://www-01.ibm.com/support/docview.wss?uid=swg21114927
NEW QUESTION 23
An administrator would like to uninstall an instance of a multiple instance installation via response file.
How does the administrator ensure that the correct instance is uninstalled?
- A. All the features must be listed.
- B. The profile ID must point to the correct instance.
- C. The offering IDmust point to the correct instance.
- D. The repository location must point to the correct instance.
Answer: D
Explanation:
References:https://www.ibm.com/support/knowledgecenter/en/SSAW57_8.5.5/com.ibm.websphere.installation.nd.doc/ae/cins_WASv85_nd_modify_Win32.html
NEW QUESTION 24
When creating a health policy, which condition should be selected to track requests that have a significantly decreased response time?
- A. Workload
- B. Age-based
- C. Storm drain
- D. Excessive response time
Answer: C
Explanation:
The Storm drain condition tracks requests that have a significantly decreased response time.
References:https://www.ibm.com/support/knowledgecenter/en/SSAW57_8.5.5/com.ibm.websphere.nd.doc/ae/cwve_odhealth.html
NEW QUESTION 25
What does the –Dcom.ibm.webshpere.alarmthreadmonitor.generate.javacore JVM argument do?
- A. Creates a javacore dump when a thread is hung
- B. Generates a Tracemessage that a javacore should be generated
- C. Generates a SystemOut message that a javacore should be generated
- D. Allows the administrator to choose whether or not to generate a javacore when a hang is detected
Answer: A
Explanation:
If you want to monitor the activity of threads on which system alarms execute, add the following JVM generic arguments to the server settings.
-Dcom.ibm.websphere.alarmthreadmonitor.generate.javacore
Set to any value to cause a javacore dump to be created when an hung system alarm threadis detected. The threads section of the javacore dump can be analyzed to determine what the reported thread and other related threads are doing.
References:https://www.ibm.com/support/knowledgecenter/en/SSAW57_8.5.5/com.ibm.websphere.nd.doc/ae/ttrb_confighangdet.html
NEW QUESTION 26
......
100% Valid and Newest Version C9510-418 Questions & Answers shared by Dumpscollection.com, Get Full Dumps HERE: https://www.dumpscollection.net/dumps/C9510-418/ (New 65 Q&As)