All About 100% Guarantee 412-79v9 Testing Engine
we provide Accurate EC-Council 412-79v9 exam which are the best for clearing 412-79v9 test, and to get certified by EC-Council EC-Council Certified Security Analyst (ECSA) v9. The 412-79v9 Questions & Answers covers all the knowledge points of the real 412-79v9 exam. Crack your EC-Council 412-79v9 Exam with latest dumps, guaranteed!
Free 412-79v9 Demo Online For EC-Council Certifitcation:
NEW QUESTION 1
Which one of the following components of standard Solaris Syslog is a UNIX command that is used to add single-line entries to the system log?
- A. “Logger”
- B. ”/etc/syslog.conf”
- C. “Syslogd”
- D. “Syslogd.conf”
Answer: A
NEW QUESTION 2
Many security and compliance projects begin with a simple idea: assess the organization's risk, vulnerabilities, and breaches. Implementing an IT security risk assessment is critical to the overall security posture of any organization.
An effective security risk assessment can prevent breaches and reduce the impact of realized breaches.
What is the formula to calculate risk?
- A. Risk = Budget x Time
- B. Risk = Goodwill x Reputation
- C. Risk = Loss x Exposure factor
- D. Risk = Threats x Attacks
Answer: C
NEW QUESTION 3
Attackers create secret accounts and gain illegal access to resources using backdoor while bypassing the authentication procedures. Creating a backdoor is a where an attacker obtains remote access to a computer on a network.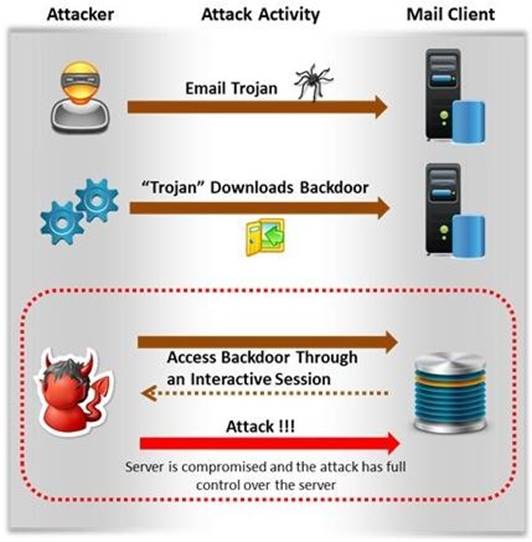
Which of the following techniques do attackers use to create backdoors to covertly gather
critical information about a target machine?
- A. Internal network mapping to map the internal network of the target machine
- B. Port scanning to determine what ports are open or in use on the target machine
- C. Sniffing to monitor all the incoming and outgoing network traffic
- D. Social engineering and spear phishing attacks to install malicious programs on the target machine
Answer: D
NEW QUESTION 4
A penetration test consists of three phases: pre-attack phase, attack phase, and post- attack phase.
Active reconnaissance which includes activities such as network mapping, web profiling, and perimeter mapping is a part which phase(s)?
- A. Post-attack phase
- B. Pre-attack phase and attack phase
- C. Attack phase
- D. Pre-attack phase
Answer: D
Explanation:
Reference: https://www.duo.uio.no/bitstream/handle/10852/34904/Shrestha-masterthesis.pdf?sequence=1 (page 28, first para)
NEW QUESTION 5
An external intrusion test and analysis identify security weaknesses and strengths of the client's systems and networks as they appear from outside the client's security perimeter, usually from the Internet. The goal of an external intrusion test and analysis is to demonstrate the existence of known vulnerabilities that could be exploited by an external attacker.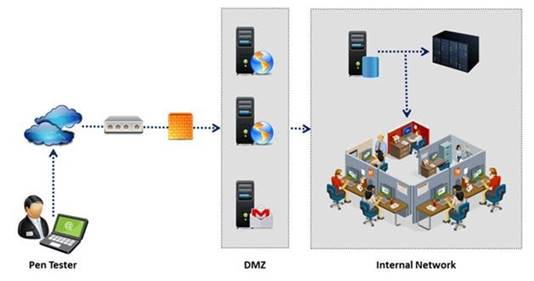
During external penetration testing, which of the following scanning techniques allow you to determine a port’s state without making a full connection to the host?
- A. XMAS Scan
- B. SYN scan
- C. FIN Scan
- D. NULL Scan
Answer: B
NEW QUESTION 6
Which of the following information gathering techniques collects information from an organization’s web-based calendar and email services?
- A. Anonymous Information Gathering
- B. Private Information Gathering
- C. Passive Information Gathering
- D. Active Information Gathering
Answer: D
Explanation:
Reference: http://luizfirmino.blogspot.com/2011/09/footprinting-terminologies.html
NEW QUESTION 7
Transmission control protocol accepts data from a data stream, divides it into chunks, and adds a TCP header creating a TCP segment.
The TCP header is the first 24 bytes of a TCP segment that contains the parameters and state of an end-to-end TCP socket. It is used to track the state of communication between two TCP endpoints.
For a connection to be established or initialized, the two hosts must synchronize. The synchronization requires each side to send its own initial sequence number and to receive a confirmation of exchange in an acknowledgment (ACK) from the other side
The below diagram shows the TCP Header format: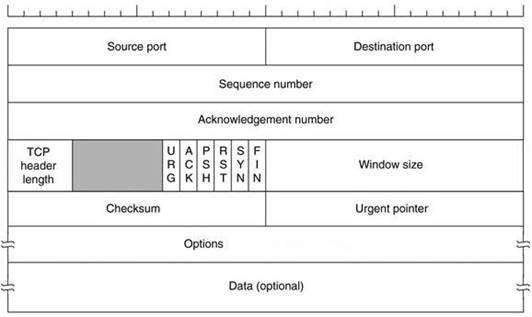
How many bits is a acknowledgement number?
- A. 16 bits
- B. 32 bits
- C. 8 bits
- D. 24 bits
Answer: B
Explanation:
Reference: http://en.wikipedia.org/wiki/Transmission_Control_Protocol (acknowledgement number)
NEW QUESTION 8
The amount of data stored in organizational databases has increased rapidly in recent years due to the rapid advancement of information technologies. A high percentage of these data is sensitive, private and critical to the organizations, their clients and partners.
Therefore, databases are usually installed behind internal firewalls, protected with intrusion detection mechanisms and accessed only by applications. To access a database, users have to connect to one of these applications and submit queries through them to the database. The threat to databases arises when these applications do not behave properly and construct these queries without sanitizing user inputs first.
Identify the injection attack represented in the diagram below: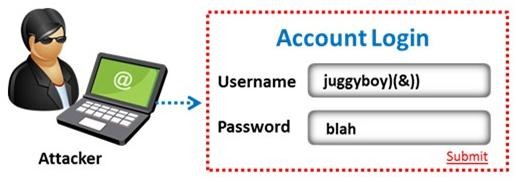
- A. Frame Injection Attack
- B. LDAP Injection Attack
- C. XPath Injection Attack
- D. SOAP Injection Attack
Answer: B
Explanation:
Reference: e https://www.blackhat.com/presentations/bh-europe-08/Alonso-Parada/Whitepaper/bh-eu-08-alonso-parada-WP.pdf ( page 3 to 5)
NEW QUESTION 9
Port numbers are used to keep track of different conversations crossing the network at the same time. Both TCP and UDP use port (socket) numbers to pass information to the upper
layers. Port numbers have the assigned ranges. The port numbers above 1024 are considered as which one of the following? (Select all that apply)
- A. Well-known port numbers
- B. Dynamically assigned port numbers
- C. Unregistered port numbers
- D. Statically assigned port numbers
Answer: B
NEW QUESTION 10
Which of the following is not a characteristic of a firewall?
- A. Manages public access to private networked resources
- B. Routes packets between the networks
- C. Examines all traffic routed between the two networks to see if it meets certain criteria
- D. Filters only inbound traffic but not outbound traffic
Answer: D
NEW QUESTION 11
One of the steps in information gathering is to run searches on a company using complex keywords in Google.
Which search keywords would you use in the Google search engine to find all the PowerPoint presentations containing information about a target company, ROCHESTON?
- A. ROCHESTON fileformat:+ppt
- B. ROCHESTON ppt:filestring
- C. ROCHESTON filetype:ppt
- D. ROCHESTON +ppt:filesearch
Answer: C
Explanation:
Reference: http://blog.hubspot.com/blog/tabid/6307/bid/1264/12-Quick-Tips-To-Search-Google-Like-An-Expert.aspx (specific document types)
NEW QUESTION 12
Which of the following acts is a proprietary information security standard for organizations that handle cardholder information for the major debit, credit, prepaid, e-purse, ATM, and POS cards and applies to all entities involved in payment card processing?
- A. PIPEDA
- B. PCI DSS
- C. Human Rights Act 1998
- D. Data Protection Act 1998
Answer: B
Explanation:
Reference: http://en.wikipedia.org/wiki/Payment_Card_Industry_Data_Security_Standard
NEW QUESTION 13
TCP/IP model is a framework for the Internet Protocol suite of computer network protocols that defines the communication in an IP-based network. It provides end-to-end connectivity specifying how data should be formatted, addressed, transmitted, routed and received at the destination. This functionality has been organized into four abstraction layers which are used to sort all related protocols according to the scope of networking involved.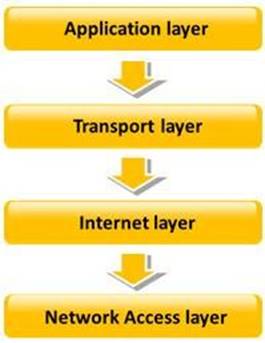
Which of the following TCP/IP layers selects the best path through the network for packets to travel?
- A. Transport layer
- B. Network Access layer
- C. Internet layer
- D. Application layer
Answer: C
NEW QUESTION 14
Which of the following will not handle routing protocols properly?
- A. “Internet-router-firewall-net architecture”
- B. “Internet-firewall-router-net architecture”
- C. “Internet-firewall -net architecture”
- D. “Internet-firewall/router(edge device)-net architecture”
Answer: B
NEW QUESTION 15
Identify the type of testing that is carried out without giving any information to the employees or administrative head of the organization.
- A. Unannounced Testing
- B. Double Blind Testing
- C. Announced Testing
- D. Blind Testing
Answer: B
NEW QUESTION 16
Which of the following is the objective of Gramm-Leach-Bliley Act?
- A. To ease the transfer of financial information between institutions and banks
- B. To protect the confidentiality, integrity, and availability of data
- C. To set a new or enhanced standards for all U.
- D. public company boards, management and public accounting firms
- E. To certify the accuracy of the reported financial statement
Answer: A
Explanation:
Reference: http://www.itap.purdue.edu/security/policies/glb_safeguards_rule_training_general.pdf
NEW QUESTION 17
Which of the following contents of a pen testing project plan addresses the strengths, weaknesses, opportunities, and threats involved in the project?
- A. Project Goal
- B. Success Factors
- C. Objectives
- D. Assumptions
Answer: D
NEW QUESTION 18
Which one of the following is a useful formatting token that takes an int * as an argument, and writes the number of bytes already written, to that location?
- A. “%n”
- B. “%s”
- C. “%p”
- D. “%w”
Answer: A
NEW QUESTION 19
Internet Control Message Protocol (ICMP) messages occur in many situations, such as whenever a datagram cannot reach the destination or the gateway does not have the buffering capacity to forward a datagram. Each ICMP message contains three fields: type, code, and checksum. Different types of Internet Control Message Protocols (ICMPs) are identified by a type and code field.
Which of the following ICMP messages will be generated if the destination port is not
reachable?
- A. ICMP Type 11 code 1
- B. ICMP Type 5 code 3
- C. ICMP Type 3 code 2
- D. ICMP Type 3 code 3
Answer: D
NEW QUESTION 20
HTTP protocol specifies that arbitrary binary characters can be passed within the URL by using %xx notation, where 'xx' is the
- A. ASCII value of the character
- B. Binary value of the character
- C. Decimal value of the character
- D. Hex value of the character
Answer: D
Explanation:
https://books.google.nl/books?id=0RfANAwOUdIC&pg=PA720&lpg=PA720&dq=%22xx+no tation%22+binary&source=bl&ots=pGMqass7ti&sig=rnIg1xZ78ScUvuIlTmDY3r7REuc&hl= nl&sa=X&ei=8C4dVYe1NorgasrzgoAL&ved=0CEQQ6AEwBQ#v=onepage&q=%22xx%20n
otation%22%20binary&f=false
NEW QUESTION 21
Which of the following password hashing algorithms is used in the NTLMv2 authentication mechanism?
- A. AES
- B. DES (ECB mode)
- C. MD5
- D. RC5
Answer: C
NEW QUESTION 22
How many bits is Source Port Number in TCP Header packet?
- A. 48
- B. 32
- C. 64
- D. 16
Answer: D
NEW QUESTION 23
Rule of Engagement (ROE) is the formal permission to conduct a pen-test. It provides top- level guidance for conducting the penetration testing.
Various factors are considered while preparing the scope of ROE which clearly explain the limits associated with the security test.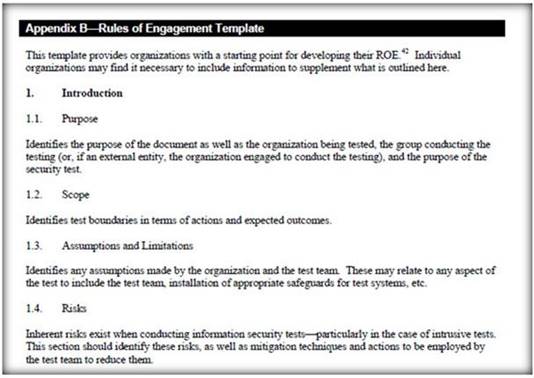
Which of the following factors is NOT considered while preparing the scope of the Rules of Engagment (ROE)?
- A. A list of employees in the client organization
- B. A list of acceptable testing techniques
- C. Specific IP addresses/ranges to be tested
- D. Points of contact for the penetration testing team
Answer: A
NEW QUESTION 24
You are conducting a penetration test against a company and you would like to know a personal email address of John, a crucial employee. What is the fastest, cheapest way to find out John’s email address.
- A. Call his wife and ask for his personal email account
- B. Call a receptionist and ask for John Stevens’ personal email account
- C. Search in Google for his personal email ID
- D. Send an email to John stating that you cannot send him an important spreadsheet attachment file to his business email account and ask him if he has any other email accounts
Answer: D
NEW QUESTION 25
Identify the framework that comprises of five levels to guide agency assessment of their security programs and assist in prioritizing efforts for improvement:
- A. Information System Security Assessment Framework (ISSAF)
- B. Microsoft Internet Security Framework
- C. Nortells Unified Security Framework
- D. Federal Information Technology Security Assessment Framework
Answer: D
NEW QUESTION 26
Which of the following shields Internet users from artificial DNS data, such as a deceptive or mischievous address instead of the genuine address that was requested?
- A. DNSSEC
- B. Firewall
- C. Packet filtering
- D. IPSec
Answer: A
Explanation:
Reference: http://tools.ietf.org/html/draft-osterweil-dane-ipsec-01 (abstract, first para)
NEW QUESTION 27
The SnortMain () function begins by associating a set of handlers for the signals, Snort receives. It does this using the signal () function. Which one of the following functions is used as a programspecific signal and the handler for this calls the DropStats() function to output the current Snort statistics?
- A. SIGUSR1
- B. SIGTERM
- C. SIGINT
- D. SIGHUP
Answer: A
NEW QUESTION 28
The Web parameter tampering attack is based on the manipulation of parameters exchanged between client and server in order to modify application data, such as user credentials and permissions, price and quantity of products, etc. Usually, this information is stored in cookies, hidden form fields, or URL Query Strings, and is used to increase application functionality and control.
This attack takes advantage of the fact that many programmers rely on hidden or fixed fields (such as a hidden tag in a form or a parameter in a URL) as the only security measure for certain operations. Attackers can easily modify these parameters to bypass the security mechanisms that rely on them.
What is the best way to protect web applications from parameter tampering attacks?
- A. Validating some parameters of the web application
- B. Minimizing the allowable length of parameters
- C. Using an easily guessable hashing algorithm
- D. Applying effective input field filtering parameters
Answer: D
NEW QUESTION 29
A wireless intrusion detection system (WIDS) monitors the radio spectrum for the presence of unauthorized, rogue access points and the use of wireless attack tools. The system monitors the radio spectrum used by wireless LANs, and immediately alerts a systems administrator whenever a rogue access point is detected.
Conventionally it is achieved by comparing the MAC address of the participating wireless devices.
Which of the following attacks can be detected with the help of wireless intrusion detection system (WIDS)?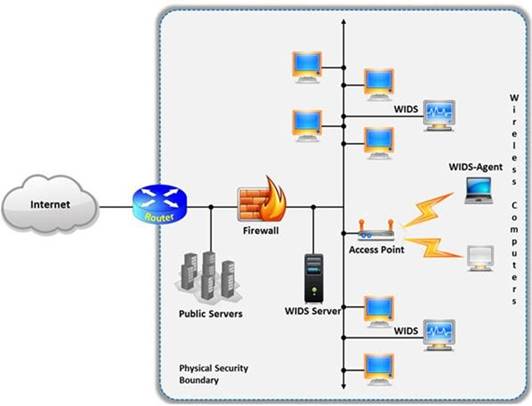
- A. Social engineering
- B. SQL injection
- C. Parameter tampering
- D. Man-in-the-middle attack
Answer: D
Explanation:
Reference: http://www.infosecwriters.com/text_resources/pdf/Wireless_IDS_JDixon.pdf (page 5)
NEW QUESTION 30
......
100% Valid and Newest Version 412-79v9 Questions & Answers shared by Dumpscollection.com, Get Full Dumps HERE: https://www.dumpscollection.net/dumps/412-79v9/ (New 203 Q&As)