Validated 400-251 Testing Software 2021
Exam Code: 400-251 (Practice Exam Latest Test Questions VCE PDF)
Exam Name: CCIE Security Written Exam
Certification Provider: Cisco
Free Today! Guaranteed Training- Pass 400-251 Exam.
Also have 400-251 free dumps questions for you:
NEW QUESTION 1
Which two statements about ICMP redirect messages are true? (Choose two.)
- A. Redirects are only punted to the CPU if the packets are also source-routed.
- B. The messages contain an ICMP Type 3 and ICMP code 7.
- C. By default, configuring HSRP on the interface disables ICMP redirect functionality.
- D. They are generated when a packet enters and exits the same route interface.
- E. They are generated by the host to inform the router of an temate route to the destination.
Answer: CD
NEW QUESTION 2
Which description of a hybrid SDN framework is true?
- A. The control plane and data plane are pulled from the networking element and put in an SDN controller and SDN agent
- B. The control plane function is split between a SDN controller and the networking element.
- C. The data plane is pulled from the networking element and put in an SDN controller.
- D. The control plane is pulled from the networking element and put in an SDN controller
Answer: B
NEW QUESTION 3
Which statement about Local Web Authentication is true?
- A. It supports Change of Authorization and VLAN enforcement
- B. It can use VLANs and ACLs to enforce authorization
- C. The network device handles guest authentication
- D. The ISE servers web pages
- E. It supports posture and profiling services
- F. The web portal can be customized locally or managed by the ISE
Answer: C
NEW QUESTION 4
Which statement about Remote Triggered Black Hole Filtering feature is true?
- A. It works in conjunction with QoS to drop the traffic that has a lower priority.
- B. The Null0 interface used for filtering able to receive the traffic but never forwards it.
- C. In RTBH filtering, the trigger device redistributes dynamic routes to the eBGP peers.
- D. It helps mitigate DDoS attack based only on destination address.
- E. It drops malicious traffic at the customer edge router by forwarding it to a Null0 interface.
- F. In RTBH filtering, the trigger device is always an ISP edge router.
Answer: C
NEW QUESTION 5
What are two characteristics of RPL, used in IoT environments?(Choose two)
- A. It is an Exterior Gateway Protocol
- B. It is a Interior Gateway Protocol
- C. It is a hybrid protocol
- D. It is link-state protocol
- E. It is a distance-vector protocol
Answer: BE
NEW QUESTION 6
Which of the following Cisco products gives ability to interact with malware for its behavior analysis?
- A. NGIPS
- B. FMC
- C. ASA
- D. DNA
- E. Threat Grid
- F. pxGrid
Answer: E
NEW QUESTION 7
Which feature does Cisco VSG use to redirect traffic in a Cisco Nexus 1000v Series Switch?
- A. VEM
- B. VPC
- C. VDC
- D. vPath
Answer: D
NEW QUESTION 8
Refer to the exhibit.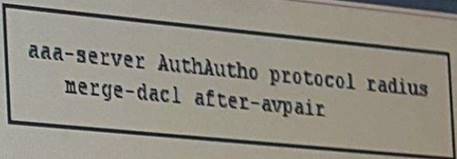
Which effect of this configuration is true?
- A. The downloadable ACL and AV pair ACL are merged after three connection attempts are made to the RADIUS server.
- B. The downloadable ACL and AV pair ACL are merged immediately when the RADIUS server is activated.
- C. For all users, entries in a downloadable ACL are given priority over entries in an AC pair ACL.
- D. The downloadable ACL and AV pair ACL entries are merged together,one ACE at a time.
- E. A downloadable ACL is applied after an AV pair ACL.
Answer: E
NEW QUESTION 9
In your network, you require all guests to authenticate to the network before getting access. However, you don't want to be stuck creating or approving accounts. It is preferred that this is all taken care by the user, as long as their device is registered. Which two mechanisms can be used to provide this functionality? (Choose two.)
- A. Social media login, with device registration
- B. Guest's own organization authentication service, with device registration
- C. PAP based authentication, with device registration
- D. Active Directory, with device registration
- E. 802.1x based user registration, with device registration
- F. Self-registration of user, with device registration
Answer: AF
NEW QUESTION 10
1821 How does the Cisco Firepower Decrypt-known method perform SSI decryption on inbound traffic?
- A. The system identifies the server certificate during the SSL handshake and downloads the associate private key from the CA to decrypt the traffic
- B. The system matches the incoming server certificate to a previously stored certificate on the server and uses the private key to decrypt the traffic
- C. The system uses a CA certificate on the server to resign the exchanges server certificate then uses the private key of the CA certificate to decrypt the traffic ^^^^
- D. The system uses a CA certificate cm the server to resign the exchanges server certificate then uses separate private key to decrypt the traffic ^^^Jicun me »cr 1-tjCeWnV
Answer: C
NEW QUESTION 11
In your corporate environment, you have various Active Directory groups based on the organizational structure and would like to ensure that users are only able to access certain resources depending on which group(s) they belong to. This policy should apply across the network. You have ISE, ASA and WSA deployed, and would like to ensure the appropriate policies are present to ensure access is only based on the user's group membership. Additionally, you don't want the user to authenticate multiple times to get access. Which two policies are used to set this up? (Choose two.)
- A. Deploy Cisco TrustSec infrastructure, with ASA and WSA integrated with the ISE to transparently identify user based on SGT assignment, when the user authenticates to the networ
- B. The SGTs can then be used in access policies.
- C. Deploy ISE, integrate it with Active Directory, and based on group membership authorize the user to specific VLAN
- D. These VLANs (with specific subnets) should then be used in access policies on the ASA as well as the WSA.
- E. Deploy a Single Sign-On infrastructure such as Ping, and integrate ISE, ASA and WSA with i
- F. Access policies will be applied based on the user's group membership retrieved from the authentication infrastructure.
- G. Configure ISE as an SSO Service Provider, and integrate with ASA and WSA using pxGri
- H. ASA and WSA will be able to extract the relevant identity information from ISE to apply to the access policies once the user has authenticated to the network.
- I. Integrate ISE, ASA and WSA with Active Director
- J. Once user is authenticated to the network through ISE, the ASA and WSA will automatically extract the identity information from AD to apply the appropriate access policies.
- K. Configure ISE to relay learned SGTs for the authenticated sessions with the binded destination address using SXP speakers that will be used to apply access policies at the traffic ingress point for segmentation
Answer: AC
NEW QUESTION 12
Which two statements about Cisco ASA authentication using LDAP are true? (Choose two.)
- A. It is a closed standard that manages directory-information services over distributed networks.
- B. It can combine AD attributes and LDAP attributes to configure group policies on the Cisco ASA.
- C. It uses attribute maps to map the AD memberOf attribute to the Cisco ASAGroup-Policy attribute.
- D. It can assign a group policy to a user based on access credentials.
- E. It uses AD attribute maps to assign users to group policies configured under the WebVPN context.
- F. The Cisco ASA can use more than one AD memberOf attribute to match a user to multiple group policies.
Answer: CE
NEW QUESTION 13
How is the Cisco IronPort email data loss prevention licensed?
- A. It is a per-site license
- B. It comes free with Iron Port Email server
- C. It is a per-enterprise license
- D. It is a per-server license
- E. It is a per-user license
Answer: E
NEW QUESTION 14
Which of the following is used by WSA to extract session information from ISE and use that in access policies?
- A. RPC
- B. pxGrid
- C. SXP
- D. Proprietary protocol over TCP/8302
- E. EAP
- F. RADIUS
Answer: B
NEW QUESTION 15
Which statement about the pxGrid connection agent is true?
- A. It manages the sharing of contextual information between partner platforms
- B. It can fetch user information from Active Directory on behalf of a WSA or Cisco ISE
- C. It enables communication from the partner platform to the pxGrid controller
- D. It supports an agentless solution for Cisco ISE
- E. It leverages Cisco ISE control functions to manage connections and share information between partners
- F. It fetches user information from Active Directory and transmits it to the pxGrid controller
Answer: A
NEW QUESTION 16
All your employees must authenticate their devices to the network, be they company-owned or
employee-owned assets, with ISE as the authentication server, i ne primary identity store used is Microsoft Active Directory, with username and password authentication. To ensure the security of your enterprise, your security policy dictates that only company owned assets get access to the enterprise network, while personal assets have restricted access. Which configuration allows you to enforce this policy using only ISE and Active Directory?
- A. Configure an authentication policy that checks against the MAC address database of company assets in the ISE endpoint identity store to determine the level of access depending on the device.
- B. Deployment of a Mobile Device Management solution is required, which can be used to register all devices against the MDM server, and use that to assign appropriate access levels.
- C. Configure an authorization policy that assigns the device the appropriate profile based on whether the device passes Machine Authentication or not.
- D. Configure an authorization policy that checks against the MAC address database of company assets in the ISE endpoint identity store to ^determine the level of access depending on the device.
- E. Configure an authentication policy that uses the computer credentials in Active Directory to determine whether the device is company-owned or personal.
Answer: D
NEW QUESTION 17
Your customer wants to implement Cisco Firepower IPS and 1 secure policy.
However, a monitoring period of 2 weeks is applied against real traffic without causing an outage before going in to fu of the default policies as a base and set the policy action to ensure.
Which two policies to achieve these requirements are true?
- A. Set IPs policy to trust
- B. Set IPs policy to Monitor
- C. Base the IPS policy on the default Advanced Security over Connection
- D. Base the IPS policy on the default Balanced Security and Connection
- E. Base the IPS policy on the default Connectivity over Security
- F. Base the IPS policy on the default Security over Connectivity
- G. Set IPS Policy to No Drop
Answer: BD
NEW QUESTION 18
Which statement is correct regarding the SenderBase functionality?
- A. ESA sees a high negative score from SenderBase as very unlikely that sender is sending spam.
- B. SenderBase uses DNS/based blacklist as one of the sources of information to define reputation score of sender's IP address.
- C. WSA uses SenderBase information to confiugre URL filtering policies.
- D. ESA uses destination address reputation information from SenderBase to configure mail policies.
- E. SenderBase uses spam complaints as one of the sources of information of defined reputation score of receiver IP address.
- F. ESA sees a high positive score from SenderBase as very likely that sender is sending spam.
Answer: B
NEW QUESTION 19
Which two statements about MACsec are true? (Choose two)
- A. It maintains network intelligence as it applied to router uplinks and downlinks.
- B. It works in conjunction with IEEE 802.1X -2010 port-based access control.
- C. It uses symmetric-key encryption to protect data confidentiality.
- D. It encrypts packets at Layer 3, which allows devices to handle packets in accordance with network polices.
- E. It can be enabled on individual port at Layer 3 to allow MACsec devices to access the network.
- F. It can use IEEE 802.1x master keys to encrypt wired and wireless links
Answer: BC
NEW QUESTION 20
In TLS Implementation on the Cisco Email Security Appliance cluster, the machine is removed from the cluster and then added back. Which description of what happens to the machine-level certificate true?
- A. ESA cannot provider privacy for point-to point transmission of emails through encryption
- B. The machine-level certificates are lost
- C. The machine-level certificates are rebuilt by RAID 5
- D. The cluster goes down.
Answer: C
NEW QUESTION 21
Which command sequence can you enter to enable IP multicast for WCCPv2?
- A. Router(config)#ip wccp web-cache group-address 224.1.1.100 Router(config)# interface FastEthernet0/0Router(config-if)#ip wccp web-cache redirect out
- B. Router(config)#ip wccp web-cache group-list Router(config)# interface FastEthernet0/0 Router(config)# ip wccp web-cache group-listen
- C. Router(config)#ip wccp web-cache service-list Router(config)# interface FastEthernet0/0 Router(config)# ip wccp web-cache group-listen
- D. Router(config)#ip wccp web-cache group-address 224.1.1.100 Router(config)# interface FastEthernet0/0Router(config)# ip wccp web-cache redirect in
- E. Router(config)#ip wccp web-cache group-address 224.1.1.100 Router(config)# interface FastEthernet0/0Router(config)# ip wccp web-cache group-listen
Answer: E
NEW QUESTION 22
Which effect of the crypto key encrypt write rsa command on a router is true?
- A. The device locks the encrypted key, but the key is lost when the router is reloaded.
- B. The device encrypts and locks the key before authenticating it with an external CA server.
- C. The device unlocks the encrypted key, but the key is lost when the router is reloaded.
- D. The device locks the encrypted key and saves it to the NVRAM.
- E. The device saves the unlocked encrypted key to the NVRAM.
Answer: E
NEW QUESTION 23
Drag the network scan type on the left to its definition on the right.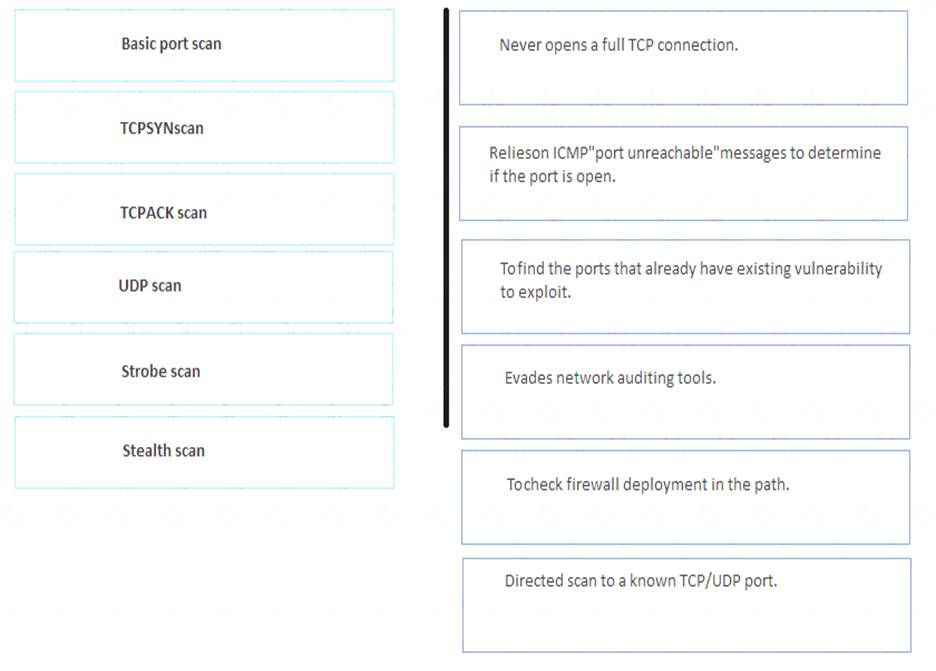
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 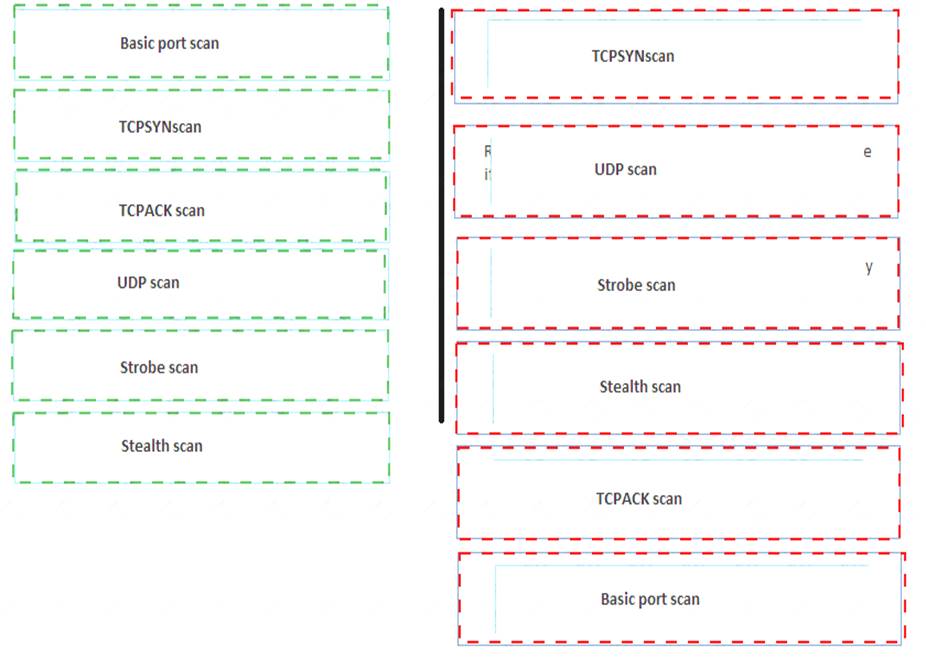
NEW QUESTION 24
Refer to the exhibit,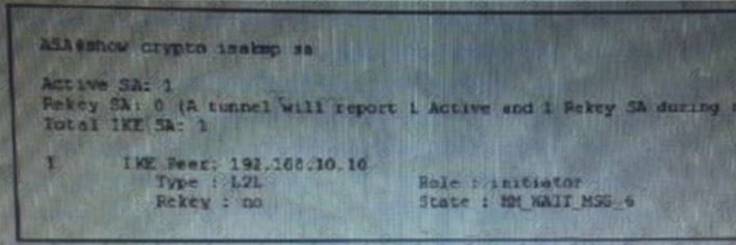
you issued the show crypto isakmp sa command to troubleshot of IPsec VPN. What possible issue does the given output indicate?
- A. The peer is failing to respond
- B. The crypto ACU are mismatched
- C. The pre-shared keys ire mismatched
- D. The transform sets are mismatched
Answer: C
NEW QUESTION 25
Which three ESMTP extensions are supported by the Cisco ASA?Choose three
- A. NOOP
- B. PIPELINING
- C. SAML
- D. 8BITMIME
- E. STARTTLS
- F. ATRN
Answer: ACE
NEW QUESTION 26
Refer to the exhibit.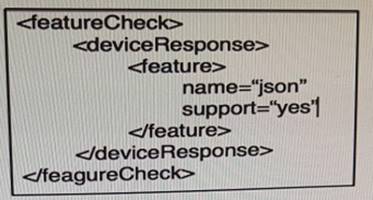
Which data format is used in this script?
- A. JSON
- B. YANG
- C. API
- D. XML
- E. JavaScript
Answer: D
NEW QUESTION 27
Which connection mechanism does the eSTREAMER service use to communicate?
- A. IPsec tunnels with 3DES or AES encryption
- B. TCP over SSL only
- C. SSH
- D. EAP-TLS tunnels
- E. TCP with optional SSL encryption
- F. IPsec tunnels with 3DES encryption only
Answer: B
NEW QUESTION 28
Which two statements about the Cisco FireAMP solution are true? (Choose two.)
- A. It can perform dynamic analysis in the Fire AMP Private Cloud.
- B. The FireAMP Connector can detect malware in network traffic and when files are downloaded.
- C. The FireAMP Private Cloud provides an on-premises option for file disposition lookups and retrospect generation.
- D. The FireAMP Connector is compatible with antivirus software on the endpoint, but you must configure exclusion to prevent the Connector form scanning the antivirus directory.
- E. The FireAMP Connector can provide information about potentially malicious network connections.
- F. The FireAMP Private cloud can act as an anonymized proxy to transport endpoint event data to the public cloud for disposition lookups.e
- G. When a FireAMP Connector detects malware in network traffic, it generates a malware event and a event.
Answer: AC
NEW QUESTION 29
Refer to the exhibit.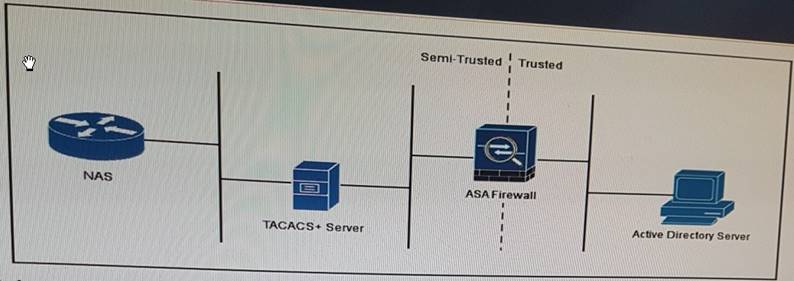
A user authenticates to the NAS , which communicates to the TACACS+ sever for
authentication. The TACACS+ server then accesses the Active Directory Server through the firewall to validate the user credentials. Which protocol-port pair must be allow access through the ASAFirewall?
- A. SMB over TCP 455
- B. DNS over UDP 53
- C. LDAP over UDP 389
- D. global catalog over UDP 3268
- E. TACACS+ over TCP 49
- F. DNS over TCP 53
Answer: C
NEW QUESTION 30
Which two functionalities doe s the Threat Grid for the technology allow?
- A. Deploy decoys for the malware to target
- B. Know what changes the malware is making
- C. Locate where the malware originated form
- D. To encrypt packet without an agent
- E. To decrypt packet without an agent
- F. Understanding of which processes the malware is affect
Answer: DF
NEW QUESTION 31
......
P.S. Certshared now are offering 100% pass ensure 400-251 dumps! All 400-251 exam questions have been updated with correct answers: https://www.certshared.com/exam/400-251/ (448 New Questions)