A Review Of Top Quality 350-901 Simulations
Our pass rate is high to 98.9% and the similarity percentage between our 350-901 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the Cisco 350-901 exam in just one try? I am currently studying for the Cisco 350-901 exam. Latest Cisco 350-901 Test exam practice questions and answers, Try Cisco 350-901 Brain Dumps First.
Online Cisco 350-901 free dumps demo Below:
NEW QUESTION 1
Which two situations are flagged by software tools designed for dependency checking in continuous integration environments, such as OWASP? (Choose two.)
- A. publicly disclosed vulnerabilities related to the included dependencies
- B. mismatches in coding styles and conventions in the included dependencies
- C. incompatible licenses in the included dependencies
- D. test case failures introduced by bugs in the included dependencies
- E. buffer overflows to occur as the result of a combination of the included dependencies
Answer: AE
NEW QUESTION 2
An automated solution is needed to configure VMs in numerous cloud provider environments to connect the environments to an SDWAN. The SDWAN edge VM is provided as an image in each of the relevant clouds and can be given an identity and all required configuration via cloud-init without needing to log into the VM once online.
Which configuration management and/or automation tooling is needed for this solution?
- A. Ansible
- B. Ansible and Terraform
- C. NSO
- D. Terraform
- E. Ansible and NSO
Answer: E
NEW QUESTION 3
Which type of file is created from issued intermediate, root, and primary certificates for SSL installation on a server?
- A. DER
- B. CSR
- C. PEM
- D. CRT
Answer: C
NEW QUESTION 4
Refer to the exhibit. An application uses an API to periodically sync a large data set. Based on the HTTP message sequence provided, which statements are true about the caching behavior seen in the scenario? (Choose two.)
- A. The full dataset was transmitted to the client twice.
- B. The dataset changed sometime between message #4 and #5.
- C. A partial dataset was transmitted to the client in message #4.
- D. The dataset did not change during the scenario.
- E. Messages #3 and #5 are equivalent.
Answer: AD
NEW QUESTION 5
Which two statements about a stateless application are true? (Choose two.)
- A. Different requests can be processed by different servers.
- B. Requests are based only on information relayed with each request.
- C. Information about earlier requests must be kept and must be accessible.
- D. The same server must be used to process all requests that are linked to the same state.
- E. No state information can be shared across servers.
Answer: AB
NEW QUESTION 6
Where should distributed load balancing occur in a horizontally scalable architecture?
- A. firewall-side/policy load balancing
- B. network-side/central load balancing
- C. service-side/remote load balancing
- D. client-side/local load balancing
Answer: B
NEW QUESTION 7
An application is hosted on Google Kubernetes Engine. A new JavaScript module is created to work with the existing application. Which task is mandatory to make the code ready to deploy?
- A. Create a Dockerfile for the code base.
- B. Rewrite the code in Python.
- C. Build a wrapper for the code to “containerize” it.
- D. Rebase the code from the upstream git repo.
Answer: D
NEW QUESTION 8
How should a web application be designed to work on a platform where up to 1000 requests per second can be served?
- A. Use algorithms like random early detection to deny excessive requests.
- B. Set a per-user limit (for example, 5 requests/minute/user) and deny the requests from the users who have reached the limit.
- C. Only 1000 user connections are allowed; further connections are denied so that all connected users can be served.
- D. All requests are saved and processed one by one so that all users can be served eventually.
Answer: D
NEW QUESTION 9
Refer to the exhibit. Which set of API requests must be executed by a Webex Teams bot after receiving a webhook callback to process messages in a room and reply with a new message back to the same room?
- A.
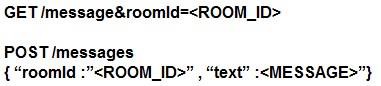
- B.
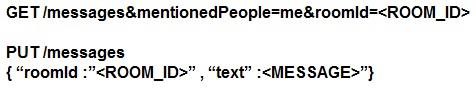
- C.
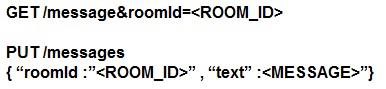
- D.
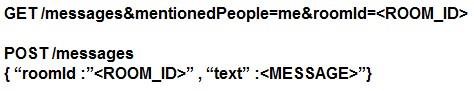
Answer: B
NEW QUESTION 10
A container running a Python script is failing when it reaches the integration testing phase of the CI/CD process. The code has been reviewed thoroughly and the build process works on this container and all other containers pass unit and integration testing.
What should be verified to resolve the issue?
- A. that the correct port is exposed in the Dockerfile
- B. that the necessary modules and packages are installed on build
- C. that the script is running from the night directory
- D. that the Python version of the container image is correct
Answer: B
NEW QUESTION 11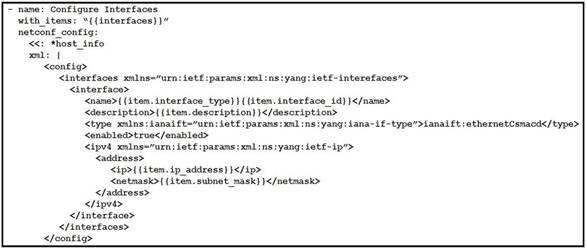
Refer to the exhibit. As part of the Ansible playbook workflow, several new interfaces are being configured using the netconf_config module. The task references the interface variables that are unique per device. In which directory is the YAML file with these variables found?
- A. host_vars directory
- B. home directory
- C. group_vars directory
- D. current working directory
Answer: A
NEW QUESTION 12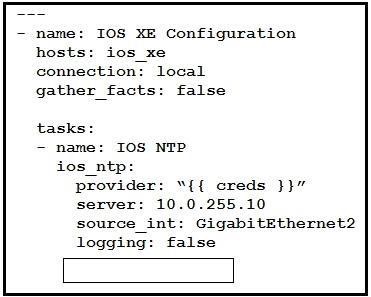
Refer to the exhibit. Which key value pair from the ios_ntp Ansible module creates an NTP server peer?
- A. state: present
- B. state: True
- C. config: present
- D. config: True
Answer: A
NEW QUESTION 13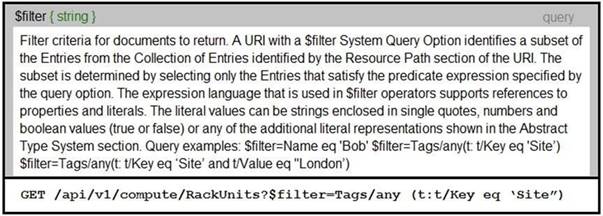
Refer to the exhibit. An Intersight API is being used to query RackUnit resources that have a tag keyword set to “Site”. What is the expected output of this command?
- A. list of all resources that have a tag with the keyword “Site”
- B. error message because the Value field was not specified
- C. error message because the tag filter should be lowercase
- D. list of all sites that contain RackUnit tagged compute resources
Answer: A
NEW QUESTION 14
Which two strategies are used to protect personally identifiable information? (Choose two.)
- A. Encrypt data in transit.
- B. Encrypt hash values of data.
- C. Encrypt data at rest.
- D. Only hash usernames and passwords for efficient lookup.
- E. Only encrypt usernames and passwords for efficient lookup.
Answer: AB
NEW QUESTION 15
Click on the GET Resource button above to view resources that will help with this question.
An engineer is managing a DC with 6000 Cisco UCS servers installed and running. The engineer has been asked to identify all resources where the model is in the UCSB family and the available memory is less than or equal to 5 GB.
Which REST API call accomplishes this task?
- A. GET/api/v1/compute/RackUnits?$select=Vendor,Model,Serial&$filter=not(Model eq ‘UCSC’) and AvailableMemory le 5000
- B. GET/api/v1/compute/RackUnits?$select=Vendor,Model,Serial&$filter=Model eq ‘UCSB’ and AvailableMemory lt 5000
- C. GET/api/v1/compute/RackUnits?$select=Vendor,Model,Serial&$filter=contains(Model, UCSB’) and AvailableMemory lt 5000
- D. GET/api/v1/compute/RackUnits?$select=Vendor,Model,Serial&$filter=contains(Model, UCSB’) and AvailableMemory le 5000
Answer: D
NEW QUESTION 16
A developer has just completed the configuration of an API that connects sensitive internal systems. Based on company policies, the security of the data is a high priority. Which approach must be taken to secure API keys and passwords?
- A. Embed them directly in the code.
- B. Store them in a hidden file.
- C. Store them inside the source tree of the application.
- D. Change them periodically.
Answer: D
NEW QUESTION 17
An organization manages a large cloud-deployed application that employs a microservices architecture across multiple data centers. Reports have received about application slowness. The container orchestration logs show that faults have been raised in a variety of containers that caused them to fail and then spin up brand new instances.
Which two actions can improve the design of the application to identify the faults? (Choose two.)
- A. Automatically pull out the container that fails the most over a time period.
- B. Implement a tagging methodology that follows the application execution from service to service.
- C. Add logging on exception and provide immediate notification.
- D. Do a write to the datastore every time there is an application failure.
- E. Implement an SNMP logging system with alerts in case a network link is slow.
Answer: BC
NEW QUESTION 18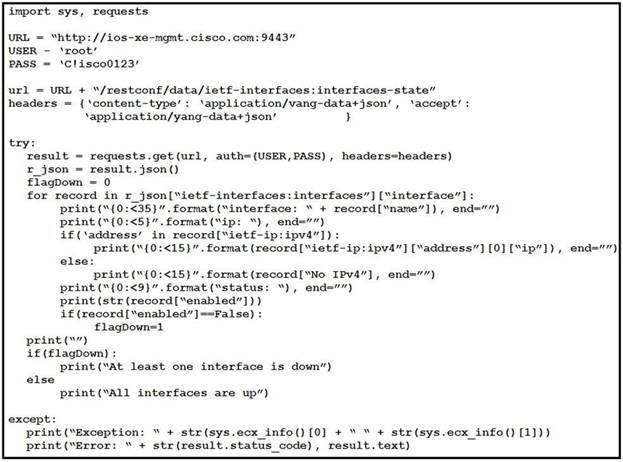
Refer to the exhibit. What is the output of this IOS-XE configuration program?
- A. interface operational status in IPv6 addresses
- B. interface administrative status in IPv4 addresses
- C. interface operational status in IPv4 addresses
- D. interface administrative status in IPv6 addresses
Answer: D
NEW QUESTION 19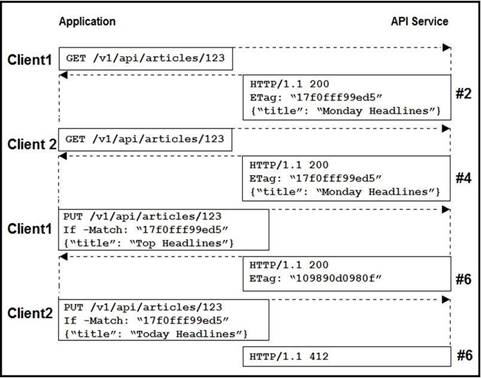
Refer to the exhibit. Two editors are concurrently updating an article’s headline from their mobile devices. What results from this scenario based on this REST API sequence?
- A. The article is marked as “Conflicted”
- B. The article headline is “Monday Headlines”
- C. The article headline is “Today Headlines”
- D. The article headline is “Top Headlines”
Answer: B
NEW QUESTION 20
User report that they can no longer process transactions with the online ordering application, and the logging dashboard is displaying these messages.
Fri Jan 10 19:37:31.123 EST 2021 [FRONTEND] INFO: Incoming request to add item to cart from user 45834534858 Fri Jan 10 19:37:31 247 EST 2021 [BACKEND] INFO: Attempting to add item to cart
Fri Jan 10 19:37:31 250 EST 2021 [BACKEND] ERROR: Failed to add item: MYSQLDB ERROR: Connection refused What is causing the problem seen in these log messages?
- A. The database server container has crashed.
- B. The backend process is overwhelmed with too many transactions.
- C. The backend is not authorized to commit to the database.
- D. The user is not authorized to add the item to their cart.
Answer: A
NEW QUESTION 21
Which two techniques protect against injection attacks? (Choose two.)
- A. input validation
- B. trim whitespace
- C. limit text areas to 255 characters
- D. string escaping of user free text and data entry
- E. only use dropdown, checkbox, and radio button fields
Answer: AE
NEW QUESTION 22
A network operations team is using the cloud to automate some of their managed customer and branch locations. They require that all of their tooling be ephemeral by design and that the entire automation environment can be recreated without manual commands. Automation code and configuration state will be stored in git for change control and versioning. The engineering high-level plan is to use VMs in a cloud-provider environment then configure open source tooling onto these VMs to poll, test, and configure the remote devices, as well as deploy the tooling itself.
Which configuration management and/or automation tooling is needed for this solution?
- A. Ansible
- B. Ansible and Terraform
- C. NSO
- D. Terraform
- E. Ansible and NSO
Answer: B
NEW QUESTION 23
Refer to the exhibit. Which two functions are performed by the load balancer when it handles traffic originating from the Internet destined to an application hosted on the file server farm? (Choose two.)
- A. Terminate the TLS over the UDP connection from the router and originate an HTTPS connection to the selected server.
- B. Terminate the TLS over the UDP connection from the router and originate an HTTP connection to the selected server.
- C. Terminate the TLS over the TCP connection from the router and originate an HTTP connection to the selected server.
- D. Terminate the TLS over the TCP connection from the router and originate an HTTPS connection to the selected server.
- E. Terminate the TLS over the SCTP connection from the router and originate an HTTPS connection to the selected server.
Answer: DE
NEW QUESTION 24
......
P.S. Easily pass 350-901 Exam with 0 Q&As Dumps-files.com Dumps & pdf Version, Welcome to Download the Newest Dumps-files.com 350-901 Dumps: https://www.dumps-files.com/files/350-901/ (0 New Questions)