Updated Ethical Hacking And Countermeasures (CEHv6) 312-50 Pdf Exam
It is impossible to pass EC-Council 312-50 exam without any help in the short term. Come to Actualtests soon and find the most advanced, correct and guaranteed EC-Council 312-50 practice questions. You will get a surprising result by our Update Ethical Hacking and Countermeasures (CEHv6) practice guides.
Online 312-50 free questions and answers of New Version:
NEW QUESTION 1
An nmap command that includes the host specification of 202.176.56-57.* will scan ____ number of hosts.
- A. 2
- B. 256
- C. 512
- D. Over 10,000
Answer: C
Explanation:
The hosts with IP address 202.176.56.0-255 & 202.176.56.0-255 will be scanned (256+256=512)
NEW QUESTION 2
What is the name of the software tool used to crack a single account on Netware Servers using a dictionary attack?
- A. NPWCrack
- B. NWPCrack
- C. NovCrack
- D. CrackNov
- E. GetCrack
Answer: B
Explanation:
NWPCrack is the software tool used to crack single accounts on Netware servers.
NEW QUESTION 3
Which of the following tools are used for enumeration? (Choose three.)
- A. SolarWinds
- B. USER2SID
- C. Cheops
- D. SID2USER
- E. DumpSec
Answer: BDE
Explanation:
USER2SID, SID2USER, and DumpSec are three of the tools used for system enumeration. Others are tools such as NAT and Enum. Knowing which tools are used in each step of the hacking methodology is an important goal of the CEH exam. You should spend a portion of your time preparing for the test practicing with the tools and learning to understand their output.
NEW QUESTION 4
Which are true statements concerning the BugBear and Pretty Park worms? Select the best answers.
- A. Both programs use email to do their work.
- B. Pretty Park propagates via network shares and email
- C. BugBear propagates via network shares and email
- D. Pretty Park tries to connect to an IRC server to send your personal passwords.
- E. Pretty Park can terminate anti-virus applications that might be running to bypass them.
Answer: ACD
Explanation:
Explanations: Both Pretty Park and BugBear use email to spread. Pretty Park cannot propagate via network shares, only email. BugBear propagates via network shares and email. It also terminates anti-virus applications and acts as a backdoor server for someone to get into the infected machine. Pretty Park tries to connect to an IRC server to send your personal passwords and all sorts of other information it retrieves from your PC.
Pretty Park cannot terminate anti-virus applications. However, BugBear can terminate AV software so that it can bypass them.
NEW QUESTION 5
What do you call a system where users need to remember only one username and password, and be authenticated for multiple services?
- A. Simple Sign-on
- B. Unique Sign-on
- C. Single Sign-on
- D. Digital Certificate
Answer: C
Explanation:
Single sign-on (SSO) is a specialized form of software authentication that enables a user to authenticate once and gain access to the resources of multiple software systems.
NEW QUESTION 6
What is the proper response for a X-MAS scan if the port is closed?
- A. SYN
- B. ACK
- C. FIN
- D. PSH
- E. RST
- F. No response
Answer: E
Explanation:
Closed ports respond to a X-MAS scan with a RST.
NEW QUESTION 7
In order to attack wireless network, you put up an access point and override the signal of the real access point. And when users send authentication data, you are able to capture it. What kind of attack is this?
- A. WEP Attack
- B. Drive by hacking
- C. Rogue Access Point Attack
- D. Unauthorized Access Point Attack
Answer: C
Explanation:
A rogue access point is a wireless access point that has either been installed on a secure company network without explicit authorization from a local network management or has been created to allow a cracker to conduct a man-in-the-middle attack.
NEW QUESTION 8
You are gathering competitive intelligence on an organization. You notice that they have jobs listed on a few Internet job-hunting sites. There are two jobs for network and system administrators. How can this help you in foot printing the organization?
- A. To learn about the IP range used by the target network
- B. To identify the number of employees working for the company
- C. To test the limits of the corporate security policy enforced in the company
- D. To learn about the operating systems, services and applications used on the network
Answer: D
NEW QUESTION 9
The United Kingdom (UK) he passed a law that makes hacking into an unauthorized network a felony.
The law states:
Section1 of the Act refers to unauthorized access to computer material. This states that a person commits an offence if he causes a computer to perform any function with intent to secure unauthorized access to any program or data held in any computer. For a successful conviction under this part of the Act, the prosecution must prove that the access secured is unauthorized and that the suspect knew that this was the case. This section is designed to deal with common-or-graden hacking.
Section 2 of the deals with unauthorized access with intent to commit or facilitate the commission of further offences. An offence is committed under Section 2 if a Section 1 offence has been committed and there is the intention of committing or facilitating a further offense (any offence which attacks a custodial sentence of more than five years, not necessarily one covered but the Act). Even if it is not possible to prove the intent to commit the further offence, the Section 1 offence is still committed.
Section 3 Offences cover unauthorized modification of computer material, which generally means the creation and distribution of viruses. For conviction to succeed there must have been the intent to cause the modifications and knowledge that the modification had not been authorized
What is the law called?
- A. Computer Misuse Act 1990
- B. Computer incident Act 2000
- C. Cyber Crime Law Act 2003
- D. Cyber Space Crime Act 1995
Answer: A
Explanation:
Computer Misuse Act (1990) creates three criminal offences:
✑ Unauthorised access to computer material
✑ Unauthorised access to a computer system with intent to commit or facilitate the commission of a further offence
✑ Unauthorised modification of computer material
NEW QUESTION 10
What is the disadvantage of an automated vulnerability assessment tool?
- A. Ineffective
- B. Slow
- C. Prone to false positives
- D. Prone to false negatives
- E. Noisy
Answer: E
Explanation:
Vulnerability assessment tools perform a good analysis of system vulnerabilities; however, they are noisy and will quickly trip IDS systems.
NEW QUESTION 11
Steven works as a security consultant and frequently performs penetration tests for Fortune 500 companies. Steven runs external and internal tests and then creates reports to show the companies where their weak areas are. Steven always signs a non-disclosure agreement before performing his tests. What would Steven be considered?
- A. Whitehat Hacker
- B. BlackHat Hacker
- C. Grayhat Hacker
- D. Bluehat Hacker
Answer: A
Explanation:
A white hat hacker, also rendered as ethical hacker, is, in the realm of information technology, a person who is ethically opposed to the abuse of computer systems. Realization that the Internet now represents human voices from around the world has made the defense of its integrity an important pastime for many. A white hat generally focuses on securing IT systems, whereas a black hat (the opposite) would like to break into them.
NEW QUESTION 12
Which of the following is NOT a valid NetWare access level?
- A. Not Logged in
- B. Logged in
- C. Console Access
- D. Administrator
Answer: D
Explanation:
Administrator is an account not a access level.
NEW QUESTION 13
What does an ICMP (Code 13) message normally indicates?
- A. It indicates that the destination host is unreachable
- B. It indicates to the host that the datagram which triggered the source quench message will need to be re-sent
- C. It indicates that the packet has been administratively dropped in transit
- D. It is a request to the host to cut back the rate at which it is sending traffic to the Internet destination
Answer: C
Explanation:
CODE 13 and type 3 is destination unreachable due to communication administratively prohibited by filtering hence maybe they meant "code 13", therefore would be C).
Note:A - Type 3B - Type 4C - Type 3 Code 13D - Typ4 4
NEW QUESTION 14
One of the most common and the best way of cracking RSA encryption is to being to derive the two prime numbers, which are used in the RSA PKI mathematical process. If the two numbers p and q are discovered through a process, then the private key can be derived.
- A. Factorization
- B. Prime Detection
- C. Hashing
- D. Brute-forcing
Answer: A
Explanation:
In April 1994, an international cooperative group of mathematicians and computer scientists solved a 17-year-old challenge problem, the factoring of a 129-digit number, called RSA-129, into two primes. That is, RSA-129 = 1143816257578888676692357799761466120102182
9672124236256256184293570693524573389783059
7123563958705058989075147599290026879543541
= 34905295108476509491478496199038 98133417764638493387843990820577 times
32769132993266709549961988190834 461413177642967992942539798288533.
Se more at http://en.wikipedia.org/wiki/RSA_Factoring_Challenge
NEW QUESTION 15
A very useful resource for passively gathering information about a target company is:
- A. Host scanning
- B. Whois search
- C. Traceroute
- D. Ping sweep
Answer: B
Explanation:
A, C & D are "Active" scans, the question says: "Passively"
NEW QUESTION 16
If a competitor wants to cause damage to your organization, steal critical secrets, or put you out of business, they just have to find a job opening, prepare someone to pass the interview, have that person hired, and they will be in the organization.
How would you prevent such type of attacks?
- A. It is impossible to block these attacks
- B. Hire the people through third-party job agencies who will vet them for you
- C. Conduct thorough background checks before you engage them
- D. Investigate their social networking profiles
Answer: C
NEW QUESTION 17
You generate MD5 128-bit hash on all files and folders on your computer to keep a baseline check for security reasons?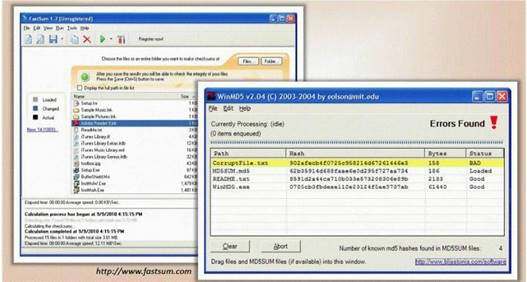
What is the length of the MD5 hash?
- A. 32 bit
- B. 64 byte
- C. 48 char
- D. 128 kb
Answer: C
NEW QUESTION 18
One of the effective DoS/DDoS countermeasures is 'Throttling'. Which statement correctly defines this term?
- A. Set up routers that access a server with logic to adjust incoming traffic to levels that will be safe for the server to process
- B. Providers can increase the bandwidth on critical connections to prevent them from going down in the event of an attack
- C. Replicating servers that can provide additional failsafe protection
- D. Load balance each server in a multiple-server architecture
Answer: A
NEW QUESTION 19
In Trojan terminology, what is a covert channel?
- A. A channel that transfers information within a computer system or network in a way that violates the security policy
- B. A legitimate communication path within a computer system or network for transfer of data
- C. It is a kernel operation that hides boot processes and services to mask detection
- D. It is Reverse tunneling technique that uses HTTPS protocol instead of HTTP protocol to establish connections
Answer: A
NEW QUESTION 20
Because UDP is a connectionless protocol: (Select 2)
- A. UDP recvfrom() and write() scanning will yield reliable results
- B. It can only be used for Connect scans
- C. It can only be used for SYN scans
- D. There is no guarantee that the UDP packets will arrive at their destination
- E. ICMP port unreachable messages may not be returned successfully
Answer: DE
Explanation:
Neither UDP packets, nor the ICMP errors are guaranteed to arrive, so UDP scanners must also implement retransmission of packets that appear to be lost (or you will get a bunch of false positives).
NEW QUESTION 21
A client has approached you with a penetration test requirements. They are concerned with the possibility of external threat, and have invested considerable resources in protecting their Internet exposure. However, their main concern is the possibility of an employee elevating his/her privileges and gaining access to information outside of their respective department.
What kind of penetration test would you recommend that would best address the client’s concern?
- A. A Black Box test
- B. A Black Hat test
- C. A Grey Box test
- D. A Grey Hat test
- E. A White Box test
- F. A White Hat test
Answer: C
NEW QUESTION 22
Null sessions are un-authenticated connections (not using a username or password.) to an NT or 2000 system. Which TCP and UDP ports must you filter to check null sessions on your network?
- A. 137 and 139
- B. 137 and 443
- C. 139 and 443
- D. 139 and 445
Answer: D
Explanation:
NULL sessions take advantage of “features” in the SMB (Server Message Block) protocol that exist primarily for trust relationships. You can establish a NULL session with a Windows host by logging on with a NULL user name and password. Primarily the following ports are vulnerable if they are accessible:
139
TCP
NETBIOS Session Service 139
UDP
NETBIOS Session Service
445
TCP SMB/CIFS
NEW QUESTION 23
Joseph has just been hired on to a contractor company of the Department of Defense as their senior Security Analyst. Joseph has been instructed on the Company’s strict security policies that have been implemented and the policies that have yet to be put in place. Per the Department of Defense, all DoD users and the users of their contractors must use two-factor authentication to access their networks. Joseph has been delegated the task of researching and implementing the best two-factor authentication method for his company. Joseph’s supervisor has told him that they would like to use some type of hardware device in tandem with a security or identifying pin number.
Joseph’s company has already researched using smart cards and all the resources needed to implement them, but found the smart cards to not be cost effective. What type of device should Joseph use for two-factor authentication?
- A. Security token
- B. Biometric device
- C. OTP
- D. Proximity cards
Answer: A
Explanation:
A security token (sometimes called an authentication token) is a small hardware device that the owner carries to authorize access to a network service. The device may be in the form of a smart card or may be embedded in a commonly used object such as a key fob. Security tokens provide an extra level of assurance through a method known as two-factor authentication: the user has a personal identification number (PIN), which authorizes them as the owner of that particular device; the device then displays a number which uniquely identifies the user to the service, allowing them to log in.
NEW QUESTION 24
Network Administrator Patricia is doing an audit of the network. Below are some of her findings concerning DNS. Which of these would be a cause for alarm?
Select the best answer.
- A. There are two external DNS Servers for Internet domain
- B. Both are AD integrated.
- C. All external DNS is done by an ISP.
- D. Internal AD Integrated DNS servers are using private DNS names that are
- E. unregistered.
- F. Private IP addresses are used on the internal network and are registered with the internal AD integrated DNS server.
Answer: A
Explanation:
A: There are two external DNS Servers for Internet domains. Both are AD integrated. This is the correct answer. Having an AD integrated DNS external server is a serious cause for alarm. There is no need for this and it causes vulnerability on the network.
B: All external DNS is done by an ISP.
This is not the correct answer. This would not be a cause for alarm. This would actually reduce the company's network risk as it is offloaded onto the ISP.
C: Internal AD Integrated DNS servers are using private DNS names that are unregistered. This is not the correct answer. This would not be a cause for alarm. This would actually reduce the company's network risk.
D: Private IP addresses are used on the internal network and are registered with the internal AD integrated DNS server.
This is not the correct answer. This would not be a cause for alarm. This would actually reduce the company's network risk.
NEW QUESTION 25
How would you prevent session hijacking attacks?
- A. Using biometrics access tokens secures sessions against hijacking
- B. Using non-Internet protocols like http secures sessions against hijacking
- C. Using hardware-based authentication secures sessions against hijacking
- D. Using unpredictable sequence numbers secures sessions against hijacking
Answer: D
Explanation:
Protection of a session needs to focus on the unique session identifier because it is the only thing that distinguishes users. If the session ID is compromised, attackers can impersonate other users on the system. The first thing is to ensure that the sequence of identification numbers issued by the session management system is unpredictable; otherwise, it's trivial to hijack another user's session. Having a large number of possible session IDs (meaning that they should be very long) means that there are a lot more permutations for an attacker to try.
NEW QUESTION 26
Jim’s organization has just completed a major Linux roll out and now all of the organization’s systems are running the Linux 2.5 kernel. The roll out expenses has posed constraints on purchasing other essential security equipment and software. The organization requires an option to control network traffic and also perform stateful inspection of traffic going into and out of the DMZ.
Which built-in functionality of Linux can achieve this?
- A. IP Tables
- B. IP Chains
- C. IP Sniffer
- D. IP ICMP
Answer: A
Explanation:
iptables is a user space application program that allows a system administrator to configure the netfilter tables, chains, and rules (described above). Because iptables requires elevated privileges to operate, it must be executed by user root, otherwise it fails to function. On most Linux systems, iptables is installed as /sbin/iptables. IP Tables performs stateful inspection while the older IP Chains only performs stateless inspection.
NEW QUESTION 27
......
Recommend!! Get the Full 312-50 dumps in VCE and PDF From Certshared, Welcome to Download: https://www.certshared.com/exam/312-50/ (New 765 Q&As Version)