Simulation 300-206 Braindump 2021
Exam Code: 300-206 (Practice Exam Latest Test Questions VCE PDF)
Exam Name: Implementing Cisco Edge Network Security Solutions
Certification Provider: Cisco
Free Today! Guaranteed Training- Pass 300-206 Exam.
NEW QUESTION 1
Which device can be managed by the Cisco Prime Security Manager?
- A. ASA CX
- B. ISR G2
- C. Nexus
- D. UCM
Answer: A
Explanation:
https://www.cisco.com/c/en/us/td/docs/security/asacx/9-2/user/guide/b_User_Guide_for_ASA_CX_and_PRSM_9_2/prsm-ug-intro.html
NEW QUESTION 2
What can you do to enable inter-interface firewall communication for traffic that flows between two
interfaces of the same security level?
- A. Run the command same-security-traffic permit inter-interface globally.
- B. Run the command same-security-traffic permit intra-interface globally.
- C. Configure both interfaces to have the same security level.
- D. Run the command same-security-traffic permit inter-interface on the interface with the highest security level.
Answer: A
NEW QUESTION 3
If a switch port goes directly into a blocked state only when a superior BPDU is received, what mechanism must be in use?
- A. STP bpdu guard
- B. STP root guard
- C. SPT bpdu filter
Answer: B
NEW QUESTION 4
Which statement describes what the arp outside 1.1.1.1 0192.7gid.0020 command accomplishes?
- A. enable ARP inspection for host 1.1.1.1
- B. configures proxy ARP for host 1.1.1.1
- C. assigns virtual MAC address for host 1.1.1.1
- D. creates static ARP entry for host 1.1.1.1 .
Answer: D
Explanation:
That command adds a static ARP entry to allow ARP responses from the host at 1.1.1.1 with the MAC address 0009.7cbe.2100 on the outside interface http://www.cisco.com/c/en/us/td/docs/security/asa/asa82/configuration/guide/config/fwmode.html#wp1224694
NEW QUESTION 5
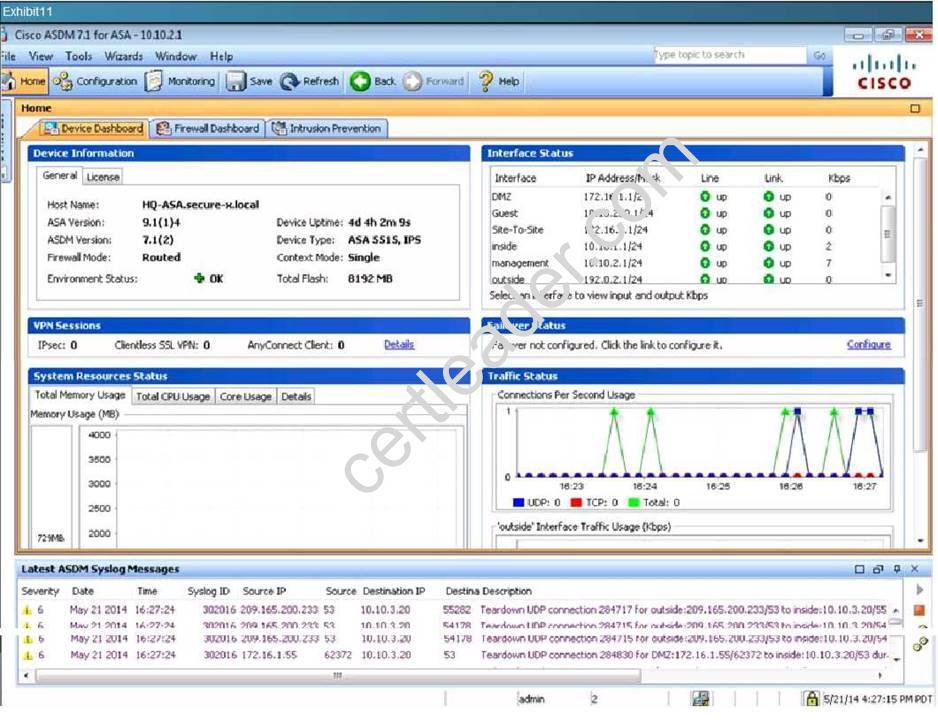
According to the logging configuration on the Cisco ASA, what will happen if syslog server 10.10.2.40
fails?
- A. New connections through the ASA will be blocked and debug system logs will be sent to the internal buffer.
- B. New connections through the ASA will be blocked and informational system logs will be sent to the internalbuffer.
- C. New connections through the ASA will be blocked and system logs will be sent to server 10.10.2.41.
- D. New connections through the ASA will be allowed and system logs will be sent to server 10.10.2.41.
- E. New connections through the ASA will be allowed and informational system logs will be sent to the internalbuffer.
- F. New connections through the ASA will be allowed and debug system logs will be sent to the internal buffer.
Answer: B
Explanation:
This is shown by the following screen shot: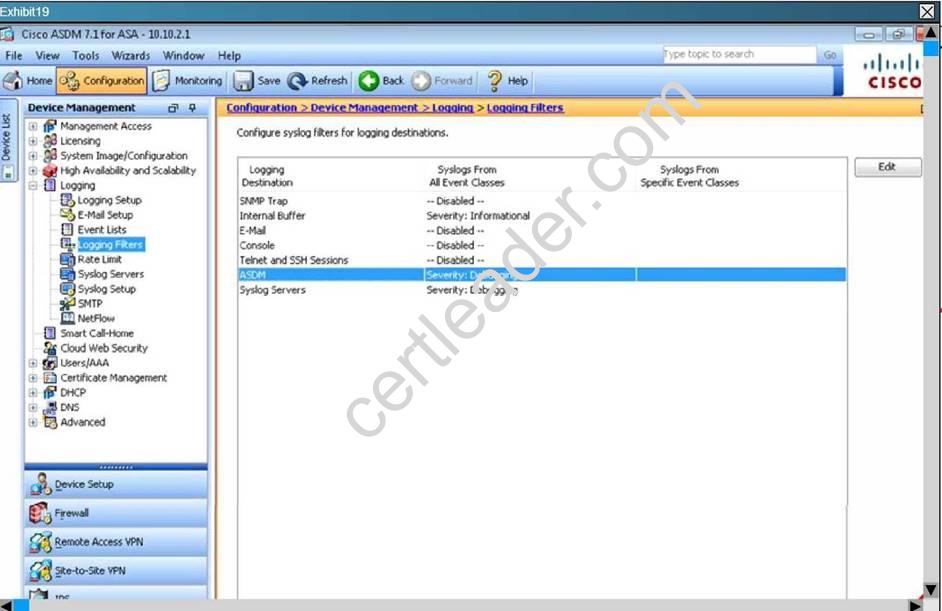
NEW QUESTION 6
In which two modes is zone-based firewall high availability available? (Choose two.)
- A. IPv4 only
- B. IPv6 only
- C. IPv4 and IPv6
- D. routed mode only
- E. transparent mode only
- F. both transparent and routed modes
Answer: CD
NEW QUESTION 7
Which statement about traffic storm control behavior is true?
- A. Traffic storm control cannot determine if the packet is unicast or broadcast.
- B. If you enable broadcast and multicast traffic storm control and the combined broadcast and multicast traffic exceeds the level within a 1 second traffic storm interval, storm control drops all broadcast and multicast traffic until the end of the storm interval
- C. Traffic storm control uses the Individual/Group bit in the packet source address to determine if the packet isunicast or broadcast.
- D. Traffic storm control monitors incoming traffic levels over a 10 second traffic storm control interval
Answer: B
NEW QUESTION 8
When access rule properties are configured within ASDM, which traffic direction type is required by
global and management access rule?
- A. Any
- B. Both in and out
- C. In
- D. Out
Answer: C
NEW QUESTION 9
You moved your servers from physical to virtual infrastructure, how to defend it ?
- A. Cisco V
- B. Cisco ASA 1000V
- C. VXLAN
- D. VSG
Answer: BD
Explanation:
Cisco VSG and the ASA 1000V provide complementary functionalities. The VSG provides virtual machine
context-aware and zone-based security capabilities. The ASA 1000V provides tenant edge security and default gateway functionalities. Together, they provide a trusted and comprehensive virtual and cloud security Portfolio.
From: https://www.cisco.com/c/en/us/products/switches/virtual-security-gateway/index.html
NEW QUESTION 10
Which set of commands enables logging and displays the log buffer on a Cisco ASA?
- A. enable loggingshow logging
- B. logging enableshow logging
- C. enable logging int e0/1view logging
- D. logging enablelogging view config
Answer: B
NEW QUESTION 11
If you disable PortFast on switch ports that are connected to a Cisco ASA and globally turn on BPDU filtering, what is the effect on the switch ports?
- A. The switch ports are prevented from going into an err-disable state if a BPDU is received.
- B. The switch ports are prevented from going into an err-disable state if a BPDU is sent.
- C. The switch ports are prevented from going into an err-disable state if a BPDU is received and sent.
- D. The switch ports are prevented from forming a trunk.
Answer: C
NEW QUESTION 12
Best practices for hardening of management plane have been implemented on an ASA (or IOS router). Which protocols will be affected?
- A. BGP
- B. ICMP
- C. ARP
- D. HTTP
Answer: B
NEW QUESTION 13
Which option is the default logging buffer size In memory of the Cisco ASA adaptive security appliance?
- A. 8KB
- B. 32KB
- C. 2KB
- D. 16KB
- E. 4KB
Answer: E
Explanation:
http://www.cisco.com/c/en/us/td/docs/security/asa/asa91/configuration/general/asa_91_general_c onfig/ monitor_syslog.html
NEW QUESTION 14
Which Cisco TrustSec role does a Cisco ASA firewall serve within an identity architecture?
- A. Access Requester
- B. Policy Decision Point
- C. Policy Information Point
- D. Policy Administration Point
- E. Policy Enforcement Point
Answer: E
NEW QUESTION 15
Refer to the exhibit.
Which option describes the expected result of the capture ACL?
- A. The capture is applied, but we cannot see any packets in the capture
- B. The capture does not get applied and we get an error about mixed policy.
- C. The capture is applied and we can see the packets in the capture
- D. The capture is not applied because we must have a host IP as the source
Answer: B
NEW QUESTION 16
Refer to the exhibit. An engineer has configured NAT rules on an ASA using ASDM. Which action does rule Number 1 accomplish?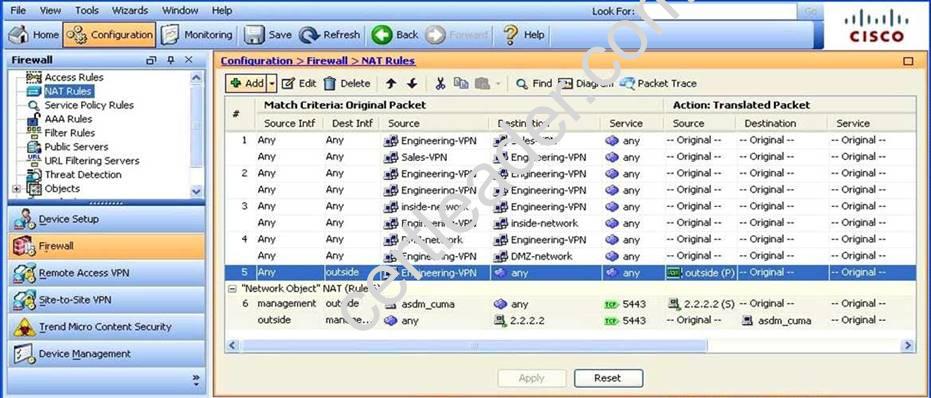
- A. It allows the engineering VPN address pool to access the Internet through the tunnel
- B. It allows hosts in the address pool to reach other hosts in the engineering VPN address pool
- C. It allows hosts in the engineering VPN object to reach the hosts in the Sales VPN without being nat-ed
- D. It allows the connection between the engineering VPN address pool and the DMZ network
Answer: C
NEW QUESTION 17
What are three attributes that can be applied to a user account with RBAC? (Choose three.)
- A. domain
- B. password
- C. ACE tag
- D. user roles
- E. VDC group tag
- F. expiry date
Answer: BDF
NEW QUESTION 18
DRAG DROP
Drag and Drop Syslog security level to match its related.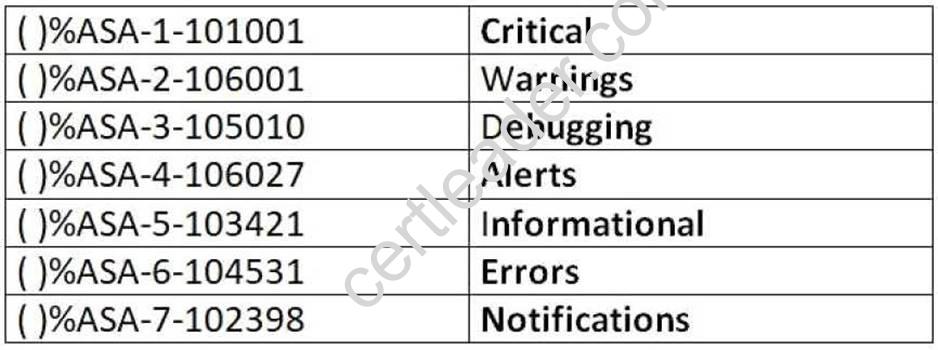
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 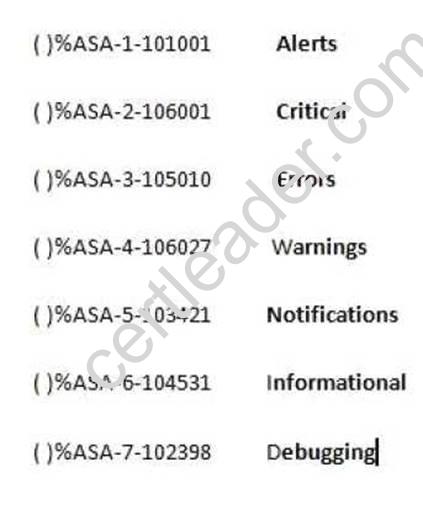
NEW QUESTION 19
Private VLANs have been configured in the data center. Which type of Private VLAN port would allow a new server to communicate with all other interfaces?
- A. isolated
- B. community
- C. private
- D. promiscuous
- E. shared
Answer: D
NEW QUESTION 20
Which two features block traffic that is sourced from non-topological IPv6 addresses? (Choose two.)
- A. DHCPv6 Guard
- B. IPv6 Prefix Guard
- C. IPv6 RA Guard
- D. IPv6 Source Guard
Answer: BD
NEW QUESTION 21
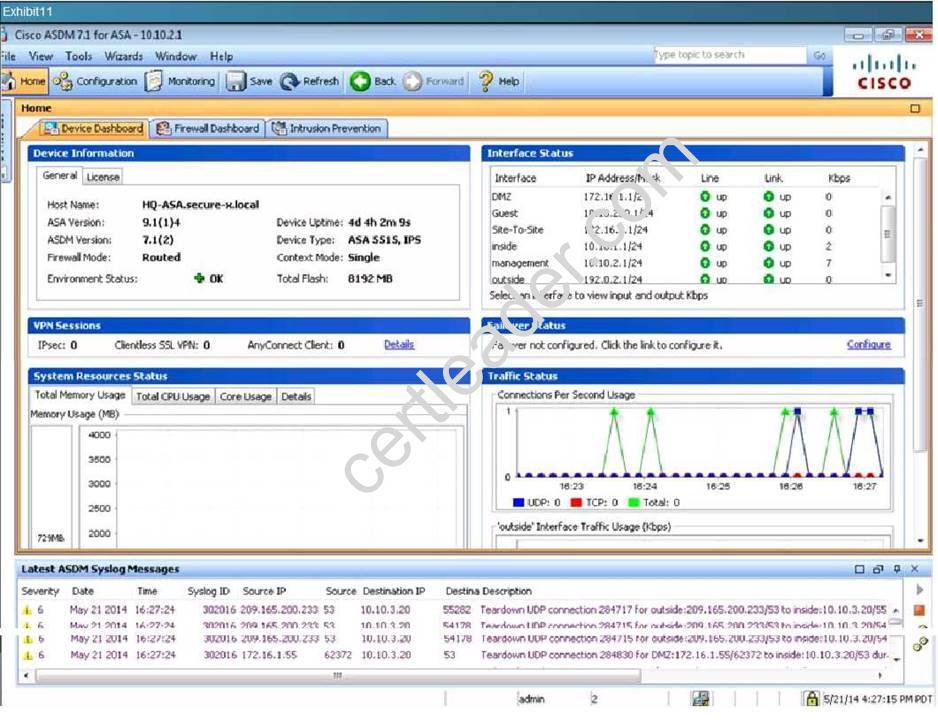
In your role as network security administrator, you have installed syslog server software on a server
whose IP address is 10.10.2.40. According to the exhibits, why isn't the syslog server receiving any syslog messages?
- A. Logging is not enabled globally on the Cisco ASA.
- B. The syslog server has failed.
- C. There have not been any events with a severity level of seven.
- D. The Cisco ASA is not configured to log messages to the syslog server at that IP address.
Answer: B
Explanation:
By process of elimination, we know that the other answers choices are not correct so that only leaves us with the server must have failed. We can see from the following screen shots, that events are being generated with severity level of debugging and below, The 10.10.2.40 IP address has been configured as a syslog server, and that logging has been enabled globally: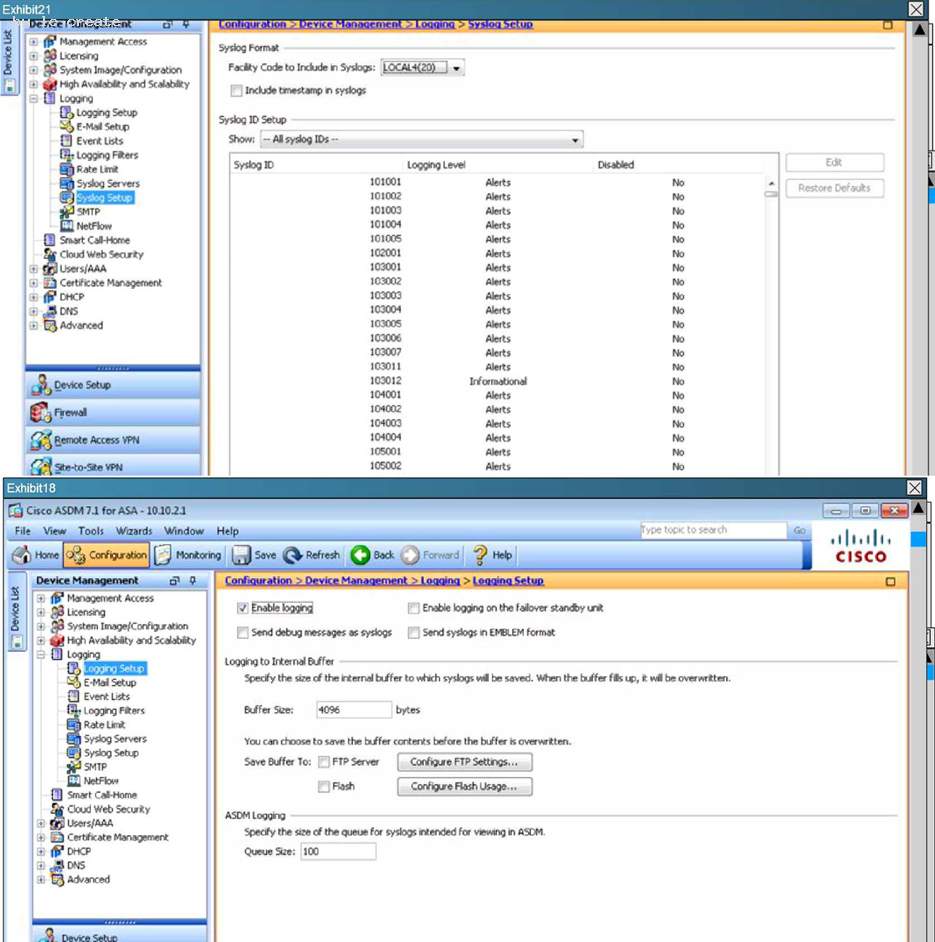
NEW QUESTION 22
When configured in accordance to Cisco best practices, the ip verify source command can mitigate which two types of Layer 2 attacks? (Choose two.)
- A. rogue DHCP servers
- B. ARP attacks
- C. DHCP starvation
- D. MAC spoofing
- E. CAM attacks
- F. IP spoofing
Answer: DF
NEW QUESTION 23
Which benefit of using centralized management to manage a Cisco IronPort ESA is true?
- A. It reduces licensing cost
- B. It requires no initial setup
- C. It requires a light client on managed devices
- D. It reduces administration time
Answer: D
NEW QUESTION 24
Which statement describes a unique feature of Cisco NetFlow Secure Event Logging for Cisco ASAs?
- A. Multiple NetFlow collectors and NetFlow exporters are supported.
- B. Secure NetFlow connections are optimized for Cisco Prime Infrastructure.
- C. Flow-create events are delayed, which reduce overall traffic.
- D. Advanced NetFlow v9 templates and legacy v5 formatting are supported.
Answer: C
NEW QUESTION 25
What is the default behavior of an access list on the Cisco ASA security appliance?
- A. It will permit or deny traffic based on the access-list criteria.
- B. It will permit or deny all traffic on a specified interface.
- C. An access group must be configured before the access list will take effect for traffic control.
- D. It will allow all traffic.
Answer: C
NEW QUESTION 26
Which three options correctly identify the Cisco ASA1000V Cloud Firewall? (Choose three.)
- A. operates at Layer 2
- B. operates at Layer 3
- C. secures tenant edge traffic
- D. secures intraswitch traffic
- E. secures data center edge traffic
- F. replaces Cisco VSG
- G. complements Cisco VSG
- H. requires Cisco VSG
Answer: BCG
NEW QUESTION 27
Which Cisco ASA show command groups the xlates and connections information together in its
output?
- A. show conn
- B. show conn detail
- C. show xlate
- D. show asp
- E. show local-host
Answer: E
NEW QUESTION 28
What are two reasons for implementing NIPS at enterprise Internet edges? (Choose two.)
- A. Internet edges typically have a lower volume of traffic and threats are easier to detect.
- B. Internet edges typically have a higher volume of traffic and threats are more difficult to detect.
- C. Internet edges provide connectivity to the Internet and other external networks.
- D. Internet edges are exposed to a larger array of threats.
- E. NIPS is more optimally designed for enterprise Internet edges than for internal network configurations.
Answer: CD
NEW QUESTION 29
Which two attacks are common at Layer 2? (Choose two)
- A. teardrop attack
- B. MAC spoofing
- C. DHCP spoofing
- D. ICMP attacks
- E. packet sniffing
Answer: BC
NEW QUESTION 30
......
P.S. Simply pass now are offering 100% pass ensure 300-206 dumps! All 300-206 exam questions have been updated with correct answers: https://www.simply-pass.com/Cisco-exam/300-206-dumps.html (411 New Questions)