What Best Quality 200-201 Exam Dumps Is
Your success in Cisco 200-201 is our sole target and we develop all our 200-201 braindumps in a way that facilitates the attainment of this target. Not only is our 200-201 study material the best you can find, it is also the most detailed and the most updated. 200-201 Practice Exams for Cisco 200-201 are written to the highest standards of technical accuracy.
Cisco 200-201 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Which two compliance frameworks require that data be encrypted when it is transmitted over a public network?
(Choose two.)
- A. PCI
- B. GLBA
- C. HIPAA
- D. SOX
- E. COBIT
Answer: AC
NEW QUESTION 2
The target web application server is running as the root user and is vulnerable to command injection. Which result of a successful attack is true?
- A. cross-site scripting
- B. cross-site scripting request forgery
- C. privilege escalation
- D. buffer overflow
Answer: B
NEW QUESTION 3
When communicating via TLS, the client initiates the handshake to the server and the server responds back with its certificate for identification.
Which information is available on the server certificate?
- A. server name, trusted subordinate CA, and private key
- B. trusted subordinate CA, public key, and cipher suites
- C. trusted CA name, cipher suites, and private key
- D. server name, trusted CA, and public key
Answer: D
NEW QUESTION 4
Which principle is being followed when an analyst gathers information relevant to a security incident to determine the appropriate course of action?
- A. decision making
- B. rapid response
- C. data mining
- D. due diligence
Answer: A
NEW QUESTION 5
An analyst is exploring the functionality of different operating systems.
What is a feature of Windows Management Instrumentation that must be considered when deciding on an operating system?
- A. queries Linux devices that have Microsoft Services for Linux installed
- B. deploys Windows Operating Systems in an automated fashion
- C. is an efficient tool for working with Active Directory
- D. has a Common Information Model, which describes installed hardware and software
Answer: D
NEW QUESTION 6
An organization has recently adjusted its security stance in response to online threats made by a known hacktivist group.
What is the initial event called in the NIST SP800-61?
- A. online assault
- B. precursor
- C. trigger
- D. instigator
Answer: B
NEW QUESTION 7
Which security principle requires more than one person is required to perform a critical task?
- A. least privilege
- B. need to know
- C. separation of duties
- D. due diligence
Answer: C
NEW QUESTION 8
Refer to the exhibit.
Which packet contains a file that is extractable within Wireshark?
- A. 2317
- B. 1986
- C. 2318
- D. 2542
Answer: D
NEW QUESTION 9
Which two elements are used for profiling a network? (Choose two.)
- A. session duration
- B. total throughput
- C. running processes
- D. listening ports
- E. OS fingerprint
Answer: DE
NEW QUESTION 10
Refer to the exhibit.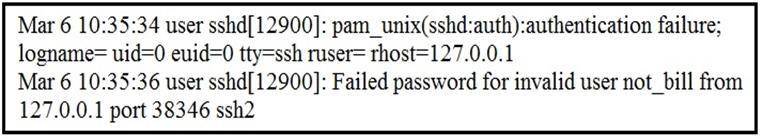
In which Linux log file is this output found?
- A. /var/log/authorization.log
- B. /var/log/dmesg
- C. var/log/var.log
- D. /var/log/auth.log
Answer: D
NEW QUESTION 11
Drag and drop the security concept on the left onto the example of that concept on the right.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 
NEW QUESTION 12
What is the difference between a threat and a risk?
- A. Threat represents a potential danger that could take advantage of a weakness in a system
- B. Risk represents the known and identified loss or danger in the system
- C. Risk represents the nonintentional interaction with uncertainty in the system
- D. Threat represents a state of being exposed to an attack or a compromise either physically or logically
Answer: A
NEW QUESTION 13
What is the difference between an attack vector and attack surface?
- A. An attack surface identifies vulnerabilities that require user input or validation; and an attack vectoridentifies vulnerabilities that are independent of user actions.
- B. An attack vector identifies components that can be exploited; and an attack surface identifies the potential path an attack can take to penetrate the network.
- C. An attack surface recognizes which network parts are vulnerable to an attack; and an attack vector identifies which attacks are possible with these vulnerabilities.
- D. An attack vector identifies the potential outcomes of an attack; and an attack surface launches an attack using several methods against the identified vulnerabilities.
Answer: C
NEW QUESTION 14
Which open-sourced packet capture tool uses Linux and Mac OS X operating systems?
- A. NetScout
- B. tcpdump
- C. SolarWinds
- D. netsh
Answer: B
NEW QUESTION 15
A SOC analyst is investigating an incident that involves a Linux system that is identifying specific sessions. Which identifier tracks an active program?
- A. application identification number
- B. active process identification number
- C. runtime identification number
- D. process identification number
Answer: D
NEW QUESTION 16
......
Thanks for reading the newest 200-201 exam dumps! We recommend you to try the PREMIUM Downloadfreepdf.net 200-201 dumps in VCE and PDF here: https://www.downloadfreepdf.net/200-201-pdf-download.html (98 Q&As Dumps)