Up To The Immediate Present Understanding Cisco Cybersecurity Operations Fundamentals 200-201 Test
Cause all that matters here is passing the Cisco 200-201 exam. Cause all that you need is a high score of 200-201 Understanding Cisco Cybersecurity Operations Fundamentals exam. The only one thing you need to do is downloading Exambible 200-201 exam study guides now. We will not let you down with our money-back guarantee.
Free demo questions for Cisco 200-201 Exam Dumps Below:
NEW QUESTION 1
Which attack method intercepts traffic on a switched network?
- A. denial of service
- B. ARP cache poisoning
- C. DHCP snooping
- D. command and control
Answer: C
NEW QUESTION 2
Which metric is used to capture the level of access needed to launch a successful attack?
- A. privileges required
- B. user interaction
- C. attack complexity
- D. attack vector
Answer: A
NEW QUESTION 3
What is a purpose of a vulnerability management framework?
- A. identifies, removes, and mitigates system vulnerabilities
- B. detects and removes vulnerabilities in source code
- C. conducts vulnerability scans on the network
- D. manages a list of reported vulnerabilities
Answer: A
NEW QUESTION 4
How is attacking a vulnerability categorized?
- A. action on objectives
- B. delivery
- C. exploitation
- D. installation
Answer: C
NEW QUESTION 5
When trying to evade IDS/IPS devices, which mechanism allows the user to make the data incomprehensible without a specific key, certificate, or password?
- A. fragmentation
- B. pivoting
- C. encryption
- D. stenography
Answer: D
NEW QUESTION 6
What is an example of social engineering attacks?
- A. receiving an unexpected email from an unknown person with an uncharacteristic attachment from someone in the same company
- B. receiving an email from human resources requesting a visit to their secure website to update contact information
- C. sending a verbal request to an administrator who knows how to change an account password
- D. receiving an invitation to the department’s weekly WebEx meeting
Answer: B
NEW QUESTION 7
Which IETF standard technology is useful to detect and analyze a potential security incident by recording session flows that occurs between hosts?
- A. SFlow
- B. NetFlow
- C. NFlow
- D. IPFIX
Answer: D
NEW QUESTION 8
Which regex matches only on all lowercase letters?
- A. [az]+
- B. [^az]+
- C. az+
- D. a*z+
Answer: A
NEW QUESTION 9
What is a benefit of agent-based protection when compared to agentless protection?
- A. It lowers maintenance costs
- B. It provides a centralized platform
- C. It collects and detects all traffic locally
- D. It manages numerous devices simultaneously
Answer: B
NEW QUESTION 10
An analyst received an alert on their desktop computer showing that an attack was successful on the host. After investigating, the analyst discovered that no mitigation action occurred during the attack. What is the reason for this discrepancy?
- A. The computer has a HIPS installed on it.
- B. The computer has a NIPS installed on it.
- C. The computer has a HIDS installed on it.
- D. The computer has a NIDS installed on it.
Answer: C
NEW QUESTION 11
Which step in the incident response process researches an attacking host through logs in a SIEM?
- A. detection and analysis
- B. preparation
- C. eradication
- D. containment
Answer: A
NEW QUESTION 12
Which list identifies the information that the client sends to the server in the negotiation phase of the TLS handshake?
- A. ClientStart, ClientKeyExchange, cipher-suites it supports, and suggested compression methods
- B. ClientStart, TLS versions it supports, cipher-suites it supports, and suggested compression methods
- C. ClientHello, TLS versions it supports, cipher-suites it supports, and suggested compression methods
- D. ClientHello, ClientKeyExchange, cipher-suites it supports, and suggested compression methods
Answer: C
NEW QUESTION 13
Refer to the exhibit.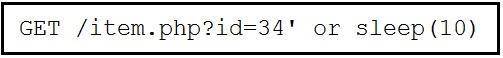
This request was sent to a web application server driven by a database. Which type of web server attack is represented?
- A. parameter manipulation
- B. heap memory corruption
- C. command injection
- D. blind SQL injection
Answer: D
NEW QUESTION 14
What causes events on a Windows system to show Event Code 4625 in the log messages?
- A. The system detected an XSS attack
- B. Someone is trying a brute force attack on the network
- C. Another device is gaining root access to the system
- D. A privileged user successfully logged into the system
Answer: B
NEW QUESTION 15
Why is encryption challenging to security monitoring?
- A. Encryption analysis is used by attackers to monitor VPN tunnels.
- B. Encryption is used by threat actors as a method of evasion and obfuscation.
- C. Encryption introduces additional processing requirements by the CPU.
- D. Encryption introduces larger packet sizes to analyze and store.
Answer: B
NEW QUESTION 16
......
Recommend!! Get the Full 200-201 dumps in VCE and PDF From Surepassexam, Welcome to Download: https://www.surepassexam.com/200-201-exam-dumps.html (New 98 Q&As Version)