Breathing Jn0-333 Samples 2021
We provide real jn0-333 exam questions and answers braindumps in two formats. Download PDF & Practice Tests. Pass Juniper jn0-333 Exam quickly & easily. The jn0-333 PDF type is available for reading and printing. You can print more and practice many times. With the help of our Juniper jn0-333 dumps pdf and vce product and material, you can easily pass the jn0-333 exam.
Juniper jn0-333 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Click the Exhibit button. Referring to the exhibit, what will happen if client 172.16.128.50 tries to connect to destination 192.168.150.3 using HTTP?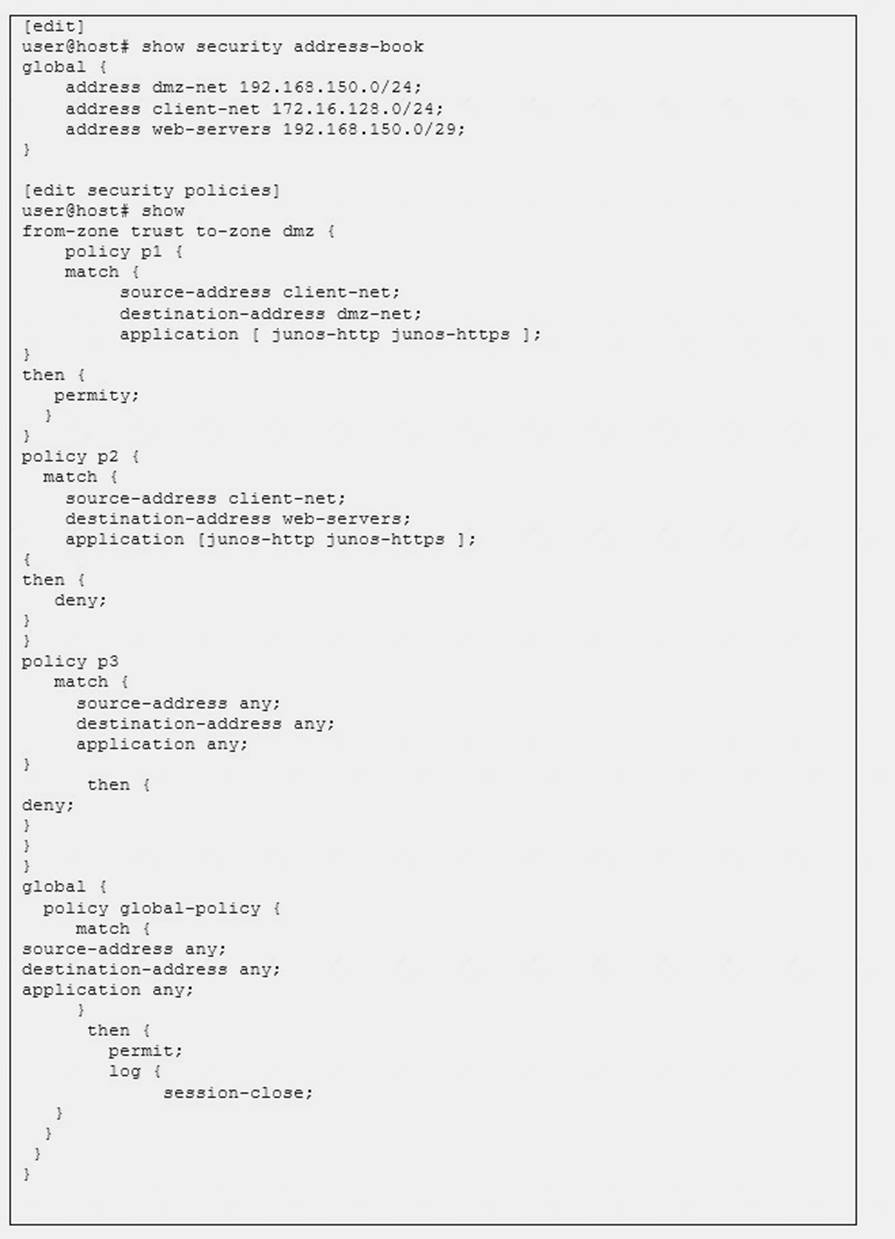
- A. The client will be permitted by policy p1.
- B. The client will be denied by policy p3.
- C. The client will be denied by policy p2.
- D. The client will be permitted by the global policy.
Answer: D
NEW QUESTION 2
Click the Exhibit button.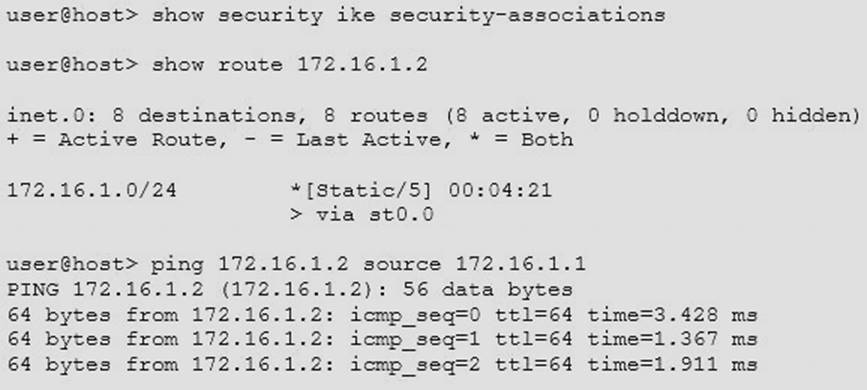
You have an IPsec tunnel between two devices. You clear the IKE security associations, but traffic continues to flow across the tunnel.
Referring to the exhibit, which statement is correct in this scenario?
- A. The IPsec security association is independent from the IKE security association
- B. The traffic is no longer encrypted
- C. The IKE security association immediately reestablishes
- D. The traffic is using an alternate path
Answer: AB
NEW QUESTION 3
Which SRX5400 component is responsible for performing first pass security policy inspection?
- A. Routing Engine
- B. Switch Control Board
- C. Services Processing Unit
- D. Modular Port Concentrator
Answer: C
NEW QUESTION 4
What are three valid virtual interface types for a vSRX? (Choose three.)
- A. SR-IOV
- B. fxp0
- C. eth0
- D. VMXNET 3
- E. virtio
Answer: ABD
NEW QUESTION 5
Click the Exhibit button.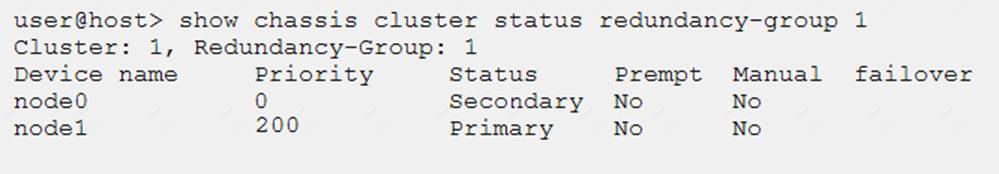
Which two statements describe the output shown in the exhibit? (Choose two.)
- A. Node 0 is controlling traffic for redundancy group 1.
- B. Node 1 is controlling traffic for redundancy group 1.
- C. Redundancy group 1 experienced an operational failure.
- D. Redundancy group 1 was administratively failed over.
Answer: BD
NEW QUESTION 6
Which feature is used when you want to permit traffic on an SRX Series device only at specific times?
- A. scheduler
- B. pass-through authentication
- C. ALGs
- D. counters
Answer: A
NEW QUESTION 7
You want to trigger failover of redundancy group 1 currently running on node 0 and make node 1 the primary node the redundancy group 1.
Which command would be used accomplish this task?
- A. user@host# set chassis cluster redundancy-group 1 node 1
- B. user@host> request chassis cluster failover redundancy-group 1 node 1
- C. user@host# set chassis cluster redundancy-group 1 preempt
- D. user@host> request chassis cluster failover reset redundancy-group 1
Answer: B
NEW QUESTION 8
You want to implement IPsec on your SRX Series devices, but you do not want to use a preshared key. Which IPsec implementation should you use?
- A. public key infrastructure
- B. next-hop tunnel binding
- C. tunnel mode
- D. aggressive mode
Answer: A
NEW QUESTION 9
Which host-inbound-traffic security zone parameter would allow access to the REST API configured to listen on custom TCP port 5080?
- A. http
- B. all
- C. xnm-clear-text
- D. any-service
Answer: D
NEW QUESTION 10
You need to configure an IPsec tunnel between a remote site and a hub site. The SRX Series device at the remote site receives a dynamic IP address on the external interface that you will use for IPsec.
Which feature would you need to configure in this scenario?
- A. NAT-T
- B. crypto suite B
- C. aggressive mode
- D. IKEv2
Answer: C
NEW QUESTION 11
Click the Exhibit button.
You are trying to create a security policy on your SRX Series device that permits HTTP traffic from your private 172.25.11.0/24 subnet to the Internet. You create a policy named permit – http between the trust and untrust zones that permits HTTP traffic.
When you issue a commit command to apply the configuration changes, the commit fails with the error shown in the exhibit.
Which two actions would correct the error? (Choose two.)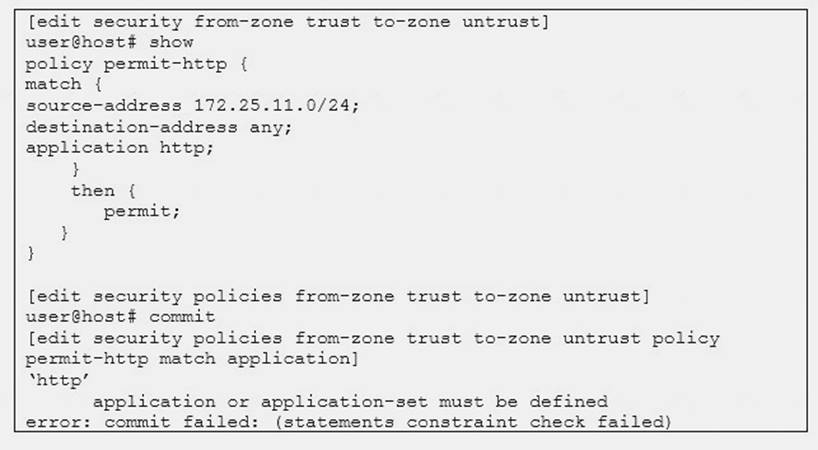
- A. Create a custom application named http at the [edit applications] hierarchy.
- B. Execute the Junos commit full command to override the error and apply the configuration.
- C. Modify the security policy to use the built-in junos-http application.
- D. Issue the rollback 1 command from the top of the configuration hierarchy and attempt the commit again.
Answer: BC
NEW QUESTION 12
Which three statements describes traditional firewalls? (Choose three.)
- A. A traditional firewall performs stateless packet processing.
- B. A traditional firewall offers encapsulation, authentication, and encryption.
- C. A traditional firewall performs stateful packet processing.
- D. A traditional firewall forwards all traffic by default.
- E. A traditional firewall performs NAT and PAT.
Answer: BCE
NEW QUESTION 13
You recently configured an IPsec VPN between two SRX Series devices. You notice that the Phase1 negotiation succeeds and the Phase 2 negotiation fails.
Which two configuration parameters should you verify are correct? (Choose two.)
- A. Verify that the IKE gateway proposals on the initiator and responder are the same.
- B. Verify that the VPN tunnel configuration references the correct IKE gateway.
- C. Verify that the IKE initiator is configured for main mode.
- D. Verify that the IPsec policy references the correct IKE proposals.
Answer: AB
NEW QUESTION 14
Which action will restrict SSH access to an SRX Series device from a specific IP address which is connected to a security zone named trust?
- A. Implement a firewall filter on the security zone trust.
- B. Implement a security policy from security zone junos-host to security zone trust.
- C. Implement host-inbound-traffic system-services to allow SSH.
- D. Implement a security policy from security zone trust to security zone junos-host.
Answer: D
NEW QUESTION 15
You want to support reth LAG interfaces on a chassis cluster.
Which setting must be enabled on the interconnecting switch to accomplish this task?
- A. RSTP
- B. 802.3ad
- C. swfab
- D. LLDP
Answer: B
NEW QUESTION 16
Click the Exhibit button.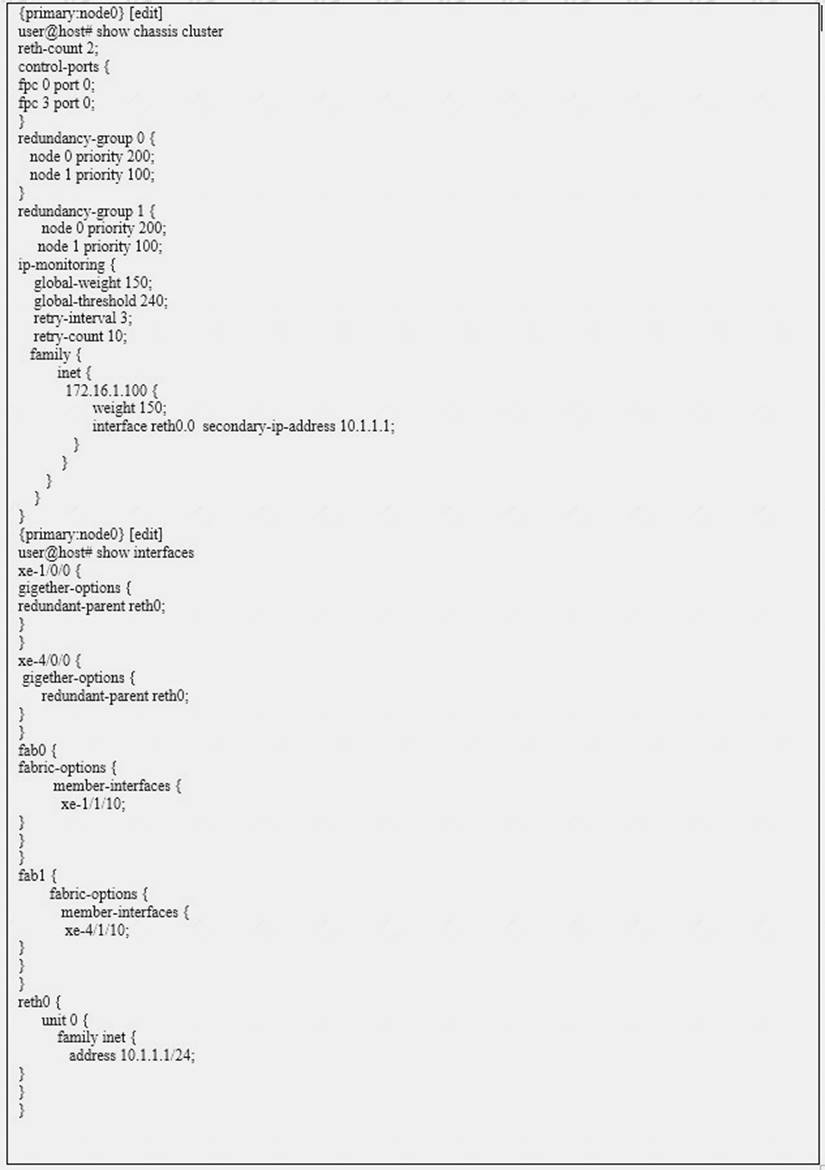
Which statement would explain why the IP-monitoring feature is functioning incorrectly?
- A. The global weight value is too large for the configured global threshold.
- B. The secondary IP address should be on a different subnet than the reth IP address.
- C. The secondary IP address is the same as the reth IP address.
- D. The monitored IP address is not on the same subnet as the reth IP address.
Answer: C
NEW QUESTION 17
You have configured source NAT with port address translation. You also need to guarantee that the same IP address is assigned from the source NAT pool to a specific host for multiple concurrent sessions.
Which NAT parameter would meet this requirement?
- A. port block-allocation
- B. port range twin-port
- C. address-persistent
- D. address-pooling paired
Answer: D
NEW QUESTION 18
Click the Exhibit button.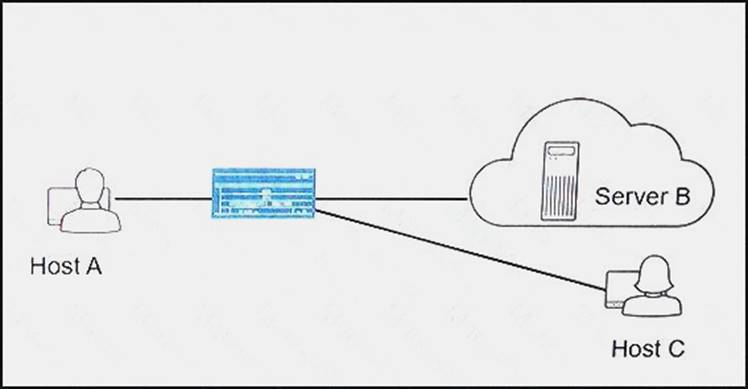
You have configured NAT on your network so that Host A can communicate with Server B. You want to ensure that Host C can initiate communication with Host A using Host A’s reflexive address.
Referring to the exhibit, which parameter should you configure on the SRX Series device to satisfy this requirement?
- A. Configure persistent NAT with the target-host parameter.
- B. Configure persistent NAT with the target-host-port parameter.
- C. Configure persistent NAT with the any-remote-host parameter.
- D. Configure persistent NAT with the port-overloading parameter.
Answer: A
NEW QUESTION 19
What are three characteristics of session-based forwarding, compared to packet-based forwarding, on an SRX Series device? (Choose three.)
- A. Session-based forwarding uses stateful packet processing.
- B. Session-based forwarding requires less memory.
- C. Session-based forwarding performs faster processing of existing session.
- D. Session-based forwarding uses stateless packet processing,
- E. Session-based forwarding uses six tuples of information.
Answer: ACE
NEW QUESTION 20
You want to ensure that any certificates used in your IPsec implementation do not expire while in use by your SRX Series devices.
In this scenario, what must be enabled on your devices?
- A. RSA
- B. TLS
- C. SCEP
- D. CRL
Answer: C
NEW QUESTION 21
You want to protect your SRX Series device from the ping-of-death attack coming from the untrust security zone.
How would you accomplish this task?
- A. Configure the host-inbound-traffic system-services ping except parameter in the untrust security zone.
- B. Configure the application tracking parameter in the untrust security zone.
- C. Configure a from-zone untrust to-zone trust security policy that blocks ICMP traffic.
- D. Configure the appropriate screen and apply it to the [edit security zone security-zone untrust] hierarchy.
Answer: D
NEW QUESTION 22
You are asked to change when your SRX high availability failover occurs. One network interface is considered more important than others in the high availability configuration. You want to prioritize failover based on the state of that interface.
Which configuration would accomplish this task?
- A. Create a VRRP group configuration that lists the reth’s IP address as the VIP while using each physical interface that make up the reth definition of each SRX HA pair.
- B. Configure IP monitoring of the important interface’s IP address and adjust the heartbeat interval and heartbeat threshold to the shortest settings.
- C. Create a separate redundancy group to isolate the important interface; set the priority of the new redundancy group to 255.
- D. Configure interface monitor inside the redundancy group that contains the important physical interface; adjust the weight associated with the monitored interface to 255.
Answer: D
NEW QUESTION 23
Your internal webserver uses port 8088 for inbound connections. You want to allow external HTTP traffic to connect to the webserver.
Which two actions would accomplish this task? (Choose two.)
- A. Create a custom application for port 8088 and create a security policy that permits the custom-http application.
- B. Remap port 80 to port 8088 in the junos-http application and create a security policy that permits the junos-http application.
- C. Use destination NAT to remap incoming traffic from port 80 to port 8088.
- D. Create an Application Layer Gateway to permit HTTP traffic on port 8088.
Answer: AC
NEW QUESTION 24
Which statement is true when destination NAT is performed?
- A. The source IP address is translated according to the configured destination NAT rules and then the security policies are applied.
- B. The destination IP address is translated according to the configured source NAT rules and then the security policies are applied.
- C. The destination IP address is translated according to the configured security policies and then the security destination NAT rules are applied.
- D. The destination IP address is translated according to the configured destination NAT rules and then the security policies are applied.
Answer: D
NEW QUESTION 25
......
P.S. Easily pass jn0-333 Exam with 75 Q&As Surepassexam Dumps & pdf Version, Welcome to Download the Newest Surepassexam jn0-333 Dumps: https://www.surepassexam.com/jn0-333-exam-dumps.html (75 New Questions)