Up To Date SY0-501 Item Pool 2021
Testking offers free demo for SY0-501 exam. "CompTIA Security+ Certification Exam", also known as SY0-501 exam, is a CompTIA Certification. This set of posts, Passing the CompTIA SY0-501 exam, will help you answer those questions. The SY0-501 Questions & Answers covers all the knowledge points of the real exam. 100% real CompTIA SY0-501 exams and revised by experts!
Check SY0-501 free dumps before getting the full version:
NEW QUESTION 1
A company hires a third-party firm to conduct an assessment of vulnerabilities exposed to the Internet. The firm informs the company that an exploit exists for an FTP server that had a version installed from eight years ago. The company has decided to keep the system online anyway, as no upgrade exists form the vendor.
Which of the following BEST describes the reason why the vulnerability exists?
- A. Default configuration
- B. End-of-life system
- C. Weak cipher suite
- D. Zero-day threats
Answer: B
NEW QUESTION 2
Confidential emails from an organization were posted to a website without the organization's knowledge. Upon investigation, it was determined that the emails were obtained from an internal actor who sniffed the emails in plain text. Which of the following protocols, if properly implemented, would have MOST likely prevented the emails from being sniffed? (Select TWO)
- A. Secure IMAP
- B. DNSSEC
- C. S/MIME
- D. SMTPS
- E. HTTPS
Answer: CD
NEW QUESTION 3
During a routine vulnerability assessment, the following command was successful:
echo "vrfy 'perl -e 'print "hi" x 500 ' ' " | nc www.company.com 25 Which of the following vulnerabilities is being exploited?
- A. Buffer overflow directed at a specific host MTA
- B. SQL injection directed at a web server
- C. Cross-site scripting directed at www.company.com
- D. Race condition in a UNIX shell script
Answer: A
NEW QUESTION 4
A new security administrator ran a vulnerability scanner for the first time and caused a system outage. Which of the following types of scans MOST likely caused the outage?
- A. Non-intrusive credentialed scan
- B. Non-intrusive non-credentialed scan
- C. Intrusive credentialed scan
- D. Intrusive non-credentialed scan
Answer: D
NEW QUESTION 5
A security technician has been receiving alerts from several servers that indicate load balancers have had a significant increase in traffic. The technician initiates a system scan. The scan results illustrate that the disk space on several servers has reached capacity. The scan also indicates that incoming internet traffic to the servers has increased. Which of the following is the MOST likely cause of the decreased disk space?
- A. Misconfigured devices
- B. Logs and events anomalies
- C. Authentication issues
- D. Unauthorized software
Answer: D
NEW QUESTION 6
A security analyst is investigating a potential breach. Upon gathering, documenting, and securing the evidence, which of the following actions is the NEXT step to minimize the business impact?
- A. Launch an investigation to identify the attacking host
- B. Initiate the incident response plan
- C. Review lessons learned captured in the process
- D. Remove malware and restore the system to normal operation
Answer: D
NEW QUESTION 7
After a merger between two companies a security analyst has been asked to ensure that the organization's systems are secured against infiltration by any former employees that were terminated during the transition.
Which of the following actions are MOST appropriate to harden applications against infiltration by former employees? (Select TWO)
- A. Monitor VPN client access
- B. Reduce failed login out settings
- C. Develop and implement updated access control policies
- D. Review and address invalid login attempts
- E. Increase password complexity requirements
- F. Assess and eliminate inactive accounts
Answer: CF
NEW QUESTION 8
A security engineer is configuring a wireless network with EAP-TLS. Which of the following activities is a requirement for this configuration?
- A. Setting up a TACACS+ server
- B. Configuring federation between authentication servers
- C. Enabling TOTP
- D. Deploying certificates to endpoint devices
Answer: D
NEW QUESTION 9
AChief Information Officer (CIO) has decided it is not cost effective to implement safeguards against a known vulnerability. Which of the following risk responses does this BEST describe?
- A. Transference
- B. Avoidance
- C. Mitigation
- D. Acceptance
Answer: D
NEW QUESTION 10
A security engineer is configuring a wireless network that must support mutual authentication of the wireless client and the authentication server before users provide credentials. The wireless network must also support authentication with usernames and passwords. Which of the following authentication protocols MUST the security engineer select?
- A. EAP-FAST
- B. EAP-TLS
- C. PEAP
- D. EAP
Answer: C
NEW QUESTION 11
A company has a security policy that specifies all endpoint computing devices should be assigned a unique identifier that can be tracked via an inventory management system. Recent changes to airline security regulations have cause many executives in the company to travel with mini tablet devices instead of laptops.
These tablet devices are difficult to tag and track. An RDP application is used from the tablet to connect into the company network.
Which of the following should be implemented in order to meet the security policy requirements?
- A. Virtual desktop infrastructure (IDI)
- B. WS-security and geo-fencing
- C. A hardware security module (HSM)
- D. RFID tagging system
- E. MDM software
- F. Security Requirements Traceability Matrix (SRTM)
Answer: E
NEW QUESTION 12
The data backup window has expanded into the morning hours and has begun to affect production users. The main bottleneck in the process is the time it takes to replicate the backups to separate severs at the offsite data center. Which of the following uses of deduplication could be implemented to reduce the backup window?
- A. Implement deduplication at the network level between the two locations
- B. Implement deduplication on the storage array to reduce the amount of drive space needed
- C. Implement deduplication on the server storage to reduce the data backed up
- D. Implement deduplication on both the local and remote servers
Answer: B
NEW QUESTION 13
Which of the following use the SSH protocol?
- A. Stelnet
- B. SCP
- C. SNMP
- D. FTPS
- E. SSL
- F. SFTP
Answer: BF
NEW QUESTION 14
A forensic analyst is asked to respond to an ongoing network attack on a server. Place the items in the list below in the correct order in which the forensic analyst should preserve them.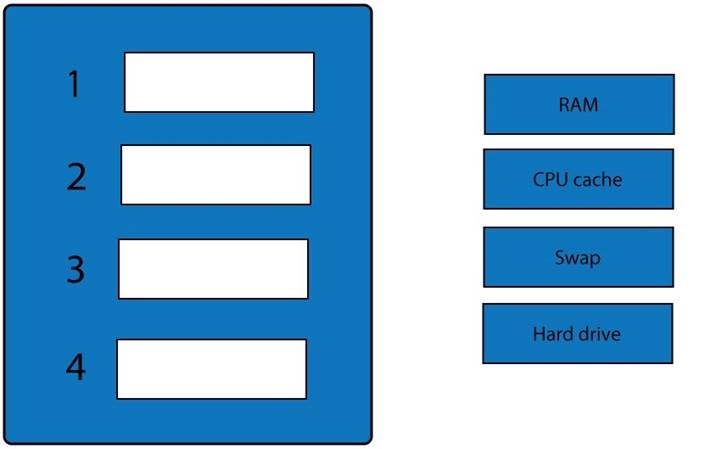
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
When dealing with multiple issues, address them in order of volatility (OOV); always deal with the most volatile first. Volatility can be thought of as the amount of time that you have to collect certain data before a window of opportunity is gone. Naturally, in an investigation you want to collect everything, but some data will exist longer than others, and you cannot possibly collect all of it once. As an example, the OOV in an investigation may be RAM, hard drive data, CDs/DVDs, and printouts.
Order of volatility: Capture system images as a snapshot of what exists, look at network traffic and logs, capture any relevant video/screenshots/hashes, record time offset on the systems, talk to witnesses, and track total man-hours and expenses associated with the investigation.
NEW QUESTION 15
An organization wishes to provide better security for its name resolution services. Which of the following technologies BEST supports the deployment of DNSSEC at the organization?
- A. LDAP
- B. TPM
- C. TLS
- D. SSL
- E. PKI
Answer: E
NEW QUESTION 16
Which of the following is the appropriate network structure used to protect servers and services that must be provided to external clients without completely eliminating access for internal users?
- A. NAC
- B. VLAN
- C. DMZ
- D. Subnet
Answer: C
NEW QUESTION 17
After a recent internal breach, a company decided to regenerate and reissue all certificates used in the transmission of confidential information. The company places the greatest importance on confidentiality and non-repudiation, and decided to generate dual key pairs for each client. Which of the following BEST describes how the company will use these certificates?
- A. One key pair will be used for encryption and decryptio
- B. The other will be used to digitally sign the data.
- C. One key pair will be used for encryptio
- D. The other key pair will provide extended validation.
- E. Data will be encrypted once by each key, doubling the confidentiality and non-repudiation strength.
- F. One key pair will be used for internal communication, and the other will be used for external communication.
Answer: A
NEW QUESTION 18
A network technician is trying to determine the source of an ongoing network based attack. Which of the following should the technician use to view IPv4 packet data on a particular internal network segment?
- A. Proxy
- B. Protocol analyzer
- C. Switch
- D. Firewall
Answer: B
NEW QUESTION 19
A network administrator at a small office wants to simplify the configuration of mobile clients connecting to an encrypted wireless network. Which of the following should be implemented in the administrator does not want to provide the wireless password or he certificate to the employees?
- A. WPS
- B. 802.1x
- C. WPA2-PSK
- D. TKIP
Answer: A
NEW QUESTION 20
An application was recently compromised after some malformed data came in via web form. Which of the following would MOST likely have prevented this?
- A. Input validation
- B. Proxy server
- C. Stress testing
- D. Encoding
Answer: A
NEW QUESTION 21
Which of the following are used to increase the computing time it takes to brute force a password using an offline attack? (Select TWO)
- A. XOR
- B. PBKDF2
- C. bcrypt
- D. HMAC
- E. RIPEMD
Answer: BC
NEW QUESTION 22
A company has three divisions, each with its own networks and services. The company decides to make its secure web portal accessible to all employees utilizing their existing usernames and passwords. The security administrator has elected to use SAML to support authentication. In this scenario, which of the following will occur when users try to authenticate to the portal? (Select two.)
- A. The portal will function as a service provider and request an authentication assertion.
- B. The portal will function as an identity provider and issue an authentication assertion.
- C. The portal will request an authentication ticket from each network that is transitively trusted.
- D. The back-end networks will function as an identity provider and issue an authentication assertion.
- E. The back-end networks will request authentication tickets from the portal, which will act as the third-party service provider authentication store.
- F. The back-end networks will verify the assertion token issued by the portal functioning as the identity provider.
Answer: AB
NEW QUESTION 23
A company wants to implement an access management solution that allows employees to use the same usernames and passwords for multiple applications without having to keep multiple credentials synchronized. Which of the following solutions would BEST meet these requirements?
- A. Multifactor authentication
- B. SSO
- C. Biometrics
- D. PKI
- E. Federation
Answer: B
NEW QUESTION 24
An organization wants to conduct secure transactions of large data files. Before encrypting and exchanging the data files, the organization wants to ensure a secure exchange of keys. Which of the following algorithms is appropriate for securing the key exchange?
- A. DES
- B. Blowfish
- C. DSA
- D. Diffie-Hellman
- E. 3DES
Answer: D
NEW QUESTION 25
Which of the following can be used to control specific commands that can be executed on a network
infrastructure device?
- A. LDAP
- B. Kerberos
- C. SAML
- D. TACACS+
Answer: D
NEW QUESTION 26
A system’s administrator has finished configuring firewall ACL to allow access to a new web server.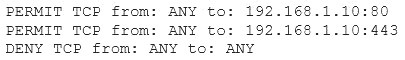
The security administrator confirms form the following packet capture that there is network traffic from the internet to the web server: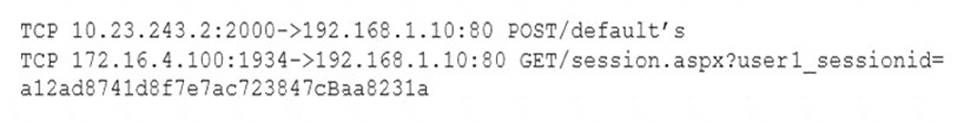
The company’s internal auditor issues a security finding and requests that immediate action be taken. With which of the following is the auditor MOST concerned?
- A. Misconfigured firewall
- B. Clear text credentials
- C. Implicit deny
- D. Default configuration
Answer: B
NEW QUESTION 27
After a routine audit, a company discovers that engineering documents have been leaving the network on a particular port. The company must allow outbound traffic on this port, as it has a legitimate business use. Blocking the port would cause an outage. Which of the following technology controls should the company implement?
- A. NAC
- B. Web proxy
- C. DLP
- D. ACL
Answer: C
NEW QUESTION 28
......
P.S. Easily pass SY0-501 Exam with 544 Q&As Certshared Dumps & pdf Version, Welcome to Download the Newest Certshared SY0-501 Dumps: https://www.certshared.com/exam/SY0-501/ (544 New Questions)