Top Tips Of Far Out SC-300 Brain Dumps
Printable of SC-300 actual exam materials and latest exam for Microsoft certification for customers, Real Success Guaranteed with Updated SC-300 pdf dumps vce Materials. 100% PASS Microsoft Identity and Access Administrator exam Today!
Check SC-300 free dumps before getting the full version:
NEW QUESTION 1
Your company has an Azure Active Directory (Azure AD) tenant named contosri.com. The company has the business partners shown in the following table.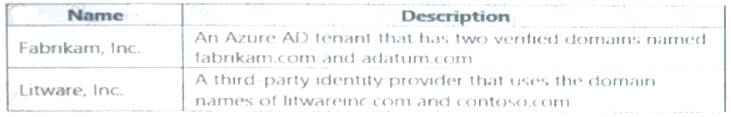
users can request access by using package 1.
Users at Fabrikam and Litware use ail then respective domain names for email addresses.
You plan to create an access package named packaqel that will be accessible only to the Fabrikam and Litware users.
You need to configure connected organizations for Fabrikam and litware so that any of their users can request access by using package1.
What is the minimum of connected organization that you should create.
- A. 1
- B. 2
- C. 3
- D. 4
Answer: C
NEW QUESTION 2
You have an Azure Active Directory (Azure AD) tenant.
You configure self-service password reset (SSPR) by using the following settings:
• Require users to register when signing in: Yes
• Number of methods required to reset: 1
What is a valid authentication method available to users?
- A. home prions
- B. mobile app notification
- C. a mobile app code
- D. an email to an address in your organization
Answer: A
NEW QUESTION 3
You need to meet the authentication requirements for leaked credentials. What should you do?
- A. Enable federation with PingFederate in Azure AD Connect.
- B. Configure Azure AD Password Protection.
- C. Enable password hash synchronization in Azure AD Connect.
- D. Configure an authentication method policy in Azure AD.
Answer: C
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/security/fundamentals/steps-secure-identity
NEW QUESTION 4
You have an Azure Active Directory (Azure AD) tenant that contains three users named User1, User1, and User3,
You create a group named Group1. You add User2 and User3 to Group1.
You configure a role in Azure AD Privileged identity Management (PIM) as shown in the application administrator exhibit. (Click the application Administrator tab.)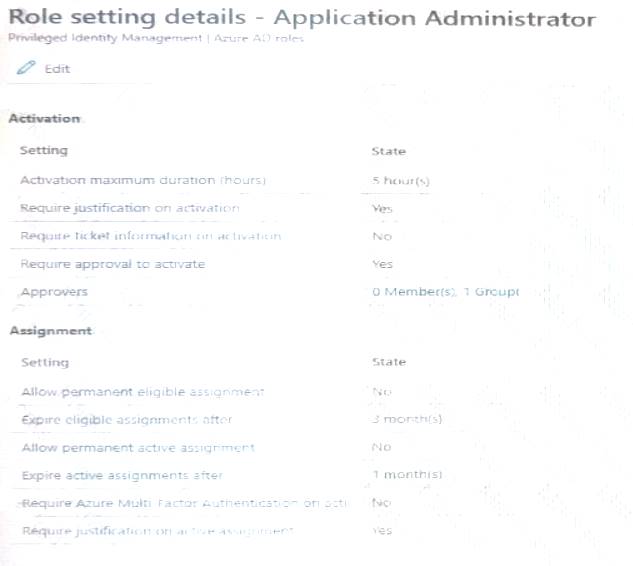
Group1 is configured as the approver for the application administrator role. You configure User2to be eligible for the application administrator role.
For User1, you add an assignment to the Application administrator role as shown in the Assignment exhibit. (Click Assignment tab)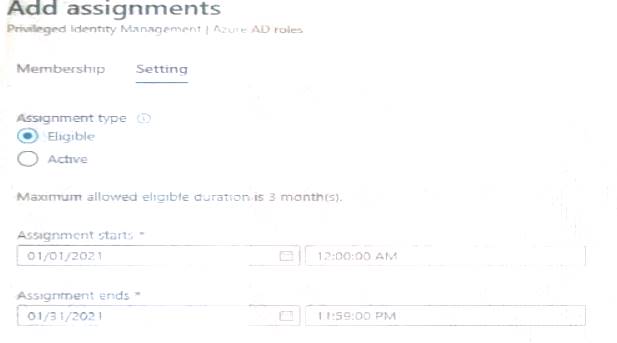
For each of the following statement, select Yes if the statement is true, Otherwise, select No. NOTE: Each correct selection is worth one point.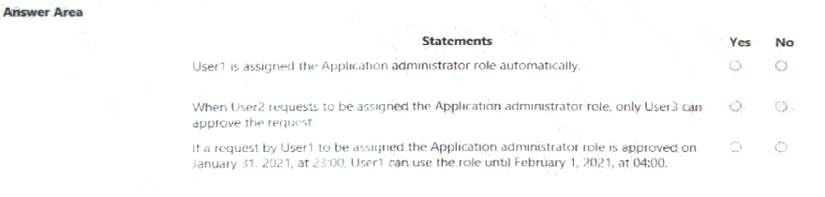
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 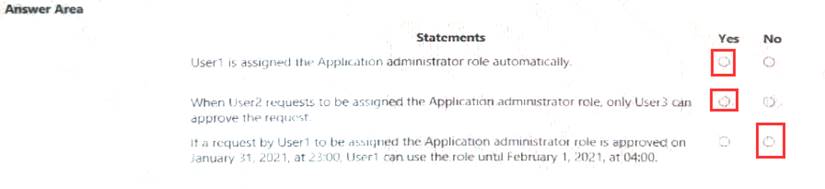
NEW QUESTION 5
Your company has two divisions named Contoso East and Contoso West. The Microsoft 365 identity architecture tor both divisions is shown in the following exhibit.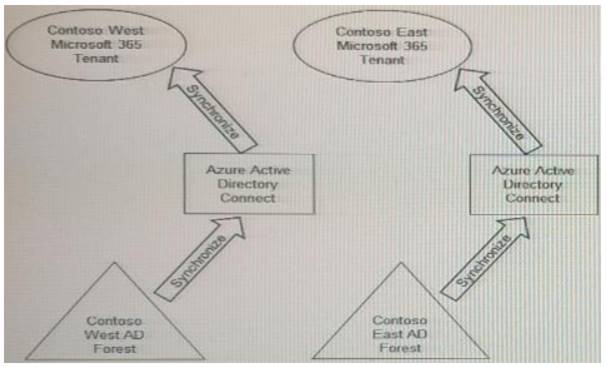
You need to assign users from the Contoso East division access to Microsoft SharePoint Online sites in the Contoso West tenant. The solution must not require additional Microsoft 3G5 licenses.
What should you do?
- A. Configure The exiting Azure AD Connect server in Contoso Cast to sync the Contoso East Active Directory forest to the Contoso West tenant.
- B. Configure Azure AD Application Proxy in the Contoso West tenant.
- C. Deploy a second Azure AD Connect server to Contoso East and configure the server to sync theContoso East Active Directory forest to the Contoso West tenant.
- D. Create guest accounts for all the Contoso East users in the West tenant.
Answer: D
NEW QUESTION 6
You have a Microsoft 365 tenant.
You currently allow email clients that use Basic authentication to conned to Microsoft Exchange Online.
You need to ensure that users can connect t to Exchange only run email clients that use Modern authentication protocols.
What should you implement?
You need to ensure that use Modern authentication
- A. a compliance policy in Microsoft Endpoint Manager
- B. a conditional access policy in Azure Active Directory (Azure AD)
- C. an application control profile in Microsoft Endpoint Manager
- D. an OAuth policy in Microsoft Cloud App Security
Answer: C
NEW QUESTION 7
You have an Azure Active Directory (Azure AD) tenant that uses conditional access policies.
You plan to use third-party security information and event management (SIEM) to analyze conditional access usage.
You need to download the Azure AD log that contains conditional access policy data. What should you export from Azure AD?
- A. sign-ins in JSON format
- B. sign-ins in CSV format
- C. audit logs in JSON format
- D. audit logs in CSV format
Answer: C
NEW QUESTION 8
You have a Microsoft 365 tenant.
You need to identify users who have leaked credentials. The solution must meet the following requirements.
• Identity sign-Ins by users who ate suspected of having leaked credentials.
• Rag the sign-ins as a high risk event.
• Immediately enforce a control to mitigate the risk, while still allowing the user to access applications. What should you use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.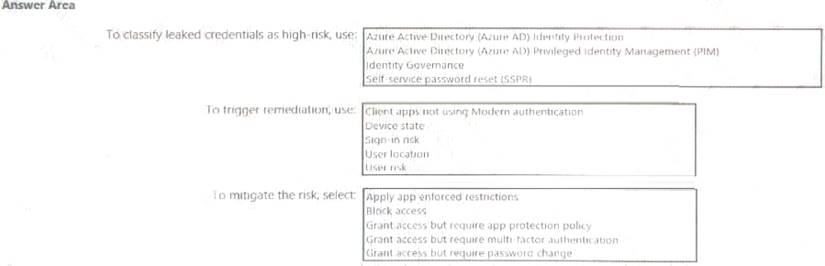
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 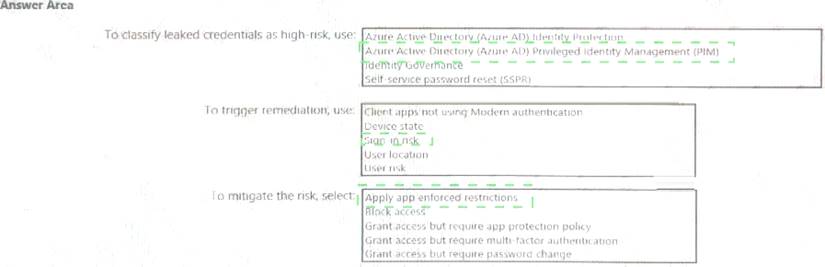
NEW QUESTION 9
You have a Microsoft Exchange organization that uses an SMTP' address space of contoso.com.
Several users use their contoso.com email address for self-service sign up to Azure Active Directory (Azure AD).
You gain global administrator privileges to the Azure AD tenant that contains the self-signed users.
You need to prevent the users from creating user accounts in the contoso.com Azure AD tenant for self-service sign-up to Microsoft 365 services.
Which PowerShell cmdlet should you run?
- A. Set-MsolCompanySettings
- B. Set-MsolDomainFederationSettings
- C. Update-MsolfederatedDomain
- D. Set-MsolDomain
Answer: A
Explanation:
https://docs.microsoft.com/en-us/azure/active-directory/enterprise-users/directory-self-service-signup
NEW QUESTION 10
You need to identify which roles to use for managing role assignments. The solution must meet the delegation requirements.
What should you do? To answer, select the appropriate options in the answer area. NOTE:Each correct selection is worth one point.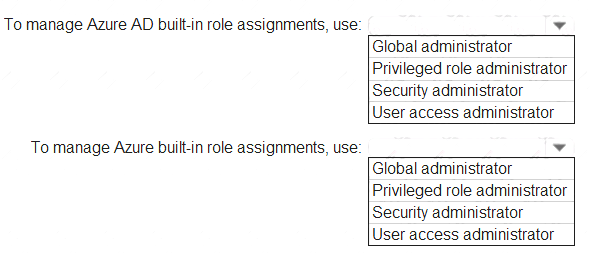
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/role-based-access-control/role-assignments-portal https://docs.microsoft.com/en-us/azure/active-directory/roles/permissions-reference
NEW QUESTION 11
Your company recently implemented Azure Active Directory (Azure AD) Privileged Identity Management (PIM).
While you review the roles in PIM, you discover that all 15 users in the IT department at the company have permanent security administrator rights.
You need to ensure that the IT department users only have access to the Security administrator role when required.
What should you configure for the Security administrator role assignment?
- A. Expire eligible assignments afterfrom the Role settings details
- B. Expire active assignments afterfrom the Role settings details
- C. Assignment type toActive
- D. Assignment type toEligible
Answer: D
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/privileged-identity-management/pim-configure
NEW QUESTION 12
You use Azure Monitor to analyze Azure Active Directory (Azure AD) activity logs.
Yon receive more than 100 email alerts each day for tailed Azure Al) user sign-in attempts. You need to ensure that a new security administrator receives the alerts instead of you. Solution: From Azure AD, you create an assignment for the Insights at administrator role. Does this meet the goal?
- A. Yes
- B. No
Answer: B
NEW QUESTION 13
You use Azure Monitor to analyze Azure Active Directory (Azure AD) activity logs.
Yon receive more than 100 email alerts each day for tailed Azure Al) user sign-in attempts. You need to ensure that a new security administrator receives the alerts instead of you. Solution: From Azure monitor, you create a data collection rule.
Does this meet the goal?
- A. Yes
- B. No
Answer: A
NEW QUESTION 14
You need to configure the MFA settings for users who connect from the Boston office. The solution must
meet the authentication requirements and the access requirements. What should you configure?
- A. named locations that have a private IP address range
- B. named locations that have a public IP address range
- C. trusted IPs that have a public IP address range
- D. trusted IPs that have a private IP address range
Answer: B
NEW QUESTION 15
You have a Microsoft 36S tenant.
You create a named location named HighRiskCountries that contains a list of high-risk countries.
You need to limit the amount of time a user can stay authenticated when connecting from a high-risk country. What should you configure in a conditional access policy? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.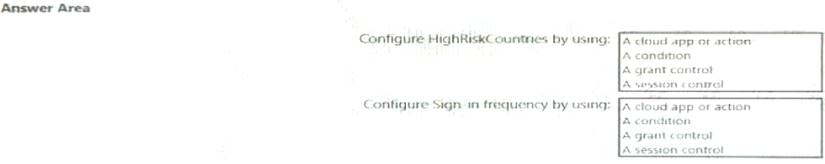
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 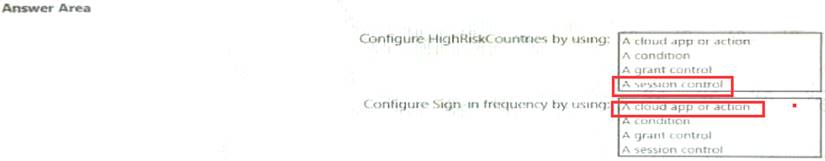
NEW QUESTION 16
You have a Microsoft 365 tenant that contains a group named Group! as shown in the Group1 exhibit. (Click the Group 1 tab.)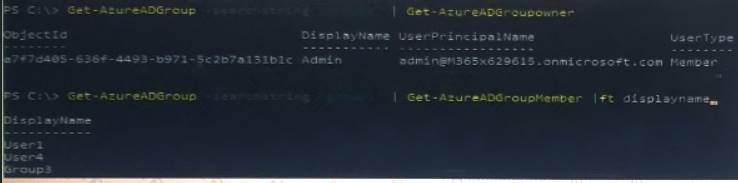
You create an enterprise application named App1 as shown in the App1 Properties exhibit. (Click the App1 Properties tab.)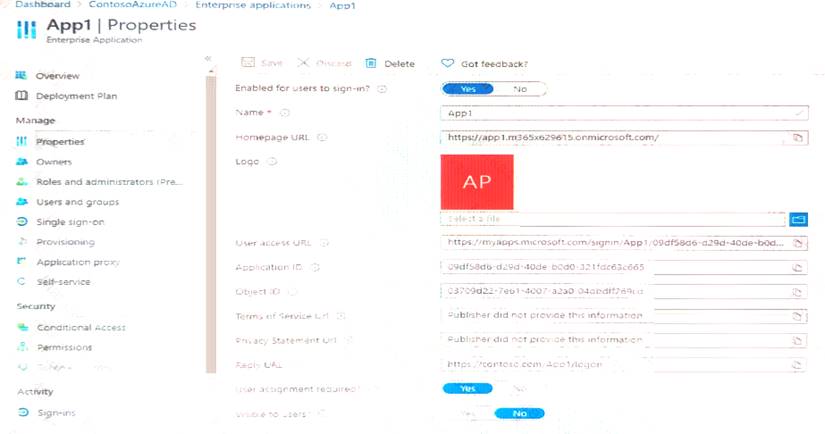
You configure self-service for App1 as shown in the App1 Self-service exhibit: (Click the App1 Self-service tab.)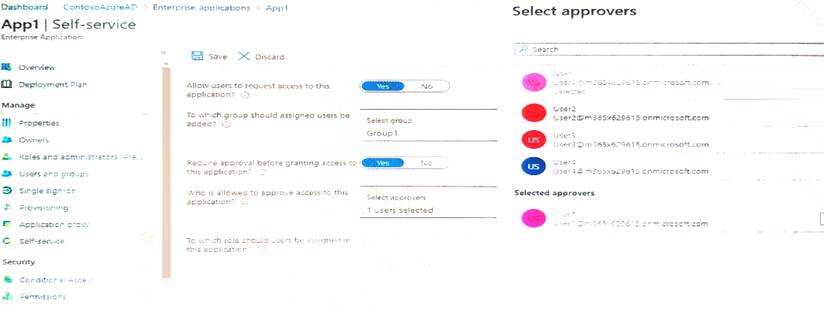
For each of the following statements, select Yes if the statement is true, Otherwise select NO. NOTE: Each correct selection is worth one point.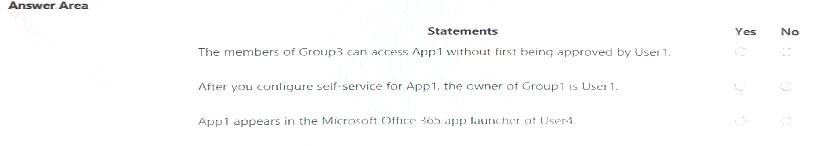
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 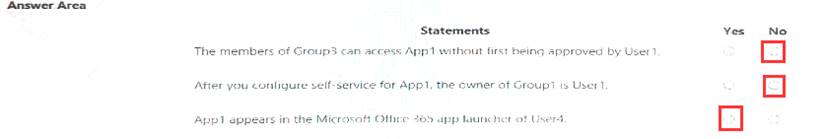
NEW QUESTION 17
You have 2,500 users who are assigned Microsoft Office 365 Enterprise E3 licenses. The licenses are assigned to individual users.
From the Groups blade in the Azure Active Directory admin center, you assign Microsoft 365 Enterprise E5 licenses to the users.
You need to remove the Office 365 Enterprise E3 licenses from the users by using the least amount of administrative effort.
What should you use?
- A. the Identity Governance blade in the Azure Active Directory admin center
- B. theSet-AzureAdUsercmdlet
- C. the Licenses blade in the Azure Active Directory admin center
- D. theSet-WindowsProductKeycmdlet
Answer: C
NEW QUESTION 18
You configure a new Microsoft 365 tenant to use a default domain name of contoso.com.
You need to ensure that you can control access to Microsoft 365 resources by using conditional access policies.
What should you do first?
- A. Disable the User consent settings.
- B. Disable Security defaults.
- C. Configure a multi-factor authentication (MFA) registration policy.
- D. Configure password protection for Windows Server Active Directory.
Answer: B
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/fundamentals/concept-fundamentals-security-defaults
NEW QUESTION 19
You have a Microsoft 365 tenant.
Sometimes, users use external, third-party applications that require limited access to the Microsoft 365 data of the respective user. The users register the applications in Azure Active Directory (Azure AD).
You need to receive an alert if a registered application gains read and write access to the users’ email. What should you do? To answer, select the appropriate options in the answer area.
NOTE:Each correct selection is worth one point.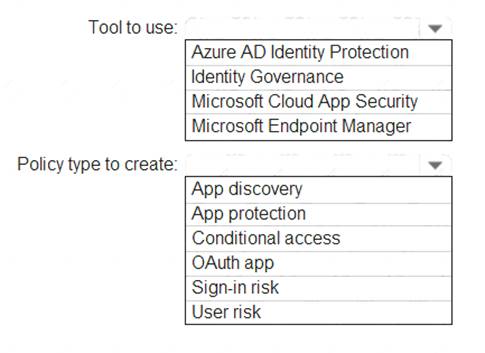
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Reference:
https://docs.microsoft.com/en-us/cloud-app-security/app-permission-policy
NEW QUESTION 20
You have a Microsoft 365 tenant.
The Sign-ins activity report shows that an external contractor signed in to the Exchange admin center. You need to review access to the Exchange admin center at the end of each month and block sign-ins if required.
What should you create?
- A. an access package that targets users outside your directory
- B. an access package that targets users in your directory
- C. a group-based access review that targets guest users
- D. an application-based access review that targets guest users
Answer: C
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/governance/access-reviews-overview
NEW QUESTION 21
You have an Azure Active Directory (Azure AD) tenant that contains the users shown in the following table.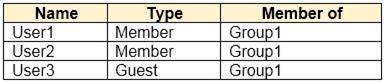
User1 is the owner of Group1.
You create an access review that has the following settings:  Users to review: Members of a group
Users to review: Members of a group Scope: Everyone
Scope: Everyone  Group: Group1
Group: Group1 Reviewers: Members (self)
Reviewers: Members (self)
Which users can perform access reviews for User3?
- A. User1, User2, and User3
- B. User3 only
- C. User1 only
- D. User1 and User2 only
Answer: B
NEW QUESTION 22
You have an Azure Active Directory (Azure AD) tenant.
You need to review the Azure AD sign-ins log to investigate sign ins that occurred in the past. For how long does Azure AD store events in the sign-in log?
- A. 14 days
- B. 30 days
- C. 90 days
- D. 365 days
Answer: B
NEW QUESTION 23
......
Recommend!! Get the Full SC-300 dumps in VCE and PDF From Certshared, Welcome to Download: https://www.certshared.com/exam/SC-300/ (New 52 Q&As Version)