Top Tips Of Abreast Of The Times NSE8 Dumps Questions
Download of NSE8 free exam materials and study guides for Fortinet certification for client, Real Success Guaranteed with Updated NSE8 pdf dumps vce Materials. 100% PASS NSE8 exam Today!
Free demo questions for Fortinet NSE8 Exam Dumps Below:
NEW QUESTION 1
A customer wants to implement a RADIUS Single Sign On (RSSO) solution for multiple FortiGate devices. The customer’s network already includes a RADIUS server that can generate the logon and logoff accounting records. However, the RADIUS server can send those records to only one destination.
What should the customer do to overcome this limitation?
- A. Send the RADIUS records to an LDAP server and add the LDAP server to the FortiGate configuration.
- B. Send the RADIUS records to an RSSO Collector Agent.
- C. Send the RADIUS records to one of the FortiGate devices, which can replicate them to the other FortiGate units.
- D. Use the RADIUS accounting proxy feature available in FortiAuthenticator devices.
Answer: B
Explanation:
References:
http://docs.fortinet.com/uploaded/files/1937/fortigate-authentication-52.pdf
NEW QUESTION 2
You have implemented FortiGate in transparent mode as shown in the exhibit. User1 from the Internet is trying to access the 192.168.10.10 Web servers.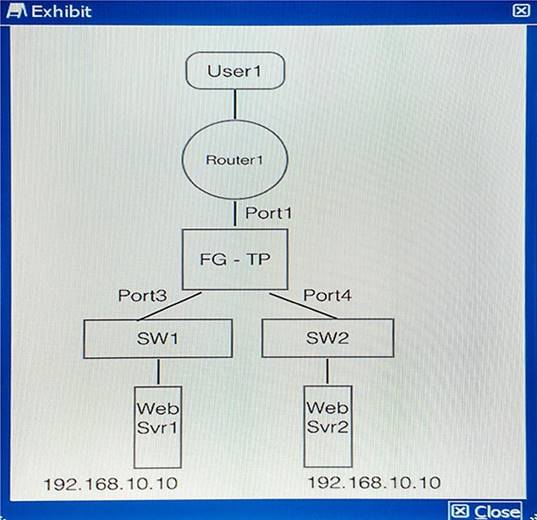
Which two statements about this scenario are true? (Choose two.)
- A. User1 would be able to access the Web server intermittently.
- B. User1 would not be able to access any of the Web servers at all.
- C. FortiGate learns Web servers MAC address when the Web servers transmit packets.
- D. FortiGate always flood packets to both Web servers at the same time.
Answer: AC
Explanation:
Both servers have same ip address, so there will be intermittent we server connectivity from outside and whichever web server forwards packets fortigate learns its mac address.
NEW QUESTION 3
Your marketing department uncompressed and executed a file that the whole department received using Skype.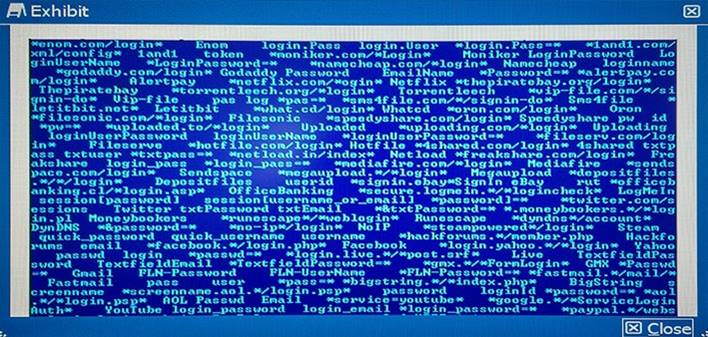
Reviewing the exhibit, which two details do you determine from your initial analysis of the payload?
- A. The payload contains strings that the malware is monitoring to harvest credentials.
- B. This is a type of Trojan that will download and pirate movies using your Netflix credentials.
- C. This type of threat of a DDoS attack using instant messaging to send e-mails to further spread the infection.
- D. This threat payload is uploading private user videos which are then used to extort Bitcoin payments.
Answer: B
NEW QUESTION 4
You have received an issue report about users not being able to use a video conferencing application. This application uses two UDP ports and two TCP ports to communicate with servers on the Internet. The network engineering team has confirmed there is no routing problem. You are given a copy of the FortiGate configuration.
Which three configuration objects will you inspect to ensure that no policy is blocking this traffic? (Choose three.)
- A. config firewall interface-policy
- B. config firewall DoS-policy
- C. config firewall policy
- D. config firewall multicast-policy
- E. config firewall sniffer-policy
Answer: BCE
NEW QUESTION 5
You are asked to write a FortiAnalyzer report that lists the session that has consumed the most bandwidth. You are required to include the source IP, destination IP, application, application category, hostname, and total bandwidth consumed.
Which dataset meets these requirements?
- A. select from_itime(itime) as timestamp, srcip, dstip, app, appcat, hostname, sum(coalesce(‘sentbyte”, 0) +coalesce(‘recbyte “, 0)) as bandwidth from $log where $filter LIMIT 1
- B. select from_itime(itime) as timestamp, srcip, dstip, app, appcat, hostname, sum(coalesce(‘sentbyte”, 0) +coalesce(‘recbyte“, 0)) as bandwidth from $log where $filter LIMIT 1
- C. select from_itime(itime) as timestamp, srcip, dstip, app, appcat, hostname, sum(coalesce(‘sentbyte”, 0) +coalesce(‘rcvdbyte“, 0)) as bandwidth from $log where $filter LIMIT 1
- D. select from_itime(itime) as timestamp, sourceip, destip, app, appcat, hostname, sum(coalesce(‘sentbyte’, 0)+coalesce(‘rcvdbyte“, 0)) as bandwidth from $log where $filter LIMIT 1
Answer: C
Explanation:
References:
http://docs.fortinet.com/uploaded/files/2617/fortianalyzer-5.2.4-dataset-reference.pdf
NEW QUESTION 6
Which Fortinet product is used for antispam protection?
- A. FortiSwitch
- B. FortiGate
- C. FortiWeb
- D. FortiDB
Answer: B
NEW QUESTION 7
Your FortiGate has multiple CPUs. You want to verify the load for each CPU. Which two commands will accomplish this task? (Choose two.)
- A. get system performance status
- B. diag system mpstat
- C. diag system cpu stat
- D. diag system top
Answer: AD
Explanation:
References: http://kb.fortinet.com/kb/documentLink.do?externalID=13825
NEW QUESTION 8
A customer wants to secure the network shown in the exhibit with a full redundancy design. Which security design would you use?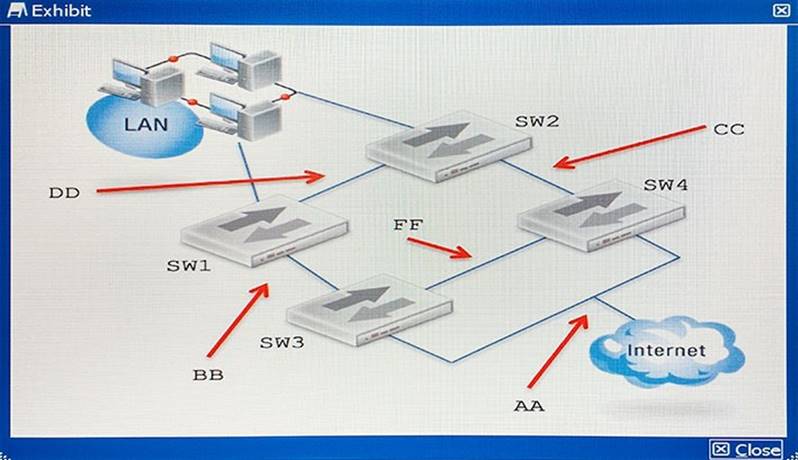
- A. Place a FortiGate FGCP Cluster between DD and AA, then connect it to SW1, SW2, SW3, and SW4.
- B. Place a FortiGate FGCP Cluster between BB and CC, then connect it to SW1, SW2, SW3, and SW4.
- C. Place a FortiGate FGCP Cluster between BB and AA, then connect it to SW1, SW2, SW3, and SW4.
- D. Place a FortiGate FGCP Cluster between DD and FF, then connect it to SW1, SW2, SW3, and SW4.
Answer: A
NEW QUESTION 9
An administrator wants to assign static IP addresses to users connecting tunnel-mode SSL VPN. Each SSL VPN user must always get the same unique IP address which is never assigned to any other user.
Which solution accomplishes this task?
- A. TACACS+ authentication with an attribute-value (AV) pair containing each user’s IP address.
- B. RADIUS authentication with each user’s IP address stored in a Vendor Specific Attribute (VSA).
- C. LDAP authentication with an LDAP attribute containing each user’s IP address.
- D. FSSO authentication with an LDAP attribute containing each user’s IP address.
Answer: D
NEW QUESTION 10
You want to enable traffic between 2001:db8:1::/64 and 2001:db8:2::/64 over the public IPv4 Internet.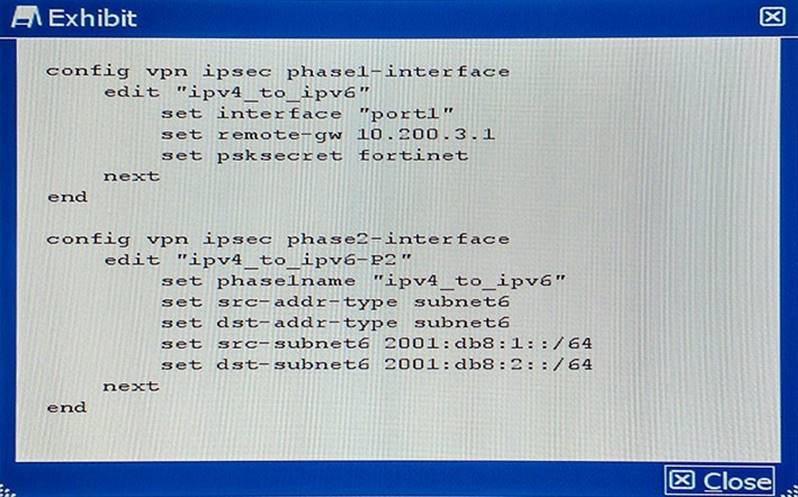
Given the CLI configuration shown in the exhibit, which two additional settings are required on this device to implement tunneling for the IPv6 transition? (Choose two.)
- A. IPv4 firewall policies to allow traffic between the local and remote IPv6 subnets.
- B. IPv6 static route to the destination phase2 destination subnet.
- C. IPv4 static route to the destination phase2 destination subnet.
- D. IPv6 firewall policies to allow traffic between the local and remote IPv6 subnets.
Answer: BD
Explanation:
References: http://docs.fortinet.com/uploaded/files/1969/IPv6%20Handbook%20for%20FortiOS%205.2. pdf
NEW QUESTION 11
The FortiGate is used as an IPsec gateway at a branch office. Two tunnels, tunA and tunB, are established between this FortiGate and the headquarters’ IPsec gateway. The branch office’s subnet is 10.1.1.0/24. The headquarters’ subnet is 10.2.2.0/24. The desired usage for tunA and tunB has been defined as follows:
- sessions initiated from 10.1.1.0/24 to 10.2.2.0/24 must be routed out over tunA when tunA is up
- sessions initiated from 10.1.1.0/24 to 10.2.2.0/24 have to be routed out over tunB when tunA is down
- sessions initiated from 10.2.2.0/24 can ingress either on tunA or on tunB Which static routing configuration meets the requirements?
- A.
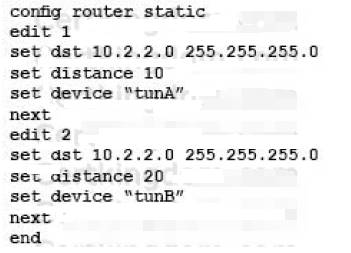
- B.
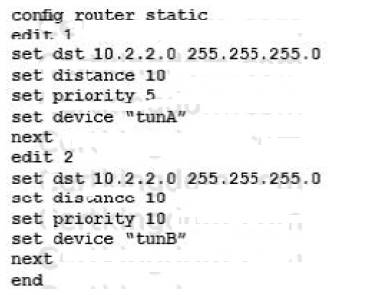
- C.
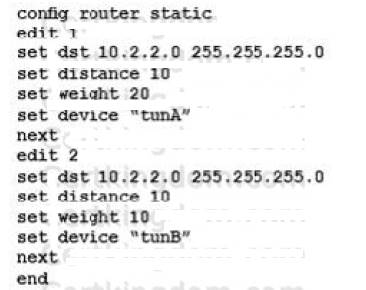
- D.
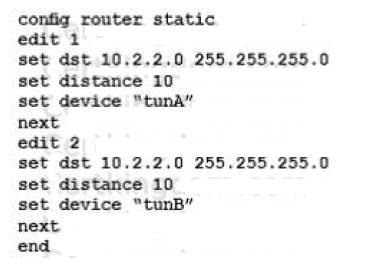
Answer: C
NEW QUESTION 12
You are asked to establish a VPN tunnel with a service provider using a third-party VPN device. The service provider has assigned subnet 30.30.30.0/24 for your outgoing traffic going towards the services hosted by the provider on network 20.20.20.0/24. You have multiple computers which will be accessing the remote services hosted by the service provider.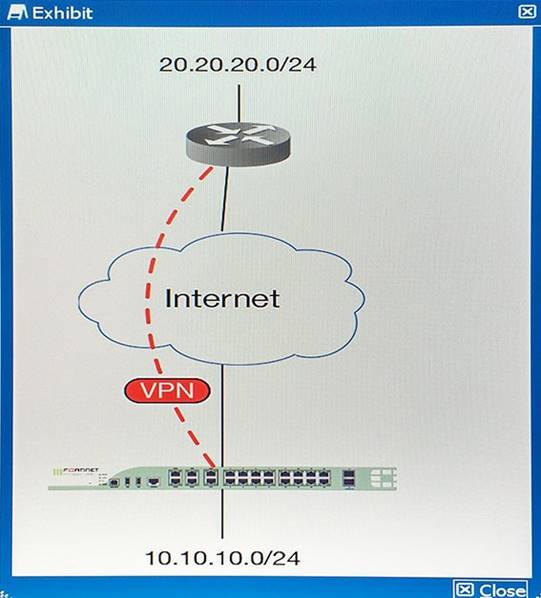
Which three configuration components meet these requirements? (Choose three.)
- A. Configure an IP Pool of type Overload for range 30.30.30.10-30.30.30.10. Enable NAT on a policy from your LAN forwards the VPN tunnel and select that pool.
- B. Configure IPsec phase 2 proxy IDs for a source of 10.10.10.0/24 and destination of 20.20.20.0/24.
- C. Configure an IP Pool of Type One-to-One for range 30.30.30.10-30.30.30.10. Enable NAT on a policy from your LAN towards the VPN tunnel and select that pool.
- D. Configure a static route towards the VPN tunnel for 20.20.20.0/24.
- E. Configure IPsec phase 2 proxy IDs for a source of 30.30.30.0/24 and destination of 20.20.20.0/24.
Answer: CDE
NEW QUESTION 13
How would you apply security to the network shown in the exhibit?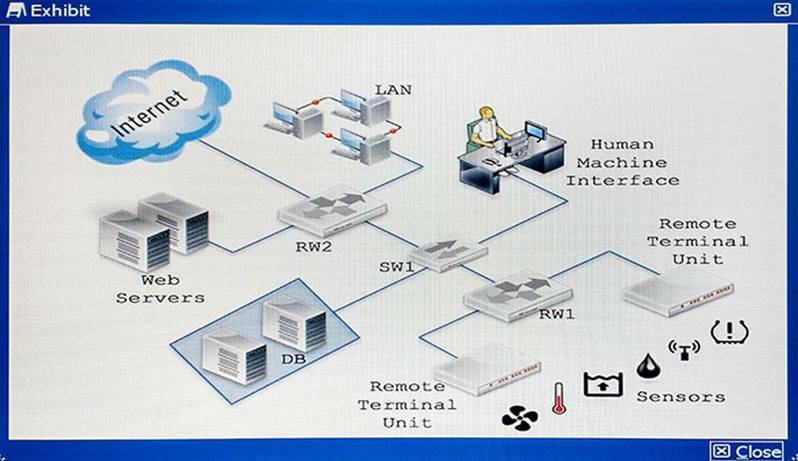
- A. Replace RW1 with a ruggedized FortiGate and RW2 with a normal FortiGat
- B. Enable industrial category on the application contro
- C. Place a FortiGate to secure Web server
- D. Configure IPsec to secure sensors dat
- E. Place a ruggedized FortiAP to provide Wi-Fi to the sensors.
- F. Replace RW1 with a normal FortiGate and RW2 with a ruggedized FortiGat
- G. Enable industrial category on the application contro
- H. Place a FortiGate to secure Web server
- I. Configure IPsec to secure sensors dat
- J. Place a FortiAP to provide Wi-Fi to the sensors.
- K. Replace RW1 with a normal FortiGate and RW2 with a ruggedized FortiGat
- L. Enable industrial category on the Web filte
- M. Place a FortiWeb to secure Web server
- N. Configure IPsec to secure sensors dat
- O. Place a ruggedized FortiAP to provide Wi-Fi to the sensors.
- P. Replace RW1 with a normal FortiGate and RW2 with a ruggedized FortiGat
- Q. Enable industrial category on the application contro
- R. Place a FortiWeb to secure Web server
- S. Configure IPsec to secure sensors dat
- T. Place a ruggedized FortiAP to provide Wi-Fi to the sensors.
Answer: D
NEW QUESTION 14
Your colleague has enabled virtual clustering to load balance traffic between the cluster units. You notice that all traffic is currently directed to a single FortiGate unit. Your colleague has applied the configuration shown in the exhibit.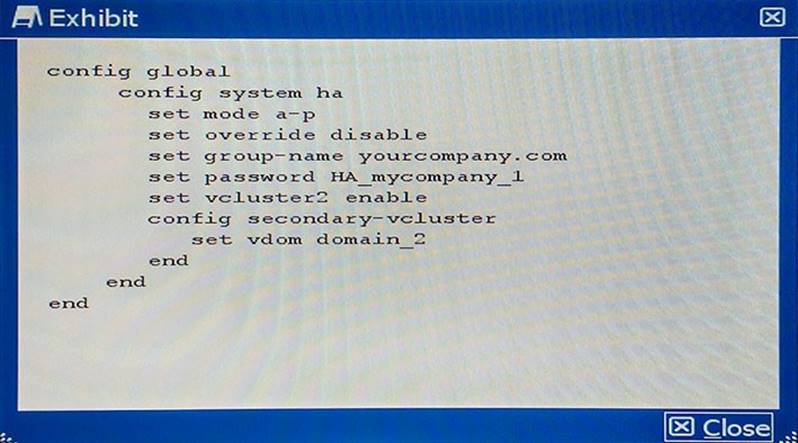
Which step would you perform to load balance traffic within the virtual cluster?
- A. Issue the diagnose sys ha reset-uptime command on the unit that is currently processing traffic to enable load balancing.
- B. Add an additional virtual cluster high-availability link to enable cluster load balancing.
- C. Input Virtual Cluster domain 1 and Virtual Cluster domain 2 device priorities for each cluster unit.
- D. Use the set override enable command on both units to allow the secondary unit to load balance traffic.
Answer: C
Explanation:
References:
NEW QUESTION 15
You have replaced an explicit proxy Web filter with a FortiGate. The human resources department requires that all URLs be logged. Users are reporting that their browsers are now indicating certificate errors as shown in the exhibit.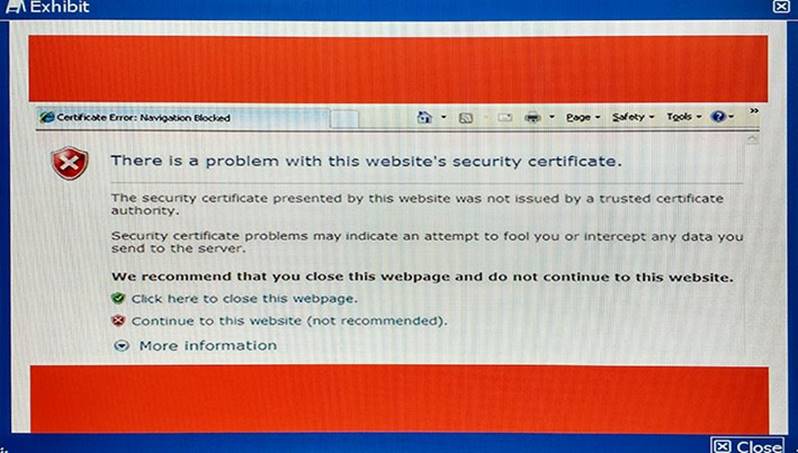
Which step is a valid solution to the problem?
- A. Make sure that the affected users’ browsers are no longer set to use the explicit proxy.
- B. Import the FortiGate’s SSL CA certificate into the Web browsers.
- C. Change the Web filter policies on the FortiGate to only do certificate inspection.
- D. Make a Group Policy to install the FortiGate’s SSL certificate as a trusted host certificate on the Web browser.
Answer: D
Explanation:
For https traffic inspection, client machine should install fortigate’s ssl certificate
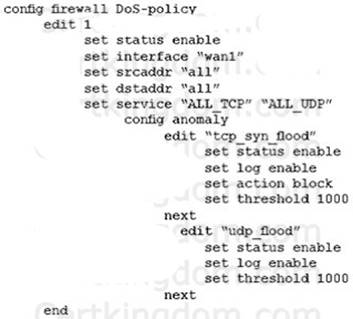
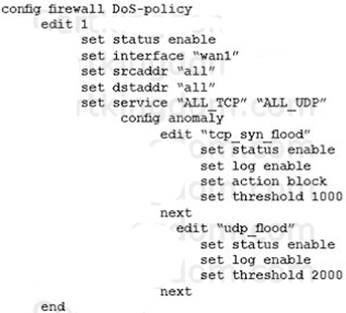
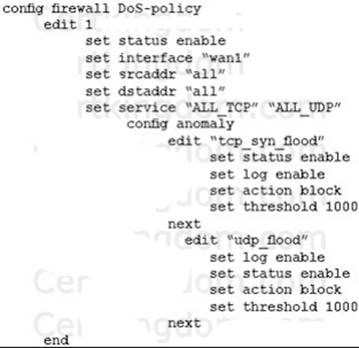
NEW QUESTION 16
A company wants to protect against Denial of Service attacks and has launched a new project. They want to block the attacks that go above a certain threshold and for some others they are just trying to get a baseline of activity for those types of attacks so they are
letting the traffic pass through without action. Given the following:
- The interface to the Internet is on WAN1.
- There is no requirement to specify which addresses are being protected or protected from.
- The protection is to extend to all services.
- The tcp_syn_flood attacks are to be recorded and blocked.
- The udp_flood attacks are to be recorded but not blocked.
- The tcp_syn_flood attack’s threshold is to be changed from the default to 1000. The exhibit shows the current DoS-policy.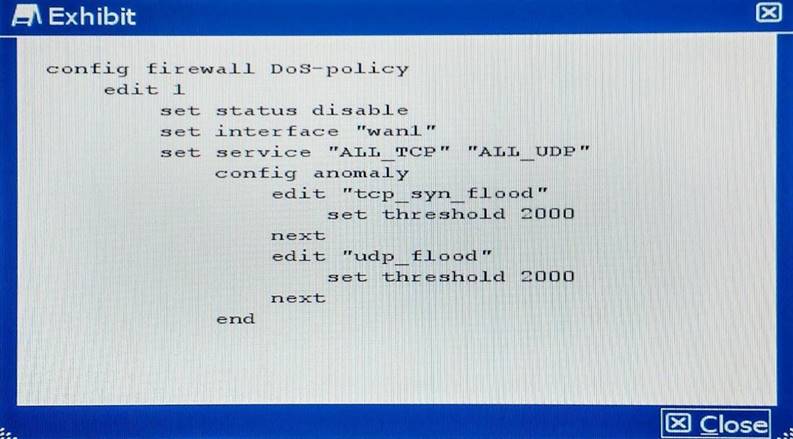
Which policy will implement the project requirements?
- A.
- B.
- C.
- D.
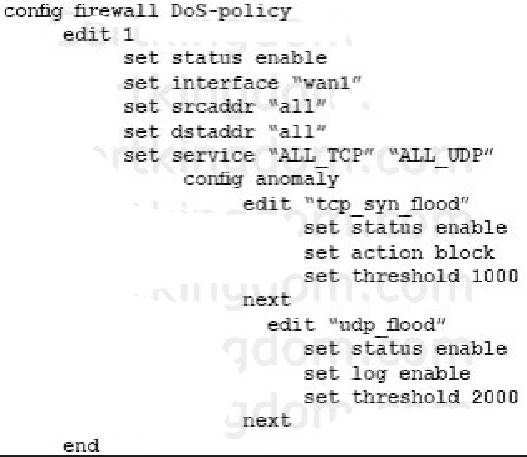
Answer: BD
Explanation:
B&D both have same policy which fulfills the above criteria. http://help.fortinet.com/fos50hlp/52data/Content/FortiOS/fortigate-firewall-52/Examples/Example-%20DoS%20Policy.htm
NEW QUESTION 17
Referring to the diagram shown in the exhibit, you deployed VRRP load balancing using two FortiGate units and two VRRP groups with a VRRP virtual MAC address enabled on both FortiGate’s port2 interface. During normal operation, both FortiGate units are processing traffic and the VRRP groups are used to load balance the traffic between the two FortiGate units.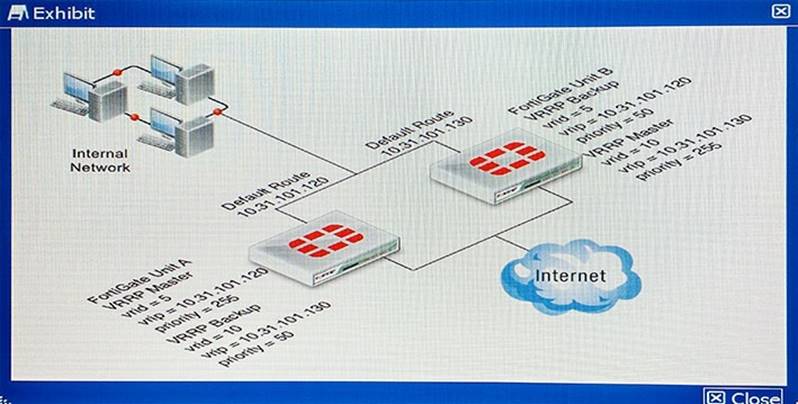
If FortiGate unit A fails, what would happen?
- A. The FortiGate Unit B port2 interface sends gratuitous ARPs to associate the VRRPvirtual router IP address with its own MAC address, and all traffic fails over to it.
- B. The FortiGate Unit B port2 interface will use virtual MAC addresses of 00-00-5e-00-01- 05 and 00-00-5e-00-01-0a, and all traffic fails over to it.
- C. The FortiGate Unit B port2 interface will use virtual MAC addresses of 00-a0-5e-00-01- 05 and 00-a0-5e-00-01-0a, and all traffic fails over to it.
- D. The FortiGate Unit B port2 interface will use the physical MAC addresses of the FortiGate Unit A port2 interface, and all traffic fails over to it.
Answer: B
Explanation:
If primary fails secondary device uses virtual mac address to forward traffic
NEW QUESTION 18
The dashboard widget indicates that FortiGuard Web Filtering is not reachable. However, AntiVirus, IPS, and Application Control have no problems as shown in the exhibit.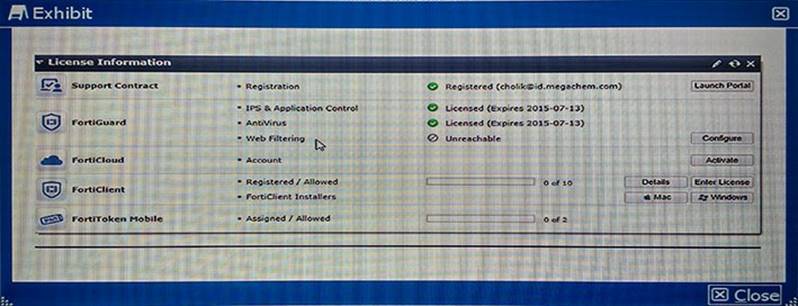
You contacted Fortinet’s customer service and discovered that your FortiGuard Web Filtering contract is still valid for several months.
What are two reasons for this problem? (Choose two.)
- A. You have another security device in front of FortiGate blocking ports 8888 and 53.
- B. FortiGuard Web Filtering is not enabled in any firewall policy.
- C. You did not enable Web Filtering cache under Web Filtering and E-mail Filtering Options.
- D. You have a firewall policy blocking ports 8888 and 53.
Answer: BD
Explanation:
If Web filtering shows unreachable then we have to verify, whether web filtering enabled in security policies or not.
Web filtering enabled in a policy but the port 8888 and 53 are not selected, means the policy blocking the ports.
References:
NEW QUESTION 19
The FortiGate is an IPsec VPN hub. A VPN spoke protecting subnet 192.168.222.0/24 has successfully brought up a tunnel with the FortiGate. This remote network is present in the FortiGate routing table as shown in the exhibit.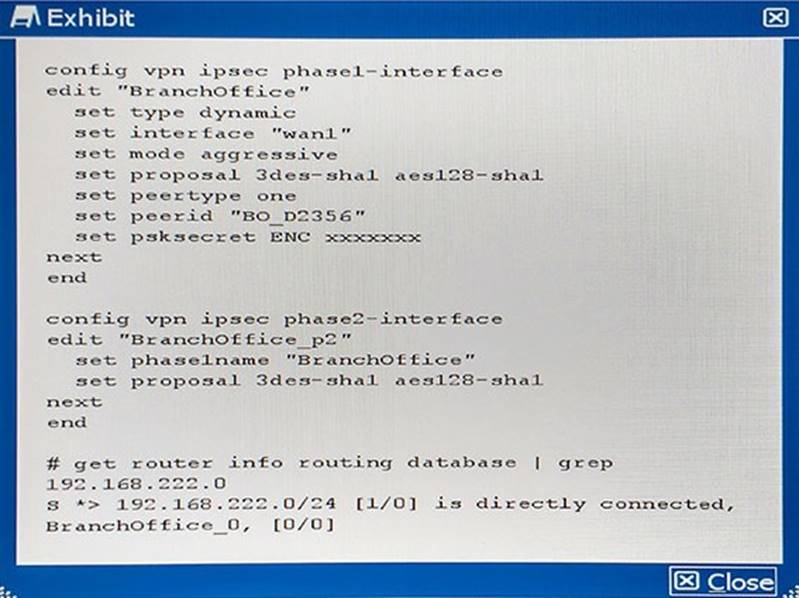
Which statement is true?
- A. This subnet was learned during quick-mode negotiation and was dynamically injected into the routing table.
- B. The FortiGate administrator configured this subnet as a locally connected subnet on the “BranchOffice” phase1 interface.
- C. The route in the exhibit is bound to “BranchOffice_0” which is a tunnel other than “BranchOffice”.
- D. The FortiGate administrator configured a static route for 192.168.222.0/24.
Answer: B
NEW QUESTION 20
A customer wants to install a FortiSandbox device to identify suspicious files received by an e-mail server. All the incoming e-mail traffic to the e-mail server uses the SMTPS protocol.
Which three solutions would be implemented? (Choose three.)
- A. FortiGate device in transparent mode sending the suspicious files to the FortiSandbox
- B. FortiSandbox in sniffer input mode
- C. FortiMail device in gateway mode using the built-in MTA and sending the suspicious files to the FortiSandbox
- D. FortiMail device in transparent mode acting as an SMTP proxy sending the suspicious files to the FortiSandbox
- E. FortiGate device in NAT mode sending the suspicious files to the FortiSandbox
Answer: BCE
Explanation:
References: http://kb.fortinet.com/kb/documentLink.do?externalID=FD34371
NEW QUESTION 21
Your NOC contracts the security team due to a problem with a new application flow. You are instructed to disable hardware acceleration for the policy shown in the exhibit for troubleshooting purposes.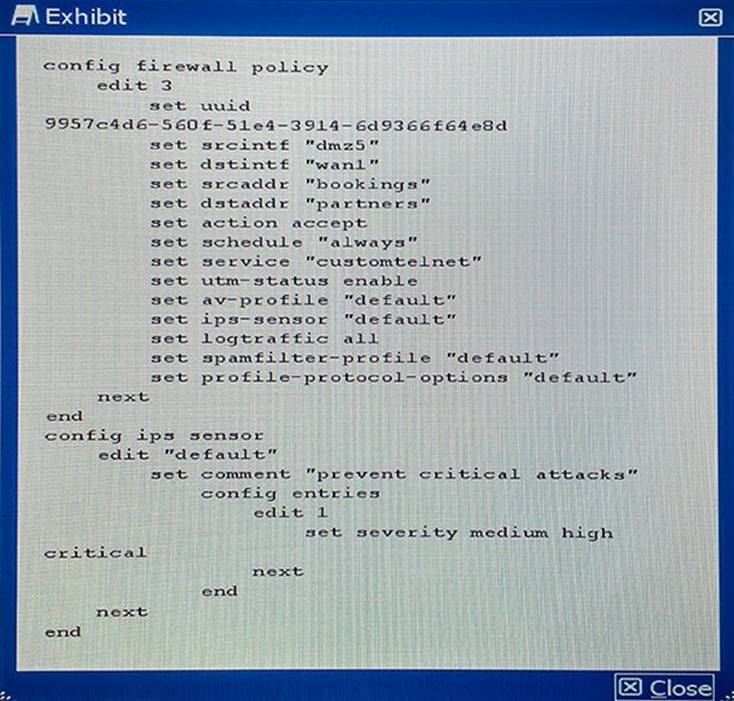
Which command will disable hardware acceleration for the new application policy?
- A.
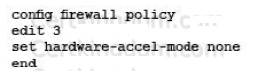
- B.
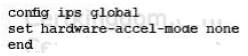
- C.
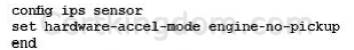
- D.
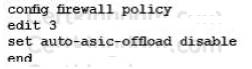
Answer: D
Explanation:
References:
http://docs.fortinet.com/uploaded/files/1607/fortigate-hardware-accel-50.pdf
NEW QUESTION 22
Which command syntax would you use to configure the serial number of a FortiGate as its host name?
- A.
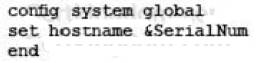
- B.
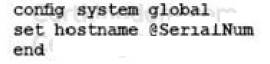
- C.
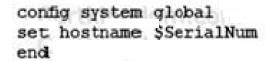
- D.
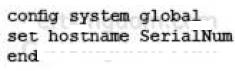
Answer: AB
Explanation:
References:
http://defadhil.blogspot.in/2014/04/how-to- protect-fortigate- from.html
NEW QUESTION 23
......
P.S. Certshared now are offering 100% pass ensure NSE8 dumps! All NSE8 exam questions have been updated with correct answers: https://www.certshared.com/exam/NSE8/ (65 New Questions)