Best Quality NSE4_FGT-6.2 Interactive Bootcamp 2021
Certleader NSE4_FGT-6.2 Questions are updated and all NSE4_FGT-6.2 answers are verified by experts. Once you have completely prepared with our NSE4_FGT-6.2 exam prep kits you will be ready for the real NSE4_FGT-6.2 exam without a problem. We have Rebirth Fortinet NSE4_FGT-6.2 dumps study guide. PASSED NSE4_FGT-6.2 First attempt! Here What I Did.
Online Fortinet NSE4_FGT-6.2 free dumps demo Below:
NEW QUESTION 1
Examine this FortiGate configuration: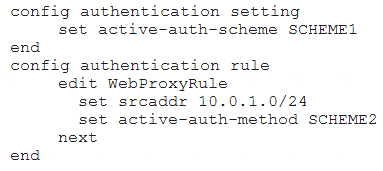
How does the FortiGate handle web proxy traffic coming from the IP address 10.2.1.200 that requires authorization?
- A. It always authorizes the traffic without requiring authentication.
- B. It drops the traffic.
- C. It authenticates the traffic using the authentication scheme SCHEME2.
- D. It authenticates the traffic using the authentication scheme SCHEME1.
Answer: D
Explanation:
“What happens to traffic that requires authorization, but does not match any authentication rule? The active and passive SSO schemes to use for those cases is defined under config authentication setting”
NEW QUESTION 2
View the exhibit.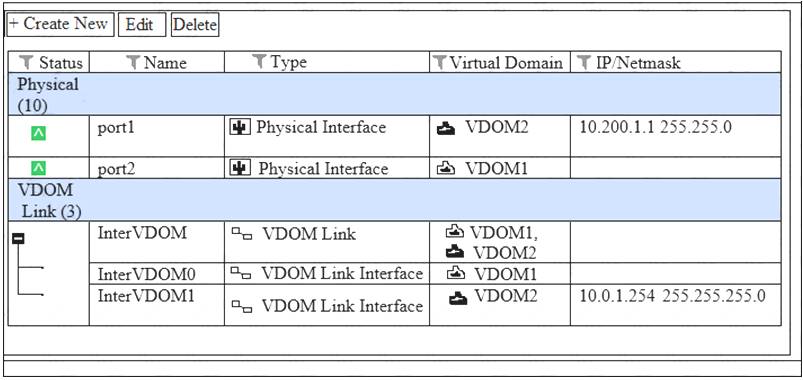
VDOM1 is operating in transparent mode VDOM2 is operating in NAT Route mode. There is an inteface VDOM link between both VDOMs. A client workstation with the IP address 10.0.1.10/24 is connected to port2. A web server with the IP address 10.200.1.2/24 is connected to port1.
What is required in the FortiGate configuration to route and allow connections from the client workstation to the web server? (Choose two.)
- A. A static or dynamic route in VDOM2 with the subnet 10.0.1.0/24 as the destination.
- B. A static or dynamic route in VDOM1 with the subnet 10.200.1.0/24 as the destination.
- C. One firewall policy in VDOM1 with port2 as the source interface and InterVDOM0 as the destination interface.
- D. One firewall policy in VDOM2 with InterVDOM1 as the source interface and port1 as the destination interface.
Answer: C
NEW QUESTION 3
An administrator is attempting to allow access to https://fortinet.com through a firewall policy that is configured with a web filter and an SSL inspection profile configured for deep inspection. Which of the following are possible actions to eliminate the certificate error generated by deep inspection? (Choose two.)
- A. Implement firewall authentication for all users that need access to fortinet.com.
- B. Manually install the FortiGate deep inspection certificate as a trusted CA.
- C. Configure fortinet.com access to bypass the IPS engine.
- D. Configure an SSL-inspection exemption for fortinet.com.
Answer: AD
NEW QUESTION 4
Which of the following services can be inspected by the DLP profile? (Choose three.)
- A. NFS
- B. FTP
- C. IMAP
- D. CIFS
- E. HTTP-POST
Answer: BCE
NEW QUESTION 5
Which statements about HA for FortiGate devices are true? (Choose two.)
- A. Sessions handled by proxy-based security profiles cannot be synchronized.
- B. Virtual clustering can be configured between two FortiGate devices that have multiple VDOMs.
- C. HA management interface settings are synchronized between cluster members.
- D. Heartbeat interfaces are not required on the primary device.
Answer: AB
NEW QUESTION 6
Examine this FortiGate configuration: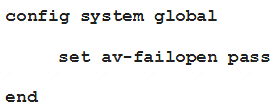
Examine the output of the following debug command: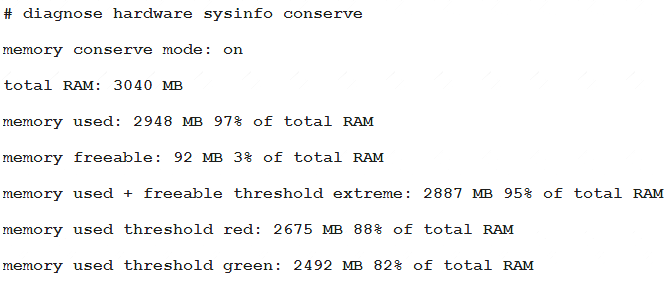
Based on the diagnostic outputs above, how is the FortiGate handling the traffic for new sessions that require inspection?
- A. It is allowed, but with no inspection
- B. It is allowed and inspected as long as the inspection is flow based
- C. It is dropped.
- D. It is allowed and inspected, as long as the only inspection required is antivirus.
Answer: A
NEW QUESTION 7
Which of the following statements describe WMI polling mode for the FSSO collector agent? (Choose two.)
- A. The NetSessionEnum function is used to track user logoffs.
- B. WMI polling can increase bandwidth usage in large networks.
- C. The collector agent uses a Windows API to query DCs for user logins.
- D. The collector agent do not need to search any security event logs.
Answer: CD
NEW QUESTION 8
Which of the following are purposes of NAT traversal in IPsec? (Choose two.)
- A. To delete intermediary NAT devices in the tunnel path.
- B. To dynamically change phase 1 negotiation mode aggressive mode.
- C. To encapsulation ESP packets in UDP packets using port 4500.
- D. To force a new DH exchange with each phase 2 rekey.
Answer: AC
NEW QUESTION 9
An administrator has configured central DNAT and virtual IPs. Which of the following can be selected in the firewall policy Destination field?
- A. A VIP group
- B. The mapped IP address object of the VIP object
- C. A VIP object
- D. An IP pool
Answer: B
NEW QUESTION 10
View the exhibit.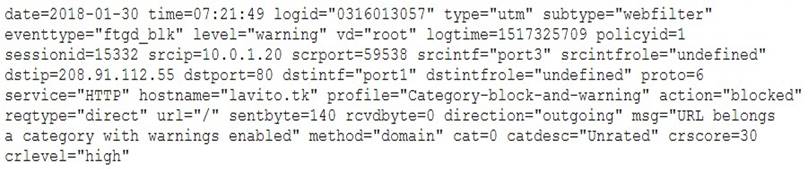
What does this raw log indicate? (Choose two.)
- A. FortiGate blocked the traffic.
- B. type indicates that a security event was recorded.
- C. 10.0.1.20 is the IP address for lavito.tk.
- D. policyid indicates that traffic went through the IPS firewall policy.
Answer: AB
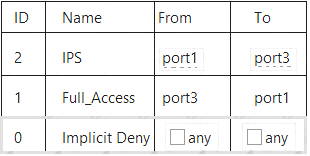
NEW QUESTION 11
Which of the following statements about central NAT are true? (Choose two.)
- A. IP tool references must be removed from existing firewall policies before enabling central NAT.
- B. Central NAT can be enabled or disabled from the CLI only.
- C. Source NAT, using central NAT, requires at least one central SNAT policy.
- D. Destination NAT, using central NAT, requires a VIP object as the destination address in a firewall.
Answer: AB
NEW QUESTION 12
Which of the following statements about backing up logs from the CLI and downloading logs from the GUI are true? (Choose two.)
- A. Log downloads from the GUI are limited to the current filter view
- B. Log backups from the CLI cannot be restored to another FortiGate.
- C. Log backups from the CLI can be configured to upload to FTP as a scheduled time
- D. Log downloads from the GUI are stored as LZ4 compressed files.
Answer: BC
NEW QUESTION 13
How do you format the FortiGate flash disk?
- A. Load a debug FortiOS image.
- B. Load the hardware test (HQIP) image.
- C. Execute the CLI command execute formatlogdisk.
- D. Select the format boot device option from the BIOS menu.
Answer: D
NEW QUESTION 14
An administration wants to throttle the total volume of SMTP sessions to their email server. Which of the following DoS sensors can be used to achieve this?
- A. tcp_port_scan
- B. ip_dst_session
- C. udp_flood
- D. ip_src_session
Answer: A
Explanation:
https://help.fortinet.com/fos50hlp/52data/Content/FortiOS/fortigate-firewall-52/Security%20Policies/DoS%20Pr
NEW QUESTION 15
How does FortiGate select the central SNAT policy that is applied to a TCP session?
- A. It selects the SNAT policy specified in the configuration of the outgoing interface.
- B. It selects the first matching central SNAT policy, reviewing from top to bottom.
- C. It selects the central SNAT policy with the lowest priority.
- D. It selects the SNAT policy specified in the configuration of the firewall policy that matches the traffic.
Answer: A
NEW QUESTION 16
Which statement is true regarding the policy ID number of a firewall policy?
- A. Defines the order in which rules are processed.
- B. Represents the number of objects used in the firewall policy.
- C. Required to modify a firewall policy using the CLI.
- D. Changes when firewall policies are reordered.
Answer: C
NEW QUESTION 17
Which statement about the IP authentication header (AH) used by IPsec is true?
- A. AH does not provide any data integrity or encryption.
- B. AH does not support perfect forward secrecy.
- C. AH provides data integrity bur no encryption.
- D. AH provides strong data integrity but weak encryption.
Answer: C
NEW QUESTION 18
A team manager has decided that while some members of the team need access to particular website, the majority of the team does not. Which configuration option is the most effective option to support this request?
- A. Implement a web filter category override for the specified website.
- B. Implement web filter authentication for the specified website
- C. Implement web filter quotas for the specified website.
- D. Implement DNS filter for the specified website.
Answer: A
NEW QUESTION 19
Why must you use aggressive mode when a local FortiGate IPSec gateway hosts multiple dialup tunnels?
- A. In aggressive mode, the remote peers are able to provide their peer IDs in the first message.
- B. FortiGate is able to handle NATed connections only in aggressive mode.
- C. FortiClient only supports aggressive mode.
- D. Main mode does not support XAuth for user authentication.
Answer: A
NEW QUESTION 20
Examine this PAC file configuration.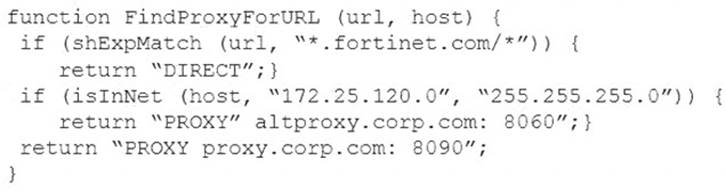
Which of the following statements are true? (Choose two.)
- A. Browsers can be configured to retrieve this PAC file from the FortiGate.
- B. Any web request to the 172.25.120.0/24 subnet is allowed to bypass the proxy.
- C. All requests not made to Fortinet.com or the 172.25.120.0/24 subnet, have to go through altproxy.corp.com: 8060.
- D. Any web request fortinet.com is allowed to bypass the proxy.
Answer: AD
NEW QUESTION 21
Which action can be applied to each filter in the application control profile?
- A. Block, monitor, warning, and quarantine
- B. Allow, monitor, block and learn
- C. Allow, block, authenticate, and warning
- D. Allow, monitor, block, and quarantine
Answer: D
NEW QUESTION 22
Which of the following conditions are required for establishing an IPSec VPN between two FortiGate devices? (Choose two.)
- A. If XAuth is enabled as a server in one peer, it must be enabled as a client in the other peer.
- B. If the VPN is configured as route-based, there must be at least one firewall policy with the action set toIPSec.
- C. If the VPN is configured as DialUp User in one peer, it must be configured as either Static IP Address or Dynamic DNS in the other peer.
- D. If the VPN is configured as a policy-based in one peer, it must also be configured as policy-based in the other peer.
Answer: AC
NEW QUESTION 23
Examine the following web filtering log.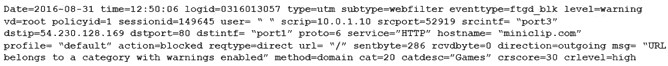
Which statement about the log message is true?
- A. The action for the category Games is set to block.
- B. The usage quota for the IP address 10.0.1.10 has expired
- C. The name of the applied web filter profile is default.
- D. The web site miniclip.com matches a static URL filter whose action is set to Warning.
Answer: C
NEW QUESTION 24
In a high availability (HA) cluster operating in active-active mode, which of the following correctly describes the path taken by the SYN packet of an HTTP session that is offloaded to a secondary FortiGate?
- A. Client > primary FortiGate> secondary FortiGate> primary FortiGate> web server.
- B. Client > secondary FortiGate> web server.
- C. Clinet >secondary FortiGate> primary FortiGate> web server.
- D. Client> primary FortiGate> secondary FortiGate> web server.
Answer: D
NEW QUESTION 25
Which of the following conditions must be met in order for a web browser to trust a web server certificate signed by a third-party CA?
- A. The public key of the web server certificate must be installed on the browser.
- B. The web-server certificate must be installed on the browser.
- C. The CA certificate that signed the web-server certificate must be installed on the browser.
- D. The private key of the CA certificate that signed the browser certificate must be installed on the browser.
Answer: C
NEW QUESTION 26
......
P.S. prep-labs.com now are offering 100% pass ensure NSE4_FGT-6.2 dumps! All NSE4_FGT-6.2 exam questions have been updated with correct answers: https://www.prep-labs.com/dumps/NSE4_FGT-6.2/ (129 New Questions)