Top Tips Of Most Recent JN0-230 Dumps Questions
We provide real JN0-230 exam questions and answers braindumps in two formats. Download PDF & Practice Tests. Pass Juniper JN0-230 Exam quickly & easily. The JN0-230 PDF type is available for reading and printing. You can print more and practice many times. With the help of our Juniper JN0-230 dumps pdf and vce product and material, you can easily pass the JN0-230 exam.
Free JN0-230 Demo Online For Juniper Certifitcation:
NEW QUESTION 1
You are configuring an IPsec VPN tunnel between two location on your network. Each packet must be encrypted and authenticated.
Which protocol would satisfy these requirements?
- A. MD5
- B. ESP
- C. AH
- D. SHA
Answer: B
NEW QUESTION 2
What should you configure if you want to translate private source IP address to a single public IP address?
- A. Source NAT
- B. Destination NAT
- C. Content filtering
- D. Security Director
Answer: A
NEW QUESTION 3
What are the valid actions for a source NAT rule in J-Web? (choose three.)
- A. On
- B. Off
- C. Pool
- D. Source
- E. interface
Answer: BCE
Explanation:
Explanation
https://www.juniper.net/documentation/en_US/junos/topics/topic-map/nat-security-source-and-source-pool.html
NEW QUESTION 4
You want to generate reports from the l-Web on an SRX Series device. Which logging mode would you use in this scenario?
- A. Syslog
- B. Stream
- C. Event
- D. local
Answer: B
NEW QUESTION 5
Which two statements are correct about using global-based policies over zone-based policies? (Choose two.)
- A. With global-based policies, you do not need to specify a destination zone in the match criteria.
- B. With global-based policies, you do not need to specify a source zone in the match criteria.
- C. With global-based policies, you do not need to specify a destination address in the match criteria.
- D. With global-based policies, you do not need to specify a source address in the match criteria.
Answer: AB
NEW QUESTION 6
On an SRX Series device, how should you configure your IKE gateway if the remote endpoint is a branch office-using a dynamic IP address?
- A. Configure the IPsec policy to use MDS authentication.
- B. Configure the IKE policy to use aggressive mode.
- C. Configure the IPsec policy to use aggressive mode.
- D. Configure the IKE policy to use a static IP address
Answer: B
NEW QUESTION 7
Which type of security policy protect restricted services from running on non-standard ports?
- A. Application firewall
- B. IDP
- C. Sky ATP
- D. antivirus
Answer: B
NEW QUESTION 8
Exhibit.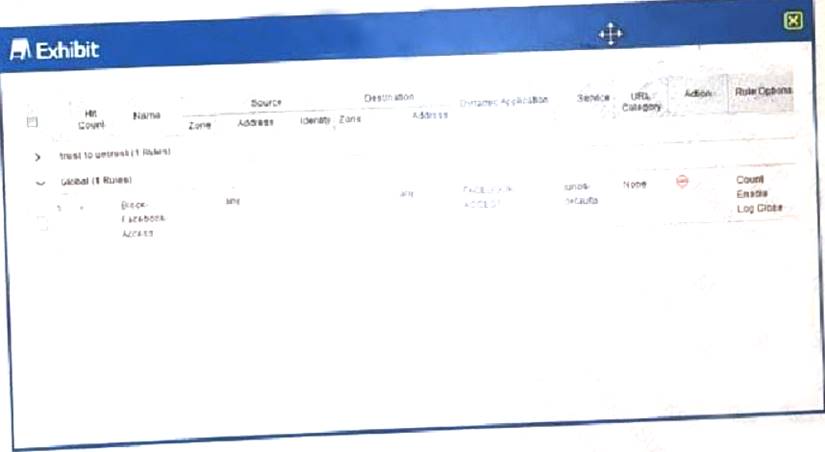
Which two statements are true? (Choose two.)
- A. Logs for this security policy are generated.
- B. Logs for this security policy are not generated.
- C. Traffic static for this security policy are not generated.
- D. Traffic statistics for this security policy are generated.
Answer: AD
NEW QUESTION 9
Which two actions are performed on an incoming packet matching an existing session? (Choose two.)
- A. Zone processing
- B. Security policy evolution
- C. Service ALG processing
- D. Screens processing
Answer: CD
NEW QUESTION 10
What are configuring the antispam UTM feature on an SRX Series device.
Which two actions would be performed by the SRX Series device for e-mail that is identified as spam? (Choose two.)
- A. Tag the e-mail
- B. Queue the e-mail
- C. Block the e-mail
- D. Quarantine e-mail
Answer: AC
NEW QUESTION 11
The Sky ATP premium or basic-Threat Feed license is needed fort which two features? (Choose two.)
- A. Outbound protection
- B. C&C feeds
- C. Executable inspection
- D. Custom feeds
Answer: BD
NEW QUESTION 12
Which statements is correct about SKY ATP?
- A. Sky ATP is an open-source security solution.
- B. Sky ATP is used to automatically push out changes to the AppSecure suite.
- C. Sky ATP only support sending threat feeds to vSRX Series devices
- D. Sky ATP is a cloud-based security threat analyzer that performs multiple tasks
Answer: D
NEW QUESTION 13
Which security object defines a source or destination IP address that is used for an employee Workstation?
- A. Zone
- B. Screen
- C. Address book entry
- D. scheduler
Answer: C
NEW QUESTION 14
Which method do VPNs use to prevent outside parties from viewing packet in clear text?
- A. Integrity
- B. Authentication
- C. Encryption
- D. NAT_T
Answer: C
NEW QUESTION 15
Which statements is correct about Junos security zones?
- A. User-defined security must contain at least one interface.
- B. Security policies are referenced within a user-defined security zone.
- C. Logical interface are added to user defined security zones
- D. User-defined security must contains the key word ‘’zone’’
Answer: C
NEW QUESTION 16
Which statement about IPsec is correct?
- A. IPsec can be used to transport native Layer 2 packets.
- B. IPsec can provide encapsulation but not encryption
- C. IPsec is a standards-based protocol.
- D. IPsec is used to provide data replication
Answer: C
NEW QUESTION 17
Which statement is correct about IKE?
- A. IKE phase 1 is used to establish the data path
- B. IKE phase 1 only support aggressive mode.
- C. IKE phase 1 negotiates a secure channel between gateways.
- D. IKE phase 1 establishes the tunnel between devices
Answer: C
NEW QUESTION 18
Which two statements are correct about functional zones? (Choose two.)
- A. A functional zone uses security policies to enforce rules for transit traffic.
- B. Traffic received on the management interface in the functional zone cannot transit out other interface.
- C. Functional zones separate groups of users based on their function.
- D. A function is used for special purpose, such as management interface
Answer: BD
NEW QUESTION 19
You are concerned that unauthorized traffic is using non-standardized ports on your network.
In this scenario, which type of security feature should you implement?
- A. Application firewall
- B. Sky ATP
- C. Firewall filters
- D. Zone-based policies
Answer: A
NEW QUESTION 20
Which two feature on the SRX Series device are common across all Junos devices? (Choose two.)
- A. Stateless firewall filters
- B. UTM services
- C. The separation of control and forwarding planes
- D. screens
Answer: AC
NEW QUESTION 21
Which statements is correct about global security policies?
- A. Global policies allow you to regulate traffic with addresses and applications, regardless of their security zones.
- B. Traffic matching global is not added to the session table.
- C. Global policies eliminate the need to assign interface to security zones.
- D. Global security require you to identify a source and destination zone.
Answer: A
NEW QUESTION 22
Referring to the exhibit.
****Exhibit is Missing****
Which type of NAT is performed by the SRX Series device?
- A. Source NAT with PAT
- B. Source Nat without PAT
- C. Destination NAT without PAT
- D. Destination NAT with PAT
Answer: D
NEW QUESTION 23
What must you do first to use the Monitor/Alarms/Policy Log workspace in J-Web?
- A. You must enable logging that uses the SD-Syslog format.
- B. You must enable security logging that uses the TLS transport mode.
- C. You must enable stream mode security logging on the SRX Series device.
- D. You must enable event mode security logging on the SRX Series device.
Answer: D
NEW QUESTION 24
Which two statements are true about security policy actions? (Choose two.)
- A. The reject action drops the traffic and sends a message to the source device.
- B. The deny action silently drop the traffic.
- C. The deny action drops the traffic and sends a message to the source device.
- D. The reject action silently drops the traffic.
Answer: AB
NEW QUESTION 25
What are two characteristic of static NAT SRX Series devices? (Choose two.)
- A. Source and destination NAT rules take precedence over static NAT rules.
- B. A reverse mapping rule is automatically created for the source translation.
- C. Static NAT rule take precedence over source and destination NAT rules.
- D. Static rules cannot coexist with destination NAT rules on the same SRX Series device configuration.
Answer: BC
NEW QUESTION 26
......
100% Valid and Newest Version JN0-230 Questions & Answers shared by Certifytools, Get Full Dumps HERE: https://www.certifytools.com/JN0-230-exam.html (New 65 Q&As)