A Review Of Download ECSAv10 Training
Exam Code: ECSAv10 (Practice Exam Latest Test Questions VCE PDF)
Exam Name: EC-Council Certified Security Analyst (ECSA) v10 : Penetration Testing
Certification Provider: EC-Council
Free Today! Guaranteed Training- Pass ECSAv10 Exam.
Free ECSAv10 Demo Online For EC-Council Certifitcation:
NEW QUESTION 1
Mason is footprinting an organization to gather competitive intelligence. He visits the company's website for contact information and telephone numbers but does not find any. He knows the entire staff directory was listed on their website 12 months. How can he find the directory?
- A. Visit Google’s search engine and view the cached copy
- B. Crawl and download the entire website using the Surfoffline tool and save them to his computer
- C. Visit the company's partners’ and customers' website for this information
- D. Use Way Back Machine in Archive.org web site to retrieve the Internet archive
Answer: D
NEW QUESTION 2
Identify the type of testing that is carried out without giving any information to the employees or administrative head of the organization.
- A. Unannounced Testing
- B. Double Blind Testing
- C. Announced Testing
- D. Blind Testing
Answer: B
NEW QUESTION 3
John, a penetration tester from a pen test firm, was asked to collect information about the host file in a Windows system directory. Which of the following is the location of the host file in Window system directory?
- A. C:WindowsSystem32Boot
- B. C:WINNTsystem32driversetc
- C. C:WINDOWSsystem32cmd.exe
- D. C:WindowsSystem32restore
Answer: B
NEW QUESTION 4
You just passed your ECSA exam and are about to start your first consulting job running security audits for a financial institution in Los Angeles. The IT manager of the company you will be working for tries to see if you remember your ECSA class. He asks about the methodology you will be using to test the company's network.
How would you answer?
- A. IBM Methodology
- B. LPT Methodology
- C. Google Methodology
- D. Microsoft Methodology
Answer: B
NEW QUESTION 5
Harold is a security analyst who has just run the rdisk /s command to grab the backup SAM file on a computer. Where should Harold navigate on the computer to find the file?
- A. %systemroot%LSA
- B. %systemroot%repair
- C. %systemroot%system32driversetc
- D. %systemroot%system32LSA
Answer: B
NEW QUESTION 6
You are assisting a Department of Defense contract company to become compliant with the stringent
security policies set by the DoD. One such strict rule is that firewalls must only allow incoming connections that were first initiated by internal computers.
What type of firewall must you implement to abide by this policy?
- A. Circuit-level proxy firewall
- B. Packet filtering firewall
- C. Application-level proxy firewall
- D. Statefull firewall
Answer: D
NEW QUESTION 7
During the process of fingerprinting a web application environment, what do you need to do in order to analyze HTTP and HTTPS request headers and the HTML source code?
- A. Examine Source of the Available Pages
- B. Perform Web Spidering
- C. Perform Banner Grabbing
- D. Check the HTTP and HTML Processing by the Browser
Answer: D
NEW QUESTION 8
Jim performed a vulnerability analysis on his network and found no potential problems. He runs another utility that executes exploits against his system to verify the results of the vulnerability test. The second utility executes five known exploits against his network in which the vulnerability analysis said were not exploitable.
What kind of results did Jim receive from his vulnerability analysis?
- A. True negatives
- B. False negatives
- C. False positives
- D. True positives
Answer: B
NEW QUESTION 9
Julia is a senior security analyst for Berber Consulting group. She is currently working on a contract for a small accounting firm in Florida. They have given her permission to perform social engineering attacks on the company to see if their in-house training did any good. Julia calls the main number for the accounting firm and talks to the receptionist. Julia says that she is an IT technician from the company's main office in Iowa.
She states that she needs the receptionist's network username and password to troubleshoot a problem they are having. Julia says that Bill Hammond, the CEO of the company, requested this information. After hearing the name of the CEO, the receptionist gave Julia all the information she asked for.
What principal of social engineering did Julia use?
- A. Reciprocation
- B. Friendship/Liking
- C. Social Validation
- D. Scarcity
Answer: A
NEW QUESTION 10
What is the target host IP in the following command?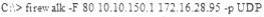
- A. Firewalk does not scan target hosts
- B. 172.16.28.95
- C. This command is using FIN packets, which cannot scan target hosts
- D. 10.10.150.1
Answer: A
NEW QUESTION 11
George is the network administrator of a large Internet company on the west coast. Per corporate policy, none of the employees in the company are allowed to use FTP or SFTP programs without obtaining approval from the IT department. Few managers are using SFTP program on their computers.
Before talking to his boss, George wants to have some proof of their activity. George wants to use Ethereal t monitor network traffic, but only SFTP traffic to and from his network. What filter should George use in Ethereal?
- A. net port 22
- B. udp port 22 and host 172.16.28.1/24
- C. src port 22 and dst port 22
- D. src port 23 and dst port 23
Answer: C
NEW QUESTION 12
HTTP protocol specifies that arbitrary binary characters can be passed within the URL by using %xx notation, where 'xx' is the
- A. ASCII value of the character
- B. Binary value of the character
- C. Decimal value of the character
- D. Hex value of the character
Answer: D
NEW QUESTION 13
After attending a CEH security seminar, you make a list of changes you would like to perform on your
network to increase its security. One of the first things you change is to switch the Restrict Anonymous setting from 0 to 1 on your servers. This, as you were told, would prevent anonymous users from establishing a null session on the server.
Using User info tool mentioned at the seminar, you succeed in establishing a null session with one of the servers. Why is that?
- A. Restrict Anonymous must be set to "2" for complete security
- B. Restrict Anonymous must be set to "3" for complete security
- C. There is no way to always prevent an anonymous null session from establishing
- D. Restrict Anonymous must be set to "10" for complete security
Answer: A
NEW QUESTION 14
An attacker injects malicious query strings in user input fields to bypass web service authentication mechanisms and to access back-end databases. Which of the following attacks is this?
- A. Frame Injection Attack
- B. LDAP Injection Attack
- C. XPath Injection Attack
- D. SOAP Injection Attack
Answer: D
NEW QUESTION 15
Which of the following is NOT related to the Internal Security Assessment penetration testing strategy?
- A. Testing to provide a more complete view of site security
- B. Testing focused on the servers, infrastructure, and the underlying software, including the target
- C. Testing including tiers and DMZs within the environment, the corporate network, or partner company connections
- D. Testing performed from a number of network access points representing each logical and physical segment
Answer: B
NEW QUESTION 16
A firewall protects networked computers from intentional hostile intrusion that could compromise confidentiality or result in data corruption or denial of service. It examines all traffic routed between the two networks to see if it meets certain criteria. If it does, it is routed between the networks, otherwise it is stopped.
Why is an appliance-based firewall is more secure than those implemented on top of the commercial operating system (Software based)?
- A. Appliance based firewalls cannot be upgraded
- B. Firewalls implemented on a hardware firewall are highly scalable
- C. Hardware appliances does not suffer from security vulnerabilities associated with the underlying operating system
- D. Operating system firewalls are highly configured
Answer: A
NEW QUESTION 17
The SnortMain () function begins by associating a set of handlers for the signals, Snort receives. It does this using the signal () function. Which one of the following functions is used as a programspecific signal and the handler for this calls the DropStats() function to output the current Snort statistics?
- A. SIGUSR1
- B. SIGTERM
- C. SIGINT
- D. SIGHUP
Answer: A
NEW QUESTION 18
Identify the port numbers used by POP3 and POP3S protocols.
- A. 113 and 981
- B. 111 and 982
- C. 110 and 995
- D. 109 and 973
Answer: C
NEW QUESTION 19
You work as an IT security auditor hired by a law firm in Boston. You have been assigned the responsibility to audit the client for security risks. When assessing the risk to the clients network, what step should you take first?
- A. Analyzing, categorizing and prioritizing resources
- B. Evaluating the existing perimeter and internal security
- C. Checking for a written security policy
- D. Analyzing the use of existing management and control architecture
Answer: C
NEW QUESTION 20
Attackers create secret accounts and gain illegal access to resources using backdoor while bypassing the authentication procedures. Creating a backdoor is a where an attacker obtains remote access to a computer on a network.
Which of the following techniques do attackers use to create backdoors to covertly gather critical information about a target machine?
- A. Internal network mapping to map the internal network of the target machine
- B. Port scanning to determine what ports are open or in use on the target machine
- C. Sniffing to monitor all the incoming and outgoing network traffic
- D. Social engineering and spear phishing attacks to install malicious programs on the target machine
Answer: D
NEW QUESTION 21
Which of the following will not handle routing protocols properly?
- A. “Internet-router-firewall-net architecture”
- B. “Internet-firewall-router-net architecture”
- C. “Internet-firewall -net architecture”
- D. “Internet-firewall/router(edge device)-net architecture”
Answer: B
NEW QUESTION 22
What is the difference between penetration testing and vulnerability testing?
- A. Penetration testing goes one step further than vulnerability testing; while vulnerability tests check for known vulnerabilities, penetration testing adopts the concept of ‘in-depth ethical hacking’
- B. Penetration testing is based on purely online vulnerability analysis while vulnerability testing engages ethical hackers to find vulnerabilities
- C. Vulnerability testing is more expensive than penetration testing
- D. Penetration testing is conducted purely for meeting compliance standards while vulnerability testing is focused on online scans
Answer: A
NEW QUESTION 23
The term social engineering is used to describe the various tricks used to fool people (employees, business partners, or customers) into voluntarily giving away information that would not normally be known to the general public.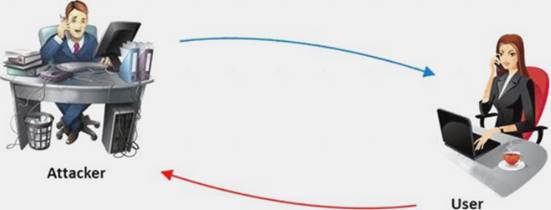
What is the criminal practice of social engineering where an attacker uses the telephone system in an attempt to scam the user into surrendering private information?
- A. Phishing
- B. Spoofing
- C. Tapping
- D. Vishing
Answer: D
NEW QUESTION 24
What does ICMP Type 3/Code 13 mean?
- A. Host Unreachable
- B. Port Unreachable
- C. Protocol Unreachable
- D. Administratively Blocked
Answer: D
NEW QUESTION 25
The first and foremost step for a penetration test is information gathering. The main objective of this test is to gather information about the target system which can be used in a malicious manner to gain access to the target systems.
Which of the following information gathering terminologies refers to gathering information through social engineering on-site visits, face-to-face interviews, and direct questionnaires?
- A. Active Information Gathering
- B. Pseudonymous Information Gathering
- C. Anonymous Information Gathering
- D. Open Source or Passive Information Gathering
Answer: A
NEW QUESTION 26
Which of the following password hashing algorithms is used in the NTLMv2 authentication mechanism?
- A. AES
- B. DES (ECB mode)
- C. MD5
- D. RC5
Answer: C
NEW QUESTION 27
Which of the following defines the details of services to be provided for the client’s organization and the list of services required for performing the test in the organization?
- A. Draft
- B. Report
- C. Requirement list
- D. Quotation
Answer: D
NEW QUESTION 28
Identify the type of firewall represented in the diagram below: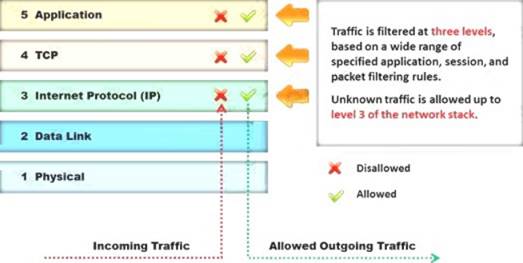
- A. Stateful multilayer inspection firewall
- B. Application level gateway
- C. Packet filter
- D. Circuit level gateway
Answer: A
NEW QUESTION 29
......
100% Valid and Newest Version ECSAv10 Questions & Answers shared by 2passeasy, Get Full Dumps HERE: https://www.2passeasy.com/dumps/ECSAv10/ (New 201 Q&As)