Most Recent Certified Ethical Hacker (CEH) CEH-001 Preparation Exams
Top Quality of CEH-001 training materials and braindump for GAQM certification for IT engineers, Real Success Guaranteed with Updated CEH-001 pdf dumps vce Materials. 100% PASS Certified Ethical Hacker (CEH) exam Today!
GAQM CEH-001 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Employees in a company are no longer able to access Internet web sites on their computers. The network administrator is able to successfully ping IP address of web servers on the Internet and is able to open web sites by using an IP address in place of the URL. The administrator runs the nslookup command for www.eccouncil.org and receives an error message stating there is no response from the server. What should the administrator do next?
- A. Configure the firewall to allow traffic on TCP ports 53 and UDP port 53.
- B. Configure the firewall to allow traffic on TCP ports 80 and UDP port 443.
- C. Configure the firewall to allow traffic on TCP port 53.
- D. Configure the firewall to allow traffic on TCP port 8080.
Answer: A
NEW QUESTION 2
TCP SYN Flood attack uses the three-way handshake mechanism.
1. An attacker at system A sends a SYN packet to victim at system B.
2. System B sends a SYN/ACK packet to victim A.
3. As a normal three-way handshake mechanism system A should send an ACK packet to system B, however, system A does not send an ACK packet to system B. In this case client B is waiting for an ACK packet from client A.
This status of client B is called
- A. "half-closed"
- B. "half open"
- C. "full-open"
- D. "xmas-open"
Answer: B
NEW QUESTION 3
What do you call a pre-computed hash?
- A. Sun tables
- B. Apple tables
- C. Rainbow tables
- D. Moon tables
Answer: C
NEW QUESTION 4
One of the effective DoS/DDoS countermeasures is 'Throttling'. Which statement correctly defines this term?
- A. Set up routers that access a server with logic to adjust incoming traffic to levels that will be safe for the server to process
- B. Providers can increase the bandwidth on critical connections to prevent them from going down in the event of an attack
- C. Replicating servers that can provide additional failsafe protection
- D. Load balance each server in a multiple-server architecture
Answer: A
NEW QUESTION 5
Leesa is the senior security analyst for a publicly traded company. The IT department recently rolled out an intranet for company use only with information ranging from training, to holiday schedules, to human resources data. Leesa wants to make sure the site is not accessible from outside and she also wants to ensure the site is Sarbanes-Oxley (SOX) compliant. Leesa goes to a public library as she wants to do some Google searching to verify whether the company's intranet is accessible from outside and has been indexed by Google. Leesa wants to search for a website title of "intranet" with part of the URL containing the word "intranet" and the words "human resources" somewhere in the webpage.
What Google search will accomplish this?
- A. related:intranet allinurl:intranet:"human resources"
- B. cache:"human resources" inurl:intranet(SharePoint)
- C. intitle:intranet inurl:intranet+intext:"human resources"
- D. site:"human resources"+intext:intranet intitle:intranet
Answer: C
NEW QUESTION 6
Steve scans the network for SNMP enabled devices. Which port number Steve should scan?
- A. 150
- B. 161
- C. 169
- D. 69
Answer: B
NEW QUESTION 7
Company A and Company B have just merged and each has its own Public Key Infrastructure (PKI). What must the Certificate Authorities (CAs) establish so that the private PKIs for Company A and Company B trust one another and each private PKI can validate digital certificates from the other company?
- A. Poly key exchange
- B. Cross certification
- C. Poly key reference
- D. Cross-site exchange
Answer: B
NEW QUESTION 8
Which of the following examples best represents a logical or technical control?
- A. Security tokens
- B. Heating and air conditioning
- C. Smoke and fire alarms
- D. Corporate security policy
Answer: A
NEW QUESTION 9
In order to attack a wireless network, you put up an access point and override the signal of the real access point. As users send authentication data, you are able to capture it. What kind of attack is this?
- A. Rouge access point attack
- B. Unauthorized access point attack
- C. War Chalking
- D. WEP attack
Answer: A
Explanation:
The definition of a Rogue access point is:
1. A wireless access point (AP) installed by an employee without the consent of the IT department. Without the proper security configuration, users have exposed their company's network to the outside world.
2. An access point (AP) set up by an attacker outside a facility with a wireless network. Also called an "evil twin, " the rogue AP picks up beacons (signals that advertise its presence) from the company's legitimate AP and transmits identical beacons, which some client machines inside the building associate with.
NEW QUESTION 10
Which of the following lists are valid data-gathering activities associated with a risk assessment?
- A. Threat identification, vulnerability identification, control analysis
- B. Threat identification, response identification, mitigation identification
- C. Attack profile, defense profile, loss profile
- D. System profile, vulnerability identification, security determination
Answer: A
NEW QUESTION 11
Jackson discovers that the wireless AP transmits 128 bytes of plaintext, and the station responds by encrypting the plaintext. It then transmits the resulting ciphertext using the same key and cipher that are used by WEP to encrypt subsequent network traffic. What authentication mechanism is being followed here?
- A. no authentication
- B. single key authentication
- C. shared key authentication
- D. open system authentication
Answer: C
NEW QUESTION 12
On a Linux device, which of the following commands will start the Nessus client in the background so that the Nessus server can be configured?
- A. nessus +
- B. nessus *s
- C. nessus &
- D. nessus -d
Answer: C
NEW QUESTION 13
Which of the following tools are used for enumeration? (Choose three.)
- A. SolarWinds
- B. USER2SID
- C. Cheops
- D. SID2USER
- E. DumpSec
Answer: BDE
Explanation:
USER2SID, SID2USER, and DumpSec are three of the tools used for system enumeration. Others are tools such as NAT and Enum. Knowing which tools are used in each step of the hacking methodology is an important goal of the CEH exam. You should spend a portion of your time preparing for the test practicing with the tools and learning to understand their output.
NEW QUESTION 14
In an attempt to secure his wireless network, Bob turns off broadcasting of the SSID. He concludes that since his access points require the client computer to have the proper SSID, it would prevent others from connecting to the wireless network. Unfortunately unauthorized users are still able to connect to the wireless network.
Why do you think this is possible?
- A. Bob forgot to turn off DHCP.
- B. All access points are shipped with a default SSID.
- C. The SSID is still sent inside both client and AP packets.
- D. Bob’s solution only works in ad-hoc mode.
Answer: B
Explanation:
All access points are shipped with a default SSID unique to that manufacturer, for example 3com uses the default ssid comcomcom.
NEW QUESTION 15
Which of the following attacks takes best advantage of an existing authenticated connection?
- A. Spoofing
- B. Session Hijacking
- C. Password Sniffing
- D. Password Guessing
Answer: B
Explanation:
Session hijacking is the act of taking control of a user session after successfully obtaining or generating an authentication session ID. Session hijacking involves an attacker using captured, brute forced or reverse-engineered session IDs to seize control of a legitimate user's Web application session while that session is still in progress.
NEW QUESTION 16
What results will the following command yielD. 'NMAP -sS -O -p 123-153 192.168.100.3'?
- A. A stealth scan, opening port 123 and 153
- B. A stealth scan, checking open ports 123 to 153
- C. A stealth scan, checking all open ports excluding ports 123 to 153
- D. A stealth scan, determine operating system, and scanning ports 123 to 153
Answer: D
NEW QUESTION 17
You want to perform advanced SQL Injection attack against a vulnerable website. You are unable to perform command shell hacks on this server. What must be enabled in SQL Server to launch these attacks?
- A. System services
- B. EXEC master access
- C. xp_cmdshell
- D. RDC
Answer: C
NEW QUESTION 18
WEP is used on 802.11 networks, what was it designed for?
- A. WEP is designed to provide a wireless local area network (WLAN) with a level of security and privacy comparable to what it usually expected of a wired LAN.
- B. WEP is designed to provide strong encryption to a wireless local area network (WLAN) with a lever of integrity and privacy adequate for sensible but unclassified information.
- C. WEP is designed to provide a wireless local area network (WLAN) with a level of availability and privacy comparable to what is usually expected of a wired LAN.
- D. WEOP is designed to provide a wireless local area network (WLAN) with a level of privacy comparable to what it usually expected of a wired LAN.
Answer: A
Explanation:
WEP was intended to provide comparable confidentiality to a traditional wired network (in particular it does not protect users of the network from each other), hence the name. Several serious weaknesses were identified by cryptanalysts — any WEP key can be cracked with readily available software in two minutes or less — and WEP was superseded by Wi-Fi Protected Access (WPA) in 2003, and then by the full IEEE 802.11i standard (also known as WPA2) in 2004.
NEW QUESTION 19
What type of port scan is shown below?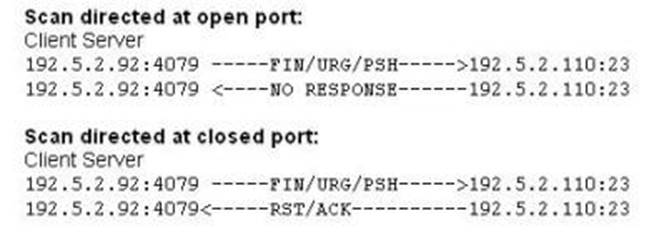
- A. Idle Scan
- B. Windows Scan
- C. XMAS Scan
- D. SYN Stealth Scan
Answer: C
NEW QUESTION 20
Within the context of Computer Security, which of the following statements describes Social Engineering best?
- A. Social Engineering is the act of publicly disclosing information
- B. Social Engineering is the means put in place by human resource to perform time accounting
- C. Social Engineering is the act of getting needed information from a person rather than breaking into a system
- D. Social Engineering is a training program within sociology studies
Answer: C
NEW QUESTION 21
In the following example, which of these is the "exploit"?
Today, Microsoft Corporation released a security notice. It detailed how a person could bring down the Windows 2003 Server operating system, by sending malformed packets to it. They detailed how this malicious process had been automated using basic scripting. Even worse, the new automated method for bringing down the server has already been used to perform denial of service attacks on many large commercial websites.
Select the best answer.
- A. Microsoft Corporation is the exploit.
- B. The security "hole" in the product is the exploit.
- C. Windows 2003 Server
- D. The exploit is the hacker that would use this vulnerability.
- E. The documented method of how to use the vulnerability to gain unprivileged access.
Answer: E
Explanation:
Explanations:
Microsoft is not the exploit, but if Microsoft documents how the vulnerability can be used to gain unprivileged access, they are creating the exploit. If they just say that there is a hole in the product, then it is only a vulnerability. The security "hole" in the product is called the "vulnerability". It is documented in a way that shows how to use the vulnerability to gain unprivileged access, and it then becomes an "exploit". In the example given, Windows 2003 Server is the TOE (Target of Evaluation). A TOE is an IT System, product or component that requires security evaluation or is being identified. The hacker that would use this vulnerability is exploiting it, but the hacker is not the exploit. The documented method of how to use the vulnerability to gain unprivileged access is the correct answer.
NEW QUESTION 22
Shayla is an IT security consultant, specializing in social engineering and external penetration tests. Shayla has been hired on by Treks Avionics, a subcontractor for the Department of Defense. Shayla has been given authority to perform any and all tests necessary to audit the company's network security.
No employees for the company, other than the IT director, know about Shayla's work she will be doing. Shayla's first step is to obtain a list of employees through company website contact pages. Then she befriends a female employee of the company through an online chat website. After meeting with the female employee numerous times, Shayla is able to gain her trust and they become friends. One day, Shayla steals the employee's access badge and uses it to gain unauthorized access to the Treks Avionics offices.
What type of insider threat would Shayla be considered?
- A. She would be considered an Insider Affiliate
- B. Because she does not have any legal access herself, Shayla would be considered an Outside Affiliate
- C. Shayla is an Insider Associate since she has befriended an actual employee
- D. Since Shayla obtained access with a legitimate company badge; she would be considered a Pure Insider
Answer: A
NEW QUESTION 23
Which of the following best describes session key creation in SSL?
- A. It is created by the server after verifying theuser's identity
- B. It is created by the server upon connection by the client
- C. It is created by the client from the server's public key
- D. It is created by the client after verifying the server's identity
Answer: D
Explanation:
An SSL session always begins with an exchange of messages called the SSL handshake. The handshake allows the server to authenticate itself to the client using public-key techniques, then allows the client and the server to cooperate in the creation of symmetric keys used for rapid encryption, decryption, and tamper detection during the session that follows. Optionally, the handshake also allows the client to authenticate itself to the server.
NEW QUESTION 24
A security analyst in an insurance company is assigned to test a new web application that
will be used by clients to help them choose and apply for an insurance plan. The analyst discovers that the application is developed in ASP scripting language and it uses MSSQL as a database backend. The analyst locates the application's search form and introduces the following code in the search input fielD.
IMG SRC=novbscript...msgbox("Vulnerable");> originalAttribute="SRC" originalPath="novbscript...msgbox("Vulnerable");>"
When the analyst submits the form, the browser returns a pop-up window that says "Vulnerable".
Which web applications vulnerability did the analyst discover?
- A. Cross-site request forgery
- B. Command injection
- C. Cross-site scripting
- D. SQL injection
Answer: C
NEW QUESTION 25
Which of the following is an automated vulnerability assessment tool?
- A. Whack a Mole
- B. Nmap
- C. Nessus
- D. Kismet
- E. Jill32
Answer: C
Explanation:
Nessus is a vulnerability assessment tool.
NEW QUESTION 26
If a competitor wants to cause damage to your organization, steal critical secrets, or put you out of business, they just have to find a job opening, prepare someone to pass the interview, have that person hired, and they will be in the organization.
How would you prevent such type of attacks?
- A. It is impossible to block these attacks
- B. Hire the people through third-party job agencies who will vet them for you
- C. Conduct thorough background checks before you engage them
- D. Investigate their social networking profiles
Answer: C
NEW QUESTION 27
What file system vulnerability does the following command take advantage of?
type c:\anyfile.exe > c:\winnt\system32\calc.exe:anyfile.exe
- A. HFS
- B. ADS
- C. NTFS
- D. Backdoor access
Answer: B
Explanation:
ADS (or Alternate Data Streams) is a “feature” in the NTFS file system that makes it possible to hide information in alternate data streams in existing files. The file can have multiple data streams and the data streams are accessed by filename:stream.
NEW QUESTION 28
......
Thanks for reading the newest CEH-001 exam dumps! We recommend you to try the PREMIUM Dumps-files.com CEH-001 dumps in VCE and PDF here: https://www.dumps-files.com/files/CEH-001/ (878 Q&As Dumps)