Best Quality Microsoft 98-368 Question Online
We provide real 98-368 exam questions and answers braindumps in two formats. Download PDF & Practice Tests. Pass Microsoft 98-368 Exam quickly & easily. The 98-368 PDF type is available for reading and printing. You can print more and practice many times. With the help of our Microsoft 98-368 dumps pdf and vce product and material, you can easily pass the 98-368 exam.
Free 98-368 Demo Online For Microsoft Certifitcation:
NEW QUESTION 1
You manage Windows 8 Pro desktop and laptop computers. Which volume types can you encrypt by using BitLocker?
- A. dynamic volumes
- B. simple volumes
- C. virtual hard disks
- D. software-used RAID
Answer: B
Explanation:
Bitlocker supports Basic (simple) volumes. Incorrect answers:
Not A: Dynamic disks are not supported by BitLocker.
Not C: Bootable and non-bootable virtual hard disks (VHDs)
Not D: Software-based RAID systems are not supported by Bitlocker. Reference: BitLocker Frequently Asked Questions (FAQ) https://technet.microsoft.com/en-us/library/hh831507.aspx
NEW QUESTION 2
You perform a bare metal installation of Microsoft Windows 10 Enterprise on a new computer. The computer has a single 1 TB hard disk that you configure as a single partition.
Which file system should you use to format the disk partition?
- A. NTFS
- B. ReFS
- C. FAT32
- D. exFAT
Answer: A
NEW QUESTION 3
This requires that you evaluate the underlined text to determine if it is correct.
You are setting up your home network. All devices on your home network connect through a wireless access point.
To share media files between your computer running Windows 10 and your video game system, you should create a public network.
Review the underlined text. If it makes the statement correct, select “No change is needed”. If the statement is incorrect, select the answer choice than makes the statement correct.
- A. No change is needed
- B. an extranet
- C. a VPN connection
- D. a private network
Answer: D
Explanation:
References:
https://www.howtogeek.com/245982/WHATS-THE-DIFFERENCE-BETWEEN-PRIVATE-AND- PUBLICNETWORKS-IN-WINDOWS/
NEW QUESTION 4
The president of your university asks you to set up a service website for students who live in dorms. The website’s official launch date is in two days, and you do not have the resources needed to set up the server infrastructure and develop the system.
You need a cloud-based solution than can have the servers and storage available in two days. Which Microsoft cloud solution achieves this goal?
- A. Microsoft Intune
- B. Microsoft Azure
- C. Achieve Directory
- D. Microsoft OneDrive
Answer: B
Explanation:
Microsoft Azure is a cloud computing platform and infrastructure, created by Microsoft, for building, deploying and managing applications and services through a global network of Microsoft-managed datacenters.
Microsoft Azure services include: Websites: High density hosting of websites. Reference: http://en.wikipedia.org/wiki/Microsoft_Azure#Services
NEW QUESTION 5
DRAG DROP
Match each type of malware to its definition.
To answer, drag the appropriate malware type from the column on the left to the definition on the right. Each malware type may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.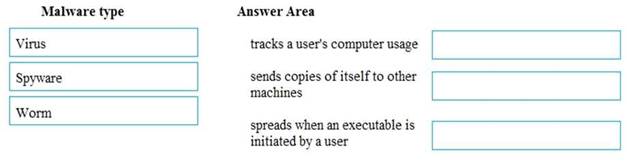
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
References:
https://www.malwarefox.com/malware-types/#tab-con-6
NEW QUESTION 6
When you copy a file from one NTFS file system partition to a different NTFS partition, what happens to the file permissions of the copied file?
- A. They are the combined permissions of the original file and destination folder
- B. They inherit the permissions of the destination folder
- C. They remain the same as the original
- D. They most restrictive permissions are applied
Answer: B
Explanation:
References:
https://support.microsoft.com/en-us/help/320246/inherited-permissions-are-not-automatically- updated-whenyou-move-fold
NEW QUESTION 7
HOTSPOT
You use a laptop running Microsoft Windows 10. You connect to the Internet using the Wi-Fi connections at a coffee shop.
You plan to visit several websites while doing a research project and want to verify that your computer is configured for safe communication.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.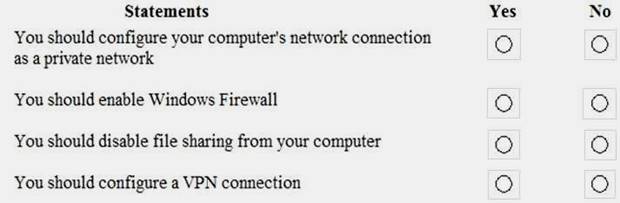
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
References:
https://thenextweb.com/insider/2015/08/08/how-to-stop-hackers-from-stealing-your-information- on-public-wi-fi/
https://www.lifewire.com/how-to-connect-to-a-wi-fi-network-2378229
NEW QUESTION 8
This question requires that you evaluate the underlined text to determine if it is correct.
"Redundant" Microsoft Azure applications are able to meet increased demand with consistent results in acceptable time window.
Instructions: Review the underlined text. If it makes the statement correct, select “No change is needed”. If the statement is incorrect, select the answer choice than makes the statement correct.
- A. No change is needed
- B. Highly Available
- C. Fault Tolerant
- D. Scalable
Answer: D
Explanation:
Scalable applications are able to meet increased demand with consistent results in acceptable time windows.
When a system is scalable, it scales horizontally or vertically to manage increases in load while maintaining consistent performance. In basic terms, horizontal scaling adds more machines of the same size (processor, memory, bandwidth) while vertical scaling increases the size of the existing machines.
Reference: Disaster Recovery and High Availability for Azure Applications
https://msdn.microsoft.com/en-us/library/azure/dn251004.aspx
NEW QUESTION 9
This question requires that you evaluate the underlined text to determine if it is correct. You manage Windows 8.1 desktop and laptop computers in your university’s computer lab.
The university’s IT team recently implemented an active directory environment.
You need to join the desktop and laptop computers to a new Active Directory domain. You should use the "Network and Internet" Control Panel applet to achieve this goal.
Instructions: Review the underlined text. If it makes the statement correct, select “No change is needed”. If the statement is incorrect, select the answer choice than makes the statement correct.
- A. No change is needed
- B. User Accounts
- C. Administrative Tools
- D. System
Answer: D
Explanation:
Join a domain, workgroup, or homegroup
Open System by swiping in from the right edge of the screen, tapping Search (or if you're using a mouse, pointing to the upper-right corner of the screen, moving the mouse pointer down, and then clicking Search), entering System in the search box, and tapping or clicking System.
Under Computer name, domain, and workgroup settings, click Change settings.  You might be asked for an admin password or to confirm your choice.
You might be asked for an admin password or to confirm your choice.
Click Network ID and follow the steps on your screen.
Reference: http://windows.microsoft.com/en-us/windows-8/join-domain-workgroup-homegroup
NEW QUESTION 10
This question requires that you evaluate the underlined text to determine if it is correct. Microsoft Azure storage solutions replicates "four" copies of your data within a single region.
Instructions: Review the underlined text. If it makes the statement correct, select “No change is needed”. If the statement is incorrect, select the answer choice than makes the statement correct.
- A. No change is needed
- B. two
- C. three
- D. six
Answer: C
Explanation:
Geo-redundant storage (GRS). Geo-redundant storage is enabled for your storage account by default when you create it. GRS maintains six copies of your data. With GRS, your data is replicated three times within the primary region, and is also replicated three times in a secondary region hundreds of miles away from the primary region, providing the highest level of durability.
Reference: Introduction to Microsoft Azure Storage
https://azure.microsoft.com/en-gb/documentation/articles/storage-introduction/
NEW QUESTION 11
You need to create an Azure storage account through Azure Storage Services to support an Azure Windows virtual machine (VM). You want to keep subscription costs to a minimum.
What type of storage account should you create?
- A. Standard storage performance tier
- B. Blob cool access tier
- C. Premium storage performance tier
- D. Blob hot access tier
Answer: D
Explanation:
References:
https://www.petri.com/choosing-azure-storage-account-type https://docs.microsoft.com/en-us/azure/storage/common/storage-introduction
NEW QUESTION 12
You are a desktop support engineer for an advertising company that uses Windows 8.1 workstations. An employee who manages video content for the company website recently lost important video files due to a single-drive failure on a Windows 8.1 workstation.
You need to prevent a single-drive failure from occurring again on this employee’s workstation, which only has a capacity for three physical hard drivers. Additionally, the employee requires optimal performance when manipulating and streaming video files.
Which Storage Space solution should you implement?
- A. three-way mirror
- B. parity spaces
- C. simple spaces
- D. two-way mirror
Answer: B
Explanation:
Parity spaces (also known as RAID-5) are designed for storage efficiency and protect your files from drive failure by keeping more than one copy. Parity spaces are best for archival data and streaming
media, like music and videos. This storage layout requires at least three drives to protect you from a single drive failure and at least seven drives to protect you from two drive failures.
Reference: Storage Spaces: FAQ
http://windows.microsoft.com/en-us/windows-8/storage-spaces-pools
NEW QUESTION 13
This question requires that you evaluate the underlined text to determine if it is correct.
"Windows Server Active Directory" enables single sign-on, which simplifies user access to thousands of cloud applications on Windows, Mac and iOS devices.
Instructions: Review the underlined text. If it makes the statement correct, select “No change is needed”. If the statement is incorrect, select the answer choice than makes the statement correct.
- A. No change is needed
- B. Microsoft Account
- C. Active Directory Rights Manager
- D. Azure Active Directory
Answer: D
Explanation:
Azure Active Directory is a comprehensive identity and access management cloud solution that provides a robust set of capabilities to manage users and groups.
Azure Active Directory enables single sign-on to simplify user access to thousands of cloud applications from Windows, Mac, Android and iOS devices.
Reference: Identity and Access Management for the Cloud
http://azure.microsoft.com/en-us/services/active-directory/
NEW QUESTION 14
This question requires that you evaluate the underlined text to determine if it is correct.
When BitLocker is enabled and and protecting a local drive, Trusted Platform Module (TPM) provides "pre-start system integrity verification for system and operating system drives".
Instructions: Review the underlined text. If it makes the statement correct, select “No change is needed”. If the statement is incorrect, select the answer choice than makes the statement correct.
- A. No change is needed
- B. 256-bit encryption that uses Advanced Encryption Standard (AES)
- C. a location that stores recovery keys for removable drives
- D. boot sector mapping for the startup process
Answer: C
Explanation:
Computers that incorporate a TPM have the ability to create cryptographic keys and encrypt them so that they can be decrypted only by the TPM. This process, often called "wrapping" or "binding" a key, can help protect the key from disclosure. Each TPM has a root "wrapping" key, called the Storage Root Key (SRK), which is stored within the TPM itself. The private portion of a key created in a TPM is never exposed to any other component, software, process, or person.
Reference: Windows Trusted Platform Module Management Step-by-Step Guide
https://technet.microsoft.com/en-us/library/cc749022%28v=ws.10%29.aspx
NEW QUESTION 15
Your company uses Windows 8.1 work folders on personal devices. The devices are all registered in Microsoft Intune.
You need to enforce the following security requirements on the personal devices:
•Company data can be removed if an employee is terminated.
•Company data cannot be accessed if a devise is lost or stolen.
What should you do?
- A. Enable selective wipe, and enforce a lock screen and password
- B. Enable selective wipe, and secure files transfers with SSL
- C. Enable selective wipe, and enforce encryption
- D. Enforce encryption and enforce a lock screen and password
Answer: C
Explanation:
* Microsoft Intune provides selective wipe, full wipe, remote lock, and passcode reset capabilities. A selective wipe to remove only company data.
* Encryption on Mobile Devices can be managed with Configuration Manager and Intune
Reference: Help protect your data with remote wipe, remote lock, or passcode reset using Microsoft Intune
https://technet.microsoft.com/en-us/library/jj676679.aspx
Reference: Managing Encryption on Mobile Devices with Configuration Manager and Intune http://blogs.technet.com/b/pauljones/archive/2014/08/04/managing-encryption-on-mobile- devices-with-configuration-manager-and-intune.aspx
NEW QUESTION 16
What is an example of the way in which a Trojan horse commonly spreads to other computers?
- A. It inserts copies of itself into other computer programs
- B. It traverses a network by exploiting a vulnerability
- C. It pretends to be a document from a friend
- D. It downloads from an infected web page
Answer: D
Explanation:
Trojan horses are commonly found on websites that offer free software, such as shareware programs. These communal gathering spots on the Web give Trojan horse writers a degree of anonymity along with the chance of attacking as many random victims as possible. Since website operators rarely have time to thoroughly examine every file posted, an occasional Trojan horse can slip through the checking procedures unnoticed. -
Reference: HOW TROJAN HORSES SPREAD
http://etutorials.org/Misc/computer+book/Part+2+Dangerous+Threats+on+the+Internet/Chapter+8
+Trojan+Horses-+Beware+of+Geeks+Bearing+Gifts/HOW+TROJAN+HORSES+SPREAD/
NEW QUESTION 17
This requires that you evaluate the underlined text to determine if it is correct.
You have a Windows 10 computer that is part of a workgroup. To share the C:\Work folder from the computer and make it available to offline users, you need to use the public share option.
Review the underlined text, if it makes the statement correct, select “No change is needed”. If the statement is incorrect, select the answer choice than makes the statement correct.
- A. No change is needed
- B. advanced
- C. HomeGroup
- D. basic
Answer: B
Explanation:
References:
https://www.digitalcitizen.life/how-customize-your-advanced-network-sharing-settings-windows-81
NEW QUESTION 18
Which type of information about users does biometrics evaluate?
- A. phrases a user has memorized
- B. where a user is located
- C. physical characteristics of a user
- D. objects a user carries with him or her
Answer: C
Explanation:
Biometrics refers to authentication techniques that rely on measurable physical characteristics that can be automatically checked.
Note: There are several types of biometric identification schemes: face: the analysis of facial characteristics
fingerprint: the analysis of an individual's unique fingerprints
hand geometry: the analysis of the shape of the hand and the length of the fingers retina: the analysis of the capillary vessels located at the back of the eye
iris: the analysis of the colored ring that surrounds the eye's pupil signature: the analysis of the way a person signs his name.
vein: the analysis of pattern of veins in the back if the hand and the wrist
voice: the analysis of the tone, pitch, cadence and frequency of a person's voice. Reference: http://www.webopedia.com/TERM/B/biometrics.html
NEW QUESTION 19
Which Microsoft cloud service can perform virtual video conferences?
- A. Azure
- B. Intune
- C. Skype for Business
- D. OneDrive
Answer: C
Explanation:
References:
https://www.skype.com/en/business/
https://www.lynda.com/SharePoint-tutorials/Microsoft-Cloud-Services-SharePoint-Online-OneDrive- Skype-Business-Online/618724-2.html
NEW QUESTION 20
Which is a feature Active Directory Rights Management Services (AD RMS)?
- A. manages Digital Rights Media (DRM) for digital media
- B. provides a permissions system that works with any cloud-based storage solution
- C. manages share and file permissions on all servers in enterprise
- D. allow users to define who can open, modify, print, or forward a document
Answer: D
Explanation:
Windows Rights Management Services (also called Rights Management Services, Active Directory Rights Management Services or RMS) is a form of Information Rights Management used on Microsoft Windows that uses encryption and a form of selective functionality denial for limiting access to documents such as corporate e-mail, Word documents, and web pages, and the operations authorized users can perform on them. Companies can use this technology to encrypt information stored in such document formats, and through policies embedded in the documents, prevent the protected content from being decrypted except by specified people or groups, in certain environments, under certain conditions, and for certain periods of time.
Reference: http://en.wikipedia.org/wiki/Active_Directory_Rights_Management_Services
NEW QUESTION 21
This requires that you evaluate the underlined text to determine if it is correct. The OneDrive service is used to create a private, enterprise-based social network.
Review the underlined text. If it makes the statement correct, select “No change is needed”. If the statement is incorrect, select the answer choice than makes the statement correct.
- A. No change is needed
- B. Skype for Business
- C. Yammer
- D. Azure
Answer: C
Explanation:
References:
https://products.office.com/en-za/yammer/yammer-overview
NEW QUESTION 22
Which two Windows 10 tools can be used to perform BitLocker encryption? (Choose two.)
- A. Manage-bde
- B. Disk Management
- C. Microsoft Management Console
- D. BitLocker control panel
Answer: AD
Explanation:
References:
https://docs.microsoft.com/en-us/windows/security/information-protection/bitlocker/bitlocker- basic-deployment
http://www.ilovefreesoftware.com/12/windows-10/enable-bitlocker-drive-encryption-windows- 10.html
NEW QUESTION 23
You manage desktop computers for your university’s computer labs. You recently upgraded these computers to Windows 8.1. You need to modify the configuration of the new computers to increase the number of items displayed in jump lists.
Which configuration tool should you use?
- A. Display Options
- B. Control Panel Personalization applet
- C. Device Manager
- D. Taskbar properties
Answer: D
Explanation:
By default up to 10 items can be added to a button's Jump List. For privacy reasons you may wish to reduce or eliminate this number. Conversely, if you find Jump Lists extremely useful you may wish to increase the number of displayed items.
1. Right-click an empty area of the taskbar and choose "Properties".
2. The "Taskbar and Start Menu Properties" multi-tabbed dialog box appears. Click the "Start Menu" tab.
3. Click the "Customize" button.
4. The "Customize Start Menu" dialog box appears. Underneath "Start menu size", next to "Number of recent items to display in Jump Lists", enter/select a value from 0-60.
Reference: Adjust Size of Jump Lists on Windows 7 Taskbar
http://malektips.com/windows-7-jump-list-size-increase-decrease.html#.VWf-4M-qpBc
NEW QUESTION 24
HOTSPOT
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.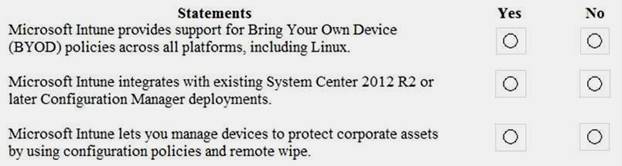
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 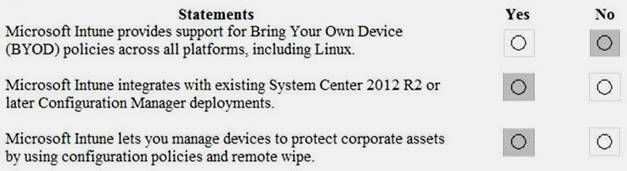
NEW QUESTION 25
This question requires that you evaluate the underlined text to determine if it is correct.
You have a Windows 8.1 computer in a WorkGroup. To share the C:\Work folder and make it available to offline users, you need to use the "public" share option.
Instructions: Review the underlined text. If it makes the statement correct, select “No change is needed”. If the statement is incorrect, select the answer choice than makes the statement correct.
- A. No change is needed
- B. advanced
- C. HomeGroup
- D. basic
Answer: B
Explanation:
In the advanced sharing dialog box Click on “Caching” button. In “Offline settings” dialog box, you can set up caching for files and programs which are offline.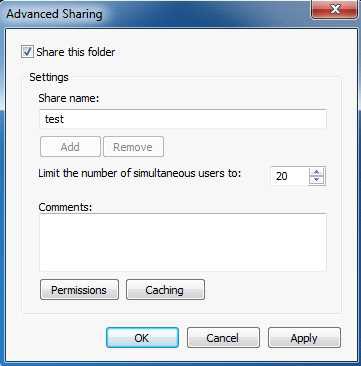
You have the following options:
i) Only the files and programs that users specify are available offline: If you select this option then, users specify the files and programs which can be accessed offline. It is the default option.
ii) No files or programs from the share are available offline: If you select this option then, caching will be turned off.
iii) All files and programs that users open from the share are automatically available offline: If you select this option then, caching is turned on for all files and programs and they can be accessed offline. Check option “Optimize for performance”.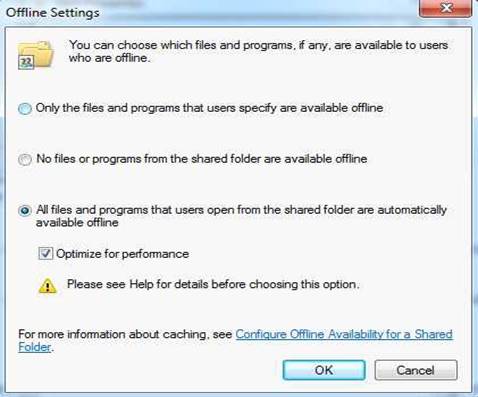
Reference: How to set advanced sharing options, custom permissions, caching for folder in Windows
7?
http://www.moreprocess.com/operating-systems/windows-7/how-to-set-advanced-sharing-options- custom-permissions-caching-for-folder-in-windows-7
NEW QUESTION 26
......
100% Valid and Newest Version 98-368 Questions & Answers shared by Allfreedumps.com, Get Full Dumps HERE: https://www.allfreedumps.com/98-368-dumps.html (New 66 Q&As)