What Highest Quality 98-367 Testing Material Is
Master the 98-367 MTA Security Fundamentals Practice Test content and be ready for exam day success quickly with this Ucertify 98-367 exam price. We guarantee it!We make it a reality and give you real 98-367 questions in our Microsoft 98-367 braindumps.Latest 100% VALID Microsoft 98-367 Exam Questions Dumps at below page. You can use our Microsoft 98-367 braindumps and pass your exam.
Also have 98-367 free dumps questions for you:
NEW QUESTION 1
You would implement a wireless intrusion prevention system to:
- A. Prevent wireless interference
- B. Detect wireless packet theft
- C. Prevent rogue wireless access points
- D. Enforce SSID broadcasting
Answer: C
Explanation:
Reference: http://en.wikipedia.org/wiki/Wireless_intrusion_prevention_system
NEW QUESTION 2
Which is the minimum requirement to create BitLocker-To-Go media on a client computer?
- A. Windows XP Professional Service Pack 3
- B. Windows Vista Enterprise Edition
- C. Windows 7 Enterprise Edition
- D. Windows 2000 Professional Service Pack 4
Answer: A
NEW QUESTION 3
A brute force attack:
- A. Uses response filtering
- B. Tries all possible password variations
- C. Uses the strongest possible algorithms
- D. Targets all the ports
Answer: B
NEW QUESTION 4
What does NAT do?
- A. It encrypts and authenticates IP packets.
- B. It provides caching and reduces network traffic.
- C. It translates public IP addresses to private addresses and vice versa.
- D. It analyzes incoming and outgoing traffic packets.
Answer: C
Explanation:
Reference: http://en.wikipedia.org/wiki/Network_address_translation
NEW QUESTION 5
Coho Winery wants to increase their web presence and hires you to set up a new web server. Coho already has servers for their business and would like to avoid purchasing a new one.
Which server is best to use as a web server, considering the security and performance concerns?
- A. SQL Server
- B. File Server
- C. Domain Controller
- D. Application Server
Answer: C
NEW QUESTION 6
HOTSPOT
For each of the following statements, select Yes if the statement is true. Otherwise, select No. Each correct selection is worth one point.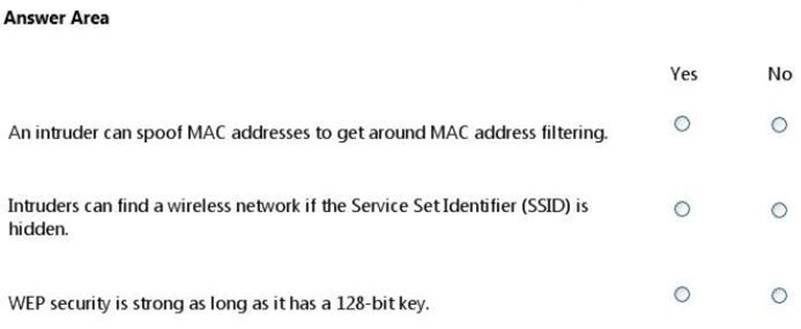
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 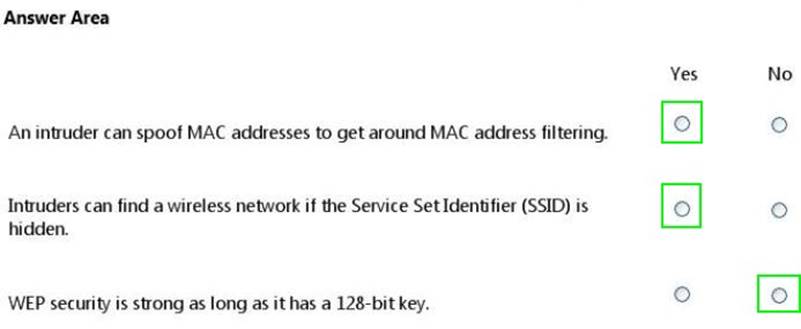
NEW QUESTION 7
Setting a minimum password age restricts when users can:
- A. Request a password reset
- B. Change their passwords
- C. Log on by using their passwords
- D. Set their own password expiration
Answer: B
Explanation:
Configure the minimum password age to be more than 0 if you want Enforce password history to be effective. Without a minimum password age, users can cycle through passwords repeatedly until they get to an old favorite.
NEW QUESTION 8
Role separation improves server security by:
- A. Enforcing principle of least privilege.
- B. Installing applications on separate hard disks.
- C. Physically separating high security servers from other servers.
- D. Placing servers on separate VLANs.
Answer: A
NEW QUESTION 9
The primary purpose of Network Access Protection (NAP) is to prevent:
- A. Loss of data from client computers on a network.
- B. Non-compliant systems from connecting to a network.
- C. Users on a network from installing software.
- D. Unauthorized users from accessing a network.
Answer: B
Explanation:
NAP enforces health policies by inspecting and assessing the health of client computers, restricting network access when client computers are noncompliant with health policy, and remediating noncompliant client computers to bring them into compliance with health policy before they are granted full network access. NAP enforces health policies on client computers that are attempting to connect to a network; NAP also provides ongoing health compliance enforcement while a client computer is connected to a network. Reference: http://technet.microsoft.com/en-us/library/cc754378(v=ws.10).aspx
NEW QUESTION 10
Passwords that contain recognizable words are vulnerable to a:
- A. Denial of Service attack
- B. Hashing attack
- C. Dictionary attack
- D. Replay attack
Answer: C
Explanation:
A dictionary attack is a method of breaking into a password-protected computer or server by systematically entering every word in a dictionary as a password. A dictionary attack can also be used in an attempt to find the key necessary to decrypt an encrypted message or document.
Dictionary attacks work because many computer users and businesses insist on using ordinary words as passwords. Dictionary attacks are rarely successful against systems that employ multiple-word phrases, and unsuccessful against systems that employ random combinations of uppercase and lowercase letters mixed up with numerals.
Reference: http://searchsecurity.techtarget.com/definition/dictionary-attack
NEW QUESTION 11
You are an intern at Litware, Inc. Your manager asks you to make password guess attempts harder by limiting login attempts on company computers.
What should you do?
- A. Enforce password sniffing.
- B. Enforce password history.
- C. Make password complexity requirements higher.
- D. Implement account lockout policy.
Answer: D
Explanation:
Reference: http://technet.microsoft.com/en-us/library/dd277400.aspx
NEW QUESTION 12
Which enables you to change the permissions on a folder?
- A. Take ownership
- B. Extended attributes
- C. Auditing
- D. Modify
Answer: D
NEW QUESTION 13
What does implementing Windows Server Update Services (WSUS) allow a company to manage?
- A. Shared private encryption key updates
- B. Updates to Group Policy Objects
- C. Active Directory server replication
- D. Windows updates for workstations and servers
Answer: D
NEW QUESTION 14
A group of users has access to Folder A and all of its contents. You need to prevent some of the users from accessing a subfolder inside Folder A.
What should you do first?
- A. Disable folder sharing
- B. Hide the folder
- C. Change the owner
- D. Block inheritance
Answer: A
NEW QUESTION 15
Bridging is a process of sending packets from source to destination on OSI layer 3.
Select the correct answer if the underlined text does not make the statement correct. Select "No change is needed" if the underlined text makes the statement correct.
- A. Routing
- B. Switching
- C. Repeating
- D. No change is needed.
Answer: A
NEW QUESTION 16
Windows Server Update Services (WSUS) is a tool that:
- A. Updates data stored in Windows servers
- B. Manages the services that run on a server
- C. Updates licensing for Windows servers
- D. Manages updates for Microsoft software
Answer: D
Explanation:
Windows Server Update Services (WSUS) enables information technology administrators to deploy the latest Microsoft product updates to computers that are running the Windows operating system. By using WSUS, administrators can fully manage the distribution of updates that are released through Microsoft Update to computers in their network.
Reference: http://technet.microsoft.com/en-us/windowsserver/bb332157.aspx
NEW QUESTION 17
An attorney hires you to increase the wireless network security for the law firm's office. The office has a very basic network, with just a modem and a router.
Which of these security modes offers the highest security?
- A. WPA-Personal
- B. WEP
- C. WPA2-Personal
- D. WPA-Enterprise
Answer: C
NEW QUESTION 18
Network Access Protection (NAP) enables administrators to control access to network resources based on a computer's:
- A. Encryption level
- B. Warranty
- C. Physical location
- D. Configuration
Answer: D
Explanation:
Network Access Protection (NAP) is a new set of operating system components included with the Windows Server® 2008 and Windows Vista® operating systems that provides a platform to help ensure that client computers on a private network meet administrator-defined requirements for system health. NAP policies define the required configuration and update status for a client computer’s operating system and critical software. For example, computers might be required to have antivirus software with the latest signatures installed, current operating system updates installed, and a host- based firewall enabled. By enforcing compliance with health requirements, NAP can help network administrators mitigate some of the risk caused by improperly configured client computers that might be exposed to viruses and other malicious software.
NEW QUESTION 19
HOTSPOT
For each of the following statements, select Yes if the statement is true. Otherwise, select No. Each correct selection is worth one point.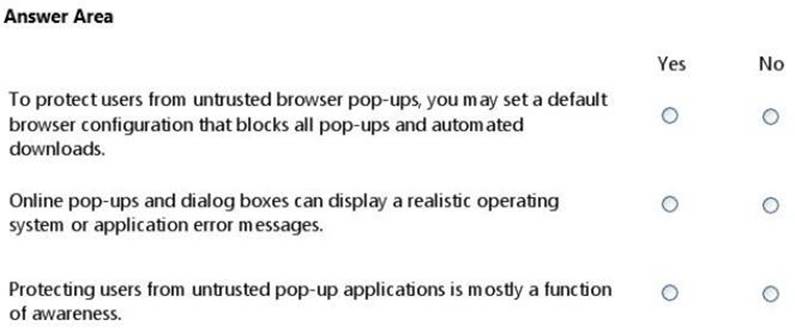
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 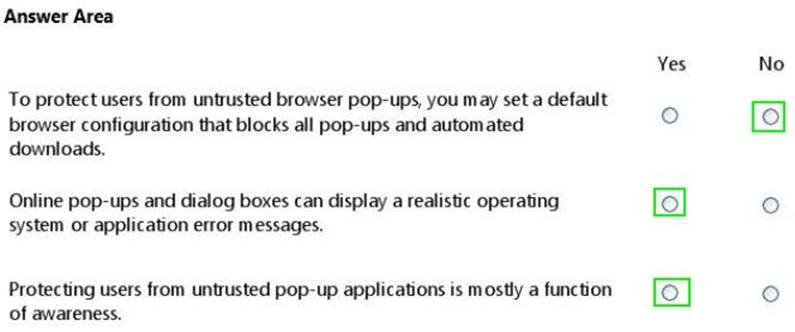
NEW QUESTION 20
Basic security questions used to reset a password are susceptible to:
- A. Hashing
- B. Social engineering
- C. Network sniffing
- D. Trojan horses
Answer: B
Explanation:
Reference: http://en.wikipedia.org/wiki/Self-service_password_reset
NEW QUESTION 21
In Internet Explorer 8, the InPrivate Browsing feature prevents:
- A. Unauthorized private data input.
- B. Unencrypted communication between the client computer and the server.
- C. User credentials from being sent over the Internet.
- D. Any session data from being stored on the computer.
Answer: D
Explanation:
Reference: http://windows.microsoft.com/en-us/windows/what-is-inprivate-browsing
NEW QUESTION 22
Which type of firewall allows for inspection of all characteristics of a packet?
- A. NAT
- B. Stateful
- C. Stateless
- D. Windows Defender
Answer: B
Explanation:
Reference: http://en.wikipedia.org/wiki/Stateful_firewall
NEW QUESTION 23
The company that you work for wants to set up a secure network, but they do not have any servers.
Which three security methods require the use of a server? (Choose three.)
- A. 802.1x
- B. WPA2 Personal
- C. WPA2 Enterprise
- D. RADIUS
- E. 802.11ac
Answer: ACD
NEW QUESTION 24
What are two attributes that an email message may contain that should cause a user to question whether the message is a phishing attempt? (Choose two.)
- A. An image contained in the message
- B. Spelling and grammar errors
- C. Threats of losing service
- D. Use of bold and italics
Answer: BC
Explanation:
Reference: http://www.microsoft.com/security/online-privacy/phishing-symptoms.aspx
NEW QUESTION 25
Creating MD5 hash for files is an example of ensuring what?
- A. Confidentiality
- B. Availability
- C. Least privilege
- D. Integrity
Answer: D
Explanation:
The MD5 message-digest algorithm is a widely used cryptographic hash function producing a 128-bit (16-byte) hash value, typically expressed in text format as a 32 digit hexadecimal number. MD5 has been utilized in a wide variety of cryptographic applications, and is also commonly used to verify data integrity.
NEW QUESTION 26
......
Recommend!! Get the Full 98-367 dumps in VCE and PDF From Dumps-hub.com, Welcome to Download: https://www.dumps-hub.com/98-367-dumps.html (New 163 Q&As Version)