Approved 70-744 Testing Software 2021
Master the 70-744 Securing Windows Server 2021 content and be ready for exam day success quickly with this Examcollection 70-744 brain dumps. We guarantee it!We make it a reality and give you real 70-744 questions in our Microsoft 70-744 braindumps.Latest 100% VALID Microsoft 70-744 Exam Questions Dumps at below page. You can use our Microsoft 70-744 braindumps and pass your exam.
Check 70-744 free dumps before getting the full version:
NEW QUESTION 1
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2021.
You have an organizational unit (OU) named Administration that contains the computer account of Server1.
You import the Active Directory module to Server1.
You create a Group Policy object (GPO) named GPO1. You link GPO1 to the Administration OU. You need to log an event each time an Active Directory cmdlet executed successfully from Server1. What should you do?
- A. From Advanced Audit Policy in GPO1. configure auditing for other privilege use events.
- B. Run the Add-NetEventProvider -Name “Microsoft-Active-Directory” -MatchAnyKeyword PowerShell command.
- C. From Advanced Audit Policy in GPO1, configure auditing for directory service changes.
- D. From Administrative Templates in GPO1, configure a Windows PowerShell polic
Answer: D
Explanation:
In the following GPO location, you can enable the setting “Turn on Module Logging” to record an
event each
time the PowerShell executes a cmdlet of a specific PowerShell module, for example “ActiveDirectory”.
“Computer Configuration\Administrative Templates\Windows Components\Windows PowerShell”
NEW QUESTION 2
You have the servers configured as shown in the following table.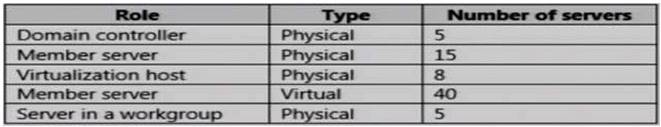
You purchase a Microsoft Azure subscription, and you create three Microsoft Operations
Management Suite (OMS) workspaces named Workspace1, Workspace2, and Workspace3
You need to deploy Microsoft Monitoring Agent to the servers to meet the following requirements:
-Antimalware data from all the servers must be visible in Workspace1.
-Security and audit data from the domain controllers and the virtualization hosts must be visible in Workspace2.
-System update data from all the servers in all the workgroups must be visible in Workspace& How many OMS agents should you deploy?
- A. 10
- B. 33
- C. 73
- D. 45
Answer: C
Explanation:
-Antimalware data from all the servers must be visible in Workspace1.
-Security and audit data from the domain controllers and the virtualization hosts must be visible in Workspace2.
-System update data from all the servers in all the workgroups must be visible in Workspace& “All the servers” mean all 5 domain controllers, plus all member servers (physical and virtual, domain and
workgroup) and virtualization hosts, so there are no exemptions.
All servers in the above table mentioned must install OMS Microsoft Monitoring agents
NEW QUESTION 3
Note: This question Is part of a series of questions that use the same or similar answer choices. An answer choice may be correct for more than one question in the series. Each question is Independent of the other questions in this series. Information and details provided in a question apply only to that question.
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2021.
Server1 has a shared folder named Share1. You need to encrypt the contents of Share1. Which tool should you use?
- A. File Explorer
- B. Shared Folders
- C. Server Manager
- D. Disk Management
- E. Storage Explorer
- F. Computer Management
- G. System Configuration
- H. File Server Resource Manager (FSRM)
Answer: A
NEW QUESTION 4
Your network contains an Active Directory domain named contoso.com. The domain contains a computer named Computer1 that runs Windows 10. Computer1 connects to a home network and a corporate network.
The corporate network uses the 172.16.0.0/24 address space internally. Computer1 runs an application named App1 that listens to port 8080.
You need to prevent connections to App1 when Computer1 is connected to the home network. Solution: From Windows Firewall with Advanced Security, you create an inbound rule. Does this meet the goal?
- A. Yes
- B. No
Answer: A
NEW QUESTION 5
The Job Title attribute for a domain user named User1 has a value of Sales Manager. User1 runs whoami /claims and receives the following output: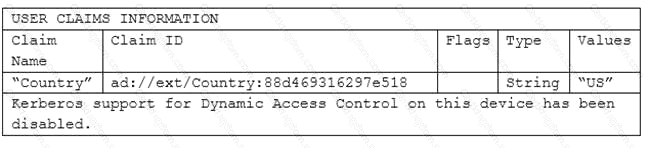
Kerberos support for Dynamic Access Control on this device has been disabled.
You need to ensure that the security token of User1 has a claim for Job Title. What should you do?
- A. From Windows PowerShell, run the New-ADClaimTransformPolicy cmdlet and specify the -Name parameter
- B. From Active Directory Users and Computers, modify the properties of the User1 account.
- C. From Active Directory Administrative Center, add a claim type.
- D. From a Group Policy object (GPO), configure KDC support for claims, compound authentication, and Kerberos armoring.
Answer: C
Explanation:
From the output, obviously, a claim type is missing (or disabled) so that the domain controller is not issuing
tickets with the “Job Title” claim type.
NEW QUESTION 6
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1.
Server1 is configured as shown in the following table.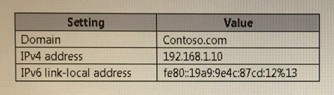
You plan to create a pilot deployment of Microsoft Advanced Threat Analytics (ATA). You need to install the ATA Center on Server1.
What should you do first?
- A. Install Microsoft Security Compliance Manager (SCM).
- B. Obtain an SSL certificate.
- C. Assign an additional IPv4 address.
- D. Remove Server1 from the domai
Answer: B
Explanation:
https://docs.microsoft.com/en-us/advanced-threat-analytics/ata-prerequisites
ATA Center which is the first component to be deployed on Server1, requires the use of SSL protocol to
communicate with ATA Gateway
To ease the installation of ATA, you can install self-signed certificates during installation.
Post deployment you should replace the self-signed with a certificate from an internal Certification Authority tobe used by the ATA Center.
Make sure the ATA Center and ATA Gateways have access to your CRL distribution point.
If the they don’t have Internet access, follow the procedure to manually import a CRL, taking care to install the all the CRL distribution points for the whole chain.
NEW QUESTION 7
Your network contains an Active Directory domain named contoio.com. The domain contains a server named Server1 that runs Windows Server 2021.
You have an organizational unit (OU) named Administration that contains the computer account of Server1.
You import the Active Directory module to Served1.
You create a Group Policy object (GPO) named GPO1 You link GPO1 to the Administration OU. You need to log an event each time an Active Directory cmdlet is executed successfully from Server1. What should you do?
- A. From Advanced Audit Policy in GPO1 configure auditing for directory service changes.
- B. Run the (Get-Module ActiveDirectory).LogPipelineExecutionDetails - $false command.
- C. Run the (Get-Module ArtiveDirectory).LogPipelineExecutionDetails = $true command.
- D. From Advanced Audit Policy in GPO1 configure auditing for other privilege use event
Answer: C
NEW QUESTION 8
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2021. You need to prevent NTLM authentication on Server1.
Solution: From Windows PowerShell, you run the New-ADAuthenticationPolicy cmdlet. Does this meet the goal?
- A. Yes
- B. No
Answer: B
Explanation:
ADDS Authentication Policy does not provide ability to prevent the use of NTLM authentication.
NEW QUESTION 9
Your network contains an Active Directory domain named contoso.com. The domain contains 100 servers.
You deploy the Local Administrator Password Solution (LAPS) to the network You need to view the password of the local administrator of a server named Server5. Which tool should you use?
- A. Active Directory Users and Computers
- B. Computer Management
- C. Accounts from the Settings app
- D. Server Manager
Answer: A
Explanation:
Use “Active Directory Users and Computers” to view the attribute value of “ms-MCS-adminpwd” of the Server5 computer account
https://blogs.technet.microsoft.com/askpfeplat/2015/12/28/local-administrator-password-solutionlapsimplementation- hints-and-security-nerd-commentaryincludingmini-threat-model/
NEW QUESTION 10
You have a server named Server1 that runs Windows Server 2021. You configure Just Enough Administration (JEA) on Server1.
You need to view a list of commands that will be available to a user named User1 when User1 establishes a JEA session to Server1.
Which cmdlet should you use?
- A. Trace-Command
- B. Get-PSSessionCapability
- C. Get-PSSessionConfiguration
- D. Show-Command
Answer: B
Explanation:
https://docs.microsoft.com/en-us/powershell/module/Microsoft.PowerShell.Core/getpssessioncapability? view=powershell-5.0.
The Get-PSSessionCapability cmdlet gets the capabilities of a specific user on a constrained session configuration.
Use this cmdlet to audit customized session configurations for users.
Starting in Windows PowerShell 5.0, you can use the RoleDefinitions property in a session configuration (.pssc) file.
Using this property lets you grant users different capabilities on a single constrained endpoint based on groupmembership.
The Get-PSSessionCapability cmdlet reduces complexity when auditing these endpoints by letting you
determine the exact capabilities granted to a user.
This command is used by I.T. Administrator (The “You” mention in the question) to verify configuration for a
User.
NEW QUESTION 11
Your network contains an Active Directory forest named contoso.com. The forest functional level is Windows Server 2012.
The forest contains 20 member servers that are configured as file servers. All domain controllers run Windows Server 2021.
You create a new forest named contosoadmin.com.
You need to use the Enhanced Security Administrative Environment (ESAE) approach for the administration of the resources in contoso.com.
Which two actions should you perform? Each correct answer presents part of the solution.
- A. From the properties of the trust, enable selective authentication.
- B. Configure contosoadmin.com to trust contoso.com.
- C. Configure contoso.com to trust contosoadmin.com.
- D. From the properties of the trust, enable forest-wide authentication.
- E. Configure a two-way trust between both forest
Answer: AC
Explanation:
https://docs.microsoft.com/en-us/windows-server/identity/securing-privileged-access/securingprivilegedaccess- reference-material#ESAE_BM
Trust configurations – Configure trust from managed forests(s) or domain(s) to the administrative forest
A one-way trust is required from production environment to the admin forest. This can be a domain trust or a forest trust.
The admin forest/domain (contosoadmin.com) does not need to trust the managed domains/forests (contoso.com) to manage Active Directory, though additional applications may require a two-way trust relationship, security validation, and testing.
Selective authentication should be used to restrict accounts in the admin forest to only logging on to the
appropriate production hosts.
NEW QUESTION 12
Note: This question Is part of a series of questions that use the same or similar answer choices. An answer choice may be correct for more than one question in the series. Each question is independent of the other questions in this series. Information and details provided in a question apply only to that question.
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2021.
Server1 has a volume named Volume1.
A central access policy named Policy1 is deployed to the domain. You need to apply Policy1 to Volume1.
Which tool should you use?
- A. File Explorer
- B. Shared Folders
- C. Server Manager
- D. Disk Management
- E. Storage Explorer
- F. Computer Management
- G. System Configuration
- H. File Server Resource Manager (FSRM)
Answer: A
Explanation:
“File Explorer” = “Windows Explorer”.
https://docs.microsoft.com/en-us/windows-server/identity/solution-guides/deploy-a-centralaccess- policy–
demonstration-steps-#BKMK_1.4
NEW QUESTION 13
Your network contains an Active Directory forest named contoso.com. The forest functional level is Windows Server 2012. All servers run Windows Server 2021.
You create a new bastion forest named admin.contoso.com. The forest functional level of admin.contoso.com is Windows Server 2012 R2.
You need to implement a Privileged Access Management (PAM) solution.
Which two actions should you perform? Each correct answer presents part of the solution.
- A. Raise the forest functional level of admm.contoso.com.
- B. Deploy Microsoft Identify Management (MIM) 2021 to admin.contoso.com.
- C. Configure contoso.com to trust admin.contoso.com.
- D. Deploy Microsoft Identity Management (MIM) 2021 to contoso.com.
- E. Raise the forest functional level of contoso.com.
- F. Configure admin.contoso.com to trust contoso.co
Answer: DE
Explanation:
https://docs.microsoft.com/en-us/microsoft-identity-manager/pam/deploy-pam-with-windowsserver- 2021
https://docs.microsoft.com/en-us/windows-server/identity/ad-ds/windows-server-2021-functionallevels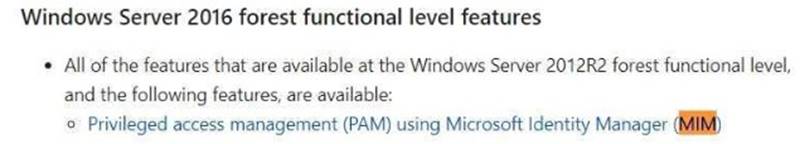
For the bastion forest which deploys MIM, you should raise the Forest Functional Level to “Windows Server
2021?
NEW QUESTION 14
Your network contains an Active Directory domain named contoso.com. The domain contains a DNS server named Server1 that runs Windows Server 2021.
A domain-based Group Policy object (GPO) is used to configure the security policy of Server1.
You plan to use Security Compliance Manager (SCM) 4.0 to compare the security policy of Server1 to the WS2012 DNS Server Security 1.0 baseline.
You need to import the security policy into SCM. What should you do first?
- A. From Security Configuration and Analysis, use the Export Template option.
- B. Run the Copy-GPO cmdlet and specify the -TargetName parameter.
- C. Run the Backup-GPO cmdlet and specify the -Path parameter.
- D. Run the secedit.exe command and specify the/export paramete
Answer: C
Explanation:
https://technet.microsoft.com/en-us/library/ee461052.aspx
Backup-GPO cmdlet and specify the -Path parameter creates a GPO backup folder with GUID name and is
suitable to import to SCM 4.0
NEW QUESTION 15
Your network contains an Active Directory domain named contoso.com. The domain contains several shielded virtual machines.
You deploy a new server named Server1 that runs Windows Server 2021. You install the Hyper-V server role on Server1.
You need to ensure that you can host shielded virtual machines on Server1. What should you install on Server1?
- A. Host Guardian Hyper-V Support
- B. BitLocker Network Unlock
- C. the Windows Biometric Framework (WBF)
- D. VM Shielding Tools for Fabric Management
Answer: A
Explanation:
This questions mentions “The domain contains several shielded virtual machines.”, which indicates a working Host Guardian Service deployment was completed.
https://docs.microsoft.com/en-us/windows-server/virtualization/guarded-fabric-shieldedvm/guarded-fabricguarded-host-prerequisites
For a new Hyper-V server to utilize an existing Host Guardian Service, install the “Host Guardian Hyper-V
Support”.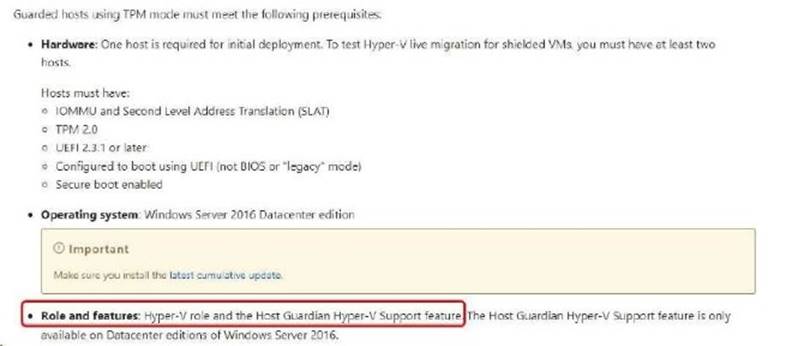
NEW QUESTION 16
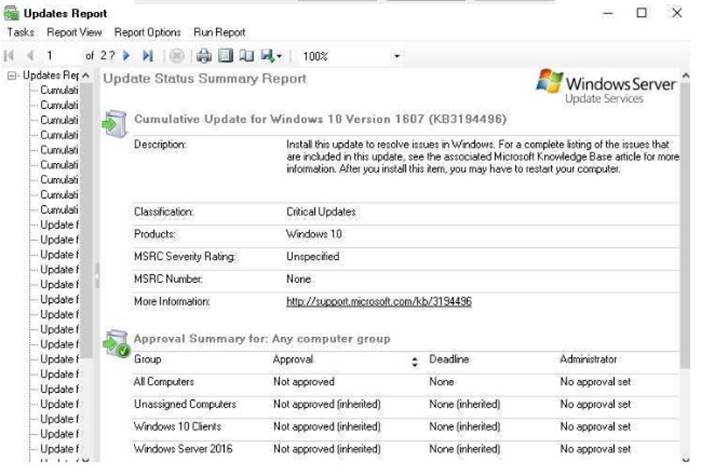
Your network contains an Active Directory domain named contoso.com.The domain contains 1,000 client computers that run either Windows 8.1 or Windows 10.
You have a Windows Server Update Services (WSUS) deployment All client computers receive updates from WSUS.
You deploy a new WSUS server named WSUS2.
You need to configure all of the client computers that run Windows 10 to send WSUS reporting data to WSUS2.
What should you configure?
- A. an approval rule
- B. a computer group
- C. a Group Policy object (GPO)
- D. a synchronization rule
Answer: C
Explanation:
https://technet.microsoft.com/en-us/library/cc708574(v=ws.10).aspx
Under “Set the intranet update service for detecting updates”, type http://wsus:8530 Under “Set the intranet statistics server”, type http://wsus2:8531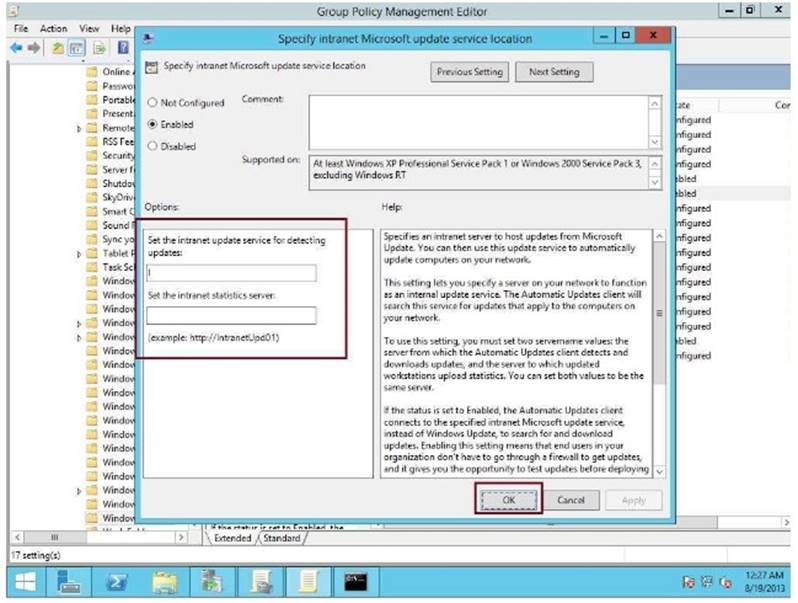
NEW QUESTION 17
Your network contains an Active Directory domain named contoso.com. All servers run Windows Server 2021.
You need to prevent direct .NET scripts invoked by interactive Windows PowerShell sessions from running on the servers.
What should you do for each server?
- A. Create an AppLocker rule.
- B. Create a Code Integrity rule.
- C. Disable PowerShell Remoting.
- D. Modify the local Kerberos policy setting
Answer: C
NEW QUESTION 18
You have a server named Server1 that runs Windows Server 2021.
You need to identity whether any connection security rules are configured on Server1. Which cmdlet should you use?
- A. Get-NetIPSecRule
- B. Get-NetFirewallRule C.Get-NetFirewallProfile
- C. Get-NetFirewallSetting
- D. Get-NetFirewallPortFilter
- E. Get-NetFirewallAddressFilter
- F. Get-NetFirewallSecurityFilter
- G. Get-NetFirewallApplicationFilter
Answer: A
Explanation:
https://technet.microsoft.com/en-us/itpro/powershell/windows/netsecurity/get-netipsecrule
Get-NetIPSecRule displays the existence and details of Connection Security Rules, as connection
security rules implements IPsec between computers (not using tunnel endpoints) or sites (using tunnel endpoints)
NEW QUESTION 19
Your network contains an Active Directory domain named contoso.com. The functional level of the forest and the domain is Windows Server 2008 R2. The domain contains the servers configured as shown in the following table.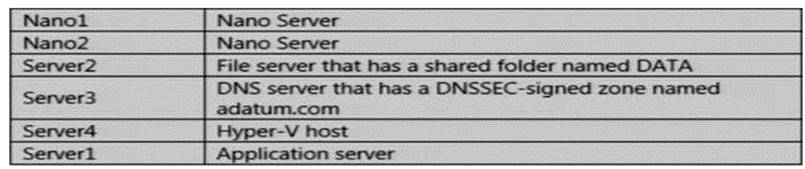
You have an organizational unit (OU) named Marketing that contains the computers in the marketing department.
You have an OU named Finance that contains the computers in the finance department. You have an OU named AppServers that contains application servers.
A Group Policy object (GPO) named GP1 is linked to the Marketing OU. A GPO named GP2 is linked to the
AppServers OU.
You install Windows Defender on Nano1.
You need to configure Nano1 as a Hyper-V Host. Which command should you run?
- A. Add-WindowsFeature Microsoft-NanoServer-Compute-Package
- B. Add-WindowsFeature Microsoft-NanoServer-Guest-Package
- C. Add-WindowsFeature Microsoft-NanoServer-Host-Package
- D. Add-WindowsFeature Microsoft-NanoServer-ShieldedVM-Package
- E. Install-Package Microsoft-NanoServer-Compute-Package
- F. Install-Package Microsoft-NanoServer-Guest-Package
- G. Install-Package Microsoft-NanoServer-Host-Package
- H. Install-Package Microsoft-NanoServer-ShieldedVM-Package
- I. Install-WindowsFeature Microsoft-NanoServer-Compute-Package
- J. Install-WindowsFeatureMicrosoft-NanoServer-Guest-Package
- K. Install-WindowsFeatureMicrosoft-NanoServer-Host-Package
- L. Install-WindowsFeature Microsoft-NanoServer-ShieldedVM-Package
Answer: E
Explanation:
https://docs.microsoft.com/en-us/windows-server/get-started/deploy-nano-server#BKMK_online The Nano Server package “Microsoft-NanoServer-Compute-Package” includes the Hyper-V role for a Nano
Server host.
Moreover, the Install-WindowsFeature or Add-WindowsFeature cmdlet are NOT available on a Nano Server.
NEW QUESTION 20
HOTSPOT
Your network contains an Active Directory forest named contoso.com. The forest has Microsoft Identity Manager (MIM) 2021 deployed. You implement Privileged Access Management (PAM).
You need to request privileged access from a client computer in contoso.com by using PAM.
How should you complete the Windows PowerShell script? To answer, select the appropriate options in the answer area.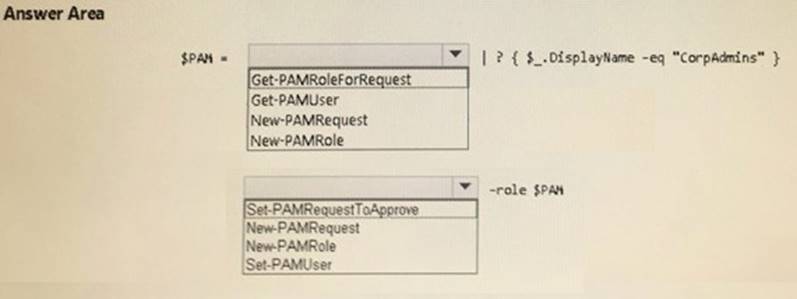
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
$PAM = Get-PAMRoleForRequest | ? {$_,DisplayName -eq “CorpAdmins” } New-PAMRequest -role $PAM
References:
https://technet.microsoft.com/en-us/library/mt604089.aspx https://technet.microsoft.com/en-us/library/mt604084.aspx
NEW QUESTION 21
The New-CIPolicy cmdlet creates a Code Integrity policy as an .xml file. If you do NOT supply either driver files or rules what will happen?
- A. The cmdlet performs a system scan
- B. An exception/warning is shown because either one is required
- C. Nothing
- D. The cmdlet searches the Code Integrity Audit log for drivers
Answer: A
Explanation:
If you do not supply either driver files or rules, this cmdlet performs a system scan similar to the Get- SystemDriver cmdlet.
The cmdlet generates rules based on Level. If you specify the Audit parameter, this cmdlet scans the Code Integrity Audit log instead.
NEW QUESTION 22
Your network contains an Active Directory domain named contoso.com.
You install the Windows Server Update Services server role on a member server named Server1. Server1 runs Windows Server 2021.
You need to ensure that a user named Used can perform the following tasks:
*View the Windows Server Update Services (WSUS) configuration.
*Generate WSUS update reports.
The solution must use the principle of least privilege. What should you do on Server1?
- A. Modify the permissions of the ReportWebService virtual folder from the WSUS Administration website.
- B. Add User1 to the WSUS Reporters local group.
- C. Add User1 to the WSUS Administrators local group.
- D. Run wsusutil.exe and specify the postinstall paramete
Answer: B
Explanation:
WSUS Reporters have read only access to the WSUS database and configuration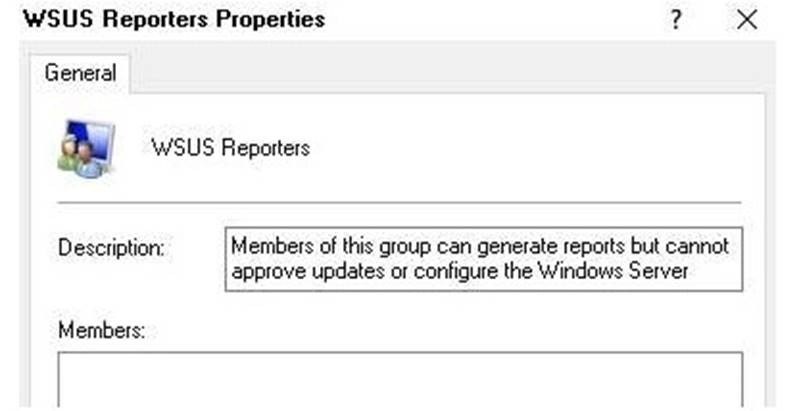
When a user with “WSUS Reporters” membership, he can view configuration and generate reports as follow:-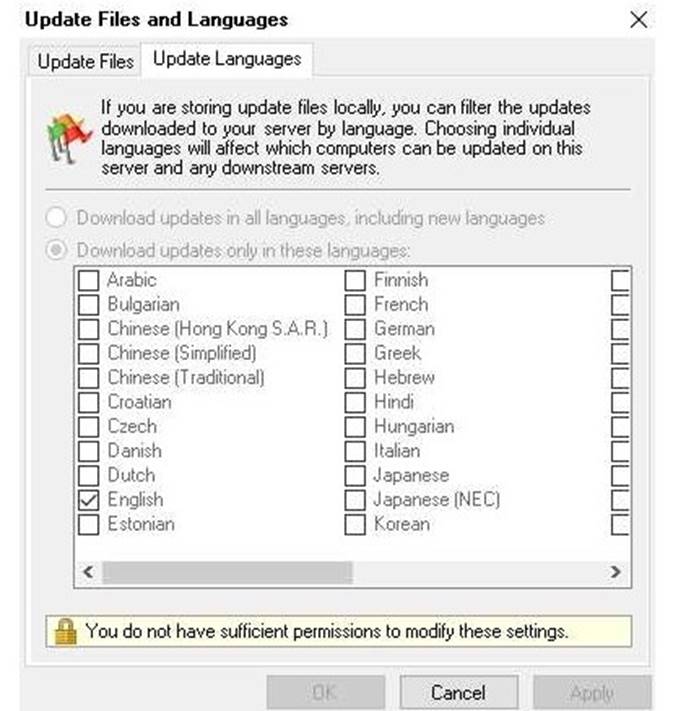
NEW QUESTION 23
Note: This question It part of a series of questions that present the same scenario. Each question In the series contains a unique solution that might meet the stated goats. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to It. As a result, these questions will not appear in the review screen.
Your network contains an Active Directory domain named contoso.com. The domain contains a computer named Computer1 that runs Windows 10. Computer1 connects to a home network and a corporate network.
The corporate network uses the 17216.0.0/24 address space internally. Computer1 runs an application named App1 that listens to port 8080.
You need to prevent connections to App1 when Computer1 is connected to the home network. Solution: From Group Policy Management you create a software restriction policy.
Does this meet the goal?
- A. Yes
- B. No
Answer: B
Explanation:
Software Restriction Policy does not filter incoming network traffic, what you actually need is Windows Firewall Inbound Rule on the Private profile
References:
https://technet.microsoft.com/en-us/library/hh831534(v=ws.11).aspx
NEW QUESTION 24
The “Network Security: Restrict NTLM: NTLM authentication in this domain” policy setting allows you to deny or allow NTLM authentication within a domain from this domain controller.
Which value would you choose so that the domain controller will deny all NTLM authentication logon attempts using accounts from this domain to all servers in the domain.
The NTLM authentication attempts will be blocked and will return an NTLM blocked error unless the server name is on the exception list in the Network security: Restrict NTLM: Add server exceptions in this domain policy setting.
- A. Deny for domain accounts
- B. Deny for domain accounts to domain servers
- C. Deny all
- D. Deny for domain servers
Answer: B
NEW QUESTION 25
......
Recommend!! Get the Full 70-744 dumps in VCE and PDF From Surepassexam, Welcome to Download: https://www.surepassexam.com/70-744-exam-dumps.html (New 221 Q&As Version)