Microsoft 70-414 Free Practice Questions 2021
for Microsoft certification, Real Success Guaranteed with Updated . 100% PASS 70-414 Implementing an Advanced Server Infrastructure exam Today!
Free 70-414 Demo Online For Microsoft Certifitcation:
NEW QUESTION 1
Your network contains an Active Directory domain named contoso.com. All servers run Windows Server 2012 R2. The network contains a System Center 2012 R2 Data Protection Manager (DPM) deployment.
The domain contains six servers. The servers are configured as shown in the following table.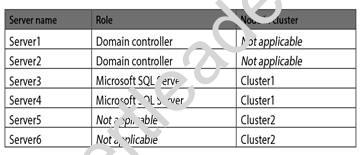
You install System Center 2012 R2 Virtual Machine Manager (VMM) on the nodes in Cluster2. You configure VMM to use a database in Cluster1. Server5 is the first node in the cluster.
You need to back up the VMM encryption key. What should you back up?
- A. a system state backup of Server2
- B. a full system backup of Server6
- C. a system state backup of Server5
- D. a full system backup of Server3
Answer: A
Explanation: Encryption keys in Active Directory Domain Services: If distributed key management (DKM) is configured, then you are storing VMM-related encryption keys in Active Directory Domain Services (AD DS). To back up these keys, back up Active Directory on a regular basis.
NEW QUESTION 2
You have a server named Host1 that runs Windows Server 2012 and has the Hyper-V server role installed. Host1 has one physical network adapter. You plan to deploy 15 virtual machines on Host1.
You need to implement a networking solution that ensures that all of the virtual machines use PXE to boot when they connect to Windows Deployment Server (WDS).
What should you do?
- A. Install legacy network adapters for each virtual machine.
- B. Modify the settings of the virtual switch.
- C. Modify the settings of the network adapter for each virtual machine.
- D. Install a second physical network adapter.
Answer: A
Explanation: Since Windows Server 2012 R2 (WS2012 R2) Hyper-V and Windows 8.1 Client Hyper-V, there are two generations of virtual machine hardware specification. Generation 1 virtual machines (the only generation on legacy versions of Hyper-V) make things a little tricky when it comes to PXE booting. The default (and better performing) synthetic Network Adapter (that leverages the Hyper-V integration components) does not support booting off of the network in Generation 1 virtual machines. If you do want to boot this type of virtual hardware using PXE then you must add an emulated Legacy Network Adapter.
NEW QUESTION 3
Your network contains five servers that run Windows Server 2012 R2.
You install the Hyper-V server role on the servers. You create an external virtual network switch on each server.
You plan to deploy five virtual machines to each Hyper-V server. Each virtual machine will have a virtual network adapter that is connected to the external virtual network switch and that has a VLAN identifier of 1.
Each virtual machine will run Windows Server 2012 R2. All of the virtual machines will run the identical web application.
You plan to install the Network Load Balancing (NLB) feature on each virtual machine and join each virtual machine to an NLB cluster. The cluster will be configured to use unicast only.
You need to ensure that the NLB feature can distribute connections across all of the virtual machines. Solution: On each Hyper-V server, you create a new external virtual network switch. From the properties of
each virtual machine, you add a second virtual network adapter and connect the new virtual network adapters
to the new external virtual network switches.
Does this meet the goal?
- A. Yes
- B. No
Answer: B
NEW QUESTION 4
You install the Service Manager Self-Service Portal on a server named CONTOSOSSP1.
Users report that they receive access denied messages when they try to connect to the portal. You must grant users the minimum required permissions.
You need to ensure that all users in the Contoso domain can access the Service Manager Self-Service Portal.
What should you do?
- A. In Active Directory, create a new group named PortalUser
- B. Add the PortalUsers group to the ContosoDomain Users group, and then add the group to the local users group on CONTOSOSSP1.
- C. Using the account that you used to install the Self-Service portal, grant the ContosoDomain Users group Read permissions to the portal.
- D. In Service Manager, create a new user role named PortalUser
- E. Grant the PortalUsers role rights to all catalog items, and then add the ContosoDomain Users Active Directory Domain Services group to the PortalUsers role.
- F. Using the account that you used to install the Self-Serviceportal, grant the ContosoDomain Users group Contribute permissions to the portal.
Answer: D
NEW QUESTION 5
Your network contains an Active Directory domain named contoso.com. The domain contains several domain controllers. The domain controllers run either Windows Server 2012 or Windows Server 2008 R2.
The domain functional level is Windows Server 2008 R2. The forest functional level is Windows Server 2008. The corporate compliance policy states that all items deleted from Active Directory must be recoverable from a Recycle Bin.
You need to recommend changes to the current environment to meet the compliance policy.
Which changes should you recommend? (Each correct answer presents part of the solution. Choose all that apply.)
- A. Run the Set-ADForestMode cmdlet.
- B. Run the New-ADObject cmdlet.
- C. Run the Set-ADObject cmdlet.
- D. Run the Set-ADDomainMode cmdlet.
- E. Run the Enable-ADOptionalFeature cmdlet.
Answer: AE
Explanation: A: You can enable Active Directory Recycle Bin only if the forest functional level of your environment is set to Windows Server 2008 R2.
The Set-ADForestMode cmdlet sets the Forest mode for an Active Directory forest. You specify the forest mode by setting the ForestMode parameter. Here we should set it to Windows2008R2Forest.
E: Enabling Active Directory Recycle Bin
After the forest functional level of your environment is set to Windows Server 2008 R2, you can enable Active Directory Recycle Bin by using the following methods:
/ Enable-ADOptionalFeature Active Directory module cmdlet (This is the recommended method.)
/ Ldp.exe
NEW QUESTION 6
Your network contains a main data center and a disaster recovery data center. Each data center contains a Storage Area Network (SAN). The main data center contains a two-node failover cluster named Cluster1 that hosts a Microsoft SQL Server 2012 database named DB1.
The database files in DB1 are stored on the SAN in the main office. The disaster recovery data center contains a server that runs SQL Server 2012.
You need to recommend a disaster recovery solution for the SQL Server database. The solution must ensure that the database remains available if the main data center fails.
What should you recommend? More than one answer choice may achieve the goal. Select the BEST answer.
- A. Deploy Distributed File System (DFS) Replication.
- B. Extend the failover cluster to the disaster recovery data center.
- C. Implement a Cluster Shared Volume (CSV) and move the database files to the CSV.
- D. Implement SQL Server database replication between the two data centers.
Answer: D
Explanation: 
NEW QUESTION 7
You have a Hyper-V host named Server1 that runs Windows Server 2012 R2. Server1 hosts 50 virtual machines that run Windows Server 2012 R2.
Your company uses smart cards for authentication. You need to ensure that you can use smart card authentication when you connect to the virtual machine by using Virtual Machine Connection.
What should you configure?
- A. The NUMA Spanning settings
- B. The RemoteFX settings
- C. The Enhanced Session Mode Policy
- D. The Integration Services settings
Answer: C
NEW QUESTION 8
You have a small Hyper-V cluster built on two hosts that run Windows Server 2012 R2 Hyper-V. You manage the virtual infrastructure by using System Center Virtual Machine Manager 2012.
Distributed Key Management is not installed. You have the following servers in the environment: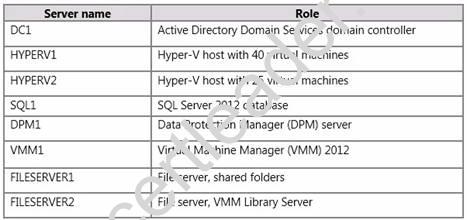
You have the following requirements:
You must back up virtual machines at the host level.
You must be able to back up virtual machines that are configured for live migration.
You must be able to restore the entire VMM infrastructure.
You need to design and implement the backup plan. What should you do?
- A. Run the following Windows PowerShell command:Get-VM VMM1 | Checkpoint-VM-SnapshotName “VMM backup”
- B. Run the following Windows PowerShell command:Set-DPMGlobalProperty-DPMServerName DPM1-KnownVMMServers VMM1
- C. Configure System State Backup for DCL.
- D. Configure backup for all disk volumes on FILESERVER1
Answer: B
Explanation: DPM can protect Hyper-V virtual machines V during live migration.
Connect servers—Run the the Set-DPMGlobalProperty PowerShell command to connect all the servers that are running Hyper-V to all the DPM servers. The cmdlet accepts multiple DPM server names.
Set-DPMGlobalProperty -dpmservername <dpmservername> -knownvmmservers <vmmservername>
NEW QUESTION 9
You plan to implement 20 highly available virtual machines on FC1, All of the virtual machines must be stored in a single shared folder You need to ensure that the VHD Files of the virtual machines can be stored on SAN1, VHD files must be available from any node in FC2.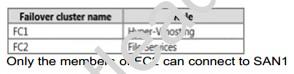
What should you do on FC2 ?
- A. Configure the clustered File server role o( the filer server tor general use.
- B. Add the iSCSI target server cluster role.
- C. Configure the clustered file server role of the scale-out file server for application data.
- D. Add the storage services role service.
Answer: BC
NEW QUESTION 10
You plan to allow users to run internal applications from outside the company’s network. You have a Windows Server 2012 R2 that has the Active Directory Federation Services (AD FS) role installed. You must secure on-premises resources by using multi-factor authentication (MFA). You need to design a solution to enforce different access levels for users with personal Windows 8.1 or iOS 8 devices.
Solution: You install a local instance of the MFA Server. You connect the instance to the Microsoft Azure MFA provider and then you use Microsoft Intune to manage personal devices.
Does this meet the goal?
- A. Yes
- B. No
Answer: A
NEW QUESTION 11
Your network contains an Active Directory domain named contoso.com. The domain contains multiple servers that are configured as Hyper-V hosts.
You plan to implement four virtual machines. The virtual machines will be configured as shown in the following table.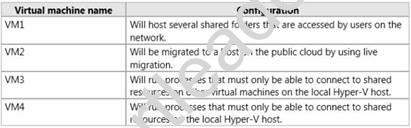
You need to identify which network must be added to each virtual machine. Which network types should you identify?
To answer, drag the appropriate Network Type to the correct virtual machine in the answer area. Each Network Type may be used once, more than once, or not at all. Additionally, you may need to drag the split bar between panes or scroll to view content.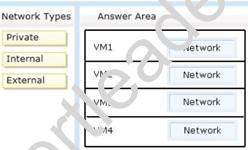
Answer:
Explanation: http://blogs.technet.com/b/jhoward/archive/2008/06/17/hyper-v-what-are-the-uses-for-different-types-of-virtual-ks.aspx
An external network, which provides communication between a virtual machine and a physical network by creating an association to a physical network adapter on the virtualization server.
An internal network, which provides communication between the virtualization server and virtual machines. A private network, which provides communication between virtual machines only.
NEW QUESTION 12
Your network contains an Active Directory domain named contoso.com. All servers run Windows Server 2012 R2. The network contains a System Center 2012 R2 Data Protection Manager (DPM) deployment.
The domain contains six servers. The servers are configured as shown in the following table.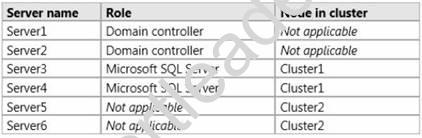
You install System Center 2012 R2 Virtual Machine Manager (VMM) on the nodes in Cluster2. You configure VMM to use a database in Cluster1. Server5 is the first node in the cluster.
You need to back up the VMM encryption key. What should you back up?
- A. A full system backup of Server1
- B. A full system backup of Server3
- C. A backup of the WindowsDigitalLocker folder on Server5
- D. A backup of the WindowsDigitalLocker folder on Server1
Answer: A
NEW QUESTION 13
You need to recommend which setting must be applied to the virtualization infrastructure of Northwind Traders to minimize the impact of multiple virtual machines starting concurrently.
What command should you recommend running? To answer, select the appropriate options in the answer area.
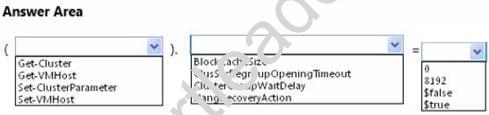
Answer:
Explanation: 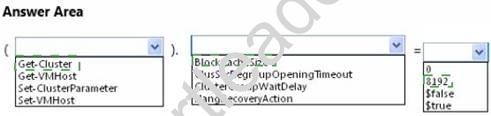
NEW QUESTION 14
You need to design a solution that meets all of the software update requirements.
Which two actions should you perform? Each correct answer presents part of the solution.
- A. Implement System Center Service Manager.
- B. Deploy a configuration baseline to all devices.
- C. Implement System Center Operations Manager.
- D. Implement System Center Configuration Manager.
Answer: BC
NEW QUESTION 15
You plan to allow users to run internal applications from outside the company's network. You have a Windows Server 2012 R2 that has the Active Directory Federation Services (AD FS) role installed. You must secure on-premises resources by using multi-factor authentication (MFA). You need to design a solution to enforce different access levels for users with personal Windows 8.1 or iOS 8 devices.
Solution: You migrate the AD FS server to Microsoft Azure and connect it to the internal Active Directory instance on the network. Then, you use the Workplace Join process to configure access for personal devices to the on-premises resources.
Does this meet the goal?
- A. Yes
- B. No
Answer: A
NEW QUESTION 16
Your company, which is named Contoso, Ltd., has offices only in North America. The company has 2,000 users. The network contains an Active Directory domain named contoso.com.
You plan to deploy an Active Directory Certificate Services (AD CS) infrastructure and assign certificates to all client computers.
You need to recommend a PKI solution to protect the private key of the root certification authority (CA) from being accessed by external users.
What should you recommend? More than one answer choice may achieve the goal. Select the BEST answer.
- A. An offline standalone root CA and an online enterprise issuing CA
- B. An online enterprise root CA and an online enterprise issuing CA
- C. An offline standalone root CA and an offline enterprise issuing CA
- D. An online enterprise root CA, an online enterprise policy CA, and an online enterprise issuing CA
Answer: A
P.S. Easily pass 70-414 Exam with 270 Q&As 2passeasy Dumps & pdf Version, Welcome to Download the Newest 2passeasy 70-414 Dumps: https://www.2passeasy.com/dumps/70-414/ (270 New Questions)