The Secret Of EC-Council 312-50v11 Test Questions
Master the 312-50v11 Certified Ethical Hacker Exam (CEH v11) content and be ready for exam day success quickly with this Pass4sure 312-50v11 exam question. We guarantee it!We make it a reality and give you real 312-50v11 questions in our EC-Council 312-50v11 braindumps.Latest 100% VALID EC-Council 312-50v11 Exam Questions Dumps at below page. You can use our EC-Council 312-50v11 braindumps and pass your exam.
Online EC-Council 312-50v11 free dumps demo Below:
NEW QUESTION 1
Which of the following is the primary objective of a rootkit?
- A. It opens a port to provide an unauthorized service
- B. It creates a buffer overflow
- C. It replaces legitimate programs
- D. It provides an undocumented opening in a program
Answer: C
NEW QUESTION 2
Which address translation scheme would allow a single public IP address to always correspond to a single machine on an internal network, allowing "server publishing"?
- A. Overloading Port Address Translation
- B. Dynamic Port Address Translation
- C. Dynamic Network Address Translation
- D. Static Network Address Translation
Answer: D
NEW QUESTION 3
What does a firewall check to prevent particular ports and applications from getting packets into an organization?
- A. Transport layer port numbers and application layer headers
- B. Presentation layer headers and the session layer port numbers
- C. Network layer headers and the session layer port numbers
- D. Application layer port numbers and the transport layer headers
Answer: A
NEW QUESTION 4
DNS cache snooping is a process of determining if the specified resource address is present in the DNS cache records. It may be useful during the examination of the network to determine what software update resources are used, thus discovering what software is installed.
What command is used to determine if the entry is present in DNS cache?
- A. nslookup -fullrecursive update.antivirus.com
- B. dnsnooping –rt update.antivirus.com
- C. nslookup -norecursive update.antivirus.com
- D. dns --snoop update.antivirus.com
Answer: C
NEW QUESTION 5
CompanyXYZ has asked you to assess the security of their perimeter email gateway. From your office in New York, you craft a specially formatted email message and send it across the Internet to an employee of CompanyXYZ. The employee of CompanyXYZ is aware of your test. Your email message looks like this:
From: jim_miller@companyxyz.com
To: michelle_saunders@companyxyz.com Subject: Test message Date: 4/3/2017 14:37
The employee of CompanyXYZ receives your email message.
This proves that CompanyXYZ’s email gateway doesn’t prevent what?
- A. Email Masquerading
- B. Email Harvesting
- C. Email Phishing
- D. Email Spoofing
Answer: D
NEW QUESTION 6
The Payment Card Industry Data Security Standard (PCI DSS) contains six different categories of control objectives. Each objective contains one or more requirements, which must be followed in order to achieve compliance. Which of the following requirements would best fit under the objective, "Implement strong access control measures"?
- A. Regularly test security systems and processes.
- B. Encrypt transmission of cardholder data across open, public networks.
- C. Assign a unique ID to each person with computer access.
- D. Use and regularly update anti-virus software on all systems commonly affected by malware.
Answer: C
NEW QUESTION 7
A large company intends to use Blackberry for corporate mobile phones and a security analyst is assigned to evaluate the possible threats. The analyst will use the Blackjacking attack method to demonstrate how an attacker could circumvent perimeter defenses and gain access to the Prometric Online Testing – Reports https://ibt1.prometric.com/users/custom/report_queue/rq_str... corporate network. What tool should the analyst use to perform a Blackjacking attack?
- A. Paros Proxy
- B. BBProxy
- C. Blooover
- D. BBCrack
Answer: B
NEW QUESTION 8
A company's policy requires employees to perform file transfers using protocols which encrypt traffic. You suspect some employees are still performing file transfers using unencrypted protocols because the employees do not like changes. You have positioned a network sniffer to capture traffic from the laptops used by employees in the data ingest department. Using Wire shark to examine the captured traffic, which command can be used as a display filter to find unencrypted file transfers?
- A. tcp.port != 21
- B. tcp.port = 23
- C. tcp.port ==21
- D. tcp.port ==21 || tcp.port ==22
Answer: D
NEW QUESTION 9
Yancey is a network security administrator for a large electric company. This company provides power for over 100, 000 people in Las Vegas. Yancey has worked for his company for over 15 years and has become very successful. One day, Yancey comes in to work and finds out that the company will be downsizing and he will be out of a job in two weeks. Yancey is very angry and decides to place logic bombs, viruses, Trojans, and backdoors all over the network to take down the company once he has left. Yancey does not care if his actions land him in jail for 30 or more years, he just wants the company to pay for what they are doing to him.
What would Yancey be considered?
- A. Yancey would be considered a Suicide Hacker
- B. Since he does not care about going to jail, he would be considered a Black Hat
- C. Because Yancey works for the company currently; he would be a White Hat
- D. Yancey is a Hacktivist Hacker since he is standing up to a company that is downsizing
Answer: A
NEW QUESTION 10
What is the minimum number of network connections in a multi homed firewall?
- A. 3
- B. 5
- C. 4
- D. 2
Answer: A
NEW QUESTION 11
Which regulation defines security and privacy controls for Federal information systems and organizations?
- A. HIPAA
- B. EU Safe Harbor
- C. PCI-DSS
- D. NIST-800-53
Answer: D
NEW QUESTION 12
You have successfully comprised a server having an IP address of 10.10.0.5. You would like to enumerate all machines in the same network quickly.
What is the best Nmap command you will use?
- A. nmap -T4 -q 10.10.0.0/24
- B. nmap -T4 -F 10.10.0.0/24
- C. nmap -T4 -r 10.10.1.0/24
- D. nmap -T4 -O 10.10.0.0/24
Answer: B
NEW QUESTION 13
In the field of cryptanalysis, what is meant by a “rubber-hose” attack?
- A. Forcing the targeted keystream through a hardware-accelerated device such as an ASIC.
- B. A backdoor placed into a cryptographic algorithm by its creator.
- C. Extraction of cryptographic secrets through coercion or torture.
- D. Attempting to decrypt ciphertext by making logical assumptions about the contents of the original plaintext.
Answer: C
NEW QUESTION 14
MX record priority increases as the number increases. (True/False.)
- A. True
- B. False
Answer: B
NEW QUESTION 15
You just set up a security system in your network. In what kind of system would you find the following string of characters used as a rule within its configuration? alert tcp any any -> 192.168.100.0/24 21 (msg: ““FTP on the network!””;)
- A. A firewall IPTable
- B. FTP Server rule
- C. A Router IPTable
- D. An Intrusion Detection System
Answer: D
NEW QUESTION 16
Which of the following is the least-likely physical characteristic to be used in biometric control that supports a large company?
- A. Iris patterns
- B. Voice
- C. Height and Weight
- D. Fingerprints
Answer: C
NEW QUESTION 17
Which of the following DoS tools is used to attack target web applications by starvation of available sessions on the web server?
The tool keeps sessions at halt using never-ending POST transmissions and sending an arbitrarily large content-length header value.
- A. My Doom
- B. Astacheldraht
- C. R-U-Dead-Yet?(RUDY)
- D. LOIC
Answer: C
NEW QUESTION 18
The Heartbleed bug was discovered in 2014 and is widely referred to under MITRE’s Common Vulnerabilities and Exposures (CVE) as CVE-2014-0160. This bug affects the OpenSSL implementation of the Transport Layer Security (TLS) protocols defined in RFC6520.
What type of key does this bug leave exposed to the Internet making exploitation of any compromised system very easy?
- A. Public
- B. Private
- C. Shared
- D. Root
Answer: B
NEW QUESTION 19
What is the BEST alternative if you discover that a rootkit has been installed on one of your computers?
- A. Copy the system files from a known good system
- B. Perform a trap and trace
- C. Delete the files and try to determine the source
- D. Reload from a previous backup
- E. Reload from known good media
Answer: E
NEW QUESTION 20
Which of the following tools can be used to perform a zone transfer?
- A. NSLookup
- B. Finger
- C. Dig
- D. Sam Spade
- E. Host
- F. Netcat
- G. Neotrace
Answer: ACDE
NEW QUESTION 21
Bob is going to perform an active session hijack against Brownies Inc. He has found a target that allows session oriented connections (Telnet) and performs the sequence prediction on the target operating system. He manages to find an active session due to the high level of traffic on the network. What is Bob supposed to do next?
- A. Take over the session
- B. Reverse sequence prediction
- C. Guess the sequence numbers
- D. Take one of the parties offline
Answer: C
NEW QUESTION 22
Why should the security analyst disable/remove unnecessary ISAPI filters?
- A. To defend against social engineering attacks
- B. To defend against webserver attacks
- C. To defend against jailbreaking
- D. To defend against wireless attacks
Answer: B
NEW QUESTION 23
You are programming a buffer overflow exploit and you want to create a NOP sled of 200 bytes in the program exploit.c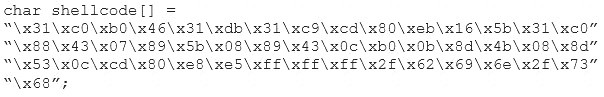
What is the hexadecimal value of NOP instruction?
- A. 0x60
- B. 0x80
- C. 0x70
- D. 0x90
Answer: D
NEW QUESTION 24
A company’s policy requires employees to perform file transfers using protocols which encrypt traffic. You suspect some employees are still performing file transfers using unencrypted protocols because the employees do not like changes. You have positioned a network sniffer to capture traffic from the laptops used by employees in the data ingest department. Using Wireshark to examine the captured traffic, which command can be used as display filter to find unencrypted file transfers?
- A. tcp.port = = 21
- B. tcp.port = 23
- C. tcp.port = = 21 | | tcp.port = =22
- D. tcp.port ! = 21
Answer: A
NEW QUESTION 25
A network administrator discovers several unknown files in the root directory of his Linux FTP server. One of the files is a tarball, two are shell script files, and the third is a binary file is named "nc." The FTP server's access logs show that the anonymous user account logged in to the server, uploaded the files, and extracted the contents of the tarball and ran the script using a function provided by the FTP server's software. The “ps” command shows that the “nc” file is running as process, and the netstat command shows the “nc” process is listening on a network port.
What kind of vulnerability must be present to make this remote attack possible?
- A. File system permissions
- B. Privilege escalation
- C. Directory traversal
- D. Brute force login
Answer: A
NEW QUESTION 26
......
Recommend!! Get the Full 312-50v11 dumps in VCE and PDF From Thedumpscentre.com, Welcome to Download: https://www.thedumpscentre.com/312-50v11-dumps/ (New 254 Q&As Version)