Cisco 210-260 Discount Pack 2021
Actualtests 210-260 Questions are updated and all 210-260 answers are verified by experts. Once you have completely prepared with our 210-260 exam prep kits you will be ready for the real 210-260 exam without a problem. We have Abreast of the times Cisco 210-260 dumps study guide. PASSED 210-260 First attempt! Here What I Did.
Check 210-260 free dumps before getting the full version:
NEW QUESTION 1
How can you stop reconnaissance attack with cdp.
- A. disable CDP on ports connected to end points (or Disable CPD on edfe ports)
- B. enable dot1x on all ports that are connected to other switches
- C. disable CDP on trunk ports
- D. enable dynamic ARP inspection on all untrusted ports
Answer: A
NEW QUESTION 2
Which two commands are used to implement Cisco IOS Resilient Configuration? (Choose two.)
- A. secure boot-image
- B. copy running-config startup-config
- C. secure boot-config
- D. copy flash:/ios.bin tftp
- E. copy running-config tftp
Answer: AC
Explanation:
The Cisco IOS Resilient Configuration feature enables a router to secure and maintain a working copy of the running image and configuration so that those files can withstand malicious attempts to erase the contents of persistent storage (NVRAM and flash).
In 12.3(8)T this feature was introduced.
The following commands were introduced or modified: secure boot-config, secure boot-image, showsecure bootset.
https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_usr_cfg/configuration/15-mt/sec-usr-cfg-15-mt-book/sec
NEW QUESTION 3
Which two ESA services are available for incoming and outgoing mails? (Choose two.)
- A. DLP
- B. reputation filter
- C. content filter
- D. anti-Dos
- E. antispam
Answer: CE
NEW QUESTION 4
Which two primary security concerns can you mitigate with a BYOD solution? (Choose two)
- A. Schedule for patching the device
- B. compliance with applicable policies
- C. device lagging and inventory
- D. Connections to public Wi-Fi networks
- E. Securing access to a trusted corporate network.
Answer: BE
NEW QUESTION 5
Refer to the exhibit.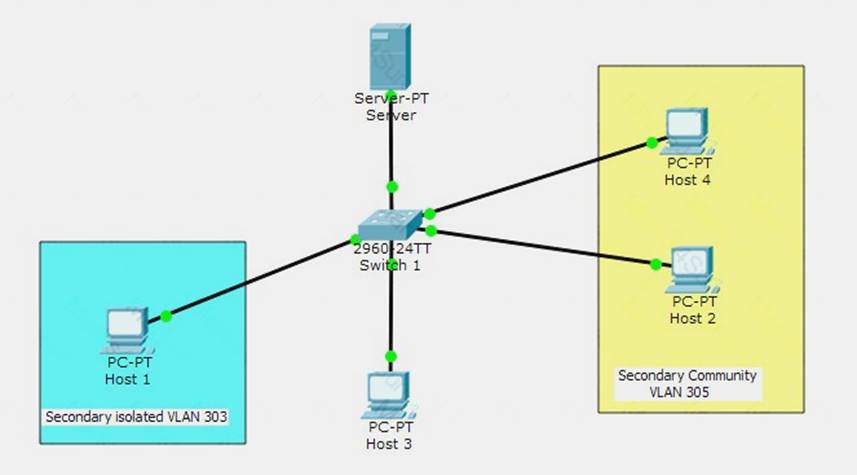
All ports on switch 1 have a primary VLAN of 300. Which devices can host 1 reach?
- A. Host 2
- B. Server
- C. Host 4
- D. Other devices within VLAN 303
Answer: B
NEW QUESTION 6
Which three options are common examples of AAA implementation on Cisco routers? (Choose three.)
- A. authenticating remote users who are accessing the corporate LAN through IPsec VPN connections
- B. authenticating administrator access to the router console port, auxiliary port, and vty ports
- C. implementing PKI to authenticate and authorize IPsec VPN peers using digital certificates
- D. tracking Cisco NetFlow accounting statistics
- E. securing the router by locking down all unused services
- F. performing router commands authorization using TACACS+
Answer: ABF
Explanation:
http://www.cisco.com/en/US/products/ps6638/products_data_sheet09186a00804fe332.html Need for AAA Services
Security for user access to the network and the ability to dynamically define a user's profile to gain access to network resources has a legacy dating back to asynchronous dial access. AAA network security services provide the primary framework through which a network administrator can set up access control on network points of entry or network access servers, which is usually the function of a router or access server.
Authentication identifies a user; authorization determines what that user can do; and accounting monitors the network usage time for billing purposes.
AAA information is typically stored in an external database or remote server such as RADIUS or TACACS+. The information can also be stored locally on the access server or router. Remote security servers, such as
RADIUS and TACACS+, assign users specific privileges by associating attribute-value (AV) pairs, which
define the access rights with the appropriate user. All authorization methods must be defined through AAA.
NEW QUESTION 7
Which statement about traffic inspection using the Cisco Modular Policy Framework on the ASA is true?
- A. HTTP inspection is supported with Cloud Web Security inspection
- B. QoS policing and QoS pnonty queuing can be configured for the same traffic
- C. ASA with FirePOWER supports HTTP inspection
- D. Traffic can be sent to multiple modules for inspection
Answer: A
NEW QUESTION 8
On an ASA, which maps are used to identify traffic?
- A. Policy maps
- B. Class maps
- C. Route maps
- D. Service maps
Answer: B
NEW QUESTION 9
What’s the technology that you can use to prevent non malicious program to run in the computer that is disconnected from the network?
- A. Firewall
- B. Software Antivirus
- C. Network IPS
- D. Host IPS.
Answer: D
NEW QUESTION 10
Which STP feature can prevent an attacker from becoming the root bridge by immediately shutting down the interface when it receives a BPDU?
- A. BPDU filtering
- B. root guard
- C. BPDU guard
- D. portFast
Answer: C
NEW QUESTION 11
Which statement about personal firewalls is true?
- A. They can protect a system by denying probing requests.
- B. They are resilient against kernel attacks.
- C. They can protect email messages and private documents in a similar way to a VPN.
- D. They can protect the network against attacks.
Answer: A
Explanation:
+ Block or alert the user about all unauthorized inbound or outbound connection attempts + Allows the user to control which programs can and cannot access the local network and/or Internet and provide the user with information about an application that makes a connection attempt + Hide the computer from port scans by not responding to unsolicited network traffic + Monitor applications that are listening for incoming connections + Monitor and regulate all incoming and outgoing Internet users + Prevent unwanted network traffic from locally installed applications + Provide information about the destination server with which an application is attempting to communicate + Track recent incoming events, outgoing events, and intrusion events to see who has accessed or tried to access your computer.
+ Personal Firewall blocks and prevents hacking attempt or attack from hackers Source: https://en.wikipedia.org/wiki/Personal_firewall
NEW QUESTION 12
Which IKE phase 1 parameter can you use to require the site-to-site VPN to us a pre-shared key?
- A. group
- B. hash
- C. authentication
- D. encryption
Answer: C
NEW QUESTION 13
Diffie-Hellman key exchange question
- A. IKE
- B. IPSEC
- C. SPAN
- D. STP
Answer: A
NEW QUESTION 14
Which quantifiable item should you consider when your organization adopts new technologies?
- A. threats
- B. vulnerability
- C. risk
- D. exploits
Answer: B
NEW QUESTION 15
What is the primary purpose of a defined rule in an IPS?
- A. to configure an event action that takes place when a signature is triggered
- B. to define a set of actions that occur when a specific user logs in to the system
- C. to configure an event action that is pre-defined by the system administrator
- D. to detect internal attacks
Answer: A
NEW QUESTION 16
Which component of CIA triad relate to safe data which is in transit?
- A. Confidentiality
- B. Integrity
- C. Availability
- D. Scalability
Answer: B
Explanation:
Integrity: Integrity for data means that changes made to data are done only by authorized individuals/systems. Corruption of data is a failure to maintain data integrity.
Source: Cisco Official Certification Guide, Confidentiality, Integrity, and Availability, p.6
NEW QUESTION 17
which are two valid TCP connection states (pick 2) is the gist of the question.
- A. SYN-RCVD
- B. Closed
- C. SYN-WAIT
- D. RCVD
- E. SENT
Answer: AB
Explanation:
TCP Finite State Machine (FSM) States, Events and Transitions + CLOSED: This is the default state that each connection starts in before the process of establishing it begins.
The state is called "fictional" in the standard.
+ LISTEN
+ SYN-SENT
+ SYN-RECEIVED: The device has both received a SYN (connection request) from its partner and sent its own SYN. It is now waiting for an ACK to its SYN to finish connection setup.
+ ESTABLISHED
+ CLOSE-WAIT
+ LAST-ACK
+ FIN-WAIT-1
+ FIN-WAIT-2
+ CLOSING
+ TIME-WAIT
Source:
http://tcpipguide.com/free/t_TCPOperationalOverviewandtheTCPFiniteStateMachineF-2.htm
NEW QUESTION 18
Which IPS mode provides the maximum number of actions?
- A. inline
- B. promiscuous
- C. span
- D. failover
- E. bypass
Answer: A
Explanation:
The first option is to put a sensor inline with the traffic, which just means that any traffic going through your network is forced to go in one physical or logical port on the sensor.
Because the sensor is inline with the network, and because it can drop a packet and deny that packet from ever reaching its final destination (because it might cause harm to that destination), the sensor has in fact just prevented that attack from being carried out. That is the concept behind intrusion prevention systems (IPS).
Whenever you hear IPS mentioned, you immediately know that the sensor is inline with the traffic, which makes it possible to prevent the attack from making it further into the network.
Source: Cisco Official Certification Guide, Difference Between IPS and IDS, p.460
NEW QUESTION 19
Which IDS/IPS solution can monitor system processes and resources?
- A. IDS
- B. HIPS
- C. PROXY
- D. IPS
Answer: B
NEW QUESTION 20
Which command do you enter to enable authentication for OSPF on an interface?
- A. router(config-if)#ip ospf message-digest-key 1 md5 CISCOPASS
- B. router(config-router)#area 0 authentication message-digest
- C. router(config-router)#ip ospf authentication-key CISCOPASS
- D. router(config-if)#ip ospf authentication message-digest
Answer: A
NEW QUESTION 21
Which filter uses in Web reputation to prevent from Web Based Attacks? (Choose two)
- A. outbreak filter
- B. buffer overflow filter
- C. bayesian overflow filter
- D. web reputation
- E. exploit filtering
Answer: AE
Explanation:
Source: http://www.cisco.com/c/en/us/products/security/email-security-appliance/outbreak_filters_index.html
NEW QUESTION 22
Refer to the exhibit.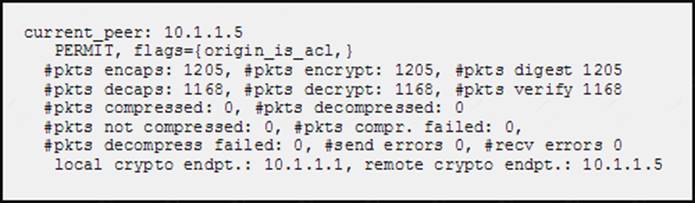
While troubleshooting site-to-site VPN, you issued the show crypto ipsec sa command. What does the given output show?
- A. IPSec Phase 2 is established between 10.1.1.1 and 10.1.1.5.
- B. ISAKMP security associations are established between 10.1.1.5 and 10.1.1.1.
- C. IKE version 2 security associations are established between 10.1.1.1 and 10.1.1.5.
- D. IPSec Phase 2 is down due to a mismatch between encrypted and decrypted packets.
Answer: A
Explanation:
This command shows IPsec SAs built between peers - IPsec Phase2. The encrypted tunnel is build between 10.1.1.5 and 10.1.1.1 (the router from which we issued the command).
NEW QUESTION 23
The command debug crypto isakmp results in ?
- A. Troubleshooting ISAKMP (Phase 1) negotiation problems
Answer: A
NEW QUESTION 24
Which two options are advantages of an application layer firewall? (Choose two.)
- A. provides high-performance filtering
- B. makes DoS attacks difficult
- C. supports a large number of applications
- D. authenticates devices
- E. authenticates individuals
Answer: BE
Explanation:
http://www.cisco.
com/en/US/prod/collateral/vpndevc/ps6032/ps6094/ps6120/prod_white_paper0900aecd8058ec85.html
Adding Intrusion Prevention
Gartner's definition of a next-generation firewall is one that combines firewall filtering and intrusion prevention systems (IPSs). Like firewalls, IPSs filter packets in real time. But instead of filtering based on user profiles and application policies, they scan for known malicious patterns in incoming code, called signatures. These signatures indicate the presence of malware, such as worms, Trojan horses, and spyware.
Malware can overwhelm server and network resources and cause denial of service (DoS) to internal employees, external Web users, or both. By filtering for known malicious signatures, IPSs add an extra layer of security to firewall capabilities; once the malware is detected by the IPS, the system will block it from the network.
Firewalls provide the first line of defense in any organization's network security infrastructure. They do so by matching corporate policies about users' network access rights to the connection information surrounding each
access attempt. If the variables don't match, the firewall blocks the access connection. If the variables do match, the firewall allows the acceptable traffic to flow through the network.
In this way, the firewall forms the basic building block of an organization's network security architecture. It pays to use one with superior performance to maximize network uptime for business-critical operations. The reason is that the rapid addition of voice, video, and collaborative traffic to corporate networks is driving the need for firewall engines that operate at very high speeds and that also support application-level inspection. While standard Layer 2 and Layer 3 firewalls prevent unauthorized access to internal and external networks, firewalls
enhanced with application-level inspection examine, identify, and verify application types at Layer 7 to make sure unwanted or misbehaving application traffic doesn't join the network. With these capabilities, the firewall can enforce endpoint user registration and authentication and provide administrative control over the use of multimedia applications.
NEW QUESTION 25
Refer to the exhibit.
The Admin user is unable to enter configuration mode on a device with the given configuration. What change can you make to the configuration to correct the problem?
- A. Remove the autocommand keyword and arguments from the username admin privilege line.
- B. Change the Privilege exec level value to 15.
- C. Remove the two Username Admin lines.
- D. Remove the Privilege exec line.
Answer: A
NEW QUESTION 26
......
P.S. Certifytools now are offering 100% pass ensure 210-260 dumps! All 210-260 exam questions have been updated with correct answers: https://www.certifytools.com/210-260-exam.html (481 New Questions)