Actual 210-255 Braindumps 2021
We provide real 210-255 exam questions and answers braindumps in two formats. Download PDF & Practice Tests. Pass Cisco 210-255 Exam quickly & easily. The 210-255 PDF type is available for reading and printing. You can print more and practice many times. With the help of our Cisco 210-255 dumps pdf and vce product and material, you can easily pass the 210-255 exam.
Online Cisco 210-255 free dumps demo Below:
NEW QUESTION 1
Which of the following is an example of a managed security offering where incident response experts monitor and respond to security alerts in a SOC?
- A. Cisco CloudLock
- B. Cisco’s Active Threat Analytics (ATA)
- C. Cisco Managed Firepower Service
- D. Cisco Jasper
Answer: B
NEW QUESTION 2
To which category do attributes belong within the VERIS schema ?
- A. victim demographics
- B. incident tracking
- C. Discovery and response
- D. incident description
Answer: D
NEW QUESTION 3
Which of the following are examples of some of the responsibility of a corporate CSIRT and the policies it helps create? (Choose four)
- A. Scanning vendor customer network
- B. incident classification and handling
- C. Information classification and protection
- D. Information dissemination
- E. Record retentions and destruction
Answer: BCDE
NEW QUESTION 4
Which string matches the regular expression r(ege)+x?
- A. rx
- B. regeegex
- C. r(ege)x
- D. rege+x
Answer: B
NEW QUESTION 5
What protocol is related to NAC?
- A. 802.1Q
- B. 802.1X (EAP-TLS, EAP-PEAP or EAP-MSCHAP)
- C. 802.1E
- D. 802.1F
Answer: B
NEW QUESTION 6
You have a video of suspect entering your office the day your data has being stolen?
- A. Direct evidence
- B. Indirect
- C. Circumstantial
Answer: B
NEW QUESTION 7
You have a video of a suspect entering a data center that was captured on the same that files in the same data center were transferred to a computer. Which type of is this?
- A. Physical evidence
- B. best evidence
- C. prima faice evidence
- D. indirect evidence
Answer: D
NEW QUESTION 8
Which element is included in an incident response plan?
- A. organization mission
- B. junior analyst approval
- C. day-to-day firefighting
- D. siloed approach to communications
Answer: A
Explanation:
The incident response plan should include the following elements:
– Mission– Strategies and goals– Senior management approval– Organizational approach to incident response– How the incident response team will communicate with the rest of the organization and with other organizations– Metrics for measuring the incident response capability and its effectiveness– Roadmap for maturing the incident response capability– How the program fits into the overall organization.
NEW QUESTION 9
Refer to the exhibit.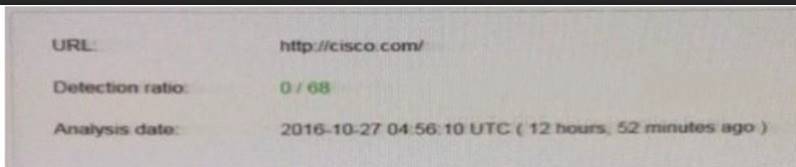
We have performed a malware detection on the Cisco website. Which statement about the result is true?
- A. The website has been marked benign on all 68 checks.
- B. The threat detection needs to run again.
- C. The website has 68 open threats.
- D. The website has been marked benign on 0 checks.
Answer: A
Explanation:
https://www.virustotal.com/en/url/df05d8e27bd760c33dc709951a5840cc6578d78d544d869890b7b94ea21e46b0
NEW QUESTION 10
Which of the following are the three metrics, or "scores," of the Common Vulnerability Scoring System (CVSS)? (Select all that apply.)
- A. Baseline score
- B. Base score
- C. Environmental score
- D. Temporal score
Answer: BCD
NEW QUESTION 11
Which process is being utilized when IPS events are removed to improve data integrity?
- A. data normalization
- B. data availability
- C. data protection
- D. data signature
Answer: A
Explanation:
Data normalization is the process of intercepting and storing incoming data so it exists in one form only. This eliminates redundant data and protects the data’s integrity.
Link: https://www.helpnetsecurity.com/2013/01/07/the-importance-of-data-normalization-in-ips/
NEW QUESTION 12
What is the process of remediation the network and systems and/or reconstructing so the responsible threat actor can be revealed?
- A. Data analysis
- B. Assets distribution
- C. Evidence collection
- D. Threat actor distribution
Answer: A
NEW QUESTION 13
Refer to the exhibit.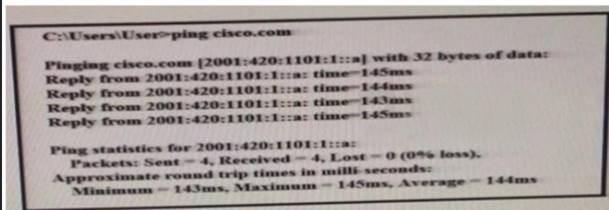
What can be determined from this ping result?
- A. The public IP address of cisco.com is 2001:420:1101:1::a.
- B. The Cisco.com website is down.
- C. The Cisco.com website is responding with an internal IP.
- D. The public IP address of cisco.com is an IPv4 address.
Answer: A
NEW QUESTION 14
Which Cyber Kill Model category does attacking vulnerability belong to?
- A. Exploitation
- B. Installation
- C. Deliver
- D. Action on Objectives
Answer: A
NEW QUESTION 15
According to NIST SP800-86, which action describes volatile data collection?
- A. collection of data during a system reboot
- B. collection of data that contains malware
- C. collection of date before system reboot
- D. collection of data after system reboot
Answer: C
NEW QUESTION 16
What is NAC?
- A. Non-Admin Closure
- B. Network Access Control
- C. Nepal Airline Corporations
- D. Network Address Control
Answer: B
NEW QUESTION 17
Refer to the following packet capture. Which of the following statements is true about this packet capture?
00:00:04.549138 IP omar.cisco.com.34548 > 93.184.216.34.telnet: Flags [S], seq
3152949738, win 29200,options [mss 1460,sackOK,TS val 1193148797 ecr 0,nop,wscale 7], length 000:00:05.547084 IP omar.cisco.com.34548 > 93.184.216.34.telnet: Flags [S], seq3152949738, win 29200,options [mss 1460,sackOK,TS val 1193149047 ecr 0,nop,wscale 7], length 000:00:07.551078 IP
omar.cisco.com.34548 > 93.184.216.34.telnet: Flags [S], seq3152949738, win 29200, options [mss 1460,sackOK,TS val 1193149548 ecr 0,nop,wscale 7], length 000:00:11.559081 IP omar.cisco.com.34548
> 93.184.216.34.telnet: Flags [S], seq3152949738, win 29200,options [mss 1460,sackOK,TS val 1193150550 ecr 0,nop,wscale 7], length 0
- A. The host with the IP address 93.184.216.34 is the source.
- B. The host omar.cisco.com is the destination.
- C. This is a Telnet transaction that is timing out and the server is not responding.
- D. The server omar.cisco.com is responding to 93.184.216.34 with four data packets.
Answer: C
NEW QUESTION 18
In Microsoft Windows, as files are deleted the space they were allocated eventually is considered available for use by other files. This creates alternating used and unused areas of various sizes. What is this called?
- A. network file storing
- B. free space fragmentation
- C. alternate data streaming
- D. defragmentation
Answer: B
Explanation:
Free (unallocated) space fragmentation occurs when there are several unused areas of the file system where new files or meta data can be written to. Unwanted free space fragmentation is generally caused by deletion or truncation of files, but file systems may also intentionally insert fragments (“bubbles”) of free space in order to facilitate extending nearby files
NEW QUESTION 19
According to NIST what option is unnecessary for containment strategy?
- A. The delayed containment
- B. Monitoring with methods other than sandboxing
Answer: AB
NEW QUESTION 20
Which of the following is not a metadata feature of the Diamond Model?
- A. Direction
- B. Result
- C. Devices
- D. Resources
Answer: C
NEW QUESTION 21
What are the metric values of the confidentiality based on the CVSS framework?
- A. Low-high
- B. Low –Medium-high
- C. High-Low-none
- D. High-none
Answer: C
NEW QUESTION 22
Which of the following has been used to evade IDS / IPS devices?
- A. SNMP
- B. HTTP
- C. TNP
- D. Fragmentation
Answer: D
NEW QUESTION 23
What is the difference between deterministic and probabilistic assessment method? (Choose Two)
- A. At deterministic method we know the facts beforehand and at probabilistic method we make assumptions
- B. At probabilistic method we know the facts beforehand and at deterministic method we make assumptions
- C. Probabilistic method has an absolute nature
- D. Deterministc method has an absolute nature
Answer: AD
NEW QUESTION 24
......
Recommend!! Get the Full 210-255 dumps in VCE and PDF From DumpSolutions, Welcome to Download: https://www.dumpsolutions.com/210-255-dumps/ (New 160 Q&As Version)