Cisco 210-250 Preparation Exams 2021
Cause all that matters here is passing the Cisco 210-250 exam. Cause all that you need is a high score of 210-250 Understanding Cisco Cybersecurity Fundamentals exam. The only one thing you need to do is downloading Examcollection 210-250 exam study guides now. We will not let you down with our money-back guarantee.
Online 210-250 free questions and answers of New Version:
NEW QUESTION 1
Which security monitoring data type is associated with application server logs?
- A. alert data
- B. statistical data
- C. session data
- D. transaction data
Answer: D
NEW QUESTION 2
Which term represents a potential danger that could take advantage of a weakness in a system?
- A. vulnerability
- B. risk
- C. threat
- D. exploit
Answer: D
NEW QUESTION 3
Which of the following are examples of system-based sandboxing implementations? (Select all that apply.)
- A. Google Project Zero
- B. Google Chromium sandboxing
- C. Java JVM sandboxing
- D. Threat Grid
- E. HTML5 “sandbox” attribute for use with iframes.
Answer: BCE
NEW QUESTION 4
Which of the following is true about heuristic-based algorithms?
- A. Heuristic-based algorithms may require fine tuning to adapt to network traffic and minimize the possibility of false positives.
- B. Heuristic-based algorithms do not require fine tuning.
- C. Heuristic-based algorithms support advanced malware protection.
- D. Heuristic-based algorithms provide capabilities for the automation of IPS signature creation and tuning.
Answer: A
NEW QUESTION 5
Which situation indicates application-level white listing?
- A. Allow everything and deny specific executable files.
- B. Allow specific executable files and deny specific executable files.
- C. Writing current application attacks on a whiteboard daily.
- D. Allow specific files and deny everything else.
Answer: D
NEW QUESTION 6
Which three options are types of Layer 2 network attack? (Choose three.)
- A. ARP attacks
- B. brute force attacks
- C. spoofing attacks
- D. DDOS attacks
- E. VLAN hopping
- F. botnet attacks
Answer: ACE
NEW QUESTION 7
Which statement about digitally signing a document is true?
- A. The document is hashed and then the document is encrypted with the private key.
- B. The document is hashed and then the hash is encrypted with the private key.
- C. The document is encrypted and then the document is hashed with the public key
- D. The document is hashed and then the document is encrypted with the public key.
Answer: B
NEW QUESTION 8
Which definition of vulnerability is true?
- A. an exploitable unpatched and unmitigated weakness in software
- B. an incompatible piece of software
- C. software that does not have the most current patch applied
- D. software that was not approved for installation
Answer: A
NEW QUESTION 9
Which hashing algorithm is the least secure?
- A. MD5
- B. RC4
- C. SHA-3
- D. SHA-2
Answer: A
NEW QUESTION 10
Which actions can a promiscuous IPS take to mitigate an attack? Choose three
- A. Denying Frames
- B. Resetting the TCP Connection
- C. Requesting host blocking
- D. Modifying packets
- E. Denying packets
- F. Requesting connection blocking
Answer: BCF
NEW QUESTION 11
For which purpose can Windows management instrumentation be used?
- A. Remote viewing of a computer
- B. Remote blocking of malware on a computer
- C. Remote reboot of a computer
- D. Remote start of a computer
Answer: A
NEW QUESTION 12
Which three fields are within an X.509v3 end entity certificate? (Choose three).
- A. Private Key associated with the certificate authority
- B. Digital signature
- C. Public key associated with the certificate authority
- D. Public key associated with the subject
- E. Basic constraints
- F. Revocation authority for use when the certificate expires
Answer: BDE
NEW QUESTION 13
Which protocols is primarily supported by the 3rd layer of the OSI ref models ?
- A. HTTP/TLS
- B. ATM/MPLS
- C. Ipv4/IPv6
- D. TCP/UDP
Answer: C
NEW QUESTION 14
Which process continues to be recorded in the process table after it has ended and the status is returned to the parent?
- A. daemon
- B. zombie
- C. orphan
- D. child
Answer: B
NEW QUESTION 15
What does the sum of the risks presented by an application represent for that application?
- A. Application attack surface
- B. Security violation
- C. Vulnerability
- D. HIPPA violation
Answer: A
NEW QUESTION 16
Which definition of a daemon on Linux is true?
- A. error check right after the call to fork a process
- B. new process created by duplicating the calling process
- C. program that runs unobtrusively in the background
- D. set of basic CPU instructions
Answer: C
NEW QUESTION 17
Which of the following are Cisco cloud security solutions?
- A. CloudDLP
- B. OpenDNS
- C. CloudLock
- D. CloudSLS
Answer: BC
NEW QUESTION 18
Which three statements about host-based IPS are true? (Choose three.)
- A. It can view encrypted files.
- B. It can have more restrictive policies than network-based IPS.
- C. It can generate alerts based on behavior at the desktop level.
- D. It can be deployed at the perimeter.
- E. It uses signature-based policies.
- F. It works with deployed firewalls.
Answer: ABC
NEW QUESTION 19
Drag the data source on the left to the left to the correct data type on the right.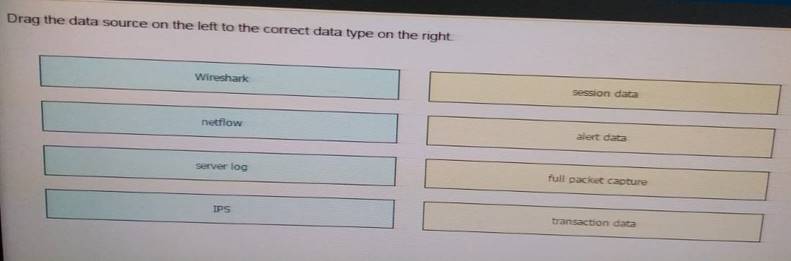
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Wireshark = Full packet capture Netflow = Session Data
Server log = Transaction Data IPS = Alert data
NEW QUESTION 20
What is one of the advantages of the mandatory access control (MAC) model?
- A. Easy and scalable.
- B. Stricter control over the information access.
- C. The owner can decide whom to grant access to.
Answer: B
NEW QUESTION 21
Which vulnerability is an example of Heartbleed?
- A. Buffer overflow
- B. Denial of service
- C. Command injection
- D. Information disclosure
Answer: D
NEW QUESTION 22
Cisco pxGrid has a unified framework with an open API designed in a hub-and-spoke architecture. pxGrid is used to enable the sharing of contextual-based information from which devices?
- A. From a Cisco ASA to the Cisco OpenDNS service
- B. From a Cisco ASA to the Cisco WSA
- C. From a Cisco ASA to the Cisco FMC
- D. From a Cisco ISE session directory to other policy network systems, such as Cisco IOS devices and the Cisco ASA
Answer: D
NEW QUESTION 23
......
Recommend!! Get the Full 210-250 dumps in VCE and PDF From prep-labs.com, Welcome to Download: https://www.prep-labs.com/dumps/210-250/ (New 145 Q&As Version)